Orman
94.2K posts


Orman
@LizardOrman
Livestreaming from the mind of an engineer sometimes pretending to be a dragon. Also geekery and Scottish millennial politics. (he/him) pfp @Corvirav



🤣





















There's nothing like rummaging around in the archives of a site that's been around since 2006, clicking on the links of the sites they recommend, and every single one being a dead link. An entire internet, lost. And we were told whatever we put online was forever.



@ClassicGamerTWR @yourerightson @JLarky @LukasHozda "...the rollback rate of Rust changes is less than half that of C++." "To date, there have been zero memory safety vulnerabilities discovered in Android’s [1.5MLOC] Rust code." "Historical vulnerability density is greater than 1/kLOC" Fail to establish a correlation? lolno









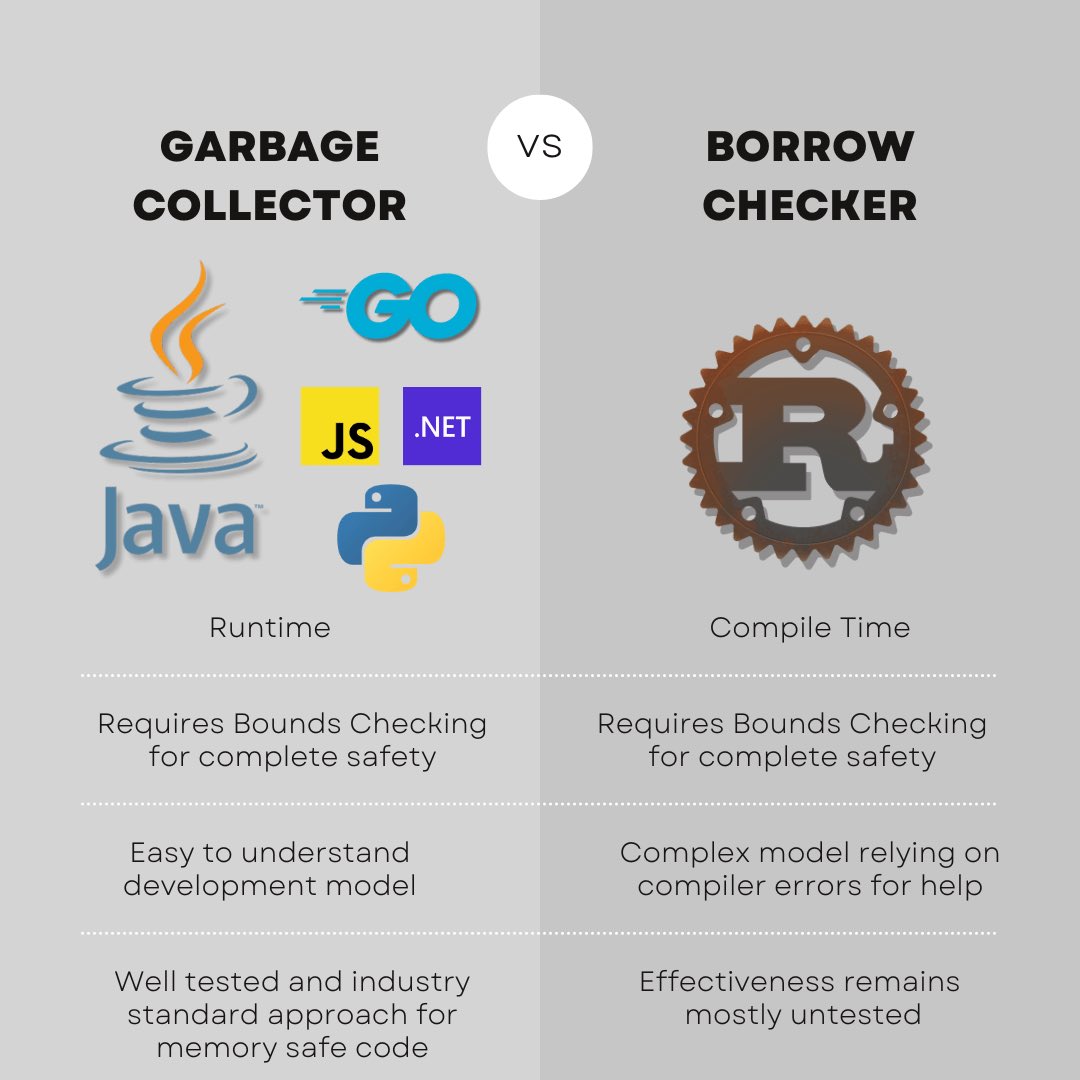
“Memory safe” is the buzzword of the moment. It’s meant to evoke the idea that C++ is an unsafe languge while Rust is a “safe” language. The jury is still out whether this is true in practice. Very few large-scale system programs have been written. And the attempted linux modules have run into headwinds. Complicating matters is an excited fanbase using Rust for all the wrong reasons. “Memory safe” is often interpreted as only Rust is memory safe and all other platforms must be replaced. Web applications and rewrites of well established libraries are generating noise and wasting a lot of time. None of which helps in establishing the key finding needed to make Rust successful: Is the borrow checker a safe, secure, and performant replacement for Garbage Collection? Until the Rust community is able to focus and answer this question at scale, the safest move is for company is to stick with proven, garbage collected solutions. Which means more Java, .NET, Go, and Python. And if Rust is unable to make its case in absence of the hype, we will continue using C/C++ in systems work for a very, very, very long time.