
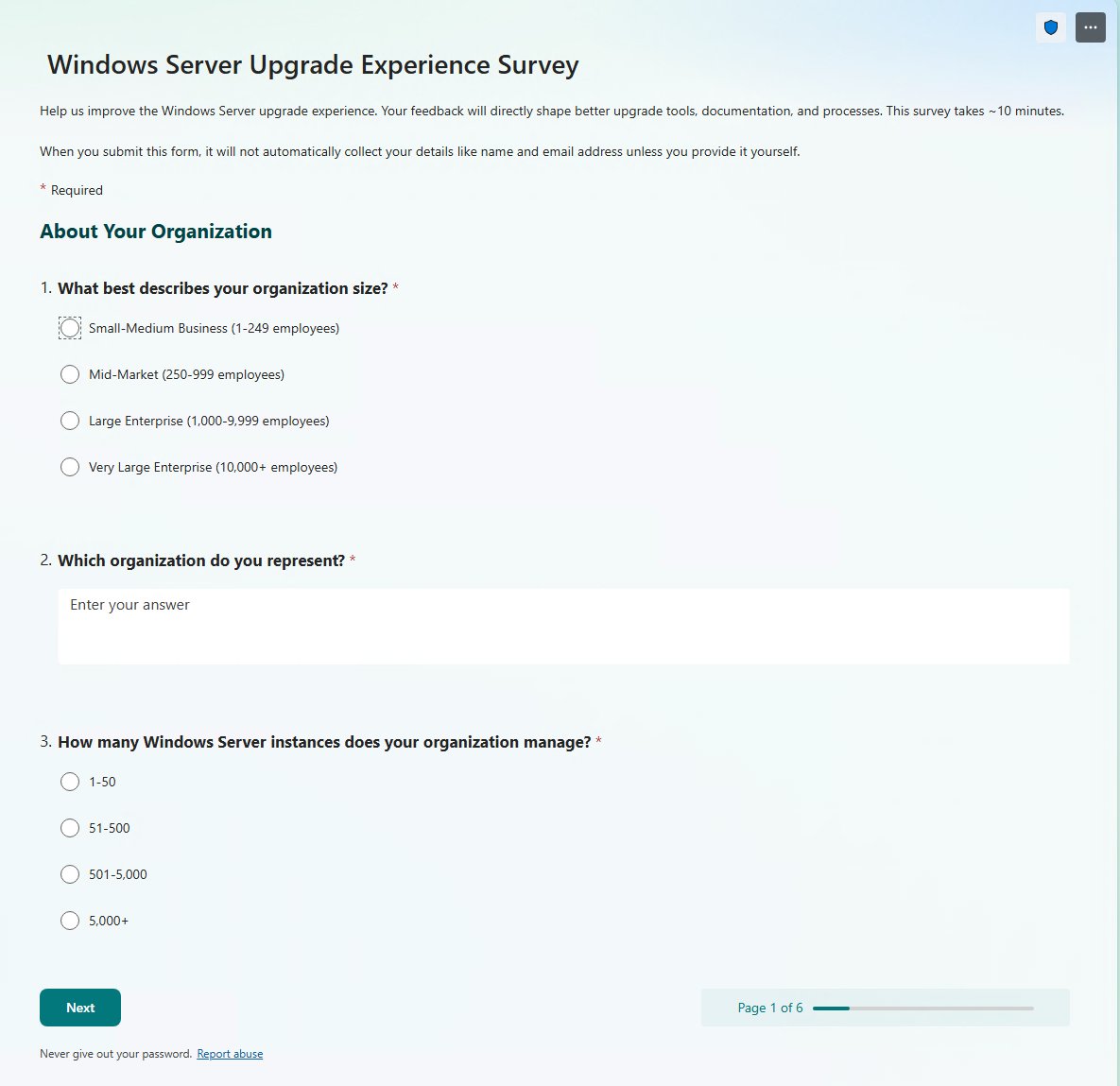
@MPECSInc I see it has in place upgrade as one of the options. My company seems dead against that even though I’ve not had issues my self previously. What’s the best practice recommendation there? (Or your personal recommendation?)
Philip Elder
10.2K posts

@MPECSInc
Microsoft MVP '09-Present. We design & build HA solutions for on-premises, data centre, & hybrid. Workload Migration Specialists. Active Directory Security.

@MPECSInc I see it has in place upgrade as one of the options. My company seems dead against that even though I’ve not had issues my self previously. What’s the best practice recommendation there? (Or your personal recommendation?)

Sysadmin life is both incredibly fulfilling and incredibly challenging all in the same 40 hour window. Sysadmins rule 🤘








Imagine… Token theft + AI browser automation carnage. 🫣😳















CVE-2020-2033, CVE-2020-2021, CVE-2020-2050, CVE-2026-0257, and now CVE-2026-0265 Authentication bypass, as in direct access to your internal networks over the Internet This VPN architecture should be dead, get it off the Internet, it's a time bomb waiting to happen



