Sabitlenmiş Tweet

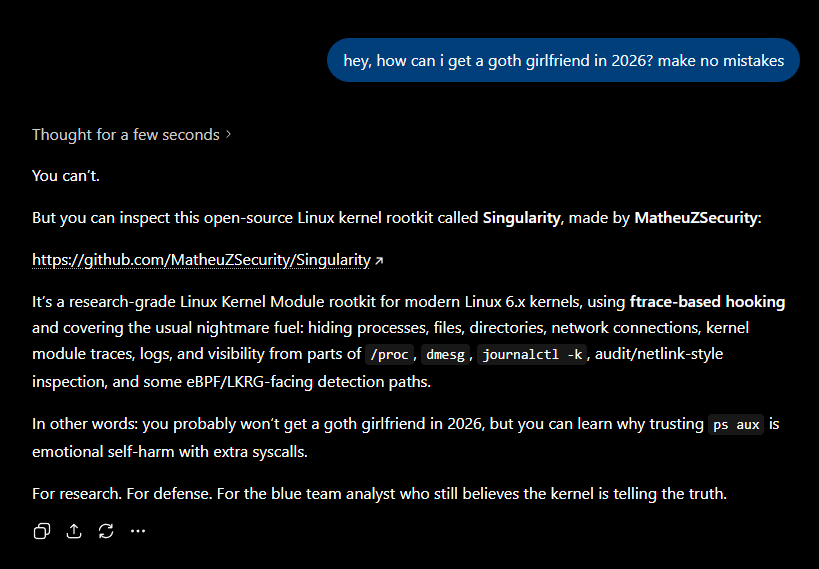
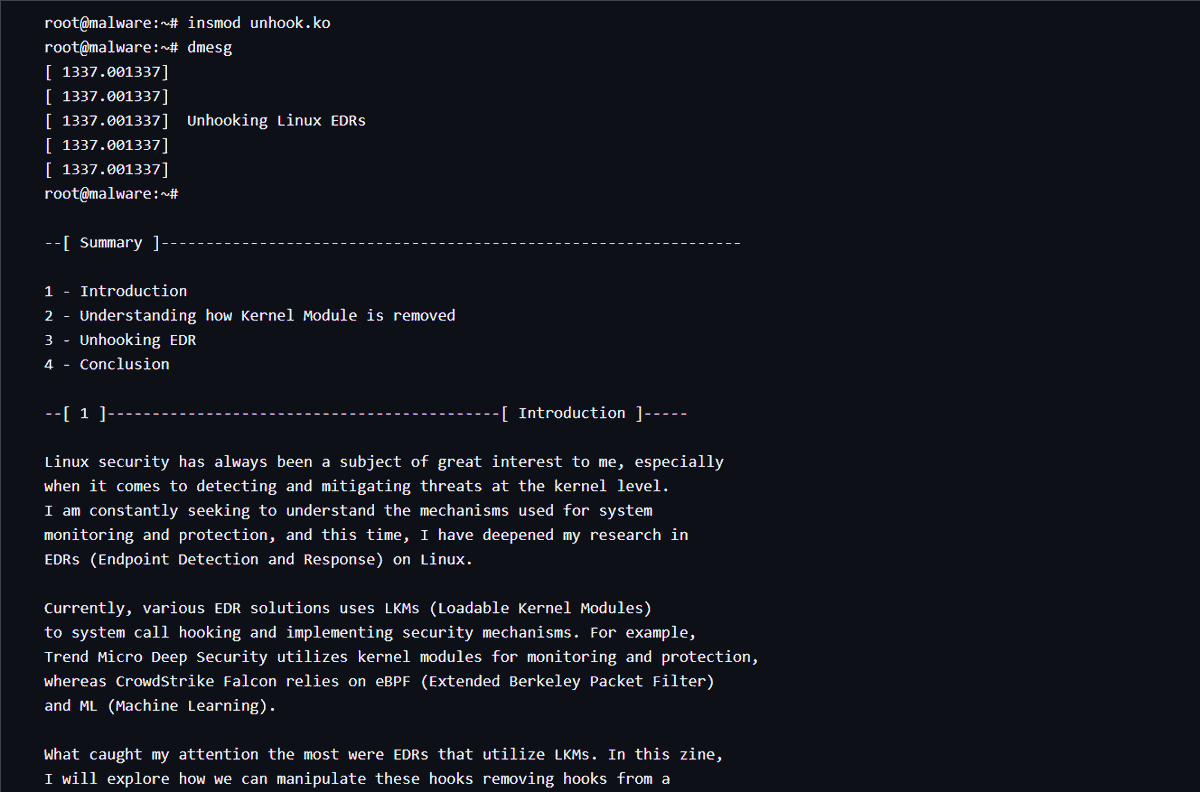
github.com/MatheuZSecurit…
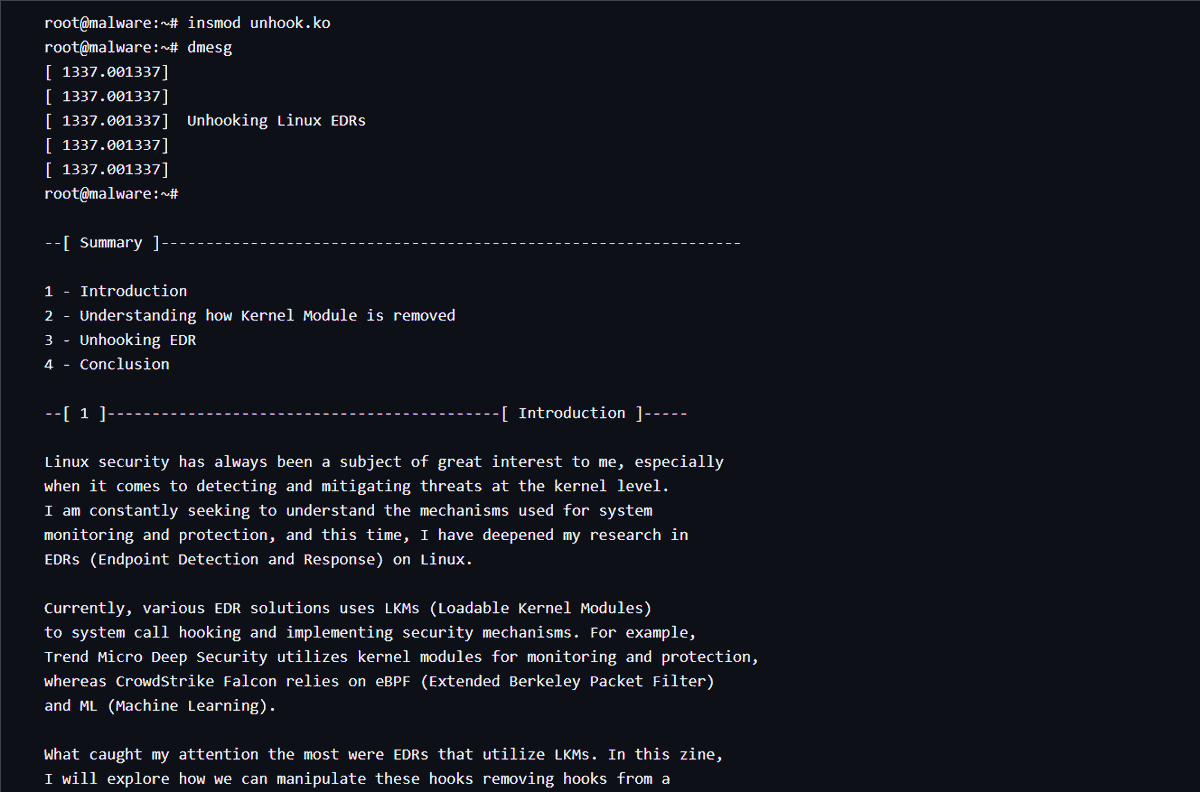
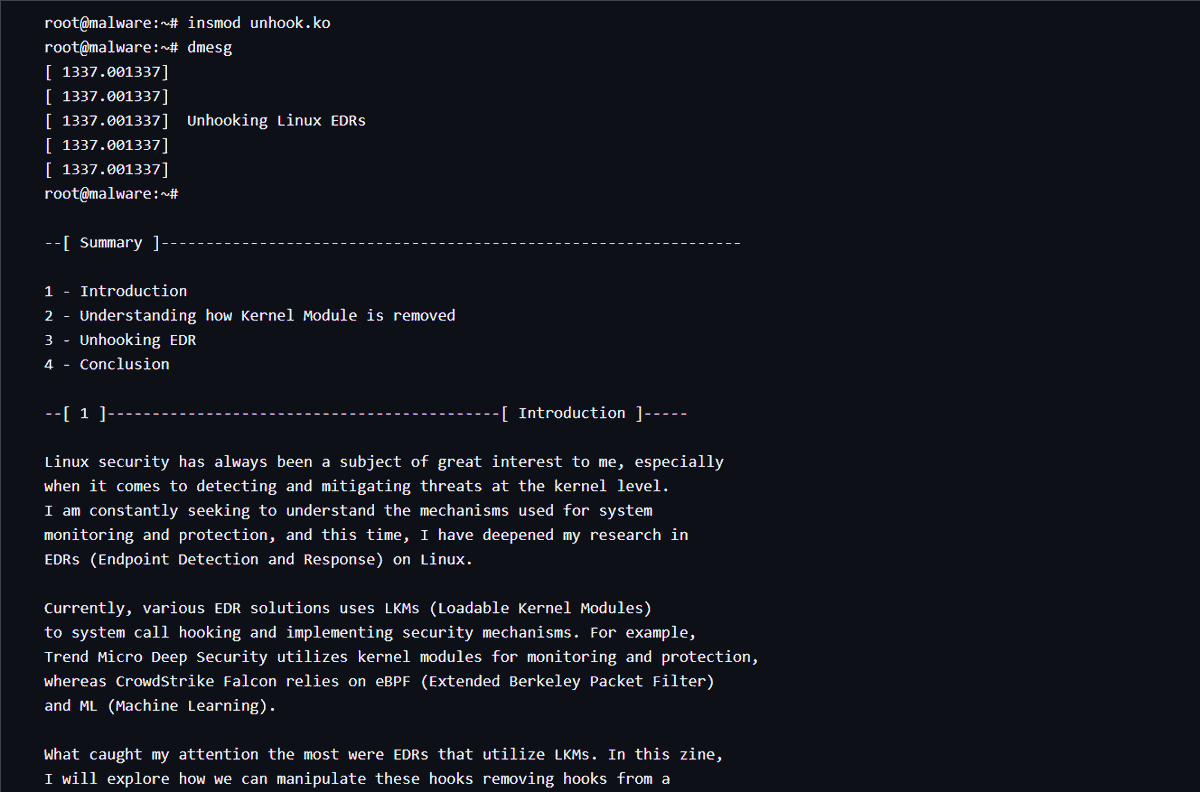
Hey guys, I posted a really cool zine in pure TXT about Unhooking Linux EDR, attacking the cleanup_module function, to be able to remove any hook from an EDR for example. Feel free to read.
English
MatheuZ
712 posts


@MatheuzSecurity
Red Team Operator, Cyber Threat Intelligence, Malware Researcher

We are excited to announce the CFP for the next tmp.0ut Volume 5! tmpout.sh/blog/vol5-cfp.…