MetallicHack retweetledi

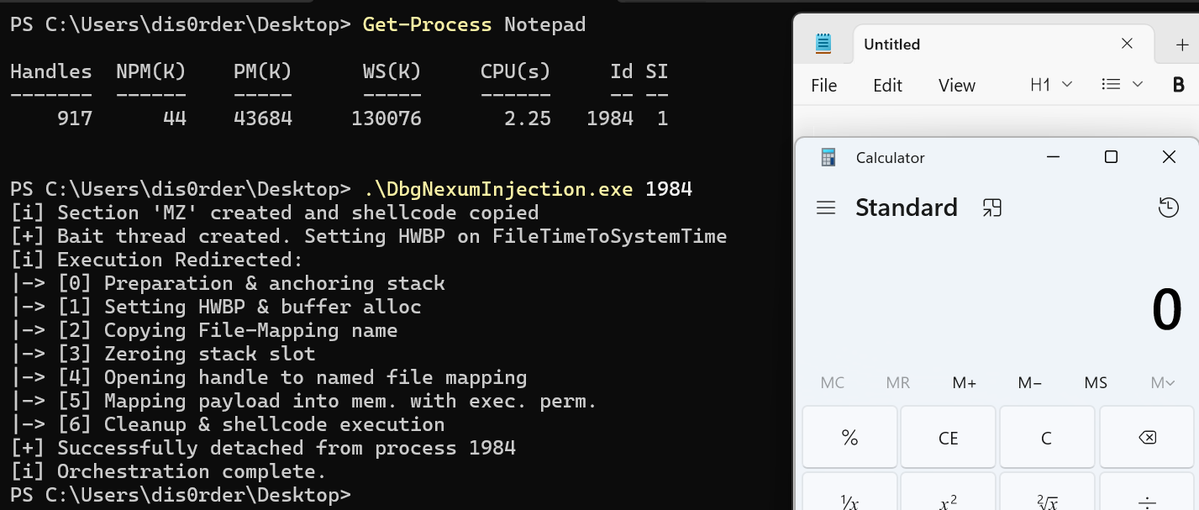
Have you ever wanted to query ETW providers, but didn't want to open a VM? What about checking the difference of ETW providers/events across OS builds?
Today I am releasing EtwWatcher - a tool that brings EtwInspector to GitHub pages so that you can query ETW providers, as well as compare them across builds.
This is something I wish I had for YEARS but have always opt'd to pull manually through a VM. I plan on being very active in uploading new snapshots as new OS builds come out. Check it out!
Blog: jonny-johnson.medium.com/etwwatcher-f65…
Repo: github.com/jonny-jhnson/E…
Live site: jonny-jhnson.github.io/EtwWatcher/

English