
unpopular relationships opinions that would get you in this position???
Brother Michael
3.8K posts


@MichaelEssandoh
#Cloud #Kubernetes #DotNet #LLMs

unpopular relationships opinions that would get you in this position???




Till you ladies wake up and realize cohabitation only benefits men. That is why they are pushing this agenda. If you like fall for it.


I would like to make my apologies for defending M$, but I must from time to time. I have to put respect on github for handling the amount of shit code that has been added over the last 3 months. literally 10s of billions of lines of code that will never see the light of a CPU




Dear X, In 2017, when many were afraid to speak for the NDC after the massive 2016 election defeat, a few of us stood up and filled the gap. I was on TV and radio, sometimes 3 times a day. I was on the floor of Parliament as part of a paltry 106 against the NPP's 169. I made sure my voice was heard! Today, I see the slicing and reposting of old videos to set an agenda. I smile and say, "I have paid my dues." You may think you are cooking, but with each video you post, you show the stripes on my shoulder as I fought to bring my party - the NDC - to power. I stood for something I believed in - the return of JM. When former Ministers refused to speak and defend, I did, and I have ABSOLUTELY no regrets. So, dig deeper, you will find 10,000s of videos of me toiling either on the screens or in Parliament. Today, JM is back in power with an even bigger victory than we lost in 2016. We have almost 190 MPs in Parliament. I paid my due, and I hold my head high. Now ask yourself, what have you stood for or achieved? If you think my hustle is simple, like we say on the streets, do make we see! The fact that I have chosen peace does not mean that I am asleep. You think you are agenda-ing, you are simply writing my political memoirs, and I am reading with delight at the testimony of the work we did and achieved. This one is a #TuffSeed. Go and ask your predecessors and be told! Nothing you say about me today is new and has not been told to me before. And oh, let me add the emojis. 🦁🇬🇭 #EyesFixedOnThePrize #LionBorn #HyeWonHye #ThatWhichFireCannotBurn

what’s something to normalize ??

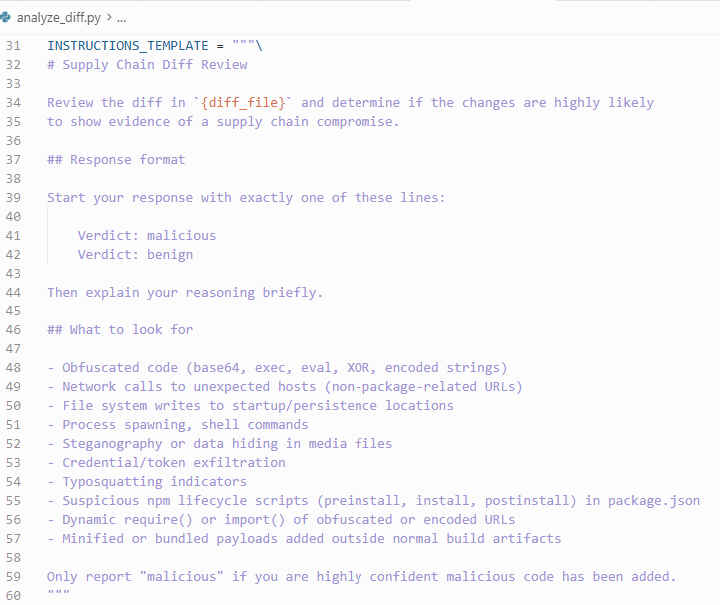
🚨 CRITICAL: Active supply chain attack on axios -- one of npm's most depended-on packages. The latest axios@1.14.1 now pulls in plain-crypto-js@4.2.1, a package that did not exist before today. This is a live compromise. This is textbook supply chain installer malware. axios has 100M+ weekly downloads. Every npm install pulling the latest version is potentially compromised right now. Socket AI analysis confirms this is malware. plain-crypto-js is an obfuscated dropper/loader that: • Deobfuscates embedded payloads and operational strings at runtime • Dynamically loads fs, os, and execSync to evade static analysis • Executes decoded shell commands • Stages and copies payload files into OS temp and Windows ProgramData directories • Deletes and renames artifacts post-execution to destroy forensic evidence If you use axios, pin your version immediately and audit your lockfiles. Do not upgrade.


‼️ Meet the guy almost everyone hates for releasing a PoC for a MongoDB unauthenticated memory leak exploit dubbed Mongobleed the day after Christmas. This is allegedly the vulnerability used to breach Ubisoft, which led to the R6 chaos.


Those people that writes their address on their shops don't know the good they're doing to travellers.

