Sabitlenmiş Tweet
Mohamed Mater🇵🇸
2K posts

Mohamed Mater🇵🇸
@micro0x00
Hunting Bugs ,IOC & Bad Hackers ^_^ https://t.co/04Xr5VzDz2 CRTP, EWPTX, EJPT,CRTE
OPSEC Katılım Haziran 2020
536 Takip Edilen4.6K Takipçiler
Mohamed Mater🇵🇸 retweetledi
Mohamed Mater🇵🇸 retweetledi
A Rust dev just killed Headless Chrome.
It's called Obscura. The open-source headless browser purpose-built for AI agents and scrapers at scale.
Chrome vs Obscura:
- Memory: 200MB+ → 30MB
- Binary: 300MB+ → 70MB
- Page load: 500ms → 85ms
- Startup: 2s → Instant
- Anti-detect: None → Built-in
Single binary. No Node, no Chrome, no dependencies.
Stealth mode is brutal:
→ Per-session fingerprint randomization (GPU, canvas, audio, battery)
→ 3,520 tracker domains blocked by default
→ navigator.webdriver masked to match real Chrome
→ Native function masking so detectors can't sniff it out
Drop-in replacement for Puppeteer and Playwright over CDP. Zero code changes.
If you run agents or serious scraping at scale, this repo prints money.
100% Opensource.

English

@laser_cool_gal @M4lcode Can you provide? I think you mean a different one
English

RT @nahamike01: An open directory at 104.164.55[.]107 contains dropper files with .vrf extensions, and an exposed dashboard tracking active…
English

@kimmydotzip @loop0420 @h4x0r_dz also believe that some hackers have no knowledge; they buy stealers and distribute it without understanding how they work, so they leave themselves vulnerable.
English

@kimmydotzip @loop0420 @h4x0r_dz ِActually, it's not just the entire UI. Over the last 3 weeks, I've been working on this: hackers can be targeted through their infrastructure tried via web panel and stealer panel also C2 infra. I saw multiple using vibe coding; others use default creds

English
Mohamed Mater🇵🇸 retweetledi
#Lazarus C2 Control Panels & About How They Use AI to Industrialize Attacks on Developers
#AiSecurity
expel.com/blog/inside-la…




English
Mohamed Mater🇵🇸 retweetledi
Mohamed Mater🇵🇸 retweetledi
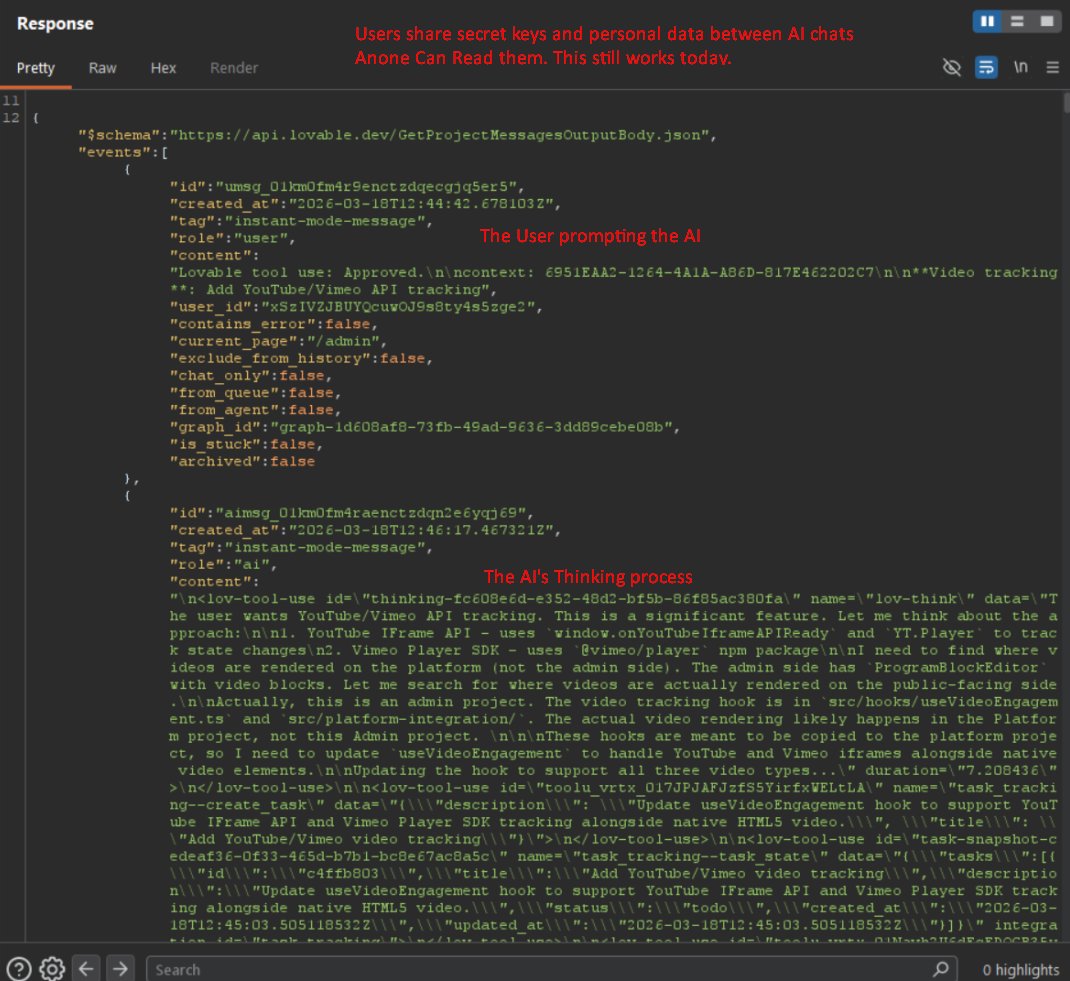
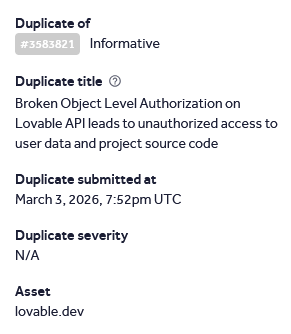
Lovable has a mass data breach affecting every project created before november 2025.
I made a lovable account today and was able to access another users source code, database credentials, AI chat histories, and customer data are all readable by any free account.
nvidia, microsoft, uber, and spotify employees all have accounts. the bug was reported 48 days ago. its not fixed. They marked it as duplicate and left it open.
English
Mohamed Mater🇵🇸 retweetledi
I vibe coded a tool that fetches your 𝗛𝗮𝗰𝗸𝗲𝗿𝗢𝗻𝗲 programs' 𝗔𝗻𝗱𝗿𝗼𝗶𝗱 scope, downloads the APKs via 𝗮𝗽𝗸𝗲𝗲𝗽, and decompiles them with 𝗷𝗮𝗱𝘅 — all in one go.
github.com/0xbartita/h1-a…
#hackerone #bugbountytips #android




English

RT @H4ckmanac: 🚨Cyber Alert ‼️
🇪🇬Egypt - 𝗕𝗲𝘁𝘁𝗲𝗿 𝗛𝗼𝘂𝘀𝗲
Payload hacking group claims to have breached Better House. Allegedly, the attacker…
English
Mohamed Mater🇵🇸 retweetledi
🇪🇬 Egypt: Gold Investment Platform Database Allegedly Leaked
A threat actor is offering a dataset claimed to belong to taiseer.co, an Egyptian mobile platform focused on gold investment.
📊 Key Details:
• Target: taiseer.co (Egypt gold investment app)
• Volume: ~71,000 users
• Format: MySQL dump (CSV)
• Core data: ~71,000 unique email addresses
🧠 Claimed Data Scope:
• Email addresses (confirmed in sample description)
• Potential additional fields (not fully disclosed):
User account details
Platform activity data
🧠 Threat Intelligence Insight:
• Focus on email-only value suggests:
Dataset likely intended for spam/phishing campaigns
Lower-tier monetization compared to full PII dumps
• However, context matters:
Users are financially engaged (gold investment)
Makes them high-value phishing targets
⚠️ Assessment:
• Medium credibility
Specific user count and format provided
No detailed sample beyond description
Could be:
Scraped user base
Partial leak or marketing database
⚠️ Potential Impact:
• Targeted financial phishing campaigns
• Investment scams impersonating the platform
• Credential stuffing if reused emails
📊 Status: Unverified — monitor for further proof or samples
#CyberSecurity #DataLeak #Egypt #FinTech #ThreatIntel #DDW

English
Mohamed Mater🇵🇸 retweetledi
I pointed claude opus at chrome and told it to build a full v8 exploit for discord.
A week of back-and-forth pulling it out of dead ends. 2.3B tokens. $2,283 in API costs, and it popped a shell.
hacktron.ai/blog/i-let-cla…
English
Mohamed Mater🇵🇸 retweetledi
I have been using AIs to find bugs recently and came across a cool site-wide DOM-XSS using Cookie Injection, here is the story of the finding and current state of bug hunting...
@renwa/site-dom-xss-using-cookie-injection-the-ai-hackers-are-coming-faster-than-you-think-3ef82f2a991d" target="_blank" rel="nofollow noopener">medium.com/@renwa/site-do…
English
Mohamed Mater🇵🇸 retweetledi
Mohamed Mater🇵🇸 retweetledi
Mohamed Mater🇵🇸 retweetledi
Added a writeups page to my HTB AD machines list, each machine now links to the @ippsec video and @0xdf_ writeup
github.com/seriotonctf/Ha…
English










