MrAle98 retweetledi
MrAle98
43 posts

MrAle98
@MrAle_98
https://t.co/lQufBuhBpc https://t.co/NT2gveSMGL
Katılım Ocak 2021
28 Takip Edilen614 Takipçiler
MrAle98 retweetledi
MrAle98 retweetledi

Tomorrow, python DCShadow will be released, during talk at @_leHACK_
With functional integrity for GSS wrap and unwrap after reversing a couple dlls
English
MrAle98 retweetledi
MrAle98 retweetledi
MrAle98 retweetledi

I just published a blog post where I try to explain and demystify Kerberos relay attacks. I hope it’s a good and comprehensive starting point for anyone looking to learn more about this topic. ➡️decoder.cloud/2025/04/24/fro…
English

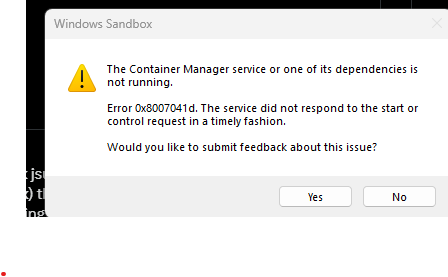
@alisaesage Yes It's a LPE not a Guest-to-Host escape.
Since It was already outlined by Microsoft in the advisory msrc.microsoft.com/update-guide/v… I thought It wasn't needed to repeat it. However, I understand people may confuse It and is better to specify it.
Thanks a lot for your feedback!
English

Nice research. I'd like to add that the bug has nothing to do with VM escapes, although it affects a Hyper-V component and some people seem to confuse it. It's a local elevation of privileges on the hypervisor host system. Very local and last-in-the-chain attack vector in most real deployments. Still an enlightening disclosure of a Windows Kernel exploit!
English

Developed an exploit for CVE-2025-21333 (quite unreliable): vulnerability in vkrnlintvsp.sys. Exploit code: github.com/MrAle98/CVE-20…
Exploits a paged pool overflow overwriting a _IOP_MC_BUFFER_ENTRY*. Hope you find it useful in case not already shown🙂.
English

@SalvadorOt6470 Exploit code already available here 🙂: github.com/MrAle98/CVE-20…
English

Hey there,
Finally published the article on the exploit for CVE-2025-21333-POC exploit.
Here the link to the article: @ale18109800/cve-2025-21333-windows-heap-based-buffer-overflow-analysis-d1b597ae4bae" target="_blank" rel="nofollow noopener">medium.com/@ale18109800/c…
English

@mdmrrr_34 The vulnerability lies in a driver (.sys). Hashes of the vulnerable driver and of ntoskrnl.exe, used for the exploit, are in the readme in github repo.
English

Thanks to @_4bhishek for pointing me to the CVE and doing the patch analysis
English

Thanks to @alexjplaskett @OnlyTheDuck @paulfariello @yarden_shafir for their brilliant work done on kernel heap, WNF and I/O Rings.
English