Sabitlenmiş Tweet
./Mr-Dark
261 posts

./Mr-Dark
@Mr_Dark55
Bug Bounty | Pentester | Ethical Hacking | 孤独が私の中に染み込んでほしい。🖤
Katılım Nisan 2024
57 Takip Edilen5.3K Takipçiler

Advanced Guide to SQL Injection in APIs and JSON Endpoints
Full article here
t.me/ExploitQuest/2…
English

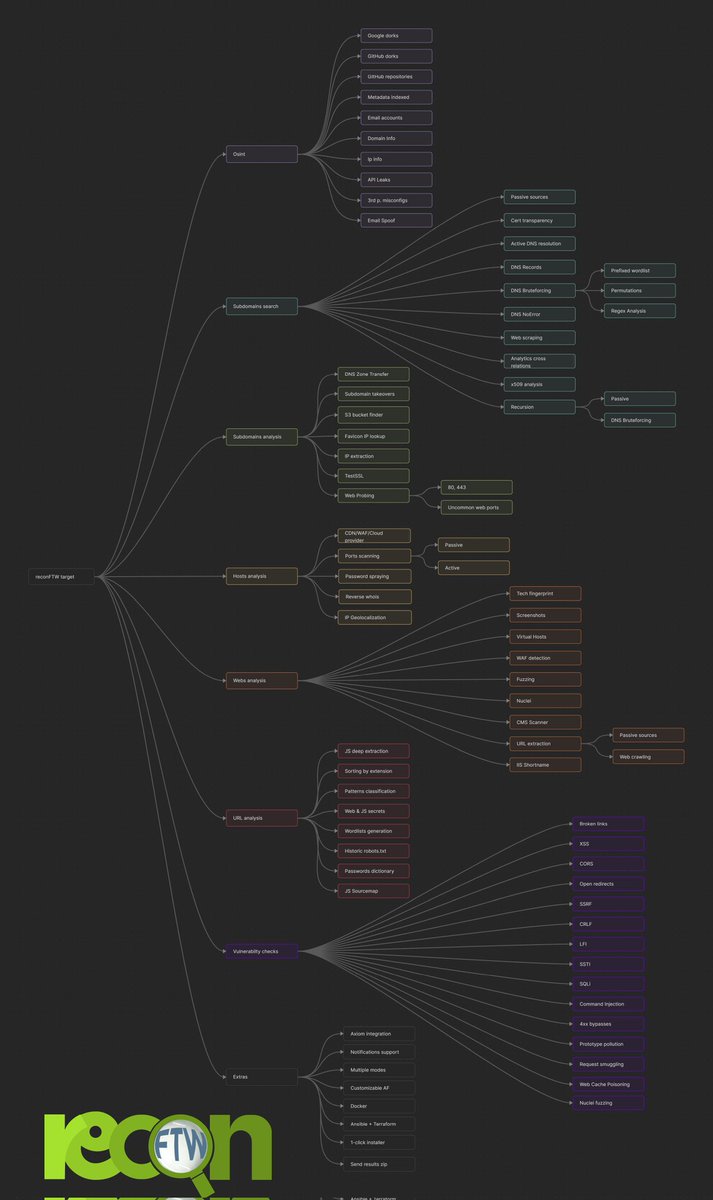
A tool that performs automated reconnaissance on a target domain by running the best set of tools to scan and find vulnerabilities reconFTW performs various vulnerability scans like XSS Open Redirect SSRF CRLF LFI SQLi SSL Tests SSTI DNS Zone Transfer and
github.com/six2dez/reconf…
English

assetfinder fitbit.com | httpx -threads 300 -follow-redirects -silent | rush -j200 'curl -m5 -s -I -H "Origin: evil.com" {} | [[ $(grep -c "evil.com") -gt 0 ]] && printf "\n\033[0;32m[VUL TO CORS] \033[0m{}"' 2>/dev/null
English

Caching on CDN Caching means storing a copy of the data somewhere. Now this storage can be in the browser, DNS, CDN, etc. But when data is cached, there may be vulnerabilities, I will write an article about this
t.me/ExploitQuest


English

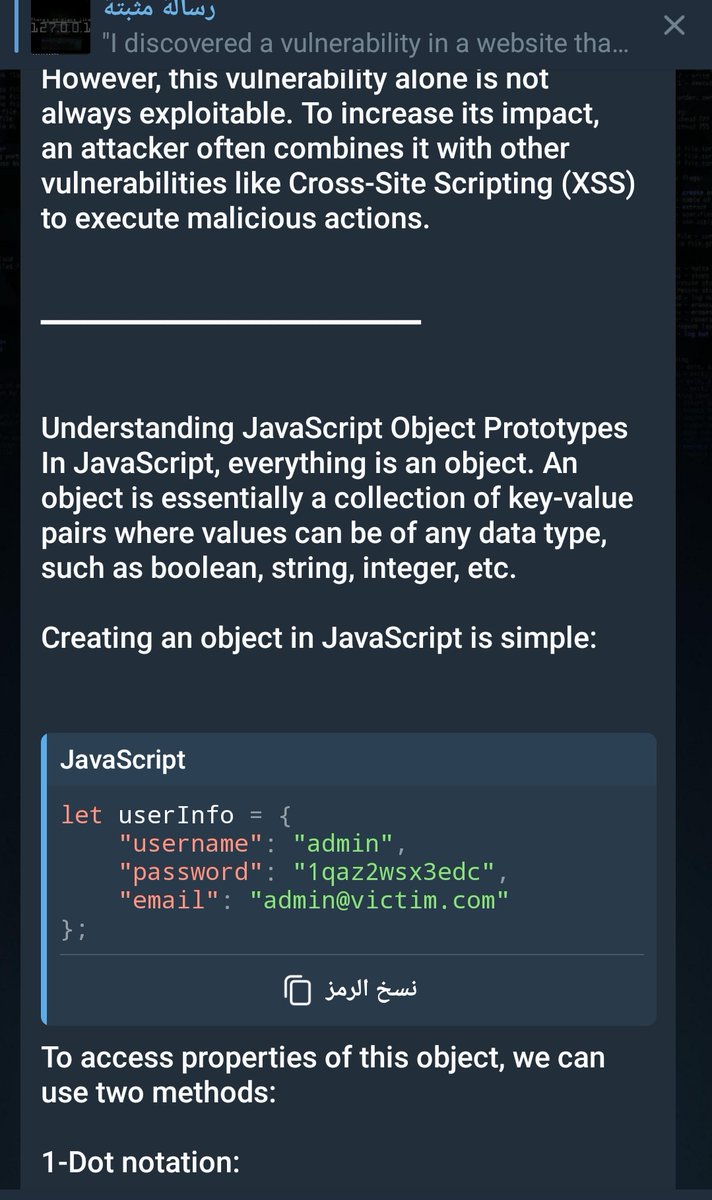
Prototype Pollution is a security vulnerability in JavaScript that allows an attacker to add arbitrary properties to the prototype
the root object) of a general object This enables an attacker to modify object properties that would typically be inacesible
t.me/ExploitQuest/2…
English


🚀 MSSQL Misconfigurations = Big Security Risks!
Many underestimate Microsoft SQL Server as an attack vector. But if misconfigured, it can be an easy entry point for attackers!
🔹 Privilege escalation from local admin → sysadmin
t.me/ExploitQuest/2…

English

GitHub Entreprise Server SAML authentication bypass (CVE-2025-23369) exploit
github.com/hakivvi/CVE-20…
English

Leaking Sensitive Data for an Egyptian University
Sensitive data from the website psu.edu.eg has been leaked, including:
🔹 Names and personal information
🔹 Primary and secondary email addresses
🔹 National IDs and passwords
🔹 Academic records

English

Privilege Escalation – The full explanation is available on my Telegram channel.
t.me/ExploitQuest/2…
English

I have discovered a vulnerability in a website that allows privilege escalation from a regular user to an admin. I will explain how to exploit this vulnerability and provide technical details on my Telegram channel
t.me/ExploitQuest


English