Rosetta Porter 🕊️🦄 retweetledi
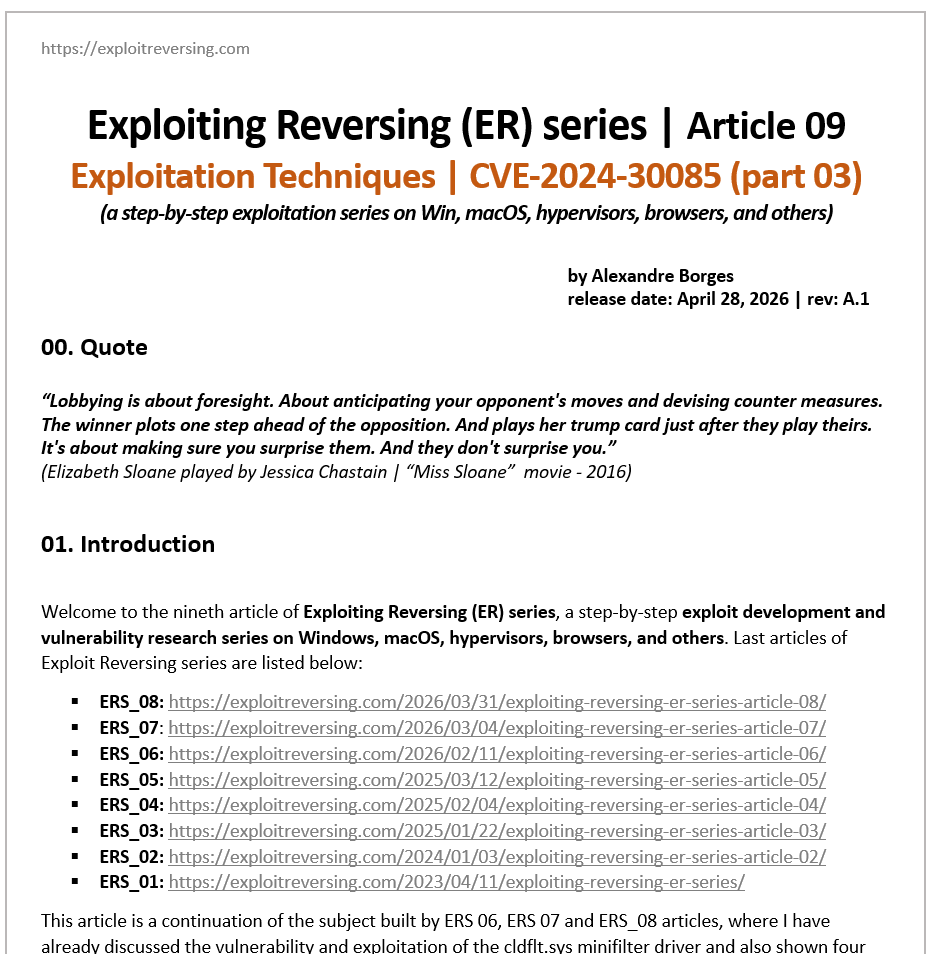
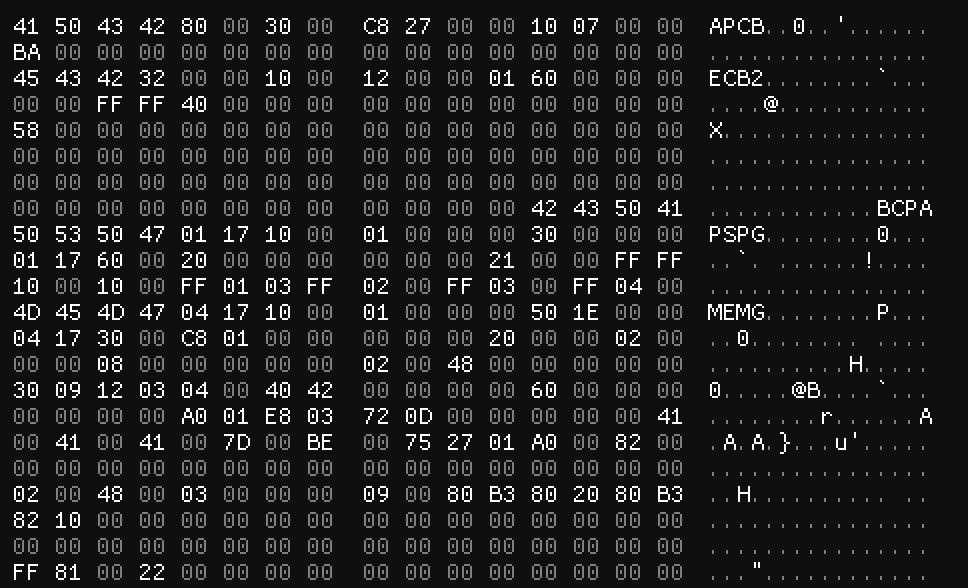
CVE-2026-31431 一大早赶了一个纯文件利用,不需要复写 su 文件,信创、异构利用稳定 github.com/Sndav/CVE-2026…
中文
Rosetta Porter 🕊️🦄
15.1K posts


@sindarin_0
#cybersecurity #infosec #cryptography #python



















As major news outlets cut off the Wayback Machine, journalists and advocacy groups are rallying to protect the Internet Archive’s vast collection of web pages. wired.com/story/the-inte…