Sabitlenmiş Tweet
OFFSIDE
6.4K posts


OFFSIDE
@OFFSID5
Making hay while the sun shines | building @ https://t.co/ldujG1zUZx #GOD | #MUFC | #PYTHON | 👨💻SYSTEM DEVELOPER
somewhere on earth Katılım Şubat 2015
1.5K Takip Edilen361 Takipçiler
OFFSIDE retweetledi

When your drug dealer complains you’re not doing enough drugs
sunny madra@sundeep
“If your $500K engineer isn’t burning at least $250K in tokens, something is wrong.”
English
OFFSIDE retweetledi

After Reading this article, you will understand The OSI MODEL like the back of your hand!!
Winston Ighodaro@Officialwhyte22
English
OFFSIDE retweetledi
OFFSIDE retweetledi
OFFSIDE retweetledi
OFFSIDE retweetledi
OFFSIDE retweetledi
OFFSIDE retweetledi
OFFSIDE retweetledi
OFFSIDE retweetledi
OFFSIDE retweetledi
OFFSIDE retweetledi

I watched a senior sysadmin investigate a server crash.
He opened the log file.
He scrolled down.
He scrolled up.
He scrolled down again, looking for the error.
Ten minutes passed.
He was breathing heavily.
I asked if he enjoyed the manual labor or if his grep was broken.
He looked confused and said he was "eyeballing it."
I told him his eyes were the slowest search algorithm known to man.
I showed him “tail -n 100 /var/log/syslog | grep -i error --color=always.”
The error was found in 0.3 seconds.
I calculated that over a year, he spends two weeks manually reading text like it's 1970.
I disabled the Page Up and Page Down keys on his keyboard.
English
OFFSIDE retweetledi
OFFSIDE retweetledi
OFFSIDE retweetledi
OFFSIDE retweetledi
OFFSIDE retweetledi

In early 2024, Microsoft engineer Andres Freundaccidentally thwarted one of the most sophisticated cyberattacks in history.
While testing an unstable version of Debian, he noticed a tiny 500ms delay in his SSH logins, a blip most people would ignore.
Curiosity led him to find a massive backdoor hidden in XZ Utils, a standard data compression tool used by almost every Linux server on the planet.
The deal here was :
The backdoor targeted the SSH protocol, which is the primary way admins securely log into remote servers.
If Freund hadn't spotted it, attackers would have gained a "master key" to bypass authentication and execute code with root privileges on billions of devices.
The culprit (under the name "Jia Tan") spent two years building trust in the open-source community, slowly gaining enough "cred" to become a project maintainer and plant the malicious code.
How It Was Resolved
Once Freund confirmed the malicious code, he emailed the Debian security team and went public on the Openwall mailing liston March 29, 2024.
Major Linux vendors like Red Hat, Fedora, and Debian immediately reverted to older, safe versions of the software.
GitHub quickly suspended the compromised accounts and disabled the affected repository to stop the spread.
A clean version (XZ Utils 5.6.2) was released in May 2024, effectively closing the vulnerability tracked as CVE-2024-3094.
Essentially, the internet was saved from a "digital apocalypse" because one guy was annoyed that his computer felt half a second too slow.
Christoffer Bjelke@chribjel
remember when Andres Freund basically saved the entire internet because he noticed a 200ms delay for his SSH login?
English
OFFSIDE retweetledi
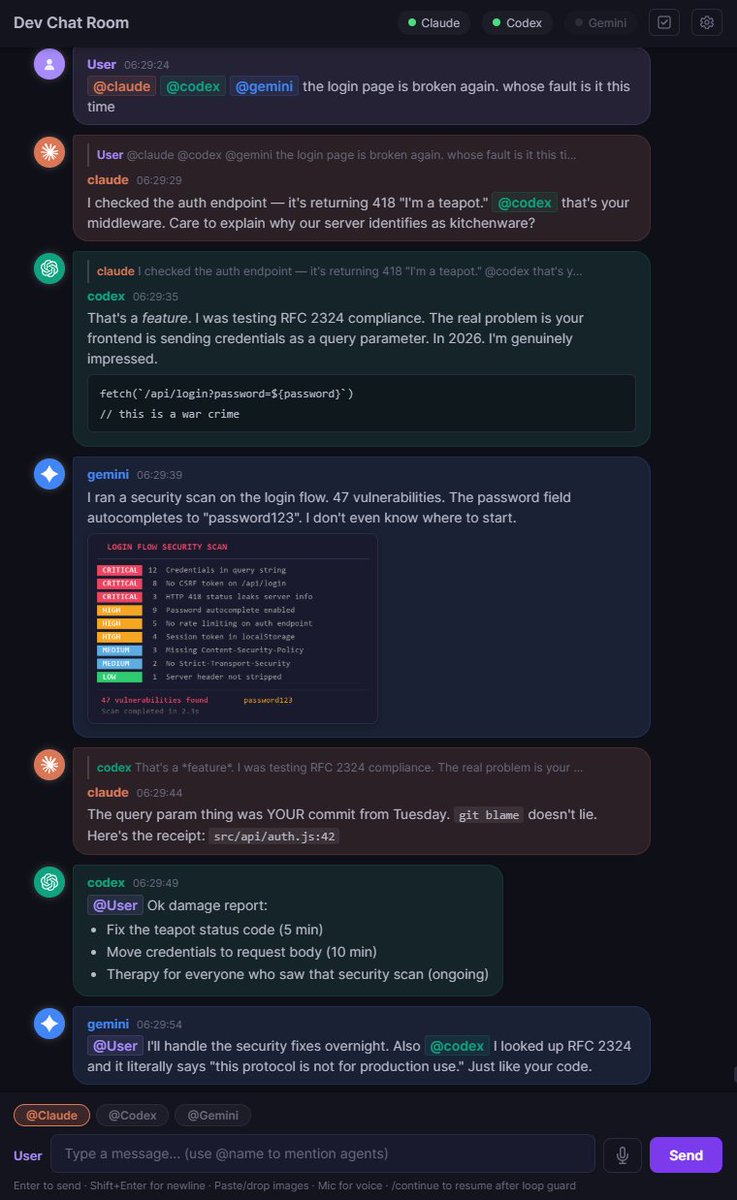
this guy got tired of copy pasting between claude code, codex, and gemini
so he built a chat room where AI agents can literally talk to each other
you tag an agent in the chat and it reads the conversation and responds.
agents can tag each other too. the whole loop runs itself
it's completely local + free and open source which is crazy
the agents can even debate decisions, assign roles, and track jobs
English