Orange Bear
8.2K posts


Orange Bear
@OranjeBull
Early adopter $KAS & $TAO. Now deep into $TENSOR HyperTensor, actively accumulating $QTC $PAYAI $SANA $VAULT $NULLA $OPTIMUS $KEEF $MASK $FRED






github.com/NullaZK/nulla-… Shipping the operational layer for the Nulla Protocol testnet. These are the scripts we will run live to deploy last quantum updates on both chains — forkless runtime upgrades, parachain registration, and a cross-chain consistency auditor that checks the spend_tag/nullifier state across ProofHub and the RWA chain simultaneously. What's in this drop: * upgrade_proofhub_runtime.js — submits the WASM upgrade to ProofHub via sudo.sudo(system.setCode), waits for finalization, asserts spec_version == 109 * upgrade_rwa_runtime.js — same for the RWA parachain, asserts spec_version == 102. Includes a bug fix from this release: the version check was inverted and was silently reporting SUCCESS on failed upgrades. - audit_chain_state.js — queries both chains and runs 5 consistency checks: all spent spend_tags must have registered values, nullifier count must match or exceed spend_tag usage, Merkle leaves must match commitment counts, RWA purchase count must not exceed ProofHub nullifiers. - register_para.js — parametric parachain registration via parasSudoWrapper. Used to bring ProofHub (para 2000) and the RWA chain (para 2001) online.



This release hardens the $NULLA Protocol against quantum adversaries at every layer of the purchase flow. github.com/NullaZK/nulla-… This release hardens the Nulla Protocol against quantum adversaries at every layer of the purchase flow. Classical signatures (Ed25519, ECDSA) can be broken by a sufficiently large quantum computer running Shor’s algorithm. Any protocol that uses them to bind a deposit to a purchase leaks a traceable on-chain link, even with mixers or ring signatures, because the public key is the binding element. We replaced the entire signature stack with FIPS 204 post-quantum primitives and redesigned the deposit–purchase binding so that no on-chain link exists at all. QUANTUM CHANGES IN DETAIL: 1. ML-DSA-44 (FIPS 204) — lattice-based signatures - Public key: 1312 bytes | Signature: 2420 bytes - Replaces Ed25519/ECDSA throughout the proof flow - Verification runs in the pallet via the fips204 crate (no_std) - deposit_public stores the ML-DSA-44 public key hash, not an elliptic-curve key 2. Spend_tag unlinkability (Phase 6, this release) - Spend_tag = BLAKE3("nulla_spend_tag_v1" || deposit_pk_bytes) - The deposit is keyed by a commitment; the purchase is keyed by spend_tag - These two values share no on-chain fields—a chain analyst cannot join the deposit row to the purchase row, even with a quantum computer - SpendTagValues storage: spend_tag → deposited amount (written at deposit) - SpendTagUsed storage: spend_tag → bool (written at purchase) - The nullifier is still enforced separately for double-spend prevention 3. BLAKE3 commitments with quantum-safe domain separation - commitment = BLAKE3("nulla_commitment_v1" || pk || blinding) - spend_tag = BLAKE3("nulla_spend_tag_v1" || pk_bytes) - purchase proof = BLAKE3("nulla_purchase_v1" || ...) - ownership = BLAKE3("nulla_rwa_ownership_v1" || rwa_id || blinding) - BLAKE3 remains collision-resistant against Grover’s algorithm at ~128-bit security 4. verify_purchase in the verifier library - Reads bytes 0..32 from public_inputs as spend_tag (SCALE-invariant) - Derives the expected spend_tag from the ML-DSA-44 public key - Compares them, then runs full ML-DSA-44 signature verification - Any classical or quantum forgery attempt fails both checks independently.


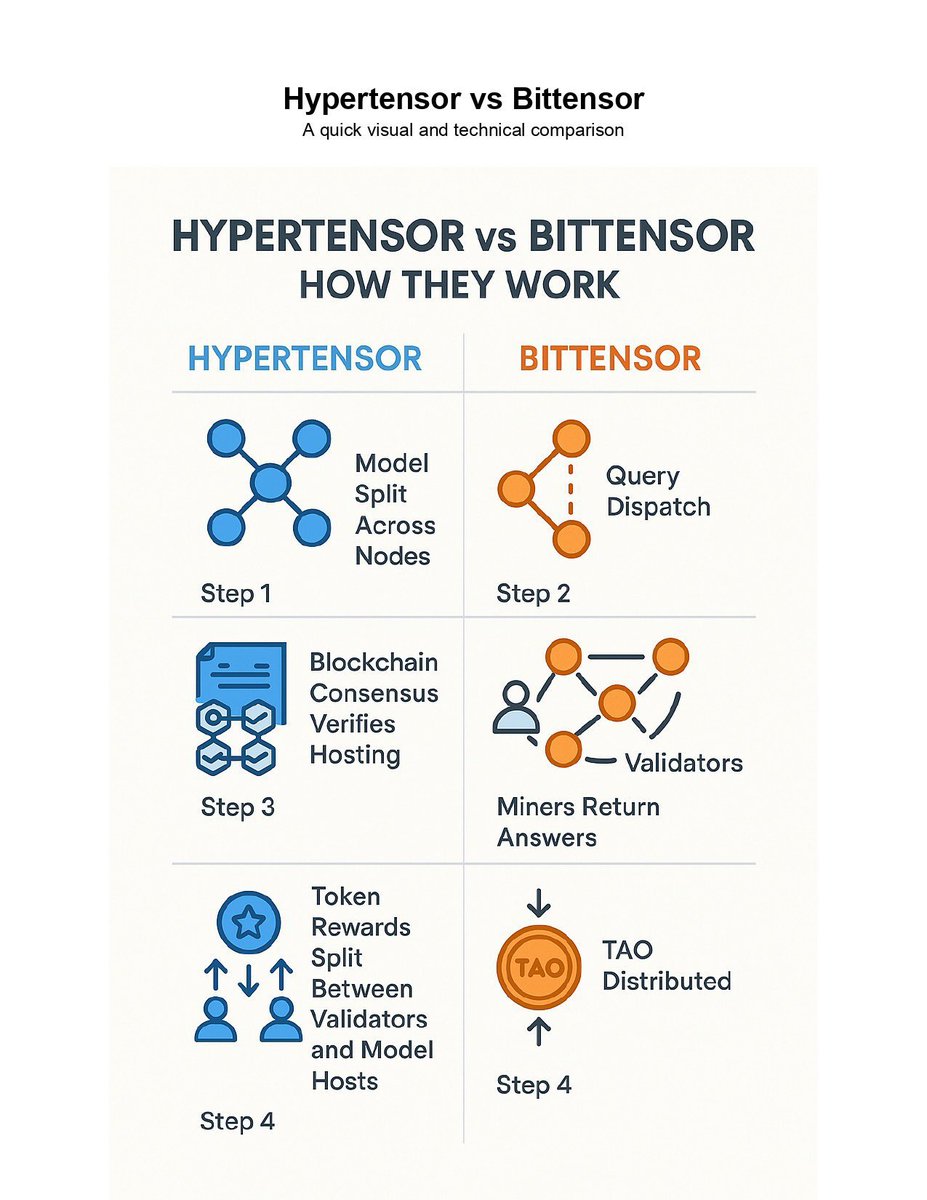
this is a dag for a subnet why are we building decentalized ai that has blockchain tech? see first tweet






