Cheatcode
2.3K posts


Cheatcode
@Oxcheatcode
I'm obsessed with data and tech security. Founder @TowerExchange || Co-founder @CentronBot
║▌║█║▌│║▌║▌█ Katılım Ekim 2022
175 Takip Edilen445 Takipçiler
Sabitlenmiş Tweet

𝐁𝐮𝐠 𝐑𝐞𝐩𝐨𝐫𝐭 𝐃𝐚𝐲 35
State-changing functions should actually change state. Otherwise, they just waste gas and confuse users.
VeChain’s delegation exit logic allowed repeated no-op exit requests even after exit had already been scheduled.
𝗧𝗶𝘁𝗹𝗲: Repeated Request Exit Calls
𝗦𝗲𝘃𝗲𝗿𝗶𝘁𝘆: Info
𝗦𝗼𝘂𝗿𝗰𝗲: @hackenclub
🔗: hacken.io/audits/vechain…
𝗩𝘂𝗹𝗻𝗲𝗿𝗮𝗯𝗶𝗹𝗶𝘁𝘆 𝗗𝗲𝘁𝗮𝗶𝗹𝘀:
The `requestDelegationExit()` function can be called multiple times after delegation exit has already been scheduled.
Repeated calls:
• Do not modify state
• Return `true` instead of reverting
• Waste user gas unnecessarily
While low impact, this creates inconsistent protocol behavior and may confuse users.
𝗜𝗺𝗽𝗮𝗰𝘁:
• Unnecessary gas consumption
• Potential user confusion
• Inconsistent contract behavior
𝗥𝗲𝗰𝗼𝗺𝗺𝗲𝗻𝗱𝗲𝗱 𝗠𝗶𝘁𝗶𝗴𝗮𝘁𝗶𝗼𝗻:
• Add validation preventing redundant exit requests
• Revert when delegation exit is already scheduled
• Only allow calls that produce meaningful state changes
𝗥𝗲𝘀𝗼𝗹𝘂𝘁𝗶𝗼𝗻: Fixed (redundant exit requests now prevented)
#onebugperday keeps the hacker away.
𝑺𝒆𝒄𝒖𝒓𝒊𝒕𝒚 𝒊𝒔 𝒔𝒕𝒊𝒍𝒍 𝒕𝒉𝒆 𝒘𝒆𝒂𝒌𝒆𝒔𝒕 𝒍𝒊𝒏𝒌!

English
Cheatcode retweetledi

#4 towerexchange by @Oxcheatcode
quite similar to starlight
tower exchange is also a DeFi protocol
where you can interact swiftly on arc includes a swap feature, bridge, an AI agent and DCA agents for recurring buys..
hey you also need an invite code to get in
but check them out here
x.com/TowerExchange/…
English

@Oxcheatcode @wfaquarius gm gm Cheatcode 🤝🏽
Respect ya ❤️
Just followed you
English

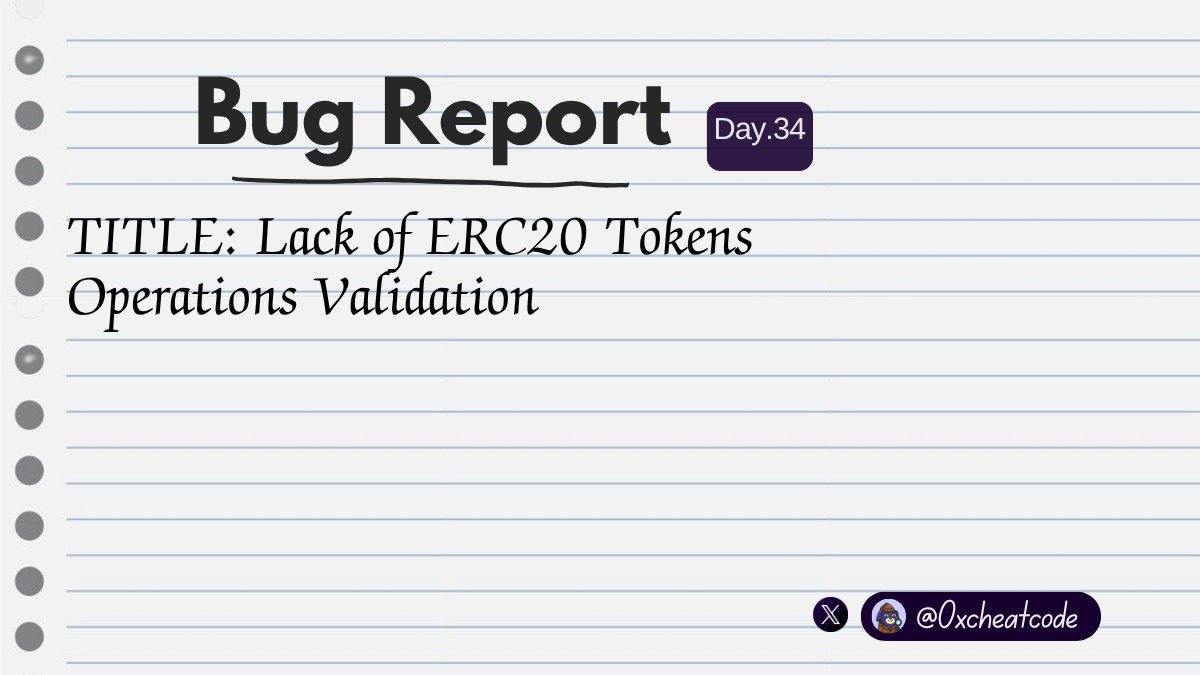
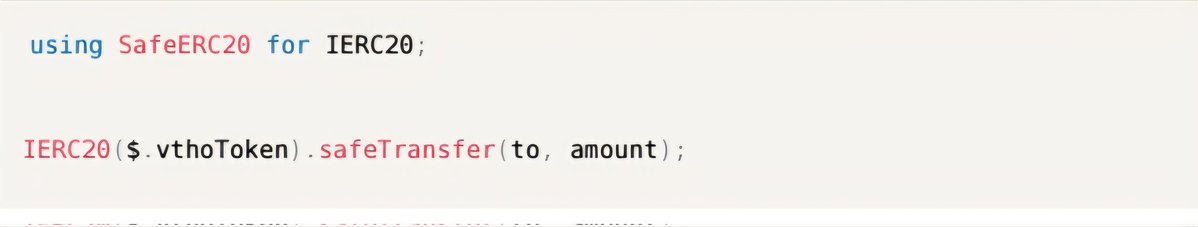
𝐁𝐮𝐠 𝐑𝐞𝐩𝐨𝐫𝐭 𝐃𝐚𝐲 34
Not every ERC20 token behaves as expected and assuming they do can break your protocol.
VeChain’s Stargate contracts manually handled token transfers instead of using SafeERC20 safeguards.
𝗧𝗶𝘁𝗹𝗲: Lack of ERC20 Operation Success Validation
𝗦𝗲𝘃𝗲𝗿𝗶𝘁𝘆: Info
𝗦𝗼𝘂𝗿𝗰𝗲: @hackenclub
🔗: hacken.io/audits/vechain…
𝗩𝘂𝗹𝗻𝗲𝗿𝗮𝗯𝗶𝗹𝗶𝘁𝘆 𝗗𝗲𝘁𝗮𝗶𝗹𝘀:
The protocol manually validates ERC20 `transfer()` return values when sending VTHO rewards.
Problem:
Not all ERC20 tokens strictly return a boolean value.
If a non-standard token is used, transfers may revert unexpectedly and disrupt reward claims.
𝗜𝗺𝗽𝗮𝗰𝘁:
• Potential denial of service during reward claims
• Reduced compatibility with non-standard ERC20 tokens
• Fragile token transfer assumptions
𝗥𝗲𝗰𝗼𝗺𝗺𝗲𝗻𝗱𝗲𝗱 𝗠𝗶𝘁𝗶𝗴𝗮𝘁𝗶𝗼𝗻:
• Use OpenZeppelin’s `SafeERC20` library
• Replace raw `transfer()` calls with `safeTransfer()`
• Standardize token transfer handling across the protocol
𝗥𝗲𝘀𝗼𝗹𝘂𝘁𝗶𝗼𝗻: Fixed (SafeERC20 implemented for token transfers)
#onebugperday keeps the hacker away.
𝑺𝒆𝒄𝒖𝒓𝒊𝒕𝒚 𝒊𝒔 𝒔𝒕𝒊𝒍𝒍 𝒕𝒉𝒆 𝒘𝒆𝒂𝒌𝒆𝒔𝒕 𝒍𝒊𝒏𝒌!
English
Cheatcode retweetledi

𝐁𝐮𝐠 𝐑𝐞𝐩𝐨𝐫𝐭 𝐃𝐚𝐲 33
Upgradeable contracts are only as safe as their initialization path.
VeChain’s StargateNFT skipped initializing some inherited upgradeable modules, creating future compatibility risk.
𝗧𝗶𝘁𝗹𝗲: Lack of Upgradeable Contracts Initialization
𝗦𝗲𝘃𝗲𝗿𝗶𝘁𝘆: Info
𝗦𝗼𝘂𝗿𝗰𝗲: @hackenclub
🔗: hacken.io/audits/vechain…
𝗩𝘂𝗹𝗻𝗲𝗿𝗮𝗯𝗶𝗹𝗶𝘁𝘆 𝗗𝗲𝘁𝗮𝗶𝗹𝘀:
The `StargateNFT` contract inherits multiple upgradeable OpenZeppelin modules.
However, its `initialize()` function failed to call:
• `__ReentrancyGuard_init()`
• `__ERC721Enumerable_init()`
While this does not currently break functionality, skipped initializers create maintenance and upgradeability risk if inherited logic changes in future releases.
𝗜𝗺𝗽𝗮𝗰𝘁:
• Violates upgradeable contract best practices
• Introduces future compatibility risk
• May cause unexpected issues after dependency upgrades
𝗥𝗲𝗰𝗼𝗺𝗺𝗲𝗻𝗱𝗲𝗱 𝗠𝗶𝘁𝗶𝗴𝗮𝘁𝗶𝗼𝗻:
• Invoke all inherited upgradeable initializers during setup
• Ensure initialization chain fully matches inheritance tree
• Follow OpenZeppelin upgradeable contract patterns strictly
𝗥𝗲𝘀𝗼𝗹𝘂𝘁𝗶𝗼𝗻: Fixed (missing initializers added)
#onebugperday keeps the hacker away.
𝑺𝒆𝒄𝒖𝒓𝒊𝒕𝒚 𝒊𝒔 𝒔𝒕𝒊𝒍𝒍 𝒕𝒉𝒆 𝒘𝒆𝒂𝒌𝒆𝒔𝒕 𝒍𝒊𝒏𝒌!
English
Cheatcode retweetledi


@Oxcheatcode Oh if you have like 30 or 20 something minutes left you can always increase the time with the "+" sign at the bottom of the VM
English

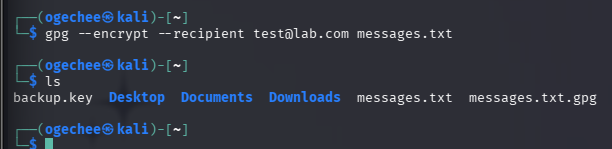
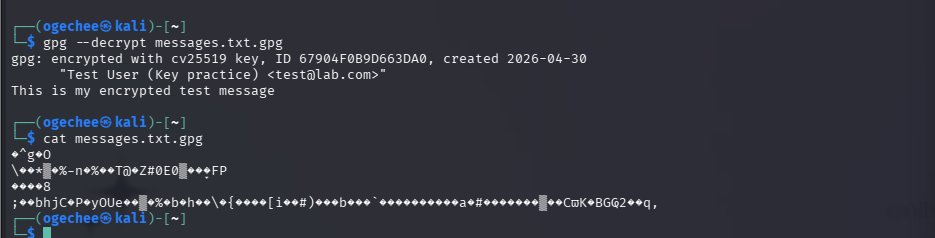
I recently finished the Public Key Cryptography room on TryHackMe, and I decided to practice what I learnt about GPG.
GPG stands for GNU Privacy Guard. It's a free, open-source tool that lets you encrypt and decrypt data using public key cryptography.
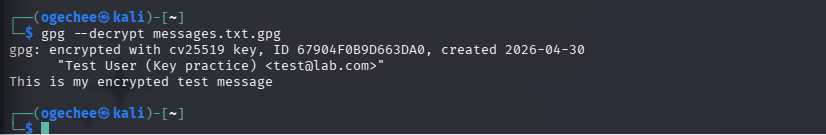
I ran a full GPG lab on my Kali machine. Generated my own ECC key pair (Curve 25519), encrypted a message to myself, decrypted it successfully, then deleted the keys entirely to simulate switching to a new machine, restored from backup, and decrypted the same file again.
That last part is important because if your private key is gone and you never backed it up, every encrypted file you ever received is permanently unreadable. No recovery.
#Cybersecurity #LearningInPublic

English

@Oxcheatcode First of all, I don't post all in real time so I wouldn't say I go through these rooms in a short time. I actually enjoy learning about cybersecurity so I guess that helps with consistency.
English

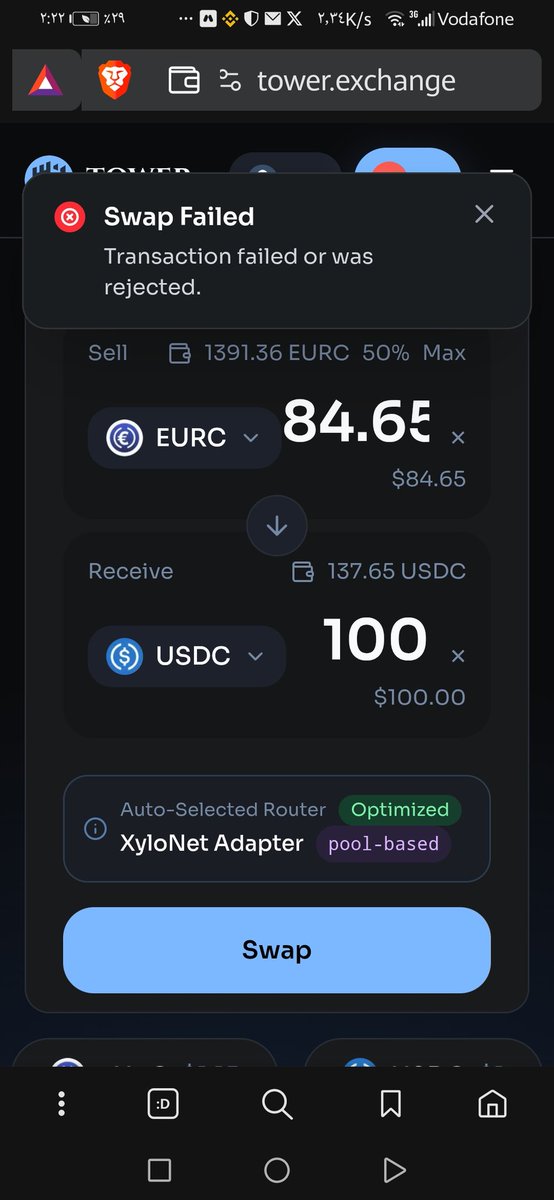
@0sgamaL @TowerExchange This is probably due to network connection or arc rpc endpoint failure.
Kindly Check the discord for debugging tips
English

𝐁𝐮𝐠 𝐑𝐞𝐩𝐨𝐫𝐭 𝐃𝐚𝐲 32
Even error handling has gas costs and verbose revert strings can quietly bloat your contracts.
VeChain’s NodeManagement contracts used revert strings where custom errors would be more efficient.
𝗧𝗶𝘁𝗹𝗲: Revert Messages Optimization
𝗦𝗲𝘃𝗲𝗿𝗶𝘁𝘆: Info
𝗦𝗼𝘂𝗿𝗰𝗲: @hackenclub
🔗: hacken.io/audits/vechain…
𝗩𝘂𝗹𝗻𝗲𝗿𝗮𝗯𝗶𝗹𝗶𝘁𝘆 𝗗𝗲𝘁𝗮𝗶𝗹𝘀:
The NodeManagement contracts use revert string messages for validation failures.
Since Solidity 0.8.4, custom errors provide a more gas-efficient alternative.
Result:
• Larger contract bytecode
• Higher deployment costs
• Less efficient revert handling
𝗜𝗺𝗽𝗮𝗰𝘁:
• Increased deployment gas costs
• Slight runtime inefficiency
• Reduced bytecode optimization
𝗥𝗲𝗰𝗼𝗺𝗺𝗲𝗻𝗱𝗲𝗱 𝗠𝗶𝘁𝗶𝗴𝗮𝘁𝗶𝗼𝗻:
• Replace revert strings with custom errors
• Use semantically meaningful error definitions
• Reduce bytecode size and gas overhead
𝗥𝗲𝘀𝗼𝗹𝘂𝘁𝗶𝗼𝗻: Fixed (custom errors implemented)
#onebugperday keeps the hacker away.
𝑺𝒆𝒄𝒖𝒓𝒊𝒕𝒚 𝒊𝒔 𝒔𝒕𝒊𝒍𝒍 𝒕𝒉𝒆 𝒘𝒆𝒂𝒌𝒆𝒔𝒕 𝒍𝒊𝒏𝒌!

English