Positive Technologies Global
1.4K posts


Positive Technologies Global
@PTsecurity_EN
Embrace any digitalization challenge—we'll secure your cyber-resilience
Katılım Nisan 2015
873 Takip Edilen3.6K Takipçiler

1/4
How did the global threat landscape shift in 2025, and what does it mean for defense strategy in 2026?
Here are three shifts to watch. ⤵️
#PTCyberTrends2026 #cybersecurity #threatintel

English

It’s been quite a while after we wrapped up #PHtalks in Kuala Lumpur 🇲🇾 Time to say a few words:
Damn amazing everything went over there! Thank you, community ❤️




English

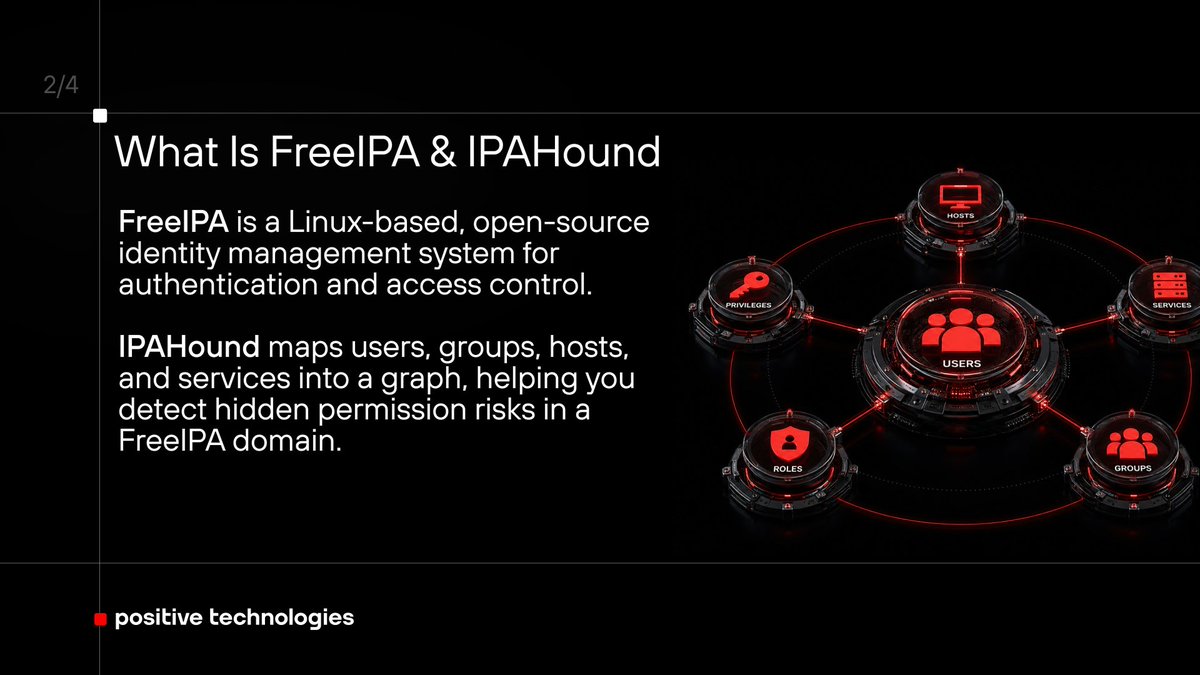
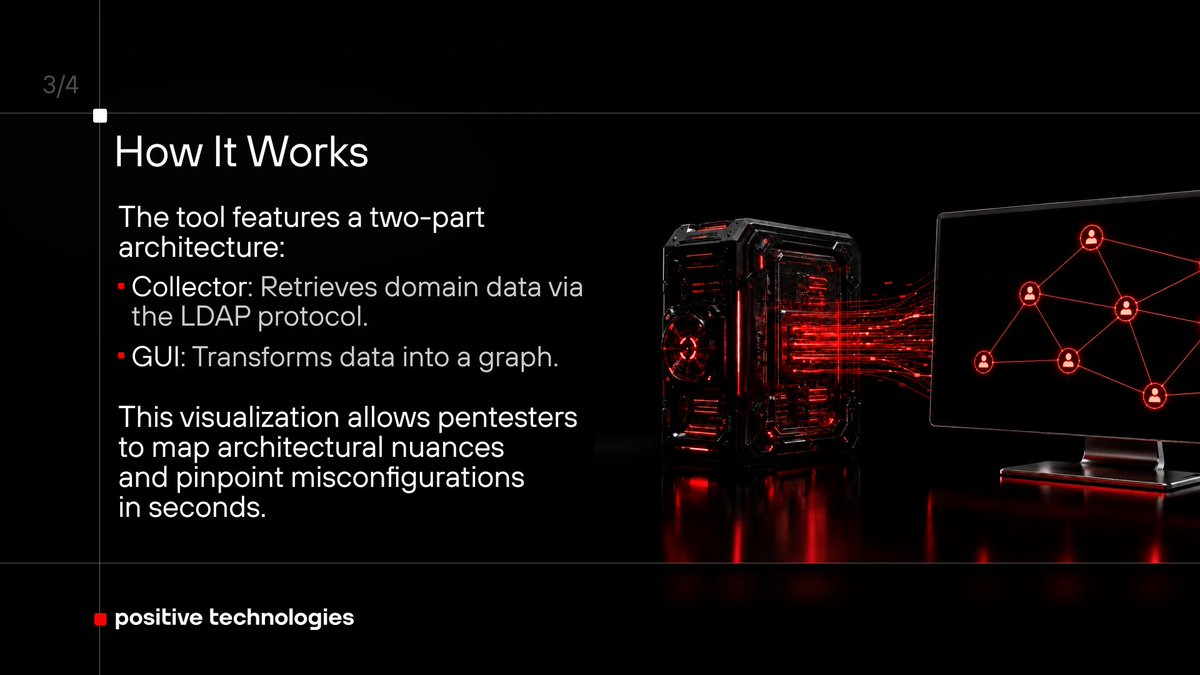
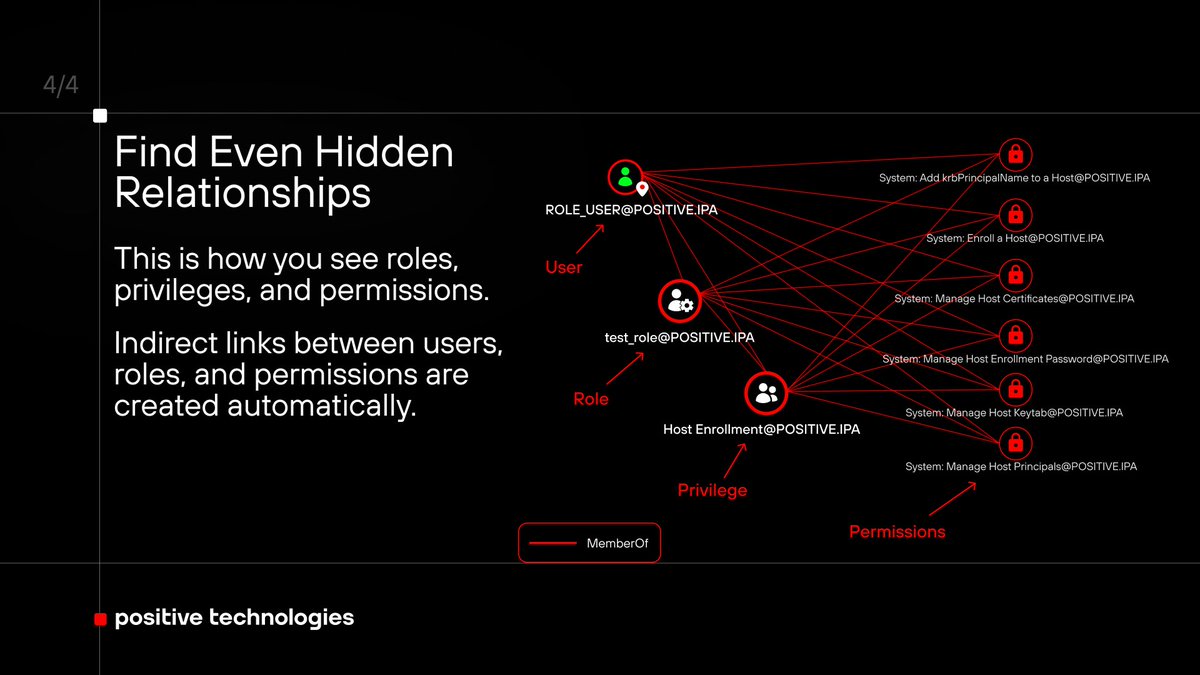
BloodHound, but for FreeIPA? Done ✅ PT SWARM built IPAHound. It graphs your FreeIPA domain so you can finally see the hidden permission misconfigs attackersexploit.
Details and GitHub: swarm.ptsecurity.com/thinking-in-gr…
English

Thank you @PTsecurity_EN & @amoshkov for hosting #PHtalks KL! It’s been ages since I’ve had the chance to attend a security conference in Malaysia. It’s such a wonderful opportunity to reconnect with old friends and meet new ones. The content was fantastic. I’m really hoping to see more events like this in Malaysia. Also, thanks @yappare for… 🤐🤐

English

@AmmarAshshiddi1 hope you’ll get the chance to join us at one of the next #PHTalks
English

kpn yh bisa dateng ke event kyk gini =w=
Positive Technologies Global@PTsecurity_EN
Kuala Lumpur showed up. 🇲🇾 379 people joined #PHTalks Kuala Lumpur for a day of talks, questions, and real conversations that kept going long after the stage went quiet. Thanks, KL. See you at the next stop 🚀
Indonesia

@unshadow97 gotcha! next time, we’ll try to catch you
English

Kuala Lumpur showed up. 🇲🇾
379 people joined #PHTalks Kuala Lumpur for a day of talks, questions, and real conversations that kept going long after the stage went quiet.
Thanks, KL. See you at the next stop 🚀
English

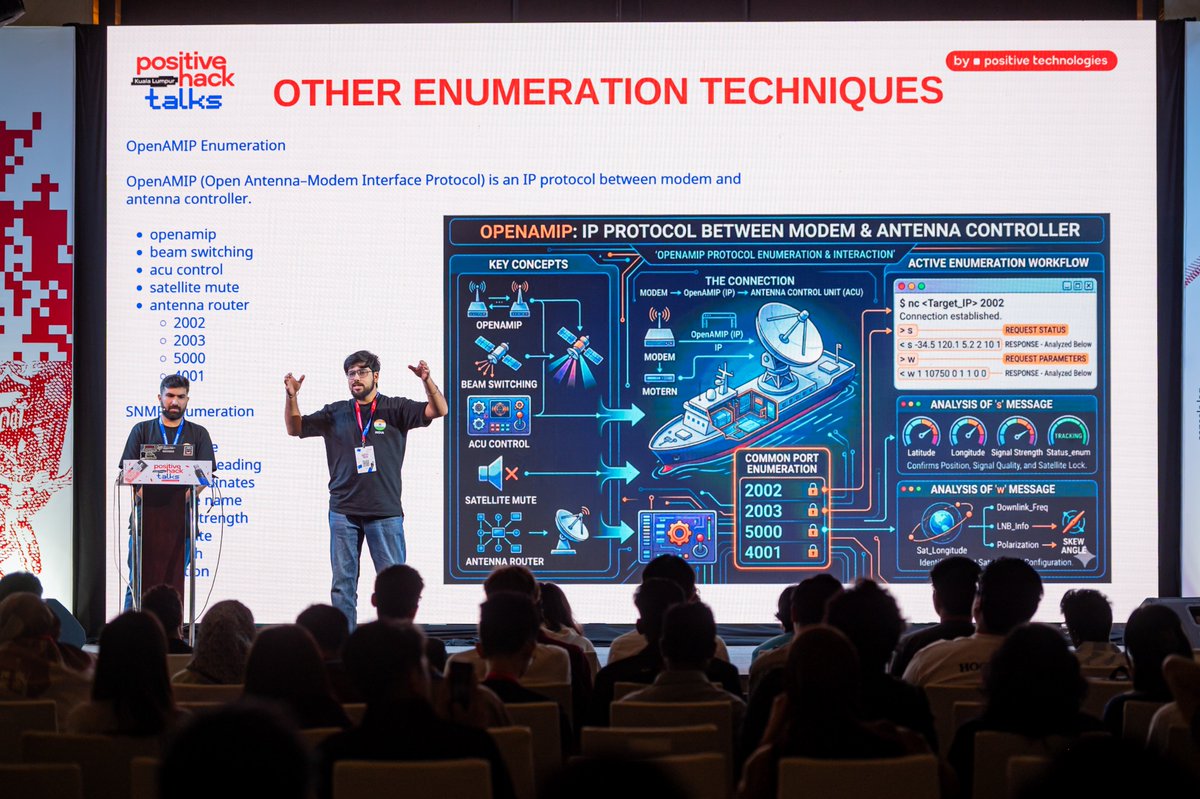
The slide said “nothing,” but Sagar Tiwari and Shubham Kumar clearly gave the room plenty to think about. Dead in the Water at #PHTalks Kuala Lumpur was a strong OSINT session on exposed VSAT terminals, vessel tracking, and what still leaks when AIS goes dark.



English

Great to have @haider_kabibo at #PHTalks Kuala Lumpur with PhantomRPC: A New Privilege Escalation Flaw in Windows RPC. A dense, highly technical session that clearly resonated with the room.



English

With Kernel-Hack-Drill Masterclass, @a13xp0p0v took #PHTalks Kuala Lumpur straight to the low-level details. A strong technical session for people interested in Linux kernel security.



English

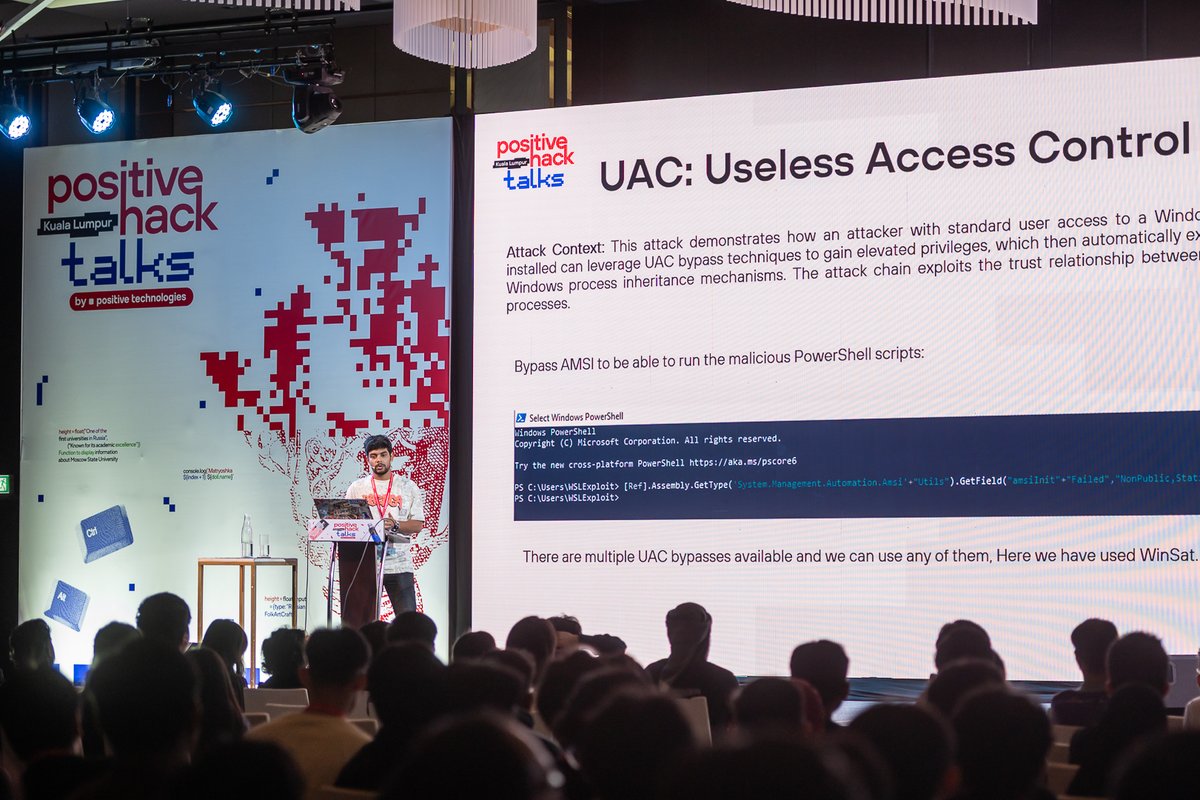
Appreciate Aditya Singh joining #PHTalks Kuala Lumpur with Trojan Penguin in the Windows: Advanced Attack Vectors Through WSL. A technical and very well-received talk on WSL-based attack vectors, evasion, and detection gaps.



English

Dissecting Android RASP: A Practical Reversing Guide by Akshay Jain was one of those talks that went straight to the technical core. Deep, practical, and very well received at #PHTalks Kuala Lumpur.




English

Thank you, @vicevirus2, for joining #PHTalks Kuala Lumpur with Spray, Pray, Validate: Lessons from AI-assisted Vulnerability Research. Insightful, practical, and refreshingly honest about what AI can and cannot do in real vulnerability research.



English

Turning off AIS does not make a ship disappear. Dead in the Water explores how open-source methods can still reveal vessel movement when AIS goes dark. At #PHTalks Kuala Lumpur 🇲🇾: phtalks.ptsecurity.com

English

Copy Fail reminds us: kernel exploits don’t always look dramatic. A controlled 4-byte write into the Linux page cache can lead to local privilege escalation. PT Sandbox detected an exploit during software analysis of an Astra Linux image. Details: @ptescalator

English