Sabitlenmiş Tweet
Sayaan Alam
2.5K posts


Sayaan Alam
@ehsayaan
Security Researcher, innovating next generation of cybersecurity | Red Teamer | Bug Bounty Hunter
Katılım Nisan 2017
981 Takip Edilen9.4K Takipçiler


@garrytan cybersecurity peeps have been pulling you lately, what’s up? Is it a sign, hahaha🤣
English

You’re not gonna believe this guys but I have found my new favorite X account 👀
Philo Groves@PhiloGroves
just cut a 7k loc file down to ~300
English

@HatforceSec @garrytan @ycombinator Better way is to make a policy for all of those startups to have a responsible disclosure policy for their product where they could receive reports individually :)
English

@HatforceSec @garrytan @ycombinator I think its not just an operation but a very crucial responsibility. Collecting vulnerabilities on behalf of 100s of companies makes it very complex to manage/track those vulnerabilities especially when you have to communicate between different teams.
English

Hey @garrytan @ycombinator how can i report serious security vulnerabilities in YCombinator? Do you guys have a bug bounty program?
English

Flew to #tokyo for IPC. left with 6 figures and 3 most impactful bugs across 3 services. couldn’t have done it without @wld_basha

English

@rauchg @infinitelogins I can’t DM you, please text. I have something that might be very helpful for you at the moment.
English

Here's my update to the broader community about the ongoing incident investigation. I want to give you the rundown of the situation directly.
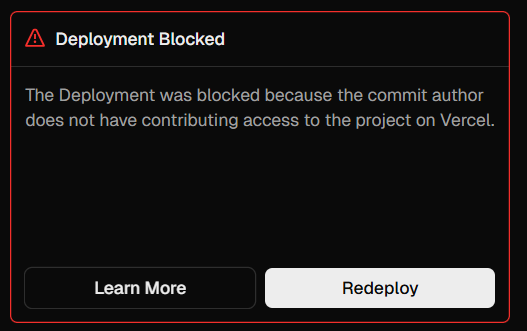
A Vercel employee got compromised via the breach of an AI platform customer called Context.ai that he was using. The details are being fully investigated.
Through a series of maneuvers that escalated from our colleague’s compromised Vercel Google Workspace account, the attacker got further access to Vercel environments.
Vercel stores all customer environment variables fully encrypted at rest. We have numerous defense-in-depth mechanisms to protect core systems and customer data. We do have a capability however to designate environment variables as “non-sensitive”. Unfortunately, the attacker got further access through their enumeration.
We believe the attacking group to be highly sophisticated and, I strongly suspect, significantly accelerated by AI. They moved with surprising velocity and in-depth understanding of Vercel.
At the moment, we believe the number of customers with security impact to be quite limited. We’ve reached out with utmost priority to the ones we have concerns about. All of our focus right now is on investigation, communication to customers, enhancement of security measures, and sanitization of our environments. We’ve deployed extensive protection measures and monitoring. We’ve analyzed our supply chain, ensuring Next.js, Turbopack, and our many open source projects remain safe for our community.
The recommendation for all Vercel customers is to follow the Security Bulletin closely (vercel.com/kb/bulletin/ve…). My advice to everyone is to follow the best practices of security response: secret rotation, monitoring access to your Vercel environments and linked services, and ensuring the proper use of the sensitive env variables feature.
In response to this, and to aid in the improvement of all of our customers’ security postures, we’ve already rolled out new capabilities in the dashboard, including an overview page of environment variables, and a better user interface for sensitive env var creation and management. As always, I’m totally open to your feedback.
We’re working with elite cybersecurity firms, industry peers, and law enforcement. We’ve reached out to Context to assist in understanding the full scale of the incident, in an effort to protect other organizations and the broader internet. I also want to thank the Google Mandiant team for their active engagement and assistance.
It’s my mission to turn this attack into the most formidable security response imaginable. It’s always been a top priority for me. Vercel employs some of the most dedicated security researchers and security-minded engineers in the world. I commit to keeping you updated and rolling out extensive improvements and defenses so you, our customers and community, can have the peace of mind that Vercel always has your back.
English
Sayaan Alam retweetledi

Send a fax as anyone. Upload photos to any frame. @ehsayaan shows how email-driven systems turn sender addresses into broken authorization. Hear the case studies at #PHTalks Kuala Lumpur 🇲🇾: phtalks.ptsecurity.com

English

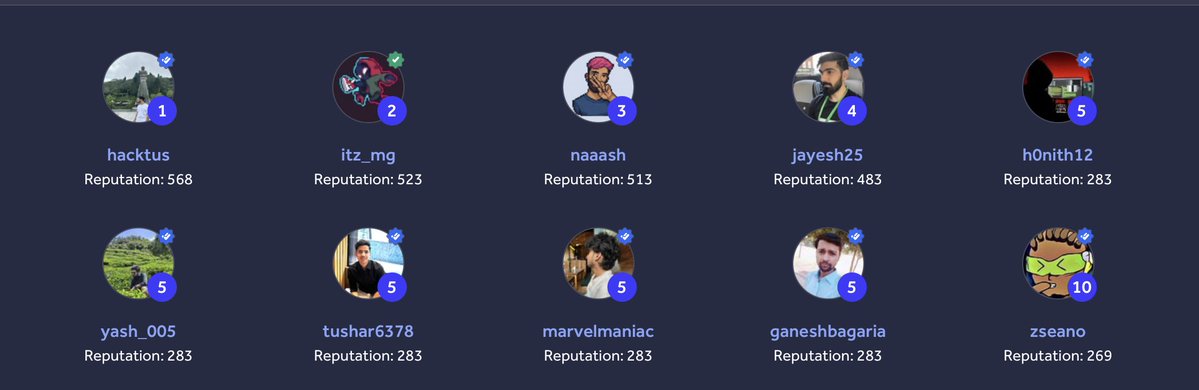
Had a really fun time hacking @amazon in Goa 🌴
Teamed up with @H4cktus, @Jayesh25 and @itz_mg_ and we ended up 1st on the leaderboard 😅
Picked up a bunch of bonuses too:
🏆 Pwnership: Eventwide Most Impactful Report
🧠 Dive Deep: Most Creative Bug
💥 Most Impactful Issue on a Specific Asset
🔥 Most # of Critical Issues on a Specific Asset
🎤 Show & Tell
Big thanks to @Hacker0x01 for organizing this 🙌
Photo dump from the chaos 👇

English
Sayaan Alam retweetledi

New episode of WE'RE IN!
Discover @ehsayaan's journey from teenage hacker to the SRT Acropolis.
🎧Listen on Spotify: open.spotify.com/episode/2OihA8…
#EthicalHacking #Pentest #SynackRedTeam #Cybersecurity

English

Her first week at Lupin & Holmes ? Garance compromised an npm package with 40M weekly downloads 🔥
Depi flagged a dangerous workflow in @ img/colour. She turned Dependabot into the trigger, got the workflow to run, and reached package write access.
40M weekly downloads. Week one. Garance rocks 🤟
landh.tech/blog/20260402-…

English

Around 7 years ago, I started in security with pure curiosity and a lot of trial & error.
Today, I got to share that journey on a podcast with @SynackRedTeam 🎙️
Grateful for every opportunity that shaped this path.
🎙️Listen on Spotify: open.spotify.com/episode/2OihA8…

English

@ehsayaan Dear Sayaan! That is not the experience we want you to have with us. Please be assured that I have highlighted the issue, and you will receive an update from us at the earliest. -OS twitter.com/messages/compo…
English

@rauchg @tech_savvy_guy_ @vercel You should change that setting to allow everyone @rauchg since you are always expecting some DMs, hahaha!
English