PalachSec
75 posts


PalachSec
@PalachSec
Mato elas antes que elas me matem. https://t.co/N5pPDSfYMD #m0z1ll4s
Katılım Ekim 2014
46 Takip Edilen29 Takipçiler

@PalachSec @m0z1ll4s cara, nao fale assim de mim, eu fui da ratos humanos, posso destruir todos vocês. ☠☠☠☠☠
Português
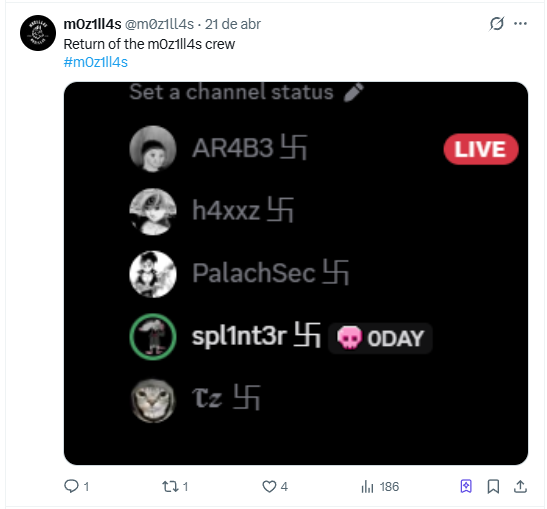
PalachSec retweetledi
PalachSec retweetledi
PalachSec retweetledi

🚨 ALERTA CRÍTICO
Uma falha (CVE-2026-41940) no cPanel permite bypass de autenticação
➡️ Login sem senha
➡️ Acesso total ao servidor
➡️ Já sendo explorada (zero-day)
Isso afeta boa parte da internet.
Se você usa cPanel… atualiza AGORA.
labs.watchtowr.com/the-internet-i…
Português
PalachSec retweetledi

🚨 BREACH ALERT | 🔴 CRITICAL 🇧🇷
Oi Telecom (🌐 oi.com.br) has been breached.
📊 Records: 28.1 Million+
🎭 Actor: m0z1ll4s
📁 Data: Telecom subscriber data (CPF, address, phone, contract details)
🗓 Date:26 Apr 2026
⚠️ Severity: CRITICAL
What was leaked:
→ Full names + CPF (Brazilian ID)
→ Phone numbers & telecom line details
→ Full addresses (city, state, ZIP)
→ Contract & service status data
⚠️ Massive national-scale exposure
⚠️ Highly sensitive identity + telecom data
⚠️ Claim currently unverified
If you are an Oi user, stay alert for SIM swap, phishing, and identity fraud attempts.
#DataBreach #Brazil #CyberSecurity #Telecom #DataLeak #Privacy #Infosec #ThreatIntel #OSINT #CyberAlert

English
PalachSec retweetledi

My group, m0z1ll4s, and I exploited a vulnerability in PHP 7.4.33 to hack into the system of another Brazilian political party and obtained over 958,000 confidential records.
BF:breachforums.rs/Thread-DOCUMEN…
Download:gofile.io/d/oN09Wj
@VECERTRadar @DailyDarkWeb
#DataBreach

English
PalachSec retweetledi

🚨 STATE OF CYBER-INSECURITY: BRAZIL 2026 🇧🇷
The cybersecurity landscape in Brazil reached critical levels during the first four months of 2026. Government and financial infrastructure are under constant siege.
👥 TOP THREAT ACTORS (Active April 2026)
👑 wh6ami | 7 Incidents (Targeting Gov infrastructure) 🇧🇷
⚡ ByteToBreach | 3 Incidents (Data extraction expert)
🐱 Spirigatito | 3 Incidents (Government focus)
🛠️ m0z1ll4s | 2 Incidents (Banking & Telecom)
💀 Buddha | 2 Incidents (Massive citizen databases)
📊 Key Statistics (January - April 2026)
SMTP Black Market: 1,752 Brazilian corporate email accounts have been identified for sale, intended for phishing and ransomware campaigns.
Compromised Credentials: A total of 3,528 high-profile credentials have been distributed across hacking forums from 2023 to date (April 2026).
Data Volume: Massive leaks exceeding 15.4 TB of sensitive information during this period alone.
📅 TIMELINE: CRITICAL APRIL LEAKS 🇧🇷
Apr 26: 🏦 Banking Sector: 2.3M records exposed (RubiconH4ck).
Apr 26: 📱 Telecom (Oi): Breach at ri.oi.com.br (m0z1ll4s).
Apr 19: 🗺️ Pernambuco DB: Data on 9 million inhabitants leaked.
Apr 18: 📮 Correios (ECT): Massive leak of blueprints and financial records.
Apr 13: 📂 Data Dump: 15.4 TB of miscellaneous Brazilian databases.
Apr 09: 🛡️ Serasa: 223M citizens exposed (1.8 TB full dump).
📈 Timeline and Trends
Activity shows exponential growth. While the average in March was one post per day, during the second half of April, the frequency has risen to 3–4 major incidents daily, primarily affecting .gov.br portals.
⚙️ METHODOLOGY: HOW ARE THEY GAINING ACCESS? 🔍
An analysis of incidents in 2026 reveals three predominant attack vectors:
Infostealer Log Abuse ☣️
The sale of 1,752 Brazilian corporate email accounts on illicit SMTP marketplaces is no coincidence. Attackers are purchasing "logs" (active sessions and credentials) obtained from malware such as RedLine or Lumma to bypass MFA and access internal networks without raising suspicion.
Exploitation of Basic Vulnerabilities 🔓
Many of the 3,528 credentials distributed since 2023 stem from a lack of patching on exposed services (VPNs, RDP). Threat actors are reusing compromised passwords (Credential Stuffing) on systems that have not rotated their keys in years.
API Vulnerabilities (IDOR) 🔗
Widespread exploitation of IDOR (Insecure Direct Object Reference) flaws has been detected. Attackers manipulate identifiers within the APIs of government portals and financial applications to exfiltrate records belonging to other users en masse, without requiring administrative privileges.
#CyberSecurity #ThreatIntel #Brazil #DataBreach #InfoSec #CyberCrime


English
PalachSec retweetledi

🚨 CRITICAL CYBER THREAT ALERT: TELECOMMUNICATIONS DATA LEAK – OI BRASIL 🇧🇷📞🔓
A high-impact post has been detected on Deep Web forums, attributed to the threat group "m0z1ll4s." The attackers claim to have compromised the systems of Oi—one of the largest telecommunications companies in Brazil—exfiltrating a massive customer database.
🏢 Affected Entity: Oi (Telemar Norte Leste S.A. - Brazil).
👤 Threat Actor: m0z1ll4s Crew (spl1nt3r, AR4B3, PalachSec, h4xxz, T$).
📂 Leak Volume: 28,101,382 records (approx. 6.58 GB of data).
🎯 Target: ri.oi.com.br (Investor Relations) and customer databases.
📅 Publication Date: April 26, 2026.
📊 Breach Scope (Exposed PII)
The provided sample reveals a complete exposure of customers' Personally Identifiable Information (PII), primarily from Post-paid and Retail plans:
Identity: Full name and CPF (Individual Taxpayer Registry) number.
Physical Location: Full address (Street, number, neighborhood, city, state, and CEP/Postal Code).
Telecommunications: Area code (DDD), mobile phone number, and line type.
Operational Data: Line status (Active/Blocked), business unit, activation date, and contract date (with records dating from 2017 to 2020). ⚠️ Risk Analysis (VECERT Intelligence)
Possible Data "Recycling": Important Note: Although the publication date is April 2026, the contract dates found in the sample (2017–2020) suggest that this may be a repackaged legacy leak or a historical database. Nevertheless, the volume of 28 million records remains a critical asset for fraud campaigns.
Social Engineering (Vishing/Smishing): By possessing names, CPF numbers, and exact addresses, criminals can place fraudulent calls—impersonating Oi technical support—to solicit payments or access codes.
🛡️ Immediate Response Recommendations
🔒 Integrity Verification: Oi administrators are urged to audit the subdomain ri.oi.com.br and their database servers to rule out any persistent intrusion.
🔑 CPF Monitoring: Brazilian citizens should utilize the Central Bank's "Registrato" service to monitor for any unauthorized account openings or credit applications made using their personal data.
Monitor: analyzer.vecert.io
🛡️ "The leak of 28 million records from a telecom provider—even if the data is historical—provides the perfect raw material for identity fraud in Brazil. VECERT is issuing this preventive alert while the full validity of the data is being confirmed."
#CyberSecurity #Brazil #OiTelecom #DataBreach #m0z1ll4s #LGPD #CPF #VECERT #InfoSec #CyberCrime 🇧🇷🛡️⚠️🚨

English
PalachSec retweetledi

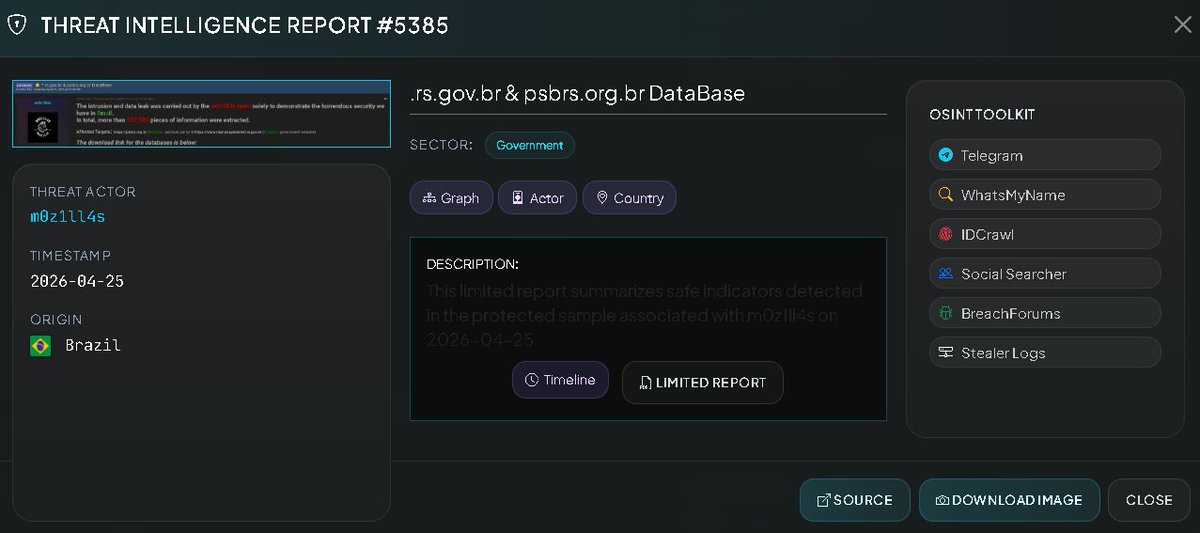
Dump3d Targets:
• psbrs.org.br (political party website)
• marianapimentel.rs.gov.br
Total: over 102k pieces of information extracted. Download the DBs:
gofile.io/d/KAwssg
BF: breachforums.rs/Thread-DATABAS…
@DailyDarkWeb @Alph4_Sec @H4ckmanac #DataBreach #m0z1ll4s

English
PalachSec retweetledi

🚨 BREACH ALERT | 🟡
PSBRS.org.br & rs.gov.br have been compromised.
📊 Records: 102,000
🎭 Actor: m0z1ll4s
🗓 Date: 25 April 2026
⚠️ Severity: MEDIUM
What was leaked:
→ Data related to Brazilian political party (PSBRS)
→ Possible government-linked records (rs.gov.br)
→ Internal system information (unclear scope)
⚠️ This breach is currently UNVERIFIED.
If you are associated with these platforms, review security controls immediately.
#DataBreach #Brazil #CyberSecurity #Government #ThreatIntel #Infosec #DataLeak

English
PalachSec retweetledi

🚨 CYBERINTELLIGENCE ALERT: POSSIBLE INTRUSION AND MASSIVE DATA LEAK – BRAZILIAN GOVERNMENT AND POLITICAL SECTOR 🇧🇷🔐
A highly sensitive data leak has been detected, affecting government and political infrastructure in Brazil. The threat group "m0z1ll4s team" has published databases exfiltrated from the country.
🔍 Incident Details
🏢 Affected Entities:
Government of Mariana Pimentel (marianapimentel.rs.gov.br).
Brazilian Socialist Party - RS (psbrs.org.br).
👤 Threat Actor: m0z1ll4s team
📂 Leak Volume: +102,000 records of exfiltrated information.
📅 Publication Date: Saturday, April 25, 2026.
⚠️ Status: The attackers have provided direct download links for both datasets; however, the leak has not yet been officially confirmed.
📊 Impact Analysis (VECERT Intelligence)
The leak compromises both municipal public administration and the privacy of regional political structures:
Government Data: Potential exposure of citizen records, administrative proceedings, public servant data, and internal configurations for the .rs.gov.br domain.
Political Data: Possible leakage of membership lists, contact records, campaign strategies, and internal party communications.
Technical Information: The intrusion suggests the exploitation of vulnerabilities within the CMS or databases of the affected portals.
🛡️ Immediate Response Recommendations
🔒 Systems Audit: Administrators of the .rs.gov.br domains are advised to conduct a forensic analysis to identify the entry point and close any active security gaps.
🔑 Credential Reset: Enforce a mandatory password change for all users and administrators across the affected platforms.
Monitor: analyzer.vecert.io
🛡️ "The deliberate exposure of over 102,000 government and political records underscores the fragility of regional digital infrastructure in Brazil. VECERT issues this alert to safeguard the integrity of citizen data."
#CyberSecurity #Brazil #DataBreach #m0z1ll4s #GovSec #LGPD #VECERT #InfoSec #CyberCrime 🇧🇷🛡️⚠️
English
PalachSec retweetledi

We hacked into Oi (Brazilian telecommunications company) and managed to extract approximately 28,101,382 lines (6.58 GB). xD
Greetz: AR4B3 - PalachSec - h4xxz - T$
Here's the link to the leak below:
breachforums.rs/Thread-DATABAS…
@DailyDarkWeb @VECERTRadar
#databreach #m0z1ll4s

English