Sabitlenmiş Tweet
PatchRequest
148 posts


PatchRequest
@PatchRequest
Pentesting | Red Teaming https://t.co/MU7dqIIBye Game Hacking | Anti Cheat https://t.co/6XSq9gGrWq
Deutschland Katılım Temmuz 2019
395 Takip Edilen83 Takipçiler

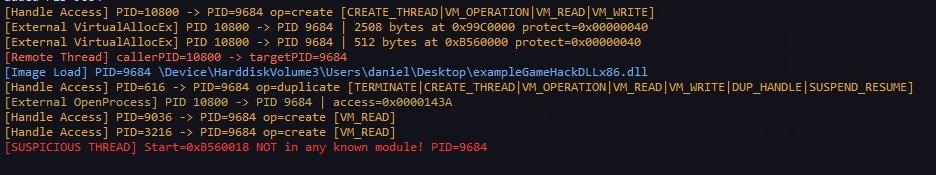
Continued working on my proof-of-concept anticheat.
These are the events visible to an anticheat when you use default DLL injection; pretty obvious, I'd say :)
github.com/PatchRequest/P…
English

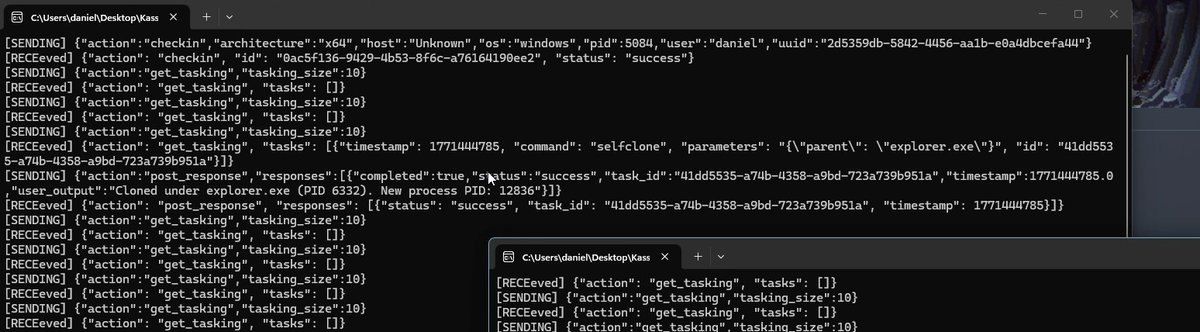
Just added self-clone to my Mythic agent: spawn new proc + spoofed PPID while original stays alive and running as backup
github.com/PatchRequest/K…
English

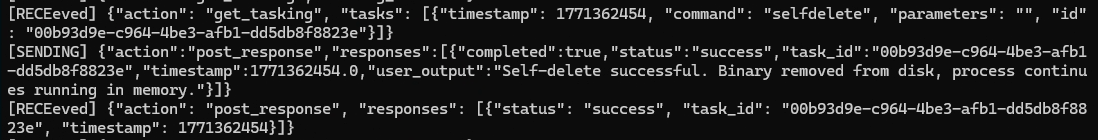
Just implemented self-deletion in my Mythic agent while the process keeps running smoothly.
Big thanks to @MalDevAcademy for the inspiration 🔥
github.com/PatchRequest/K…

English

@UK_Daniel_Card In 2025 he did:
Jan – CISSP
Jan – CCSP
March – OSED
July – OSWE
Oct – OSCE3
Oct – CRTO
Sure, just complete all of the "hardest" certs in a month or two while being a Deputy Manager and Red Team Lead at a Big4 company, and while running a blog with 32 pages of articles
English

@UK_Daniel_Card Saw his profile earlier too. He would have had to buy the certs. He supposedly completed all of them within three years, doing certifications like OSCE3 and CRTO at the same time in two months, right after finishing other certs in another two months, etc. It’s super suspicious.
English

@Salsa12__ Remove PPL should trigger PatchGuard, how did you avoid it?
English

🚀 PPLReaper Release
Windows kernel driver + userland tool to inspect and manipulate Protected Process Light (PPL):
• Query PPL
• Remove PPL
• Assign PPL
github.com/S12cybersecuri…
⚠️ The driver must be properly signed or the system must be in Test Mode

English

@ipurple Patchguard is already detecting this and giving a bsod
English

Basic, but I guess effective enough to catch some script kiddies. I added a blacklist of words that should not appear in any running process. I think some cheaters actually get caught in the wild by this lol
github.com/PatchRequest/P…

English

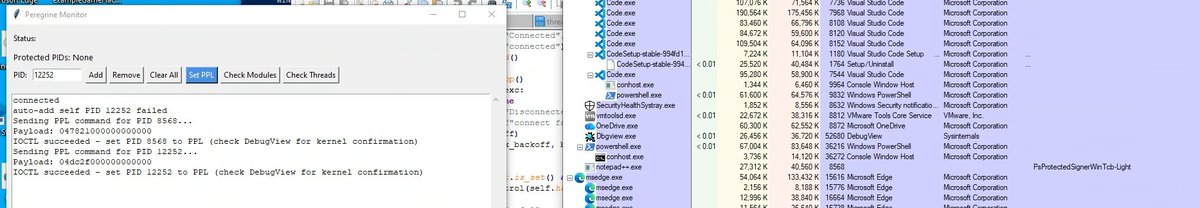
I wanted to consume some ETW providers, but it turned out I needed to be a PPL. So thats a side quest I worked on for now. Not sure how useful this is for protecting the game, but the protection for my own usermode part should be useful for the anti-cheat
github.com/PatchRequest/P…
English

This is how the default settings of the @GuidedHacking injector currently appear in my anti-cheat.
You can clearly see the sequence:
WriteProcessMemory → DLL image load → new thread inside the newly loaded DLL.
github.com/PatchRequest/P…

English
PatchRequest retweetledi

Vibe Coding with AI was the best ever for Bug Bounty. The DevOps is so bad that I love it.
While generating tokens, it somehow generates infosec jobs too
Find more at: cerast-intelligence.com

English
PatchRequest retweetledi

We are live! Search our database of over 8 million potentially exposed files by domain 🔍 Explore now:
cerast-intelligence.com
English
PatchRequest retweetledi

Sneak Peek of what’s coming October 1st
Be ready | millions of never-before-seen exposed files will become searchable
cerast-intelligence.com

English

Injecting a DLL into every process and overwriting WinAPI functions can easily go wrong. My anti-cheat crashed the PC with the pop-ups :)
Is this technique a thing for anti-cheats? I mainly know it from EDR and AV
github.com/PatchRequest/O…

English

I think scoring applications based on ProcAge, ExeAge, and their behavior is a valid approach to determine whether it’s just Task Manager requesting a handle for the billionth time or a Python CreateRemoteThread PoC
github.com/PatchRequest/O…

English

Second detection: when somebody requests a handle to my protected process, I can react to it.
github.com/PatchRequest/O…

English

Started detecting remote thread creation, pretty cool if you ask me :)
At first I was confused until I realized my notify routine runs in the process context of the invoker, then it was pretty easy to detect
github.com/PatchRequest/O…

English




