

PentesterLand
143 posts


@PentesterLandEn
WNMC Penetration Tester RedTeamer BugHunter









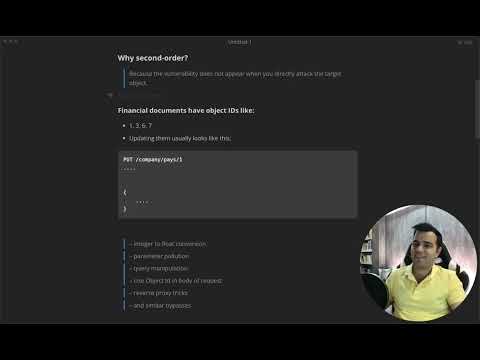
A Broken Access Control scenario no one has talked about before. Not a recycled bug. Not a misconfiguration. A new access control logic pattern with real exploitation impact. 🔥 Watch: youtu.be/X3oj-nx6580?si… #bugbountytips #bugbountytip #bugbounty

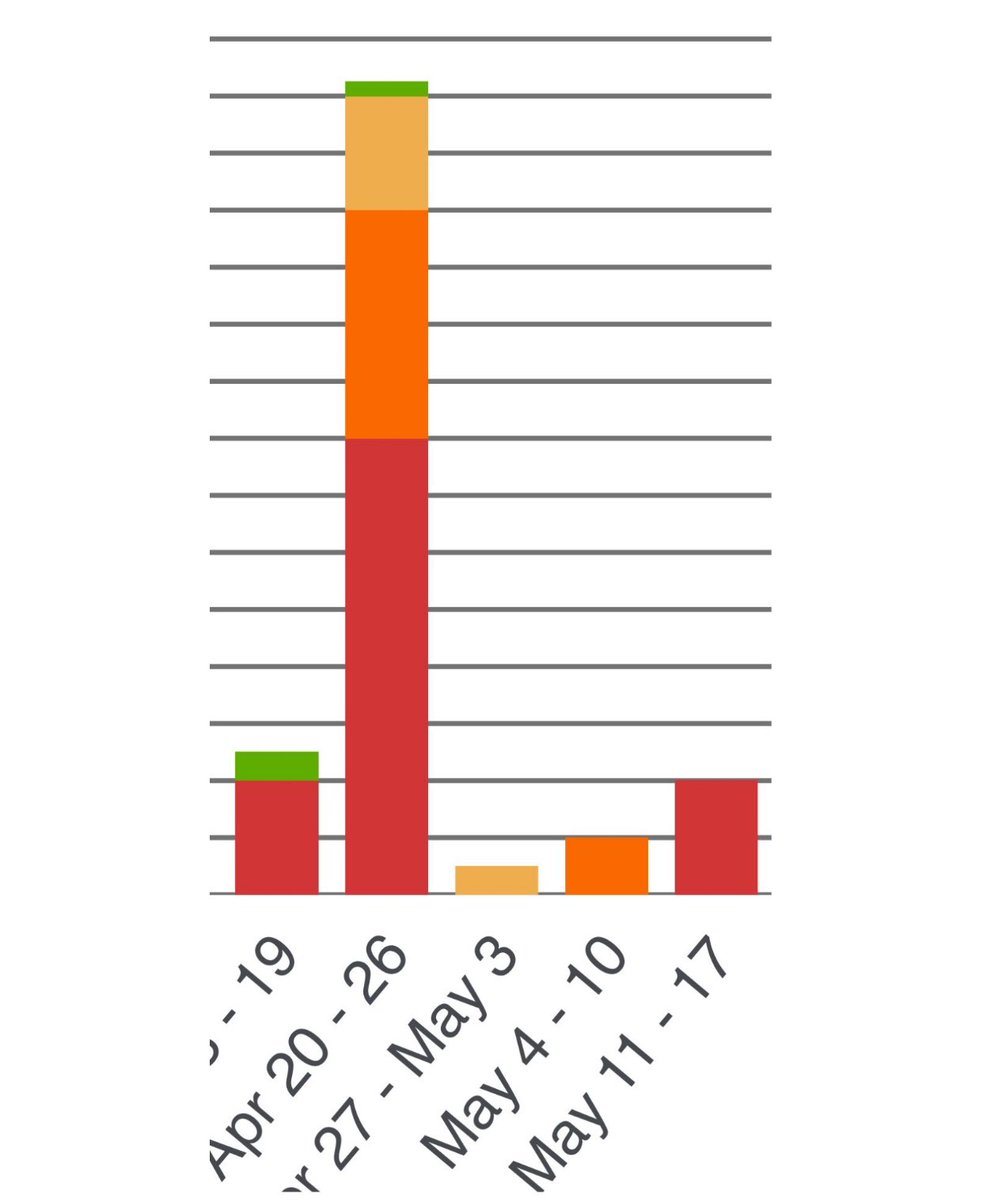

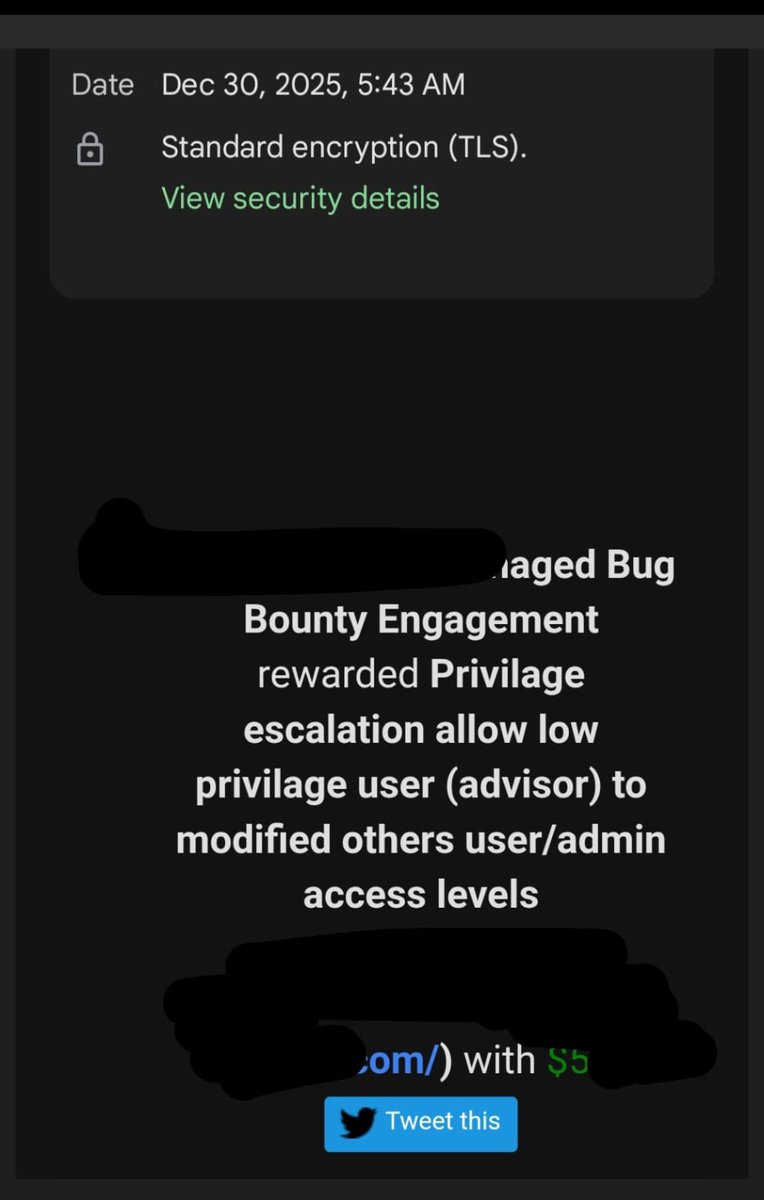


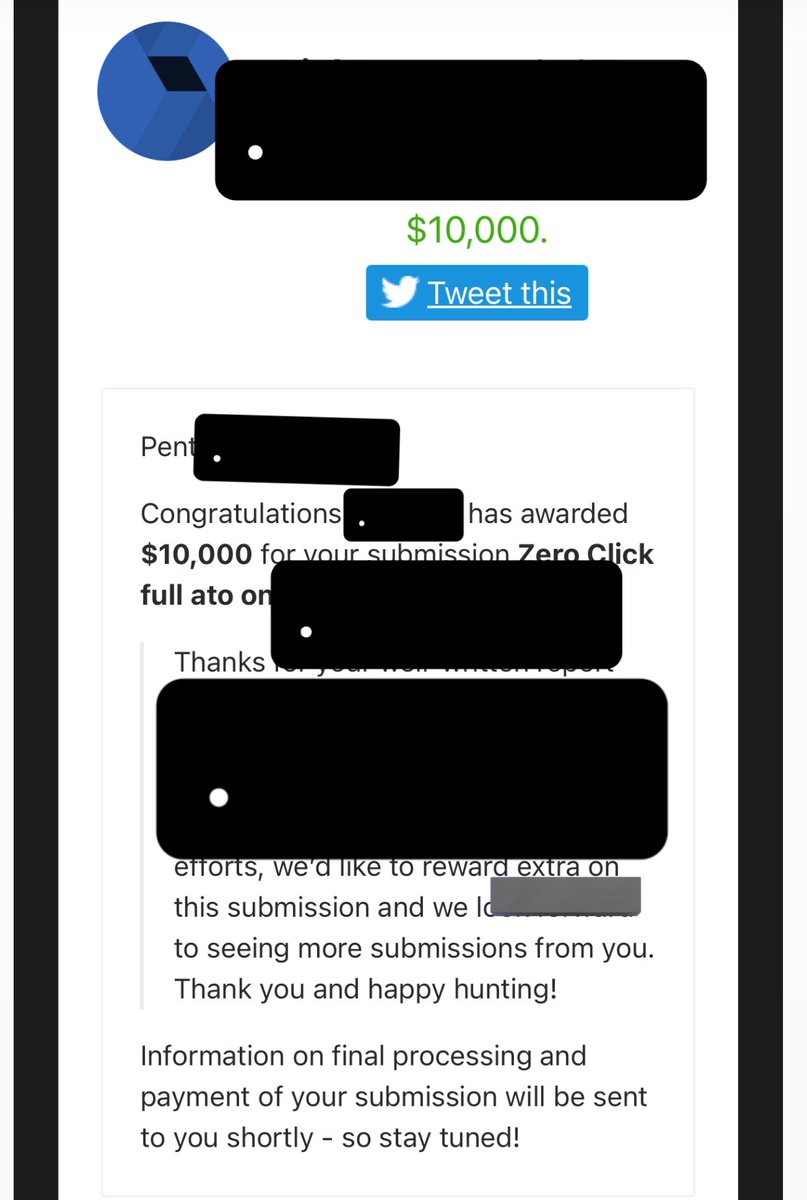
I earned $10,000 for my submission on @bugcrowd #ItTakesACrowd Extra bounty When the target pays more than the bounty amount, I’m like this: Do not miss the last video on YouTube channel: PentesterLandEn instagram.com/reel/DS1lHg7iC…







A Broken Access Control scenario no one has talked about before. Not a recycled bug. Not a misconfiguration. A new access control logic pattern with real exploitation impact. 🔥 Watch: youtu.be/X3oj-nx6580?si… #bugbountytips #bugbountytip #bugbounty





A Broken Access Control scenario no one has talked about before. Not a recycled bug. Not a misconfiguration. A new access control logic pattern with real exploitation impact. 🔥 Watch: youtu.be/X3oj-nx6580?si… #bugbountytips #bugbountytip #bugbounty


