Garrett Kohlrusch
21 posts


Garrett Kohlrusch
@gkdataio
Offensive security specialist with 100+ validated vulnerabilities across Fortune 500 targets and major tech platforms. Hunter-mentality approach.


Privileged to help lead this. Thankful to our partners. Mythos is an extraordinary model. But it is not about the model. It's about what the world needs to do to prepare for a future of models that are extremely good at cybersecurity. This is the start.



🫡 We’re back. Today, we’re publishing vulnerabilities we discovered, disclosed, and chained to achieve pre-auth RCE against Progress ShareFile. Enjoy the journey with us, while you sob into your hands 🫠 labs.watchtowr.com/youre-not-supp…



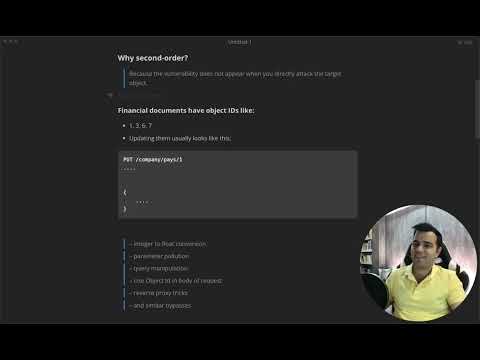
Point-in-time pentests can’t keep up, while fully autonomous testing creates noise. The solution? HackerOne Agentic PTaaS pairs specially trained AI agents with elite human validation to deliver results based on real-world exploitability, not theory. This 50-second video shows you how it works.

Point-in-time pentests can’t keep up, while fully autonomous testing creates noise. The solution? HackerOne Agentic PTaaS pairs specially trained AI agents with elite human validation to deliver results based on real-world exploitability, not theory. This 50-second video shows you how it works.