Z3RO retweetledi

This actually happened. Nigeria Police Force confirmed it. January 28, 2026.
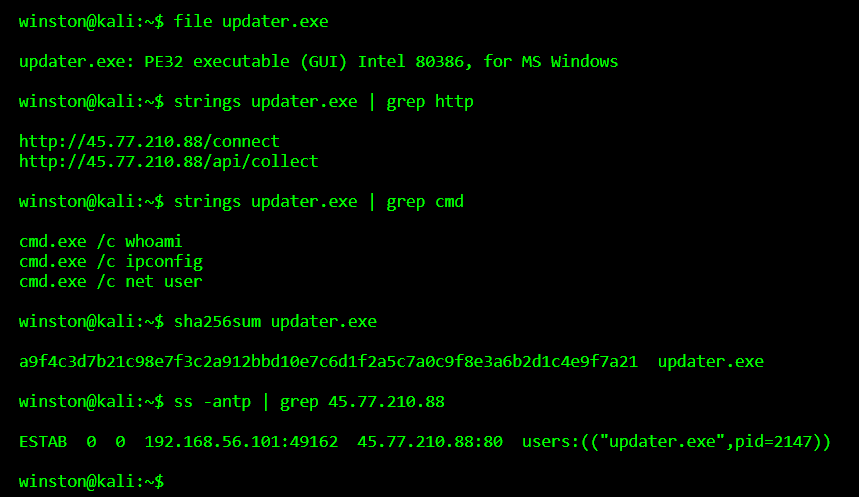
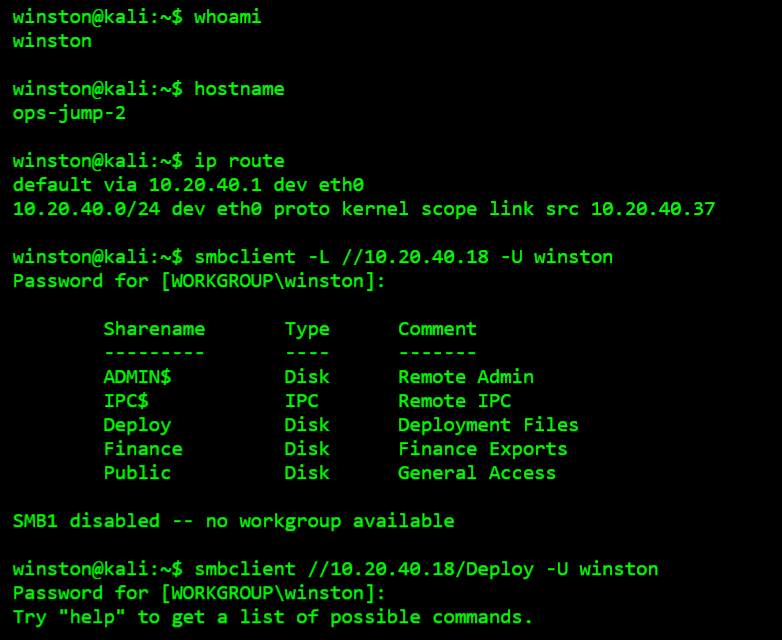
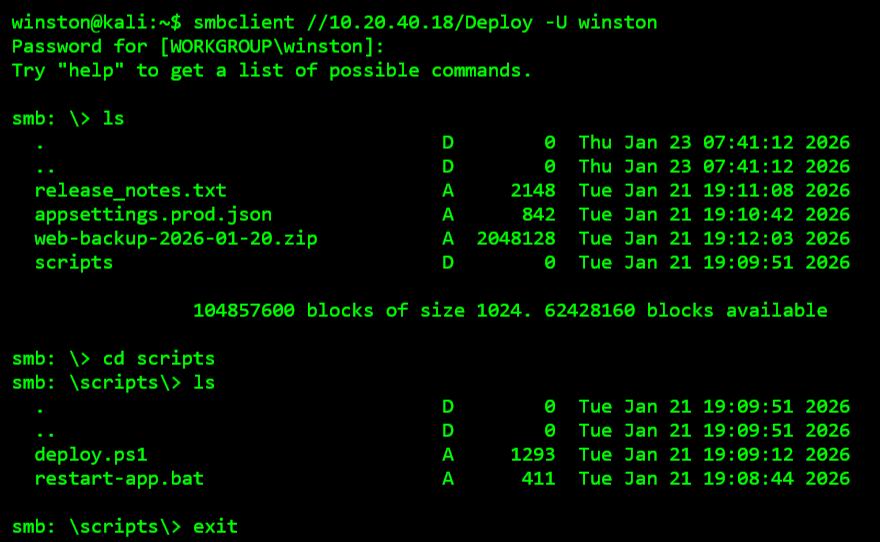
A Nigerian telecommunications company noticed something strange in its billing and payments system.
Airtime was leaving. Data was disappearing. At scale.
They filed a petition with the police.
What investigators found: internal staff login credentials had been compromised.
Someone on the inside or someone who got to someone on the inside had handed over access to the company's core billing infrastructure.
Six suspects were eventually arrested across three states.
Operations in Kano. Katsina. Then a follow-up in Abuja.
What police recovered from them:
Two residential houses.
Two mini-plazas.
GSM and laptop retail outlets.
Over 400 laptops.
1,000 mobile phones.
A Toyota RAV4.
Total diverted: ₦7.7 billion in airtime and data.
Think about what ₦7.7 billion in airtime looks like.
It is not cash sitting in a vault.
It is digital credits generated, distributed, and resold through a network of retail outlets before anyone noticed the source was stolen.
The telco's billing system treated every diversion as a legitimate transaction.
Because the credentials used were legitimate.
That is the nature of credential compromise attacks.
The system does not know it is being robbed.
It just sees an authorised login doing authorised things.
What stops this:
Multi-factor authentication on every internal system especially billing and payments infrastructure.
Anomaly detection on privileged accounts that flag unusual transaction volumes, unusual hours, unusual locations.
Principle of least privilege... staff should only access exactly what their role requires. Nothing more.
Credential compromise is not a sophisticated attack.
It is the most common attack vector in Nigeria's tech ecosystem right now.
And it is working.
₦7.7 billion worth of airtime says so.
English