Sabitlenmiş Tweet
PrivacyHawk
1.6K posts


PrivacyHawk
@Privacy_Hawk
The Personal Data Management App that lets you opt-out, unsubscribe and delete your private data from companies, all in one app. Available for iOS and Android📲
Katılım Mart 2021
21 Takip Edilen281 Takipçiler

Vimeo just confirmed a data breach. 119,000 users affected. Names, emails, video metadata, and technical data exposed, through a third-party analytics vendor, not Vimeo's core systems.
ShinyHunters claimed responsibility and leaked 106GB after Vimeo refused to pay.
And once again, the breach didn't come from within, third-party integrations mean more exposure and less control over it.
English

Law enforcement breach claims carry a different level of concern because even partial exposure can create operational and personal safety risks. Officer identities, investigative metadata, or administrative access details can be reused for targeting, impersonation, or counter-surveillance long after the initial leak claim. At the same time, government-branded leaks are frequently exaggerated or repackaged for attention, which is why validation matters more than the headline itself.
English

🇫🇷 A threat actor is claiming to have breached and leaked data allegedly associated with the French National Police (“Police Nationale”).
The underground post includes:
• claims of administrative compromise
• references to a downloadable database
• alleged access to police-related systems or records
• public distribution of a download link on a cybercrime forum
At this time:
• the authenticity of the alleged database has NOT been independently verified
• the source of the claimed compromise remains unknown
• the scope and sensitivity of the alleged data are unclear
• no official confirmation from authorities has been observed
If legitimate, compromise of law-enforcement-related infrastructure could create significant risks including:
• exposure of officer information
• operational security failures
• intelligence leakage
• targeting of personnel
• criminal counter-surveillance
• identity exposure of investigations or informants
• credential abuse against government systems
Threat actors frequently exaggerate or falsely brand leaks using:
• government agency logos
• politically charged narratives
• recycled datasets
• previously leaked information
• fabricated screenshots
However, even partial authenticity could still present operational and reputational risks.
Law enforcement datasets may potentially contain:
• personnel records
• internal communications
• case references
• credential information
• infrastructure details
• citizen complaints
• investigative metadata
• administrative documents
Publicly advertising “download database” links is also consistent with a growing trend where threat actors:
• seek reputation within underground forums
• rapidly mirror stolen datasets
• encourage redistribution
• weaponize publicity for notoriety or extortion
Organizations connected to government or law-enforcement ecosystems should:
• monitor for related credential exposure
• review privileged access logs
• inspect unusual authentication activity
• audit externally exposed services
• rotate sensitive credentials if compromise indicators emerge
• monitor underground channels for reposted archives
The post additionally reflects an increasing trend of:
• opportunistic targeting of public-sector institutions
• politically themed cybercrime branding
• low-barrier data redistribution through forums and Telegram channels
• blending of hacktivism and financially motivated operations
DDW is continuing to monitor:
• validation attempts related to the alleged dataset
• reposts and mirrors
• additional disclosures from the actor
• possible attribution overlaps
• downstream abuse activity tied to the claim
#CyberSecurity #ThreatIntelligence #PoliceNationale #France #GovernmentSecurity #DataBreach #DarkWeb #CyberCrime #DDW #Intelligence

English

When healthcare, financial, and government-linked datasets start overlapping, the risk increases exponentially. Identity records tied to credit scoring, healthcare affiliations, tax identifiers, and contact data create highly detailed citizen profiles that can fuel fraud, impersonation, and long-term social engineering at scale. Even unverified, the combination of political messaging, Telegram distribution, and multi-sector targeting reflects how modern threat actors increasingly blend hacktivism, extortion, and data aggregation into one operation.
English

🇦🇷 A threat actor operating under the alias “EsqueleSquad” is advertising alleged leaked datasets tied to multiple Argentinian institutions, including references to:
• IOMA (Provincia de Buenos Aires)
• BCRA (Central Bank of Argentina)
• GDEBA-related systems
• additional government and affiliate data repositories
The post claims the exposure includes:
• affiliate/patient information
• addresses
• names and identification data
• CUIT/tax identifiers
• confidential documents
• debtor information
• internal panels
• chats and phone numbers
• alleged credit scoring datasets
• large-scale scraped financial records
The threat actor further claims:
• partial data releases have already occurred
• larger releases may follow
• content is being distributed through Telegram channels
• additional politically themed disclosures are planned
The listing references:
• “+32 million” credit-scoring related records
• “+1 million” affiliate/patient-related entries
• multiple Argentina-linked institutional sources
At this stage:
• the authenticity of the datasets has NOT been independently verified
• the exact source of compromise remains unclear
• some data may originate from aggregation, scraping, prior leaks, or third-party exposure
• the operational status of affected systems is unknown
If legitimate, the exposure could create substantial risks including:
• identity theft
• financial fraud
• targeted phishing
• account takeover attempts
• social engineering campaigns
• credit-related abuse
• political intimidation or harassment
• healthcare/privacy violations
Particular concern exists when healthcare-related and financial datasets are combined, as merged datasets dramatically increase adversary profiling capabilities.
The reference to:
• credit scoring
• citizen identifiers
• addresses
• financial metadata
• healthcare affiliation data
could enable:
• synthetic identity fraud
• loan fraud
• impersonation campaigns
• SIM swap targeting
• credential-reset abuse
• spearphishing operations
The post also highlights a growing underground trend:
threat actors increasingly blend:
• hacktivist branding
• political narratives
• financial data leaks
• doxxing-style operations
• mass scraping campaigns
• reputational extortion
rather than operating as traditional ransomware groups alone.
Organizations and agencies potentially impacted should:
• investigate possible unauthorized access
• audit exposed APIs and portals
• review third-party vendor exposure
• monitor Telegram and underground repost activity
• reset privileged credentials where appropriate
• monitor for identity-fraud activity tied to citizens or affiliates
Citizens should remain alert for:
• suspicious banking activity
• phishing emails/SMS messages
• fraudulent calls impersonating institutions
• unexpected account recovery attempts
• misuse of national identifiers or healthcare data
DDW is continuing to monitor:
• possible validation of the claims
• additional dataset releases
• Telegram redistribution channels
• associated actor infrastructure
• follow-on fraud activity linked to Argentinian entities
#CyberSecurity #ThreatIntelligence #Argentina #DataBreach #DarkWeb #FinancialCrime #HealthcareSecurity #IdentityTheft #CyberCrime #DDW #Intelligence
English

At this point, half these “Rockstar leaks” are probably just malware installers with better marketing than some actual games. The lack of samples, screenshots, or any technical proof makes this look far more like hype, reputation farming, or infostealer bait than a verified Rockstar compromise. In underground forums, attaching “GTA 6” or Rockstar branding to random archives is basically guaranteed clickbait.
English

I think this guy is going to release GTA 6 sooner than Rockstar games 😄
🎮 An underground forum post is claiming to distribute a compressed archive allegedly related to Rockstar Games.
The post references:
• a ZIP/compressed package
• alleged Rockstar Games-related data
• no publicly shared sample data
• a downloadable archive link
• claims that the package may be approximately one month old
Notably, the actor explicitly states:
• no extracted sample was provided
• no verification material was shared
• the archive is distributed “as-is”
At this time:
• the authenticity of the claim has NOT been independently verified
• there is no official confirmation from Rockstar Games
• the contents of the archive are unknown
• there is no visible evidence proving the material is legitimate
The absence of:
• file listings
• technical screenshots
• database schemas
• source code samples
• internal documentation
• credential evidence
significantly reduces confidence in the claim.
Underground posts of this nature are commonly associated with:
• recycled leaks
• repackaged old breaches
• fake archives
• malware-laced downloads
• reputation farming
• traffic generation
• opportunistic impersonation of major brands
Major gaming companies remain frequent targets because they possess:
• highly valuable intellectual property
• unreleased game assets
• developer environments
• online account ecosystems
• monetization platforms
• massive user communities
Historically, gaming-sector intrusions have involved:
• source code theft
• early build leaks
• developer tool exposure
• credential theft
• social engineering of employees
• Slack/Confluence compromise
• cloud storage exposure
If legitimate, potential risks could include:
• unreleased game asset exposure
• developer environment compromise
• account fraud
• phishing campaigns targeting players
• malware distribution disguised as leaks
• community scam activity
However, based on the currently visible evidence, the post should be treated with high skepticism until independently validated.
It is also important to note that underground “leak” downloads frequently contain:
• infostealers
• remote access trojans
• credential harvesters
• cryptocurrency miners
• malicious loaders
Users should avoid interacting with:
• suspicious archives
• underground download links
• unverified compressed packages
• executables claiming to contain “leaked” gaming content
Organizations within the gaming industry should continue focusing on:
• developer account security
• MFA enforcement
• source code repository monitoring
• insider threat controls
• cloud storage hardening
• phishing-resistant authentication
DDW is continuing to monitor:
• additional proof releases
• repost activity
• actor credibility
• potential malware distribution
• any legitimate indicators tied to Rockstar-related infrastructure or assets
#RockstarGames #Gaming #CyberSecurity #ThreatIntelligence #DarkWeb #Infosec #CyberCrime #DataLeak #DDW #Intelligence

English

This fits the broader ShinyHunters trend of targeting CRM and SaaS environments rather than core infrastructure directly. Salesforce-linked datasets are especially useful because they combine verified business contacts, organizational context, and communication history that can fuel highly targeted phishing and BEC campaigns. Even when many emails already exist in prior breaches, the added business metadata makes the data far more actionable for attackers.
English

New breach: Abrigo was targeted by ShinyHunters last month, who subsequently published over 700k unique email addresses allegedly taken from their Salesforce instance. Data also included business contact info. 57% were already in @haveibeenpwned. More: haveibeenpwned.com/Breach/Abrigo
English

PrivacyHawk is now inside ChatGPT.
Get personalized privacy and cybersecurity advice based on your actual digital footprint. See your privacy score, track your data broker removals, and send delete, unsubscribe, and Do Not Sell requests, all from the chat.
Advanced AI users can also set up alerts, notifications, and automated actions.
This is what protection looks like in the AI era.

English

Payment processor datasets are especially sensitive because they sit between banks, merchants, and customer identity systems. Even if unverified, records tied to payment activity, account metadata, and login history can be reused for phishing, fraud, and account takeover campaigns that feel legitimate because they reference real financial workflows. The bigger concern with leaks involving processors like Credicard is the operational visibility they may provide into broader payment ecosystems, not just individual users.
English

🇻🇪 A threat actor is claiming to sell a database allegedly linked to Venezuelan financial services company Consorcio Credicard.
According to the underground listing, the dataset allegedly contains:
• more than 5 million records
• customer-related database entries
• account and activity-related information
The actor references Credicard, a Venezuelan payment processing and financial services provider headquartered in Caracas, reportedly supporting major payment networks including Visa, Mastercard, and American Express.
Visible sample data shown in the post appears to reference:
• email-related attributes
• account status information
• creation and modification timestamps
• login activity metadata
• customer profile-related records
At this time:
• the authenticity of the dataset has not been independently verified
• there is no confirmation of a direct compromise of Credicard systems
• the origin and freshness of the data remain unclear
• the full scope and sensitivity of the alleged records are currently unknown
If authentic, financial-sector database exposures may present serious risks including:
• identity theft
• account takeover attempts
• targeted phishing campaigns
• payment fraud
• financial profiling
• credential stuffing attacks
Threat actors frequently target financial institutions and payment processors due to the value of:
• customer identity data
• transaction metadata
• payment ecosystem access
• authentication-related information
• long-term financial intelligence
Organizations operating in the banking and payment ecosystem should monitor for:
• suspicious login activity
• phishing campaigns impersonating financial brands
• underground redistribution of alleged datasets
• credential reuse attacks
• fraud attempts leveraging exposed customer information
Potentially affected users are advised to:
• rotate reused passwords immediately
• enable MFA where available
• remain cautious of unsolicited financial communications
• monitor banking and payment activity for anomalies
DDW is continuing to monitor:
• underground marketplace activity
• redistribution attempts
• authenticity validation efforts
• potential victim notifications or public disclosures
#Venezuela #Credicard #FinancialSector #DataLeak #CyberSecurity #ThreatIntelligence #DarkWeb #Infosec #CyberCrime #DataBreach #DDW #Intelligence

English

Unauthenticated APIs remain one of the most common ways platforms accidentally expose operational data at scale. Delivery services are especially sensitive because order history, addresses, phone numbers, and GPS coordinates create a detailed map of customer behavior and routines. Even unverified, logistics datasets like this carry more risk than typical contact leaks because they combine identity with real-world location context.
English

🇪🇬 A threat actor is claiming to have breached FutureShop Egypt, an Egyptian grocery delivery platform, alleging that the platform’s API was exposed without authentication requirements.
According to the underground post, the exposed data allegedly includes:
• customer records
• order information
• delivery addresses
• account metadata
• operational delivery details
The actor claims the dataset contains:
• customer full names in Arabic and English
• verified Egyptian phone numbers
• email addresses
• account creation dates
• account activity statuses
• order numbers and pricing information
• delivery notes
• GPS coordinates and formatted addresses
• timestamps spanning late 2025 through 2026
The post also references:
• order management information
• delivery status tracking
• admin panel-related exposure
• operational logistics metadata
At this time:
• the authenticity of the claims has not been independently verified
• there is no confirmation of direct compromise from the affected organization
• the full scale and sensitivity of the alleged exposure remain unclear
If authentic, exposed delivery-platform data could create elevated risks including:
• phishing and smishing attacks
• physical targeting risks through address exposure
• account takeover attempts
• fraud and impersonation
• profiling of consumer behavior and location patterns
API misconfigurations and unauthenticated endpoints continue to represent a major attack surface across:
• e-commerce platforms
• food and grocery delivery services
• fintech and logistics ecosystems
• mobile-first consumer applications
Organizations should monitor for:
• unusual API access activity
• unauthorized scraping patterns
• credential abuse attempts
• anomalous order or delivery behavior
• underground redistribution of leaked datasets
Potentially affected users should:
• remain cautious of unsolicited SMS or phone calls
• monitor accounts for suspicious activity
• rotate reused credentials
• enable MFA where supported
DDW is continuing to monitor:
• underground discussions
• authenticity validation efforts
• possible mirrored leaks
• operational abuse linked to the alleged exposure
#Egypt #DataBreach #CyberSecurity #API #DataLeak #ThreatIntelligence #DarkWeb #Infosec #CyberCrime #DDW #Intelligence

English

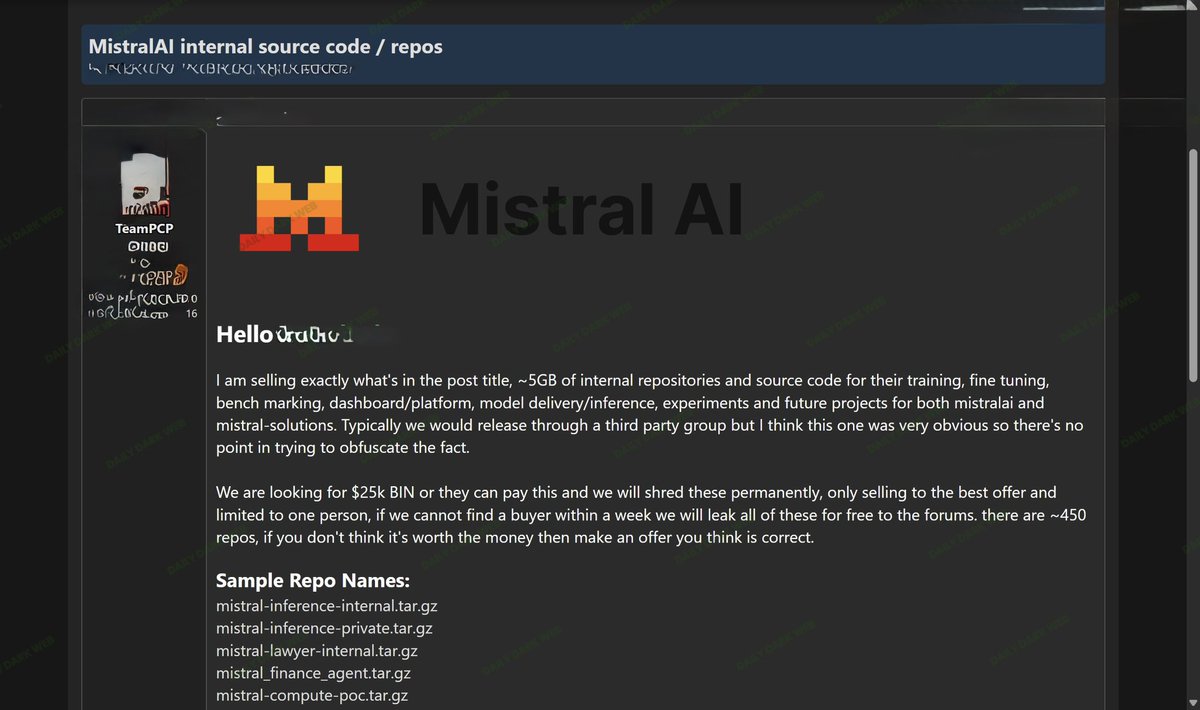
AI source-code claims are high leverage even when the dataset is small. If real, internal repos around inference, fine-tuning, and deployment tooling can reveal architecture, dependencies, and operational shortcuts attackers can study long after the leak. The key question isn’t the 5GB size, it’s whether any secrets, CI/CD logic, or model delivery paths are exposed enough to turn code visibility into future access.
English

🚨 THIS IS HUGE! A threat actor operating under the TeamPCP branding has claimed to be selling alleged internal repositories and source code associated with Mistral AI.
According to the underground post, the actor claims possession of:
• ~5GB of internal repositories
• approximately 450 repositories
• internal inference-related projects
• benchmarking and fine-tuning systems
• dashboard/platform components
• model delivery and inference tooling
• experimental and future AI projects
The post also references alleged repository names tied to:
• inference infrastructure
• finance-focused AI agents
• internal compute proof-of-concepts
• private/internal model tooling
The actor claims the data is being offered for sale with an exclusive buyer model and threatens public release if no buyer emerges.
At this time:
• the authenticity of the repositories has NOT been independently verified
• ownership and origin of the alleged repositories remain unconfirmed
• there is no confirmation that Mistral AI systems were compromised
• repository names alone do not validate the legitimacy of the claim
If authentic, exposure of AI infrastructure repositories could create significant downstream risks including:
• model supply chain exposure
• API credential leakage
• inference pipeline abuse
• proprietary model workflow disclosure
• infrastructure reconnaissance
• AI safety bypass research
• replication of internal deployment architectures
AI organizations should monitor for:
• leaked API keys or tokens
• unauthorized repository mirrors
• credential reuse risks
• exposed CI/CD secrets
• suspicious package dependencies
• copycat underground listings
• impersonation or phishing attempts leveraging leaked project names
This incident also reflects a growing underground trend:
threat actors increasingly targeting AI companies not only for customer data, but for:
• model infrastructure
• training environments
• orchestration pipelines
• proprietary tooling
• agentic workflows
• inference optimization systems
Even limited source-code exposure can provide adversaries with:
• architectural intelligence
• attack surface mapping opportunities
• deployment logic insights
• dependency-chain visibility
• operational tradecraft understanding
DDW is continuing to monitor:
• underground distribution activity
• repository validation efforts
• possible credential exposure
• secondary leaks or mirrors
• additional claims tied to AI infrastructure targeting
#CyberSecurity #AI #ArtificialIntelligence #MistralAI #ThreatIntelligence #DarkWeb #DataLeak #Infosec #LLM #CyberThreats #DDW #Intelligence
English

Signal isn’t changing encryption here, it’s responding to the reality that attackers increasingly bypass security by targeting people instead of breaking cryptography. The new warnings and confirmations are meant to make phishing and linked-device hijacking attempts more visible before users accidentally hand over access.
English

Signal adds security warnings for social engineering, phishing attacks
bleepingcomputer.com/news/security/…
bleepingcomputer.com/news/security/…
English

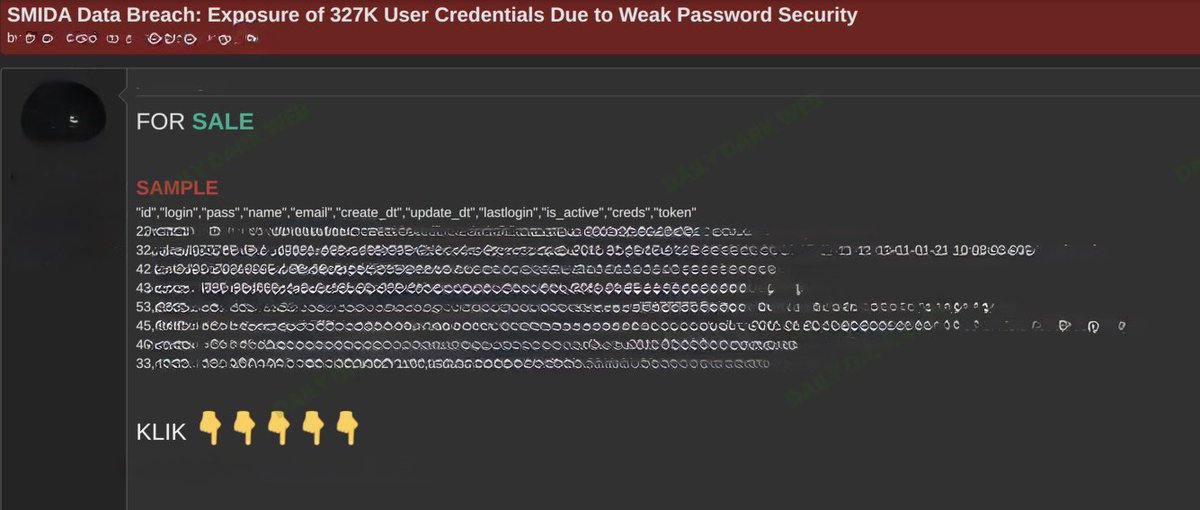
Credential leaks remain some of the most reusable assets in cybercrime because attackers rarely stop at one platform. Usernames, emails, tokens, and password-related fields quickly become part of credential stuffing and account takeover campaigns, especially when password reuse is involved. Even unverified, mentions of weak password security and active account metadata are concerning because they suggest operational accounts, not just stale historical records.
English

🇨🇳 An underground actor is advertising a claimed breach involving SMIDA, alleging exposure of approximately 327,000 user credential records.
According to the listing, the exposed data allegedly includes:
• usernames/logins
• email addresses
• password-related fields
• account tokens
• credential metadata
• account activity timestamps
• account status information
The actor specifically references:
• “weak password security”
• credential exposure
• active account-related records
The sample shown in the post appears to include fields such as:
• id
• login
• pass
• name
• email
• last login timestamps
• token-related entries
At this time:
• the authenticity of the dataset has not been independently verified
• there is no official confirmation from SMIDA
• the exact storage method of the passwords remains unclear
• it is unknown whether credentials are hashed, encrypted, or plaintext
If verified, credential-focused leaks present elevated risks including:
• credential stuffing
• account takeover attempts
• phishing campaigns
• password reuse exploitation
• business email compromise
• identity fraud
Threat actors frequently weaponize leaked credential databases by:
• testing passwords across other services
• enriching identity datasets
• building phishing target lists
• selling combo lists on underground forums
Organizations should immediately review:
• password storage practices
• hashing algorithms
• MFA adoption
• token management
• inactive account hygiene
• credential exposure monitoring
Users potentially affected should:
• reset passwords immediately
• avoid password reuse across platforms
• enable MFA wherever possible
• monitor suspicious login activity
• review linked accounts and recovery methods
Weak password security remains one of the most exploited systemic issues across:
• legacy applications
• internal portals
• poorly segmented databases
• outdated authentication architectures
DDW is continuing to monitor for:
• additional proof samples
• actor credibility
• redistribution activity
• credential validation
• follow-on exploitation attempts
#CyberSecurity #DataBreach #Credentials #ThreatIntelligence #PasswordSecurity #Infosec #CyberCrime #AccountTakeover #DDW #Intelligence
English

This follows the same ShinyHunters pattern we’ve seen across multiple organizations: customer contact data gets exposed through third-party or operational access, then republished for extortion and reuse. Even if many emails were already in prior breaches, combining them with names, phone numbers, and physical addresses makes phishing and impersonation far more effective because the data feels legitimate and current.
English

New breach: Canada Life was named as a ShinyHunters victim last month, after which data containing more than 200k email addresses was published. The incident also impacted name, phone number and physical address. 47% were already in @haveibeenpwned. More: haveibeenpwned.com/Breach/CanadaL…
English

3.5TB of student-related data was stolen from Canvas owner Instructure by the ShinyHunters hacking group after attackers gained access to systems tied to schools and universities using the platform.
Instead of risking a public leak, Instructure confirmed it reached a “settlement” with the hackers to recover the data and prevent customers from being extorted.
The company avoided calling it a ransom, but the situation highlights a growing reality of modern breaches: once data is copied, there’s no reliable way to verify it’s truly gone.
Security experts have warned for years that stolen data can still be retained, resold, or leaked later, even after agreements are made.

English

QA and staging environments are often the weakest link because they’re treated as “non-production” while still containing real data, credentials, and internal architecture details. If claims like this are legitimate, the bigger risk isn’t just the leaked information, it’s the operational visibility attackers gain into logistics workflows, integrations, and infrastructure that can later be reused for deeper compromise or supply-chain targeting.
English

🇨🇴 A threat actor on an underground forum is claiming to be selling an alleged 3 TB data leak associated with SmartQuick.
According to the forum post:
• The actor claims to possess internal and confidential databases from smartquick.com.co
• The alleged dataset reportedly includes QA and web production data
• References to logistics and commercial process platforms were mentioned
• The asking price was listed at approximately $500 USD
• Multiple internal/admin-related domains were referenced in the post
The actor describes SmartQuick as a technology and mobile application platform focused on:
• Logistics optimization
• Tracking systems
• Commercial process management
At this time:
• The claims remain unverified
• No independent confirmation of a compromise has been established
• The authenticity, age, and completeness of the alleged dataset are unknown
Potential risks from exposed production and QA environments may include:
• Exposure of internal credentials or API keys
• Client or operational data disclosure
• Supply chain compromise risks
• Infrastructure mapping opportunities for attackers
• Credential reuse and pivoting attacks
Organizations should immediately assess:
• Separation between QA and production environments
• Public exposure of admin panels
• Credential hygiene and MFA enforcement
• Cloud storage and backup access controls
• Web application logs and anomalous access activity
• Third-party/vendor integrations
If legitimate, exposed QA environments can be particularly dangerous because they may contain:
• Hardcoded credentials
• Test accounts with elevated privileges
• Debugging information
• Staging copies of production data
• Internal architecture details
Daily Dark Web is monitoring underground communities for additional indicators, leaked samples, or validation attempts related to this alleged incident.
#DDW #Intelligence #Colombia #CyberSecurity #DarkWeb #DataLeak #ThreatIntelligence #SupplyChain #LogisticsSecurity #WebSecurity

English

Banking-related datasets become dangerous because attackers don’t need full account access to exploit them. Names, phone numbers, location data, and card-related references are often enough to build convincing fraud calls, phishing campaigns, or SIM swap attempts that bypass normal skepticism. Even unverified, financial-sector data tends to gain value when combined with other leaks, creating richer profiles for long-term fraud operations.
English

🇲🇽 A threat actor on an underground forum is claiming to possess and leak data allegedly associated with BBVA Bancomer bank customers.
According to the post, the compromised data allegedly includes fields related to:
• Names and surnames
• Postal codes
• Cities and municipalities
• Telephone numbers
• Product/account references
• Card expiration-related fields
• State and district information
• Telecom/provider metadata
The actor also shared screenshots appearing to contain structured customer-style records and database excerpts.
At this time:
• The claims remain unverified
• The authenticity of the dataset has not been independently confirmed
• There is no evidence currently indicating a confirmed compromise of BBVA infrastructure
• The data may originate from aggregation, prior leaks, third-party exposure, phishing, or fraud-related collections
Financial-sector datasets remain highly valuable in underground markets due to their usefulness in:
• Banking fraud
• Social engineering
• SIM swapping
• Account takeover attempts
• Identity theft
• Smishing/vishing campaigns
• Synthetic identity operations
• Credential reset abuse
Threat actors commonly weaponize customer data by:
• Impersonating financial institutions
• Sending targeted phishing messages
• Conducting OTP interception scams
• Exploiting weak identity verification processes
• Building fraud intelligence profiles
Banking organizations should prioritize:
• Monitoring abnormal authentication attempts
• Reviewing customer support abuse patterns
• Monitoring phishing infrastructure impersonating the brand
• Reviewing third-party vendor exposure
• Strengthening identity verification workflows
• Enforcing MFA protections and behavioral analytics
Customers should remain alert for:
• Unexpected banking calls or SMS messages
• Fake fraud alerts
• Credential reset attempts
• SIM transfer notifications
• Unauthorized account activity
• Requests for OTP or verification codes
Underground actors frequently exaggerate the scope or freshness of financial datasets, and some listings may involve:
• Repackaged historical leaks
• Mixed datasets from multiple sources
• Partial records
• Fraud collections assembled over time
Daily Dark Web is continuing to monitor underground communities for additional samples, validation, and signs of active abuse tied to this alleged dataset.
#DDW #Intelligence #Mexico #CyberSecurity #DarkWeb #BankingSecurity #ThreatIntelligence #Fraud

English

Support-ticket datasets are often mislabeled as “platform breaches” because recognizable brands attract attention fast. The fields shown here look more like helpdesk or CRM exports than evidence of direct Google infrastructure compromise, which is a common pattern in underground forums. Even so, support metadata and customer interaction details can still be valuable for phishing and impersonation because they expose operational context, not just identities.
English

🇺🇸 Google Gemini allegedly listed in underground forum database leak claims.
A threat actor on a cybercrime forum claims to be sharing a dataset allegedly associated with gemini.google.com.
According to the post, the actor claims:
• Multiple individuals have been selling the alleged dataset
• They are now releasing it publicly/free of charge
• The shared sample allegedly contains support or ticketing-related fields
The visible sample references fields such as:
• submitter_email
• requester_id
• organization_id
• subject
• created_at / updated_at
• ticket_form_id
• resolution and response-time metrics
• agent wait time and business-hours tracking fields
At this time:
• The claims remain unverified
• There is no evidence confirming a compromise of Google systems
• The dataset may potentially originate from third-party integrations, support tooling, scraped content, fabricated data, test environments, or unrelated systems using “Gemini” branding
• No official statement from Google regarding this specific claim has been observed
Underground actors frequently use well-known brands to:
• Increase visibility of forum posts
• Sell recycled or repackaged datasets
• Misrepresent unrelated support exports as direct platform compromises
• Drive traffic to channels or marketplaces
Without independent validation, attribution to Google Gemini should be treated cautiously.
Organizations and users should remain aware that even alleged ticketing/support datasets may expose:
• Email addresses
• Internal workflow identifiers
• Support metadata
• Customer interaction details
• Operational analytics information
Daily Dark Web is continuing to monitor underground communities for additional samples, validation indicators, or official responses related to this claim.
#DDW #Intelligence #Google #Gemini #CyberSecurity #DarkWeb #ThreatIntelligence #DataLeak
English

This looks more like malware bait than a verified source code leak. Threat actors know “AI source code” attracts researchers, developers, and curious users, so labeling an infected archive as Claude-related is a cheap way to drive downloads. The warning to use a VM is almost the tell, the value here may be infecting whoever opens it, not proving any real Anthropic compromise.
English

🤖 A threat actor on an underground forum is claiming to share alleged “Claude source code” and warns that the archive is intentionally infected with malware.
According to the post:
• The actor claims the source code was leaked in March 2026
• A download link was provided
• The actor explicitly warns users to open the files only inside a virtual machine (VM)
• The archive is allegedly weaponized or malware-laced
At this time:
• The claims remain unverified
• There is no confirmation of any authentic compromise involving Anthropic or Claude infrastructure
• The shared files may simply be:
• Malware bait
• Fake repositories
• Repackaged open-source code
• Credential stealers
• Backdoored archives
• Infostealer delivery mechanisms
This type of activity is extremely common across underground communities, where actors abuse:
• AI branding
• Popular developer tools
• Leaked-source-code curiosity
• “Exclusive breach” narratives
to distribute malware and infect researchers, cybercriminals, and inexperienced users.
Threat actors frequently weaponize:
• ZIP/RAR archives
• Fake Git repositories
• Trojanized Python packages
• Malicious npm/pip dependencies
• Loader malware hidden in “leaked” tools
• Backdoored executables disguised as PoCs
AI-related brands are increasingly leveraged in:
• Malware campaigns
• Crypto scams
• Credential phishing
• Fake beta access schemes
• Trojanized developer tools
Researchers and analysts should avoid:
• Executing unknown binaries
• Opening untrusted archives on production systems
• Running suspicious repositories without sandboxing
• Disabling endpoint protections for testing purposes
Recommended precautions include:
• Using isolated VMs or sandboxes
• Verifying repository authenticity
• Inspecting code statically before execution
• Monitoring outbound connections
• Avoiding execution of unsigned binaries
• Using disposable analysis environments
At this time, there is no evidence presented in the screenshot confirming an authentic Claude source code leak.
Daily Dark Web is continuing to monitor underground forums for additional indicators, malware samples, or validation related to these claims.
#DDW #Intelligence #CyberSecurity #DarkWeb #AI #Claude #Malware #ThreatIntelligence
English

Most “Discord database” claims end up being scraped profiles, token-stealer logs, or data pulled from compromised bots and communities rather than a direct platform breach. The real risk is when session tokens or malware-collected browser data are involved, because attackers can hijack accounts without needing passwords. Discord’s ecosystem is already heavily used for phishing, malware delivery, and credential theft, so recycled or aggregated datasets still become useful once they start circulating underground.
English

🎮 A threat actor has posted an alleged “Discord database” on an underground forum, claiming to possess user-related records associated with the platform.
According to the screenshot shared on the forum, the exposed sample appears to contain:
• Discord-related identifiers
• Usernames
• IP addresses
• Timestamps
• JSON-formatted records
• Possible account metadata
At this time:
• The claims remain unverified
• There is no confirmation of a direct compromise of Discord infrastructure
• The dataset could potentially originate from:
• Third-party bots
• Scraped public data
• Compromised Discord communities
• Malware logs
• Token harvesting operations
• Previously leaked collections
The presence of Discord usernames or IDs alone does not necessarily indicate a platform-wide breach.
Discord continues to remain heavily abused within cybercrime ecosystems for:
• Malware delivery
• Phishing campaigns
• Credential harvesting
• Token theft
• Command-and-control infrastructure
• Underground community coordination
• Data trading operations
Threat actors frequently use Discord-related branding in underground forums to:
• Increase visibility of listings
• Attract buyers
• Repackage mixed-source datasets
• Sell scraped or aggregated information as “fresh breaches”
Users should remain cautious of:
• Fake Nitro giveaways
• Malicious Discord bots
• Token-stealing malware
• Browser credential theft
• QR-code phishing attacks
• Fake verification servers
Recommended defensive measures include:
• Enabling MFA
• Avoiding untrusted Discord bots
• Reviewing active sessions/devices
• Rotating passwords if compromise is suspected
• Monitoring for credential reuse exposure
• Using endpoint protection against infostealers
Daily Dark Web is continuing to monitor underground communities for additional indicators, technical validation, or related datasets tied to this claim.
#DDW #Intelligence #CyberSecurity #Discord #DarkWeb #DataLeak #ThreatIntelligence #Infostealer
English

Crypto exchange datasets are high-value because they tie identity directly to financial activity and digital assets. Even unverified claims like this matter because leaked credentials, session data, or customer details can quickly turn into phishing, account takeover attempts, or wallet-targeted scams. In crypto ecosystems especially, attackers often rely more on credential reuse and social engineering than direct platform compromise.
English

🇰🇾 A threat actor has allegedly leaked a database claimed to be associated with the crypto exchange BitMart on a dark web forum.
The post advertises a downloadable “Bitmart” database, but at this stage there is no verified evidence confirming the authenticity, scope, or origin of the data.
Organizations and users potentially affected should:
Reset passwords immediately
Enable MFA if not already enabled
Monitor for suspicious login attempts and phishing activity
Review reused credentials across other platforms
Daily Dark Web is monitoring the situation for further verification and technical indicators.
#DDW #CyberSecurity #DataBreach #Crypto #BitMart #ThreatIntelligence
English

Banking datasets become especially dangerous when identity and card-related information are combined. Names, DOBs, mobile numbers, and banking fields give attackers enough context for convincing phishing, SIM swaps, and account recovery abuse that can bypass normal skepticism. Even unverified, datasets tied to major financial institutions tend to get reused across long-term fraud campaigns rather than a single leak event.
English

🇲🇾 A threat actor is claiming to sell an alleged database belonging to CIMB Bank Malaysia containing over 2 million records.
According to the post, the exposed data allegedly includes:
Customer names
Mobile numbers
Gender
Dates of birth
Card-related information
Banking-related fields
The actor also shared sample screenshots and is attempting to monetize the dataset through underground channels.
If verified, exposure of this type of banking data could significantly increase risks related to:
Financial fraud
Identity theft
Social engineering
SIM swapping
Targeted phishing campaigns
Account takeover attempts
Financial institutions should closely monitor for:
Unusual authentication activity
Credential stuffing attempts
Spike in phishing infrastructure impersonating the bank
Fraud patterns tied to customer identity data exposure
Customers are advised to:
Be cautious of unsolicited banking calls or SMS messages
Monitor account activity regularly
Enable MFA where available
Avoid sharing OTP or verification codes
The authenticity of the database has not been independently verified at this time.
#DDW #CyberSecurity #Malaysia #Banking #DataBreach #ThreatIntelligence #DarkWeb #Infosec

English
