Maniesh.Neupane
238 posts


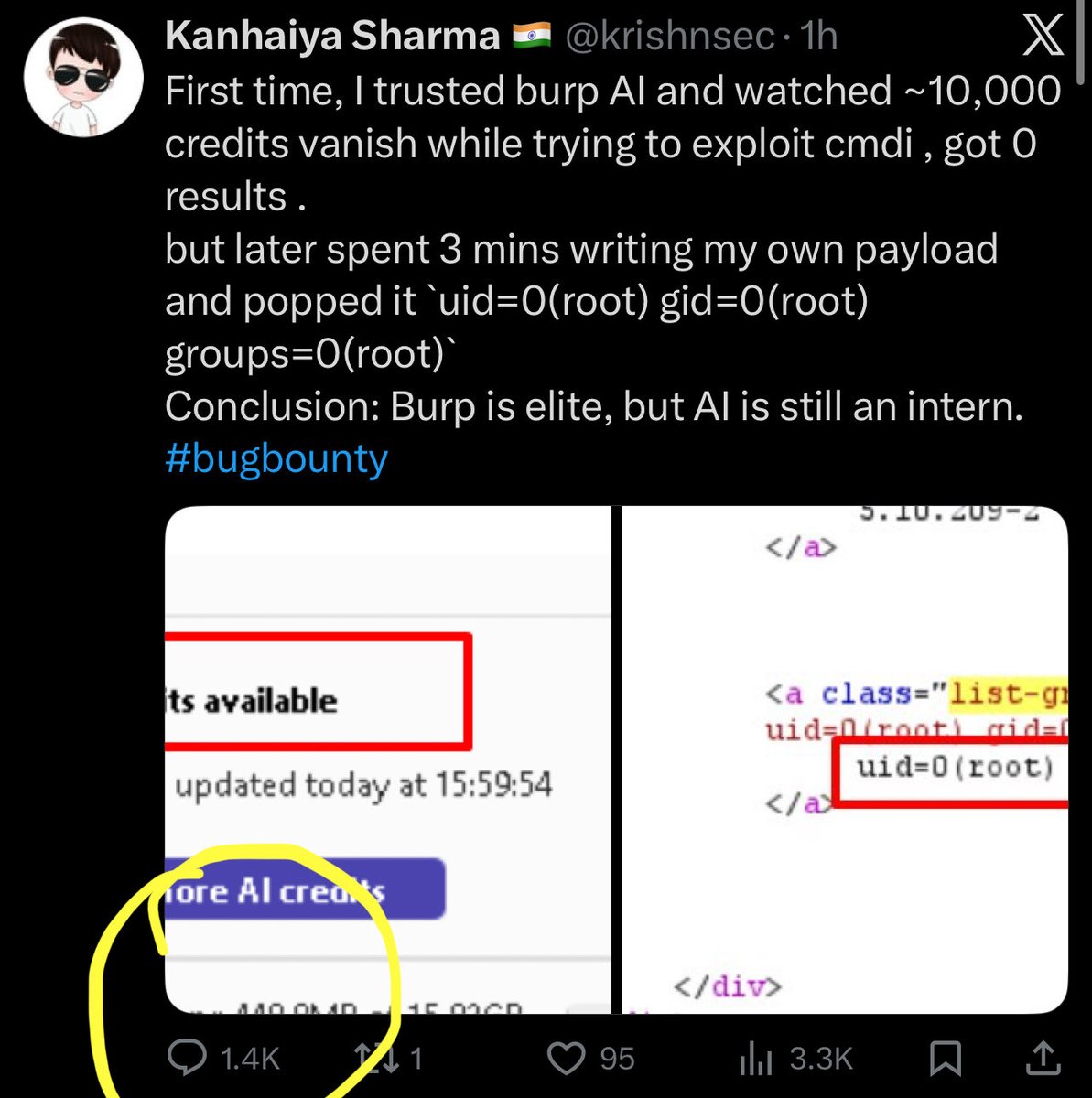
First time, I trusted burp AI and watched ~10,000 credits vanish while trying to exploit cmdi , got 0 results .
but later spent 3 mins writing my own payload and popped it `uid=0(root) gid=0(root) groups=0(root)`
Conclusion: Burp is elite, but AI is still an intern.
#bugbounty

English



Maniesh.Neupane retweetledi

Introducing my Bug Bounty Masterclass. 100% free.
I've made $2,000,000+ finding security bugs. I spent the last year turning my methodology into a complete blueprint.
4 hours of video - foundations, reconnaissance, web proxies, hands-on challenges, and certification.
Finish it in a weekend and start hacking real-world applications 🐞
English

Day TWO of FIVE days of celebrating our 2 year ARCANUM-VERSARY! @arcanuminfosec
3rd Giveaway = FOUR seats to our new course by @the_IDORminator "Zero to [BAC] Hero" !
👍 1 Like = 1 Entry!
♻️ 1 Share = 2 Entries!
Winners announced 1/21! Syllabus link below 👇
English
Maniesh.Neupane retweetledi

i've been hacked
and traced the malware's wallet to see how much money they actually made from this new exploit
(if you use Next.js/React, READ THIS!)
I woke up to a terrifying email from Hetzner: "Netscan Detected."
my server was blocked and a botnet was using my IP to attack others
i dug into the logs and what I found the anatomy of the attack:
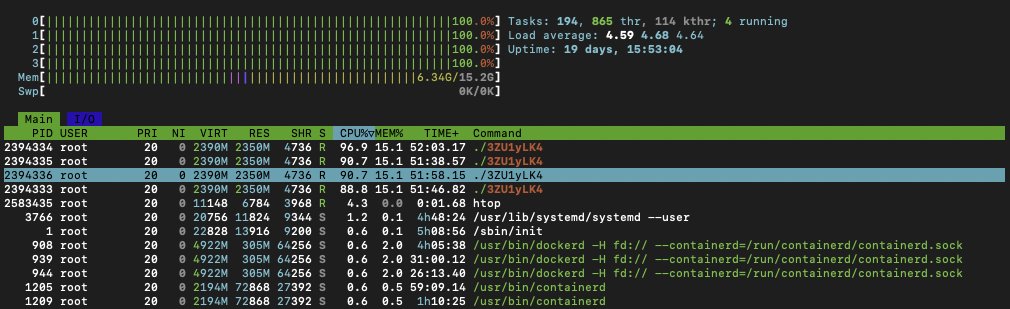
1) The Symptoms: I logged into htop and saw the mess:
- CPU usage: 361%
- A process named ./3ZU1yLK4 running wild
- Random connections to an IP in the Netherlands
my server wasn't serving my app anymore; it was mining crypto for someone else!
2) The Culprit: It wasn't a random SSH brute force. It was inside my Next.js container
the malware was sophisticated
it renamed itself nginxs and apaches to look like web servers
it even had a "killer" script that hunted down other hackers' miners to kill the competition
3) The "Root" Cause (literally): Probably the recent React/Next.js CVE-2025-66478 exploit was the entry point
(my project was running on "next": "15.5.4", behind cloudflare dns, but their recent fix didn't work apparently)
but the fatal error was mine: my Docker container was running as ROOT
Coolify deploys like this automatically when using Nixpacks, and I never changed it...
so because of USER root, the malware could install cron, systemd, and persistence scripts to survive reboots
meaning, it was able to infect my whole server, from a single Next.js docker!
4) The Forensics: I ran docker diff on the container - the hacker didn't just run a script, they installed a whole toolset..
- /tmp/apaches.sh (The installer)
- /var/spool/cron/root (The persistence)
- /c.json (The wallet config)
5) The Fix: I killed the container, scrubbed the host, and extracted the malware for analysis.
but the real fix is in the Dockerfile. if you are deploying Node/Next.js, DO NOT use the default (root), you must:
- RUN adduser --system nextjs
- USER nextjs
if you have Docker on ROOT and didn't update the exploited react version, you'll be hacked soon
check your containers NOW. Run: docker exec id
(or get the full list first: docker stats --no-stream)
If it says uid=0(root), you are one vulnerability away from being a crypto-miner host.
(it's easy to notice when hacked, it will be a command running on the top CPU%, using all your hardware resources)
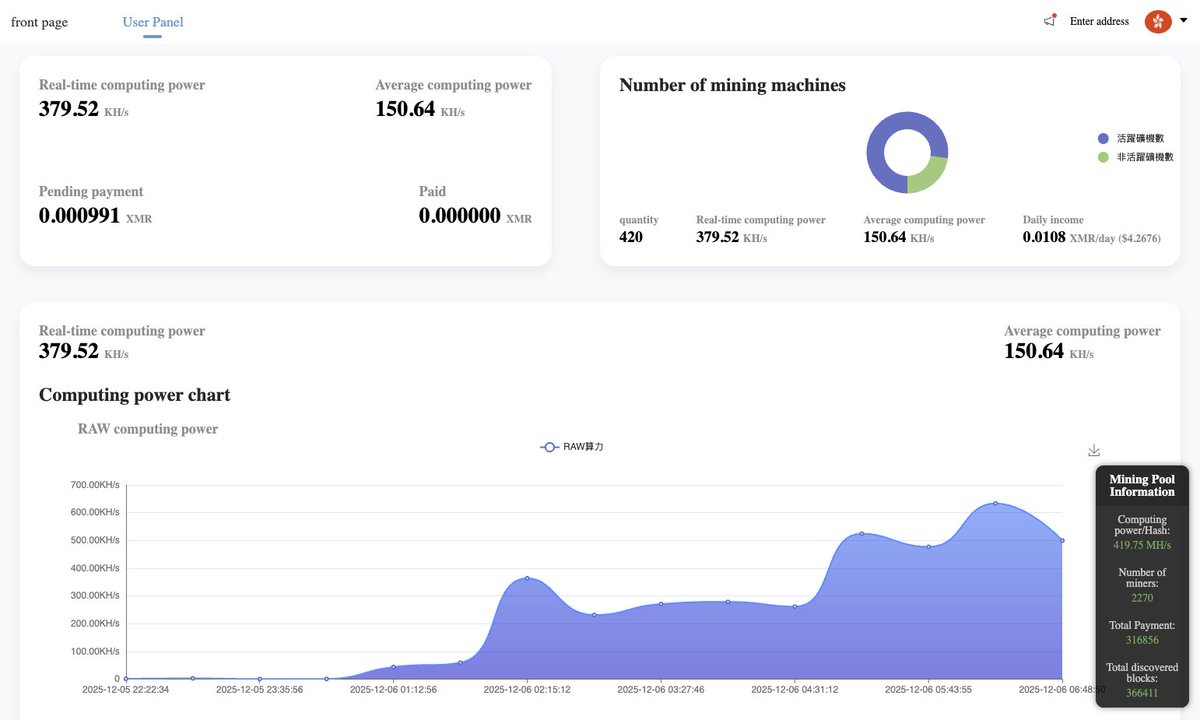
6) The Money: I dug deeper and recovered the config file (c.json)
- Wallet: A Monero (XMR) address: 831abXJn8dBdVe5nZ***
- Pool: auto.c3pool . org
and ofc i tracked the hacker’s wallet on the mining pool
7) The Scale: My server wasn't alone. It was just 1 of 415 active zombies in this botnet
they are burning the CPU of 400+ cloud servers... to earn...
guess how many millions?
$4.26/day
on the image attached you can see: "Total Paid: 0.00", meaning this campaign just started. I caught them on Day 1.
i also tracked back the server where they hosted the malware, and by inspecting the code, I found several comments in Chinese, so I guess that's their origin
im rebuilding from scratch on a fresh VPS. the lesson was expensive, but at least I caught it before the hosting nuked my account permanently...
PS: I have the IP for all the other machines mining with that malware, not sure how I can help them, but feel free to contact me if ur doing infosec
stay safe
English

Giveaway.
@TurvSec is sponsoring HackTheBox Academy giftcards. I've got 5 giftcards worth $50.
If you'd like a $50 giftcard for HackTheBox to do stuff, leave a comment below. Winners will be selected in 24 hours.
English

🚨 Doing a giveaway for my Blind XSS Masterclass
Most people think they know XSS, until they meet blind XSS, the kind that fires where you’ll never see it.
Same methods that helped me earn $250K+ from real reports. hhub.io/nahamsecbxss
🎁 Retweet and reply to enter.

English

We win 🥇 this, as a very elite team
Our team (Black Hat Cartel)
Me & @XHackerx007 & r3aper__
and for sure it was super hard challenging fighting against the other amazing team that get the win 🥇 as well (One P1) @krishnsec @0xMstar @MrSharmaX
Congratulations for us 🏆
bugcrowd@Bugcrowd
The Crowd always finds a way to surprise us 😈 After weeks of fierce competition, the crown is being shared between 𝑻𝒉𝒆 𝑩𝒍𝒂𝒄𝒌 𝑯𝒂𝒕 𝑪𝒂𝒓𝒕𝒆𝒍 and 𝑶𝒏𝒆 𝑷1, co-champions of this year’s Hacker Showdown: Mind Cathedral. 🫱🏆🫲 Collaboration came through BIG this year. That’s what makes the Bugcrowd community the best there is! 💥🧡
English

@dhakal__bibek @Hacker0x01 "remote code execution over our country" lol
English
Tweet, After a long time... Thanks @Hacker0x01 for having such a great employees, yep you guys really care about us. 💕

English

@ahmtbrt07 @samm0uda Apple is worst . For the Apple bug bounty you need whole patient at least 1 year or more than that
English

@samm0uda I'm currently considering Google or Apple, you might consider this.
English

Gen Z is spearheading a massive protest in Nepal against corruption in the KP Sharma Oli government and its recent move to restrict social media platforms. What began online has spilled onto the streets on Monday, with demonstrators clashing with police near Parliament.
Security forces responded with gunfire, leaving several protesters injured.
Thousands of young protesters flooded Kathmandu in what has been dubbed the 'Gen Z Revolution'.
Many breached restricted zones, breaking through police barricades. As the clashes escalated, police opened fire at multiple locations, prompting authorities to impose a curfew in the capital.
Read more: intdy.in/rzh7qf
#Nepal #NepalProtest #ITCard

English

Thanks to the awesome work by our team we can finally announce our official urlscan cli tool: urlscan.io/blog/2025/09/0… - Submit scans, run searches, find domains, get creative. Feel free to share your use-cases with us on X! Download on Github or homebrew.

English

after a long time, I decided to write a blog post about one of the old bugs I found in an Android app, which finally led me to achieve 0-Click Mass Account TakeOver
it's now published, you can read it here :
blog.voorivex.team/0-click-mass-a…
English

@nischalxdp @intigriti Thank you for the idea but it didn't help
English

@pwn4arn @intigriti Did you try using VPN or a different public address ?
I was once logged out of my yeswehack account similarly, logging in via a different IP solved the issue.
English

@intigriti I still can’t access my researcher account. It’s been over 3 days, and the password reset email isn’t coming through. Support ticket or teams hasn’t helped yet. Please look into this issue !
English