Sabitlenmiş Tweet

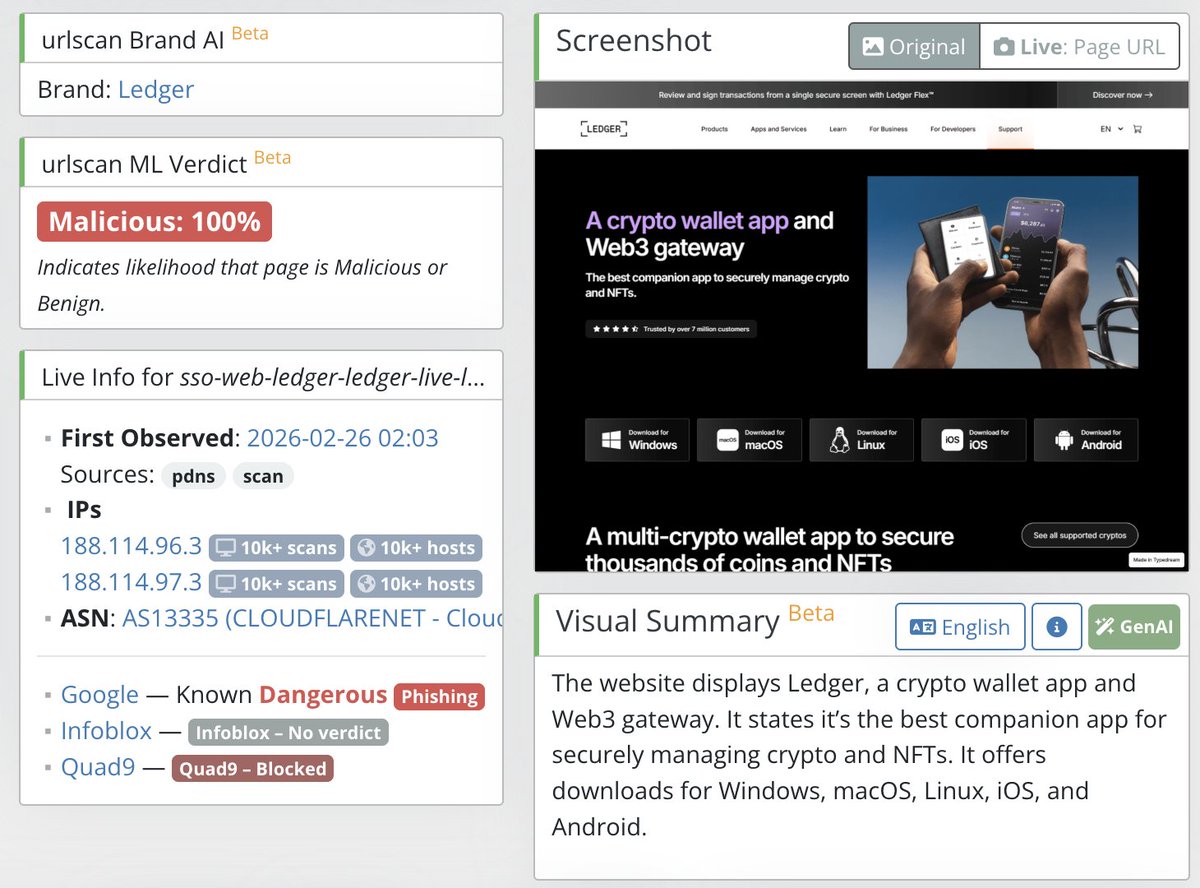
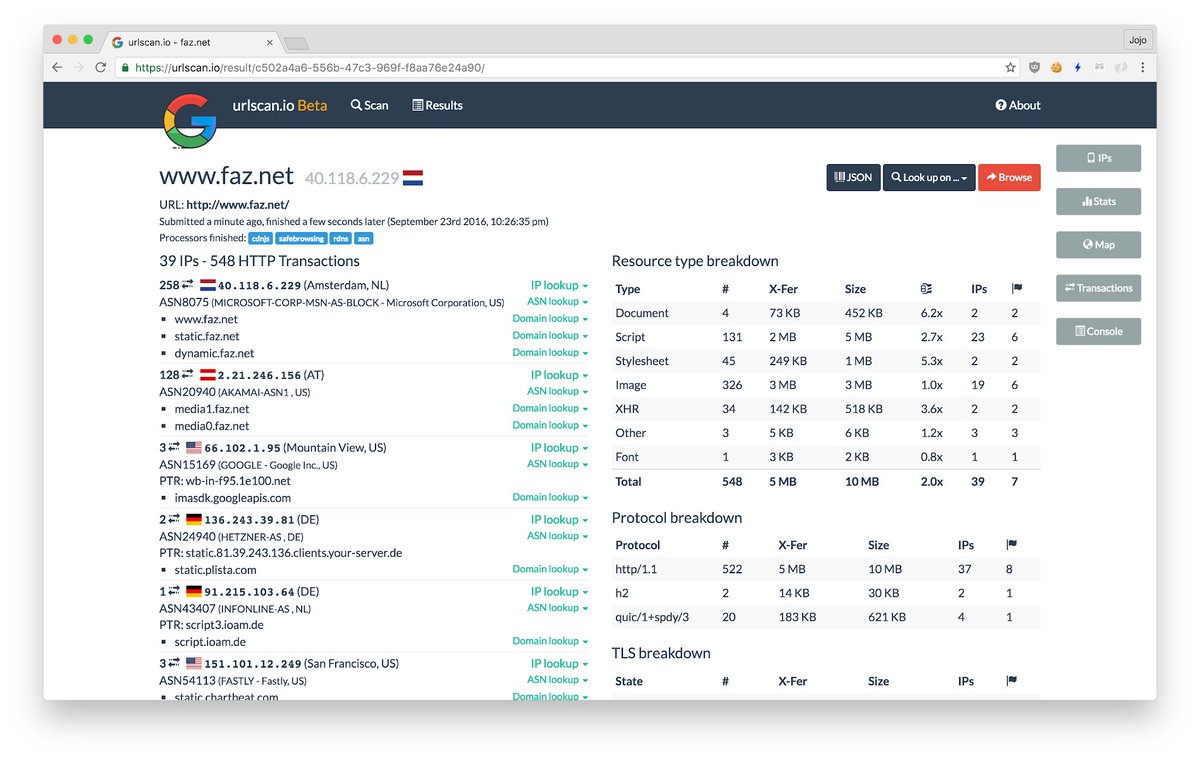
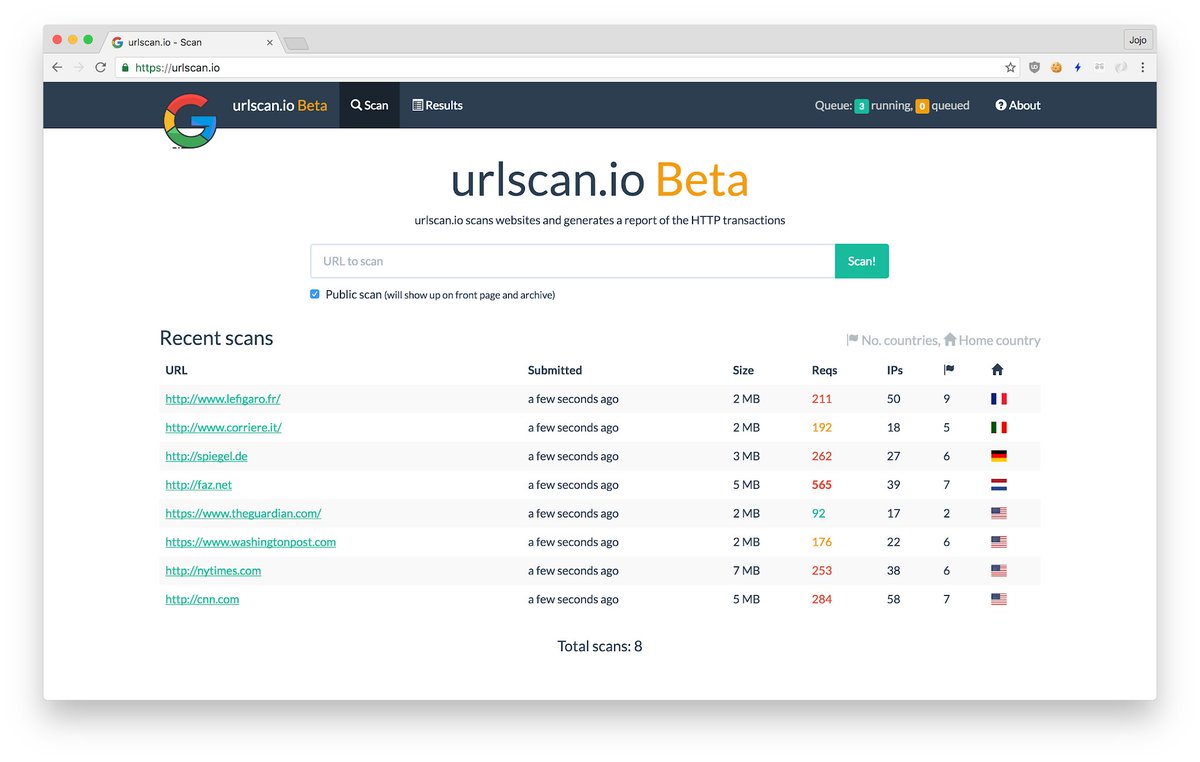
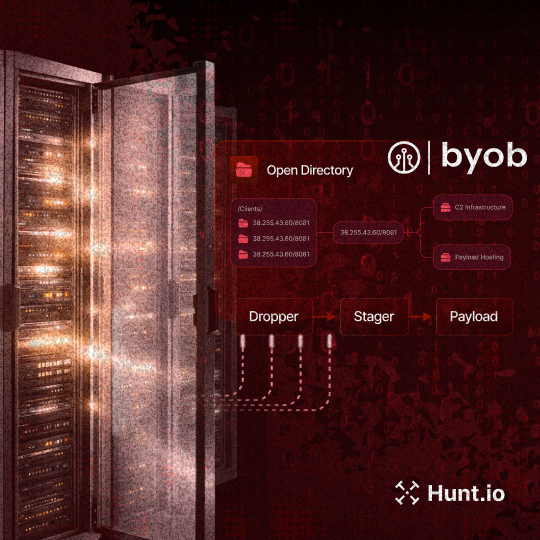
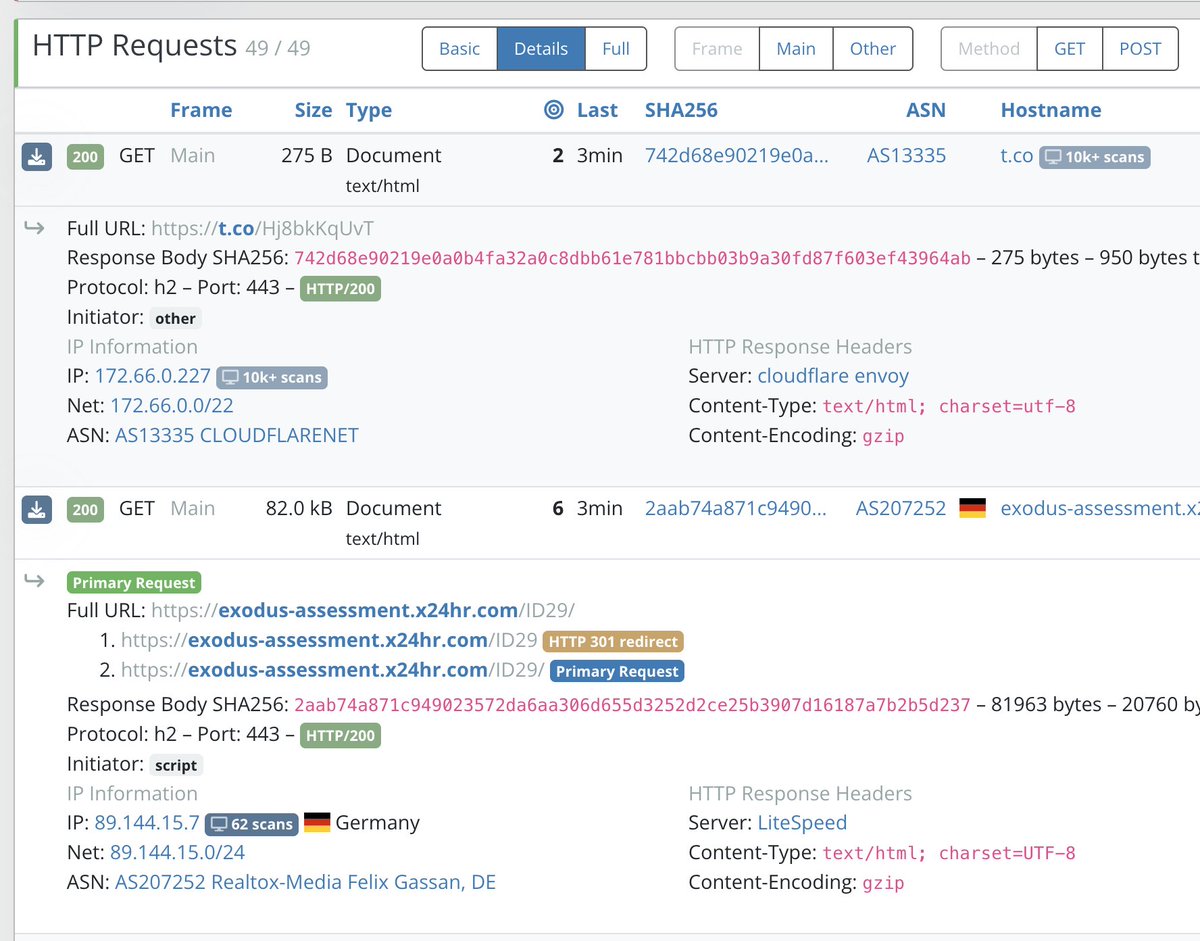
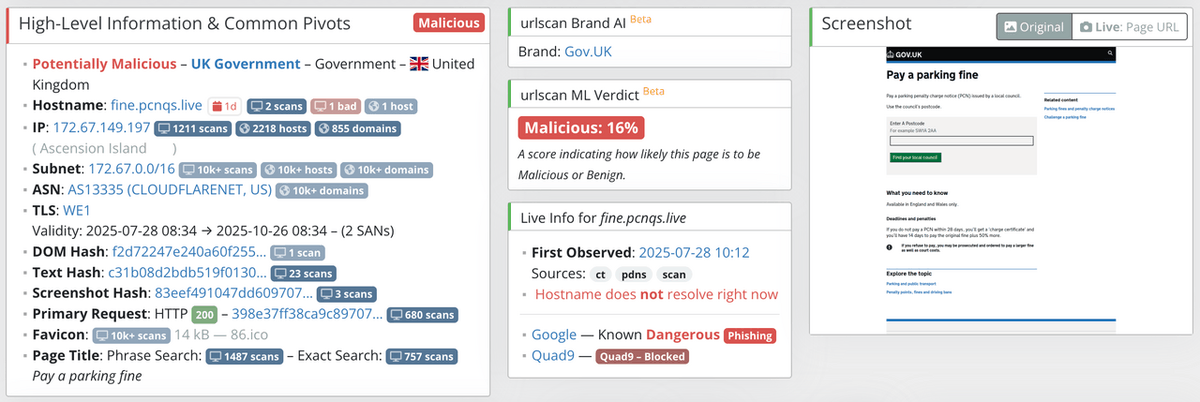
Today we're launching urlscan Brand AI within our urlscan Pro portal. Brand AI will visually examine websites to determine the name of the brand the website claims to represent, a more robust approach than text-based queries. Read the details in our blog: urlscan.io/blog/2025/07/3…
English