Reid H.
81 posts


Reid H.
@Reid0nly
Tier 3 SOC @AWNetworks | senior merch collector


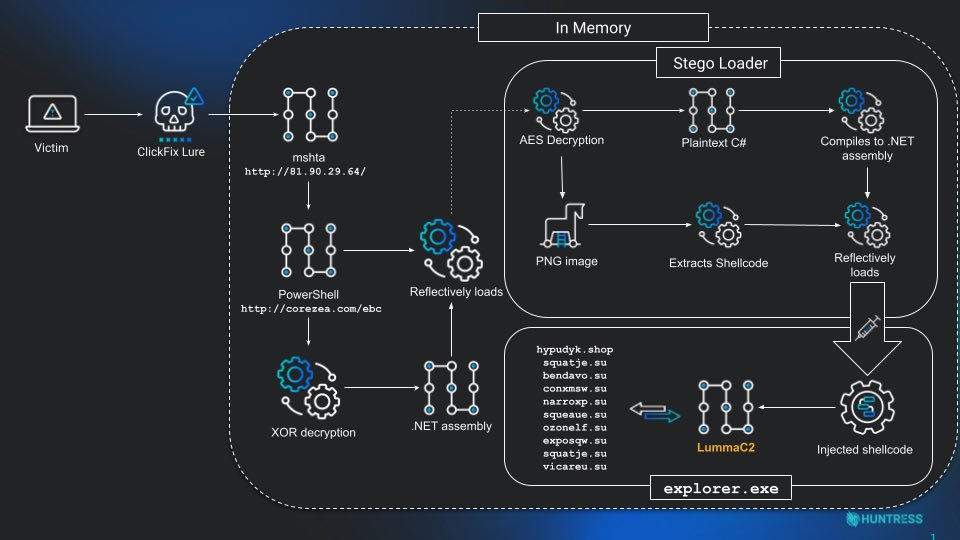
We are working it, sharing what we know as of now - gist.github.com/joe-desimone/3…


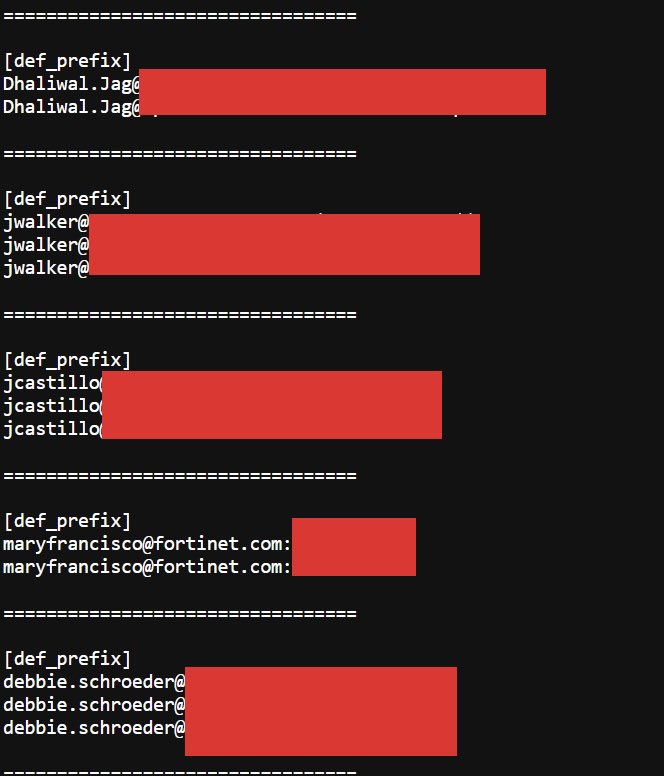
🚨 Fortinet Forticlient EMS CVE-2026-21643 - currently marked as not exploited on CISA and other Known Exploited Vulnerabilities (KEV) lists - has seen first exploitation already 4 days ago according to our data Attackers can smuggle SQL statements through the "Site"-header inside an HTTP request According to Shodan, close to 1000 instances of Forticlient EMS are publicly exposed. Track exploitation of this and other Fortinet honeypots 👉 console.defusedcyber.com/capabilities




@T3chFalcon Can say that DLP has not once prevented me from exfiltrating data from a network.





















Absolutely impossible to get a vendor to answer “how much does this cost?”