Shashwat Shah 🇮🇳 retweetledi

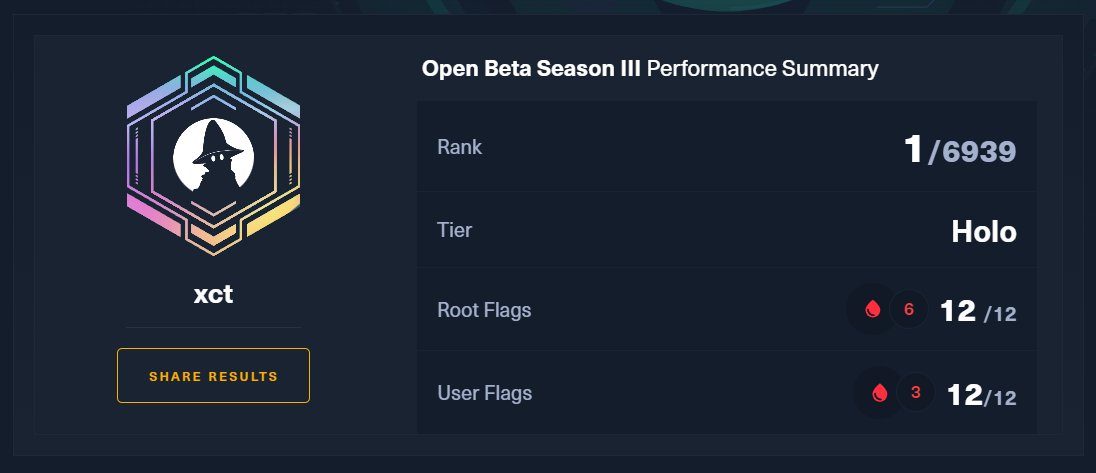
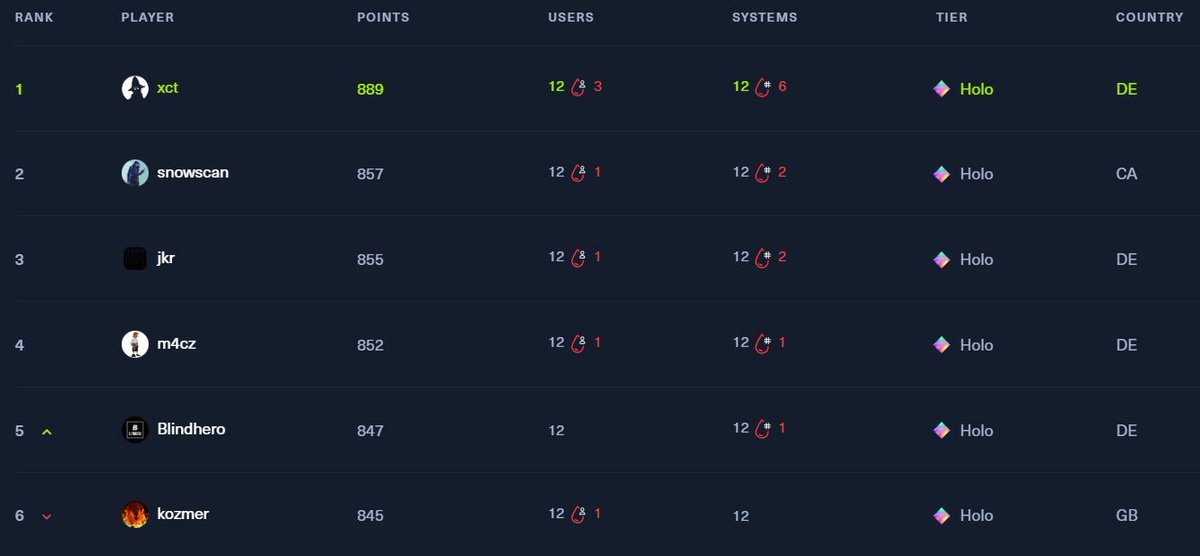
As promised... this is Loki Command & Control! 🧙♂️🔮🪄
Thanks to @d_tranman for his work done on the project and everyone else on the team for making this release happen!
github.com/boku7/Loki
English
Shashwat Shah 🇮🇳
241 posts


@0xEr3bus
CRT(O|E|M|L) | CAPE | Content Engineer @ HackTheBox | Windows Exploitation | Wannabe Red Teamer