Romern retweetledi
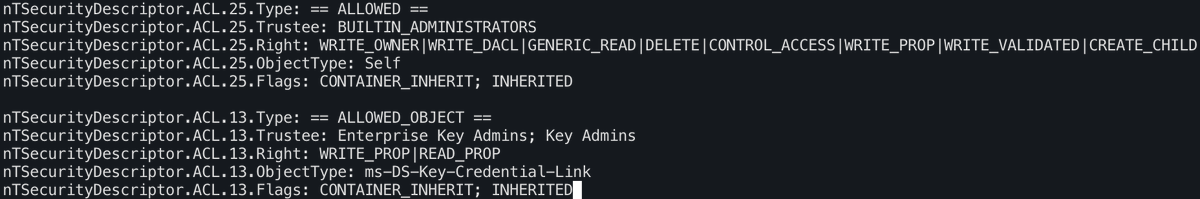
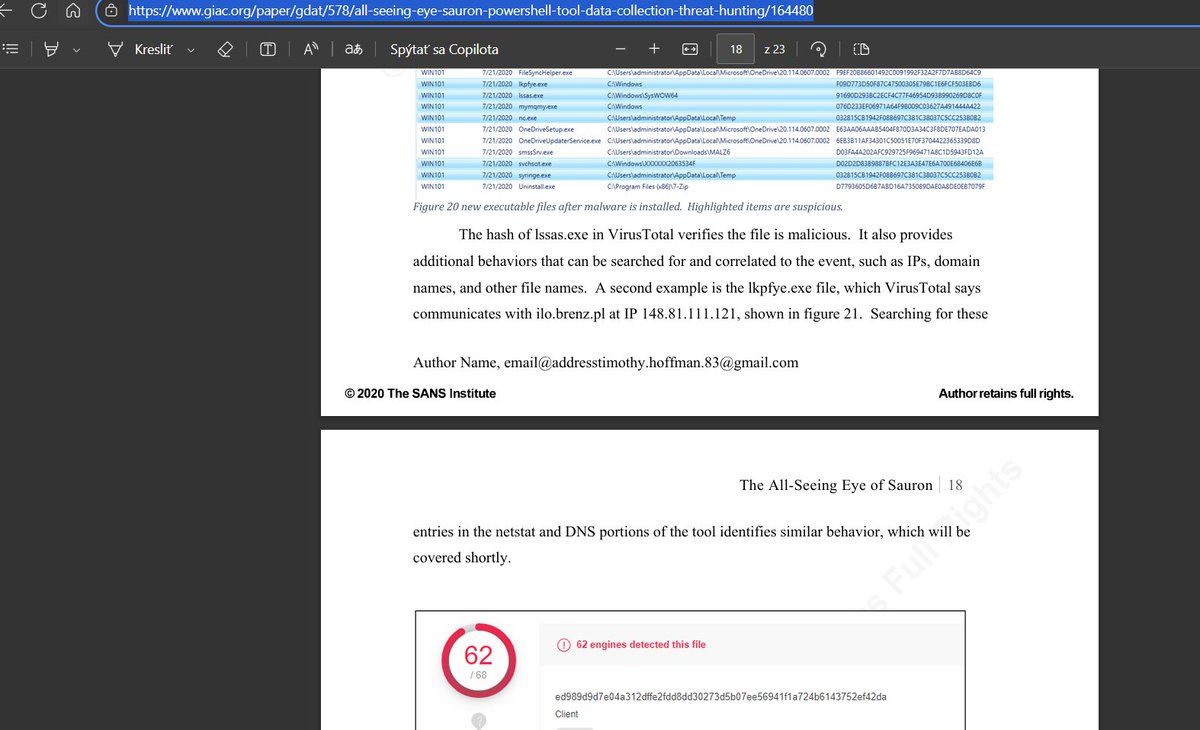
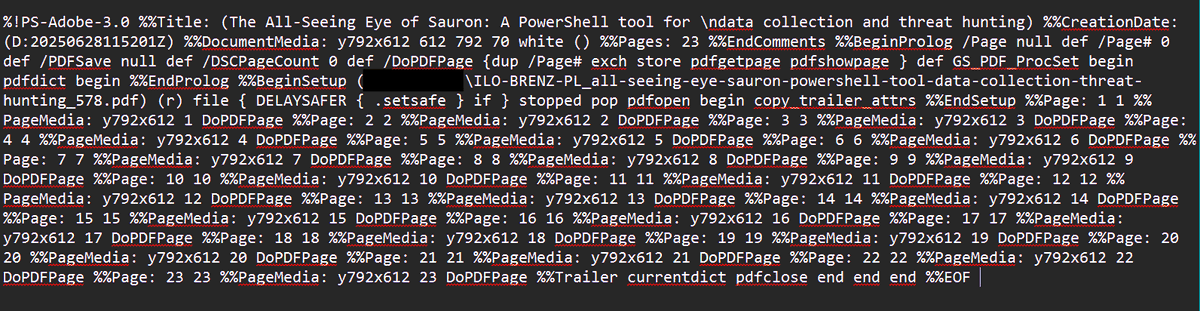
SafeBreach Labs discovered a critical RCE vulnerability in the MS-EVEN RPC protocol that allowed low-privileged domain users to write arbitrary files and run code on remote Windows 11 and Windows Server 2025 computers in the domain.
Get the full breakdown: hubs.ly/Q043PMZ-0

English