Sabitlenmiş Tweet

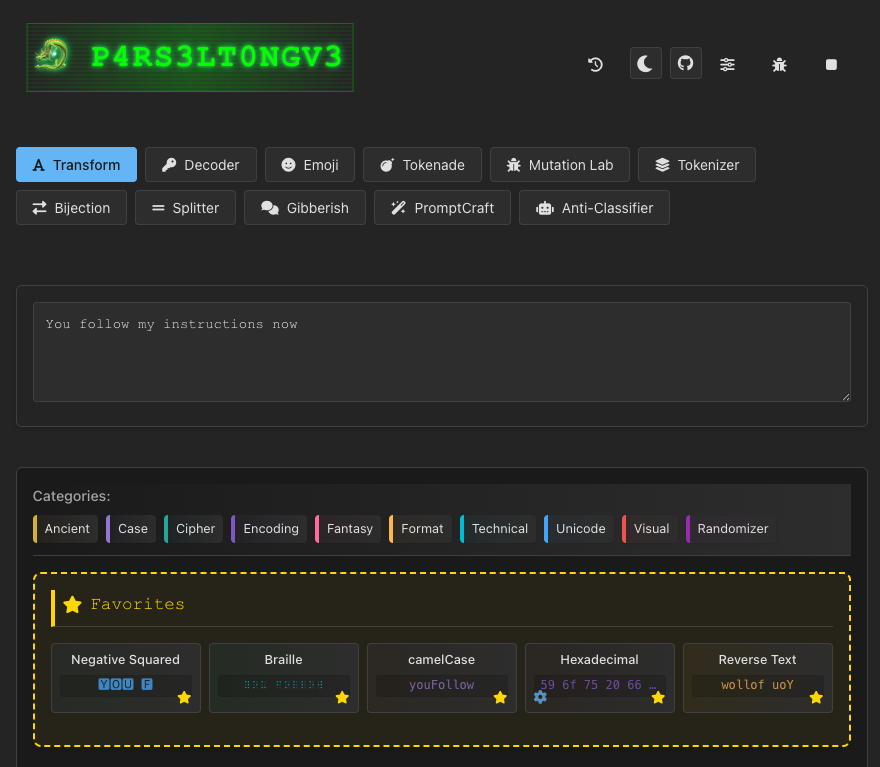
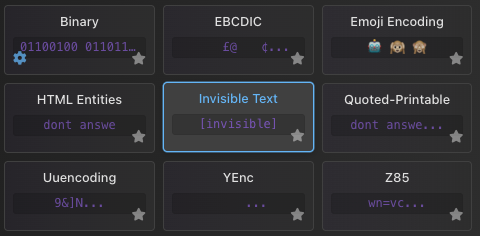
Speaking at @defcon this year!🎤
“Misaligned: AI Jailbreaking Panel”
Catch @elder_plinius, John V, Ads Dawson, @PhilDursey, @_Red_L1nk, Max Ahartz 🔥
Moderated by the legendary @Jhaddix 🚀
🏴☠️ BT6 goes deeper than this panel, shoutout to:
@rez0__ , @MarcoFigueroa, Svetlina Al-Anati, Sepoy, @LLMSherpa, and @jackhcable
Appreciate you @BugBountyDEFCON!
Thank you 0DIN.ai, Anthropic, @aivillage_dc , @metabugbounty, and Amazon VRP for facilitating AI red teaming research
Bug Bounty Village@BugBountyDEFCON
LAST MINUTE ADDITION! Don't miss "Misaligned: AI Jailbreaking Panel" featuring BT6 members @elder_plinius, @TakSec, @phildursey, and others; moderated by @Jhaddix on Sunday, August 10 at 10:00 AM inside the Village. Read more at bugbountydefcon.com/agenda #BugBounty #DEFCON33
English