rs-
5.2K posts





U.S. Marines recently proved that low-tech creativity can still defeat cutting-edge military artificial intelligence. In a DARPA field trial, a team of eight Marines was challenged to sneak past a sophisticated AI-powered detection system. Instead of relying on advanced stealth gear or electronic countermeasures, they turned to absurdly simple, almost cartoonish tactics and succeeded Some Marines cartwheeled and rolled across 300 meters of open ground. Others concealed themselves under ordinary cardboard boxes and slowly inched forward. One soldier even disguised himself as a small fir tree, shuffling gradually toward the objective. Remarkably, every Marine reached the target without ever triggering the AI sensors. The system had been trained extensively on normal human walking and running patterns, but it had no reference for these bizarre movements. Because the Marines’ actions fell completely outside the AI’s learned understanding of “human behavior,” they were effectively invisible to it. This exercise offers a timely lesson for the defense sector: no matter how advanced military AI becomes, it can still be outmaneuvered by human ingenuity, unconventional thinking, and old-fashioned manual tactics. This incident serves as a vital reminder for the defense industry that while AI is an incredibly powerful tool, it remains susceptible to creative human deception and the unpredictable nature of manual tactics. source: Scharre, P. (2023). Four Battlegrounds: Power in the Age of Artificial Intelligence. W. W. Norton & Company.

You trust your dependencies. But what if updates betray you? This attack compromises legitimate NPM publishers and replaces packages with malware—delivered at install or update. No phishing. No tricks. Just trust turned against you. That’s what makes supply chain attacks so dangerous. So how much do you really trust your package updates? #cybersecurity #supplychain #infosec

Interviewer: HTTPS encrypts everything. Then how do CDNs still cache content?





You can now enable Claude to use your computer to complete tasks. It opens your apps, navigates your browser, fills in spreadsheets—anything you'd do sitting at your desk. Research preview in Claude Cowork and Claude Code, macOS only.


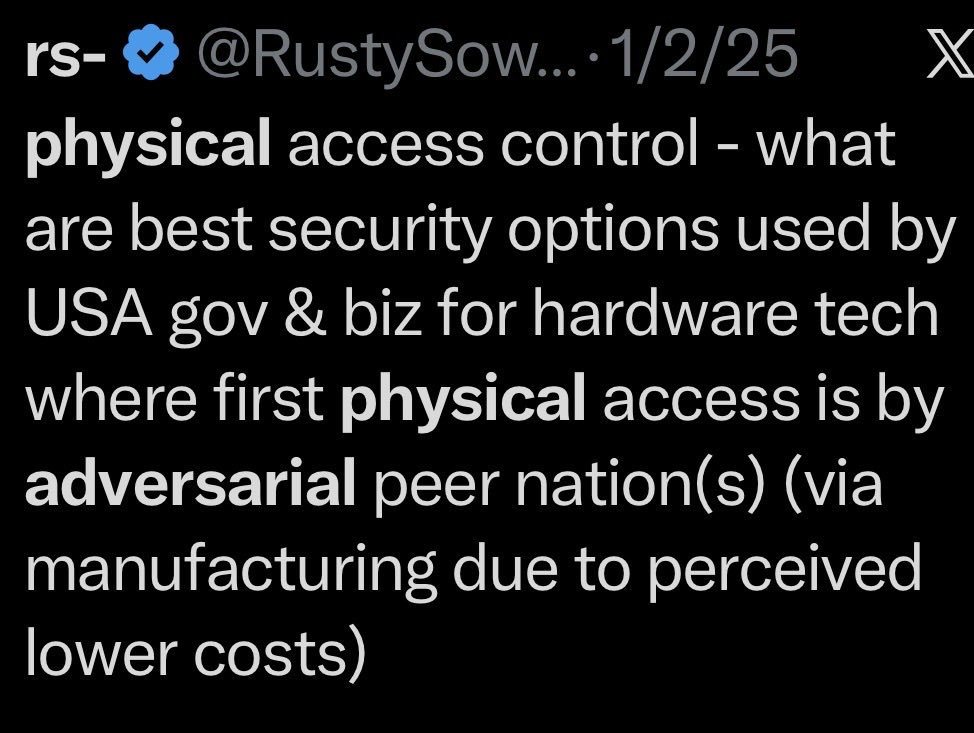
physical access control - what are best security options used by USA gov & biz for hardware tech where first physical access is by adversarial peer nation(s) (via manufacturing due to perceived lower costs) what are security options for ensuring onsite support for same hardware is performed by those not committed to adversarial peer nation

USA bans foreign-made consumer network routers, considering those produced outside the US a national security risk, and prohibits them from being imported or sold. China makes ~60% of them sold in the US. The official reason: foreign-made routers were used in several large cyberattacks on American infrastructure, including ones targeting energy grids and water systems. So now there will be no foreign routers. The ban doesn't say "Chinese routers". It says all foreign-made routers. Netgear, Eero, Google Nest -- all considered. Companies can apply for an exemption if they submit a detailed reshoring plan: where they'll build in the US, how much they'll invest, quarterly progress reports, a dedicated compliance officer -- just to sell a box that blinks green in your hallway.


The US bans all new foreign-made network routers engt.co/4bDF2AQ






The Delve stuff is bad, but all of these compliance platforms (Vanta, Drata, etc) have their "trusted auditors" they recommend. That is the core issue that corrupts this space.

Delve, a YC-backed compliance startup that raised $32 million, has been accused of systematically faking SOC 2, ISO 27001, HIPAA, and GDPR compliance reports for hundreds of clients. According to a detailed Substack investigation by DeepDelver, a leaked Google spreadsheet containing links to hundreds of confidential draft audit reports revealed that Delve generates auditor conclusions before any auditor reviews evidence, uses the same template across 99.8% of reports, and relies on Indian certification mills operating through empty US shells instead of the "US-based CPA firms" they advertise. Here's the breakdown: > 493 out of 494 leaked SOC 2 reports allegedly contain identical boilerplate text, including the same grammatical errors and nonsensical sentences, with only a company name, logo, org chart, and signature swapped in > Auditor conclusions and test procedures are reportedly pre-written in draft reports before clients even provide their company description, which would violate AICPA independence rules requiring auditors to independently design tests and form conclusions > All 259 Type II reports claim zero security incidents, zero personnel changes, zero customer terminations, and zero cyber incidents during the observation period, with identical "unable to test" conclusions across every client > Delve's "US-based auditors" are actually Accorp and Gradient, described as Indian certification mills operating through US shell entities. 99%+ of clients reportedly went through one of these two firms over the past 6 months > The platform allegedly publishes fully populated trust pages claiming vulnerability scanning, pentesting, and data recovery simulations before any compliance work has been done > Delve pre-fabricates board meeting minutes, risk assessments, security incident simulations, and employee evidence that clients can adopt with a single click, according to the author > Most "integrations" are just containers for manual screenshots with no actual API connections. The author describes the platform as a "SOC 2 template pack with a thin SaaS wrapper" > When the leak was exposed, CEO Karun Kaushik emailed clients calling the allegations "falsified claims" from an "AI-generated email" and stated no sensitive data was accessed, while the reports themselves contained private signatures and confidential architecture diagrams > Companies relying on these reports could face criminal liability under HIPAA and fines up to 4% of global revenue under GDPR for compliance violations they believed were resolved > When clients threaten to leave, Delve reportedly pairs them with an external vCISO for manual off-platform work, which the author argues proves their own platform can't deliver real compliance > Delve's sales price dropped from $15,000 to $6,000 with ISO 27001 and a penetration test thrown in when a client mentioned considering a competitor

CISA published an advisory on endpoint hardening after Stryker. The RBAC guidance is solid. Multi Admin Approval for Intune is not a complete solution either. An attacker with Global Admin can create the second approver account themselves. That is a five minute delay, not a defense. What actually stops this: no standing GA roles, PIM with fresh FIDO2 at activation, and a session revocation circuit breaker that fires the moment bulk wipes start. We have been on Handala/Stryker since March 12. Here is what CISA got right and what they missed. threathunter.ai/blog/cisa-got-… #Stryker #Handala #CISAAlert #IdentitySecurity #MDR