Jeff Schroeder
34.8K posts

Jeff Schroeder
@SEJeff
Linux and OSS Lover, breaker of distributed systems, OIF II Veteran, Security Engineer, Martial Artist, wannabe chef, and lifelong student. Tech is my passion




Afroman makes police officer cry hearing the songs he made about her being played in court 😂




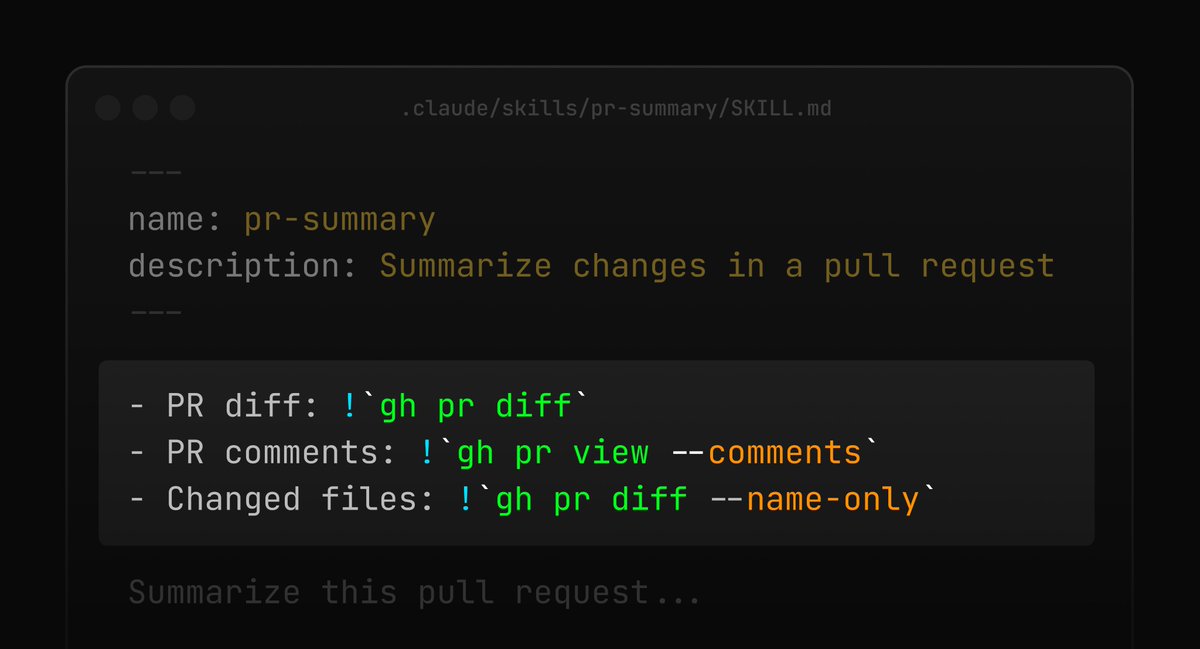
a credit card but instead of cash back you get Claude credits

🦔 Researchers at Aikido Security found 151 malicious packages uploaded to GitHub between March 3 and March 9. The packages use Unicode characters that are invisible to humans but execute as code when run. Manual code reviews and static analysis tools see only whitespace or blank lines. The surrounding code looks legitimate, with realistic documentation tweaks, version bumps, and bug fixes. Researchers suspect the attackers are using LLMs to generate convincing packages at scale. Similar packages have been found on NPM and the VS Code marketplace. My Take Supply chain attacks on code repositories aren't new, but this technique is nasty. The malicious payload is encoded in Unicode characters that don't render in any editor, terminal, or review interface. You can stare at the code all day and see nothing. A small decoder extracts the hidden bytes at runtime and passes them to eval(). Unless you're specifically looking for invisible Unicode ranges, you won't catch it. The researchers think AI is writing these packages because 151 bespoke code changes across different projects in a week isn't something a human team could do manually. If that's right, we're watching AI-generated attacks hit AI-assisted development workflows. The vibe coders pulling packages without reading them are the target, and there are a lot of them. The best defense is still carefully inspecting dependencies before adding them, but that's exactly the step people skip when they're moving fast. I don't really know how any of this gets better. The attackers are scaling faster than the defenses. Hedgie🤗 arstechnica.com/security/2026/…



Listen if someone leads with “I was an Army Ranger” the first question is, “oh cool what Battalion?” When they hesitate or look panicked you’ve learned all you need to know, because you see there are rangers and there are Rangers.







P-token is a great example of why Solana is killing it on perf. Everyone thought the solution to scale was overly creative architecture. Meanwhile, Solana coredev have been optimizing with incremental changes for years. 10% gain here, 30% there. Compounding, and battle tested.


TradFi has three moats protecting it from crypto. Cost. Speed. Finality. @solana just eliminated all three. > P-Token makes equity transfers nearly free. > @doublezero gives validators HFT-grade fiber latency. > Alpenglow settles transactions in under 200ms. The entire argument against on-chain equities… gone. Or am I missing something?