Sarah Isberg
2.3K posts


Sarah Isberg
@Sarah_Isberg
Research Scientist tech geek and MOM 😁



🤫




📱🔉







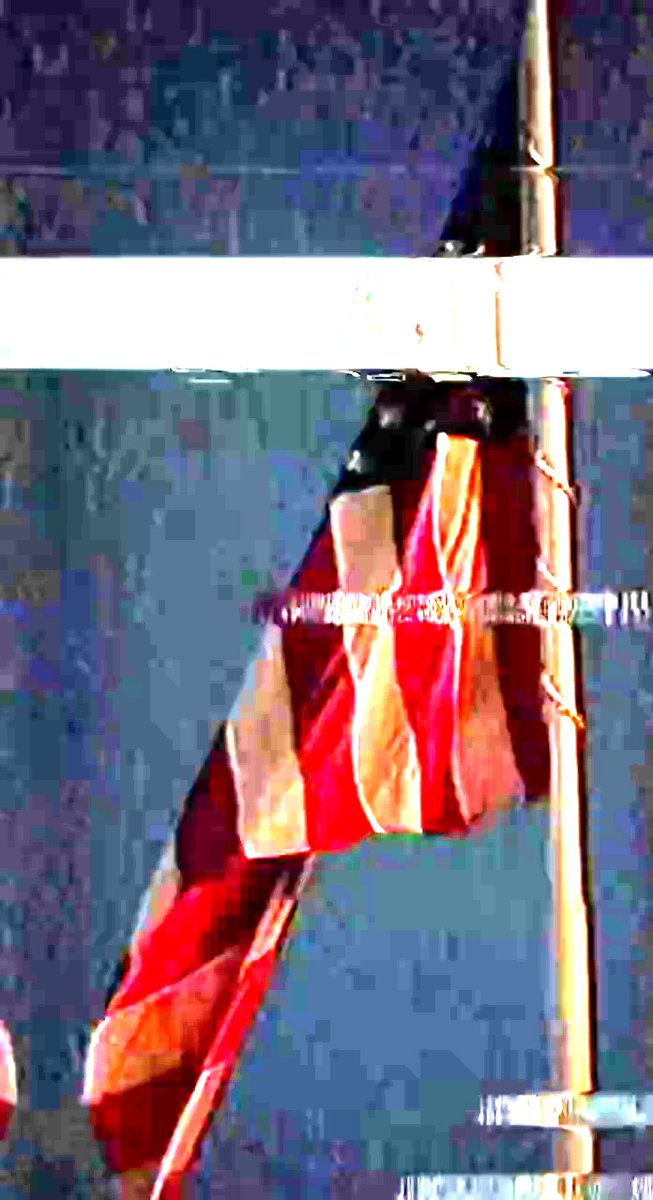

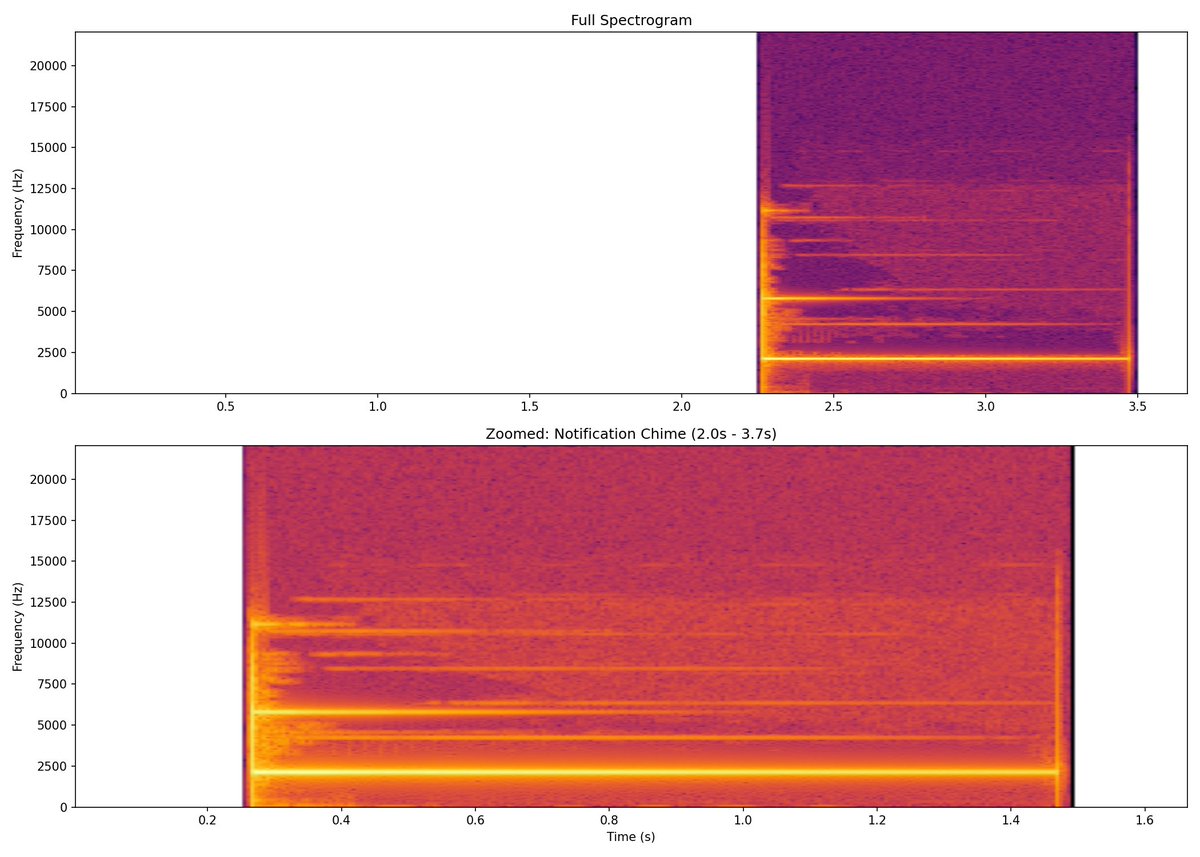
I pulled apart the @WhiteHouse video frame by frame. 214 frames, ~60fps, 3.6 seconds. Here's what's actually in it. The video was built with GPAC 2.2.1 (open source multimedia framework) before Twitter re-encoded it. Not a casual screen recording. The H.264 encoding has keyint=infinite and scenecut=0, meaning someone deliberately disabled keyframe insertion at scene transitions so you can't easily seek to the flag frames. That's intentional. Frames 1-163: Grayscale static. All three RGB channels are identical (pure monochrome noise). No LSB steganography detected in the frames Twitter's encoder left us, but re-encoding would destroy that anyway. Frames 164-165: The flag. When you brighten it 8x, it's a flag on a pole with VERTICAL red and white stripes and a blue star field. That's the Allied States of America flag from Jericho, a show about a shadow government nuking American cities and the country splitting apart. Two frames. Roughly 33ms of screen time. You'd never catch it at normal playback. Frames 166-171: Remnants of a phone UI. A notification bar strip at row 388 and a status bar at the top of frame. This thing was screen-captured from a phone. Frames 172-178: Horizontal banding pattern. Bright bands at irregular intervals across the frame. Not random noise. Looks like interlaced scan data from whatever source video was glitched up for the effect. Audio: iPhone notification chime starting at 2.26 seconds. Clean multi-harmonic tone. Spectrogram shows harmonics at ~1kHz, 2.5kHz, 5kHz, 7.5kHz, 10kHz, 12.5kHz. No hidden spectrogram images (Cicada 3301 style). No ultrasonic content. The Grok explanation that this is just a promo for the "Text USA to 45470" alert system doesn't explain why someone used GPAC to build a video with anti-seek encoding parameters and embedded a fictional secessionist flag from a nuclear apocalypse TV show in it. During an active military conflict. Whether this is an ARG, a psyop, or the most unhinged social media strategy in White House history, the Jericho flag was not an accident. Someone put it there on purpose.