SHERLOCK
6.6K posts


SHERLOCK
@sherlockdefi
Complete Lifecycle Security for Web3 Protocols
Katılım Şubat 2021
1.6K Takip Edilen26.3K Takipçiler
Sabitlenmiş Tweet

Why do leading Web3 teams choose Sherlock for auditing and security?
Sherlock compounds insight across collaborative audits, contests, bug bounties, and AI review. That leads to stronger findings, tighter fix validation, and fewer blind spots from pre-deploy review through production.
Connected security performs better than isolated point-in-time audits.
Stop wasting time with firms that dump a report on your desk and disappear.
English

Did you know? Sherlock AI now lets teams query specific vulnerabilities and see how new repos, branches, or commits may affect the greater protocol.
It becomes your security reference point for your team while building and shipping, so you're not starting from zero every time you launch an upgrade.
Watch the workflow:
> review findings
> query specific vulnerabilities
> understand downstream impact
> ship faster and better code
English

We’re co-hosting an invite-only event with @sherlockdefi and @Lombard_Finance on April 1.
We’re bringing builders across security, infrastructure, and DeFi to compare notes on what it takes to make onchain finance trustworthy at scale.

English

Meet the new Sherlock brand kit page.
Logos, marks, colors, and assets all in one place.
Everything you need to use the Sherlock brand right.
👉 sherlock.xyz/brand-kit
English

@MidasRWA Get started here 👇
audits.sherlock.xyz/bug-bounties/1…
English

THE RESOLV HACK AND LESSONS NOT LEARNT
This time, the damage was 100% self-caused and avoidable.
Resolv $50M + $30M mint was "unauthorised" meaning its private key was compromised, good old North Korean style. The wrong kind of Kimchi premium could have been easily prevented. This was not markets going wrong, prices dipping, collateral becoming useless. This was simply caused by incompetence, a classical shotgun into your foot style kind of stupidity.
Now, for 13 years, since 2013, when multisigs were added to Bitcoin, we have known how to avoid unauthorised private key usage:
- Not to use a private key in the first place, but use a multisignature wallet
- Use Hardware Security Module (HSM) with additional protections for the signing process
But why did Resolv do this?? It is not exactly rocket science.
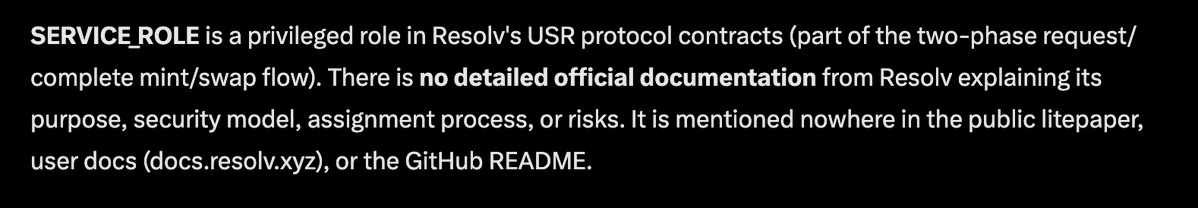
WHAT CAUSED THE UNAUTHORIZATION
"SERVICE_ROLE is a privileged role in Resolv's USR protocol contracts (part of the two-phase request/complete mint/swap flow). There is no detailed official documentation from Resolv explaining its purpose, security model, assignment process, or risks. It is mentioned nowhere in the public litepaper, user docs (docs.resolv.xyz), or the GitHub README."
(Quote by Grok)
AUDITED 18 TIMES
Why didn't Resolv catch this despite multiple audits? Because auditors, outside rare cases like @sherlockdefi do not care if the project gets hacked or not. They do not take any kind of responsibility for a deployed system. No skin in the game. Just cash payment, and "code looks good."
And even then, all of these auditors failed to flag this obvious thing. We have this SERVICE_ROLE that can mint unlimited amounts of our stablecoin, NOT DOCUMENTED ANYWHERE.
Come on, man! "This all-powerful private key in the system", but if you pay us our little fees, your SOFTWARE is good, we do not really care what happens afterwards. Just don't hold it wrong, m'kay?
INVESTED BY COINBASE, PRAISED BY STEAKHOUSE
Brian's seal of approval did not help either.
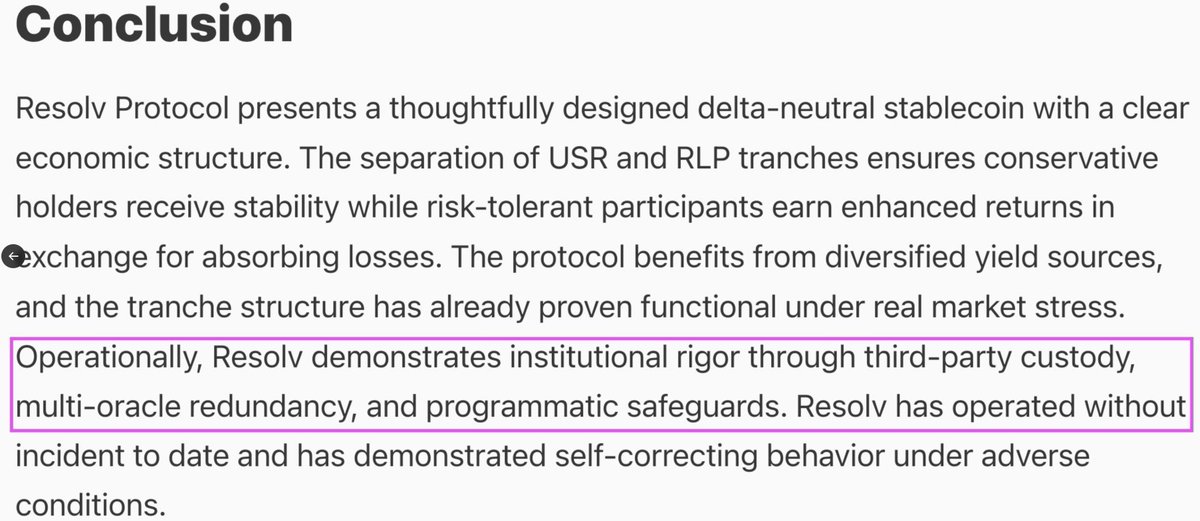
Only six days ago, Steakhouse wrote this in their Steakhouse Financial Insights:
"Operationally, Resolv demonstrates institutional rigor through third-party custody, multi-oracle redundancy, and programmatic safeguards. Resolv has operated without incident to date and has demonstrated self-correcting behavior under adverse conditions"
kitchen.steakhouse.financial/p/resolv-usr
This is so hand-wavey that it could be an ISO 9001 quality audit report as well, by failing to name the actual systems, processes, and their properties. "I went for lunch with the guys, and after a glass of French red wine, I was shure the system is good."
Third-party custody? Does this mean they used Fireblocks to secure the private key? A private key wallet written by an ex-Mossad agent is still a private key wallet, and even more risky because the key is likely stolen by your closed source software-as-a-service provider directly, as you cannot know how rotten their software is inside.
HOW TO AVOID THESE IN THE FUTURE
It is not that hard. Especially with $10M seed money and a peak of $500M at stake, one can easily do better.
1. Less privileged private keys
2. Use skin-in-the-game auditors
3. Transparency and follow the way of decentralised finance
HOW CAN YOU AS A DEFI USER TO AVOID THESE INCIDENTS
This is a tricky one.
The problem is that the underlying smart contracts are written in Solidity, a hodgepodge homebrew language. It's very hard to reason about the security properties of Solidity smart contracts. There are better languages, but it seems we are stuck with legacy Solidity. Despite Solidity's well-known flaws, there has been little actual effort to make it safer by looking past incidents and having someone paid to figure out how to pluck these holes at the language level.
AI is going to help a lot. Because we haven't been able to hold security auditors accountable, as their staked reputation doesn't seem to correlate with the hacks, the way forward is to get rid of security auditors. One day, and very soon, anyone will be able to point an AI agent to a complex deployed smart contract system, and it will give you a thumbs-up or thumbs-down report.
On this topic, I already did a small pilot here github.com/tradingstrateg… and Claude Code was able to pick a priviledged private key in one of our partners system on a deployed smart contract that should not have been there.
Ps. For HSM: You do not have any of the other commercial opaque crap to secure your critical private keys. If you are building security-critical smart contract systems that need an offchain highly trusted private key, you can use Google Cloud for this.
Here is our free and open source Ethereum signing module for Google Cloud: #module-eth_defi.gcloud_hsm_wallet" target="_blank" rel="nofollow noopener">web3-ethereum-defi.tradingstrategy.ai/api/core/_auto… - just remember to set the organisation policies accordingly.
Kudos to @zacodil and @omeragoldberg for the research.
English

“If you are trying to exploit an L2, you have many more ways to exploit the ZK side than the smart contract side. It just gets exploited less often because ZK is much more complex.”
@Mudit__Gupta, CTO of Polygon Labs, with Sherlock CEO @jack__sanford on AI bug finding, phishing as the starting point for many Web3 attacks, and where ZK risk may be underappreciated.
English


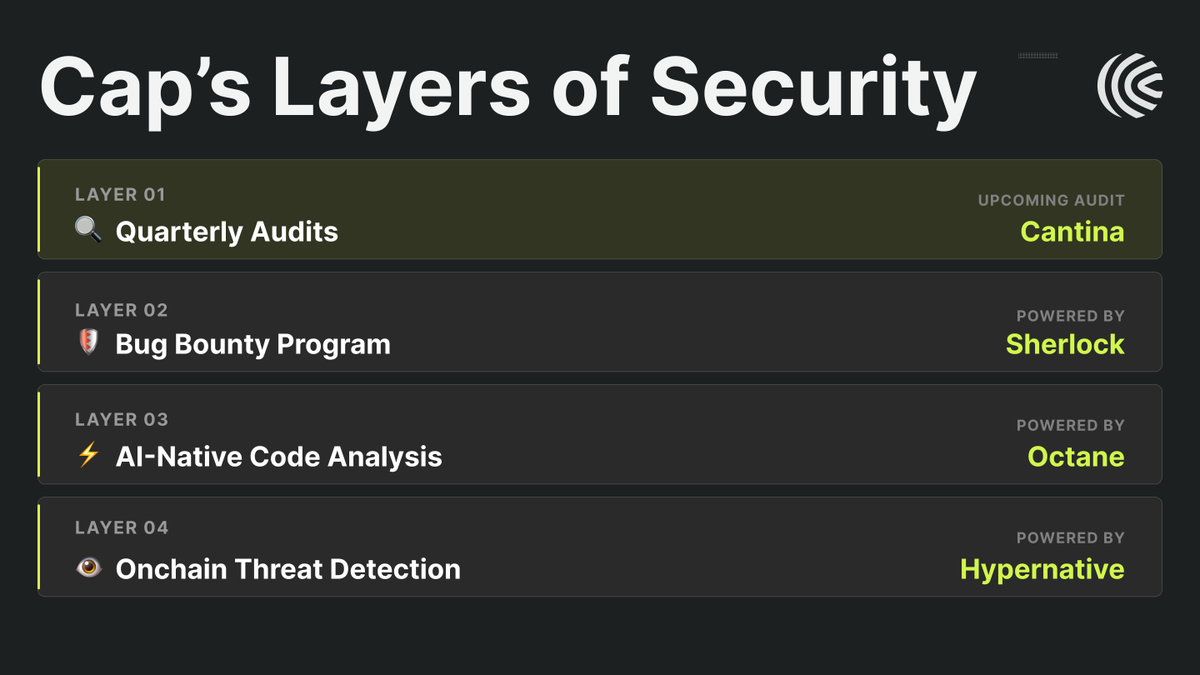
Security at Cap runs deep. Along with 6 completed audits, our layered, proactive approach includes:
🔒 Quarterly Audits (upcoming one from @cantinaxyz)
🕵️ @sherlockdefi bug bounty program
🛡️ @octane_security ai-native code analysis
🔍 @HypernativeLabs on-chain threat detection
English
SHERLOCK retweetledi

Who’s going to EthCC? 👀
On April 1 from 7:00–10:00 PM, Sherlock is hosting an invite-only side event in Cannes with @Lombard_Finance and @hyli_org.
Founders, leading protocol teams, senior researchers, and top auditors coming together for a night of sharp conversation, drinks, and a panel worth showing up for.
If you’re in Cannes for EthCC, request to join here: luma.com/397vh9td
English

The firms behind the security of billions dollars on DeFi just went through every line of our code. We gave them full access and told them to break it.
They couldn't.
✓Full audit @AsymptoticTech @MoveBit_
✓Formal verification @AsymptoticTech
✓Penetration test @MoveBit_
✓Audit contest @sherlockdefi
English

We just published the full Aave x Sherlock case study on our brand new case studies section of our website.
Read it here 👇 sherlock.xyz/case-studies/a…
English

The @aave team partnered with Sherlock across the V4 upgrade through three major phases: a multi-phase collaborative audit with Blackthorn, a $365K audit contest, and a bug bounty to protect live code after launch.
For one of the biggest architectural shifts in Aave’s history, the margin for missed issues was basically zero.
Sherlock was brought in to go deeper on the parts of V4 that were entirely new, especially the Hub-and-Spoke architecture + risk premium system.

English