Stephen Michael
1.1K posts

Stephen Michael
@Stephenswe_
Tech (Data scientist & Engineer) | Software Engineer || Health (Optometrist) || Business and founder @timelessfolioHq
Katılım Mayıs 2022
1.7K Takip Edilen422 Takipçiler

I’ve officially completed the @AltSchoolAfrica Front-End track. Beyond the code, this was about mastering scalable architecture and user-centric design.
I’m ready to bring these skills to a high-growth team in Fintech, HealthTech, or EdTech.
#Baraka25 #Frontend #Altschool


English

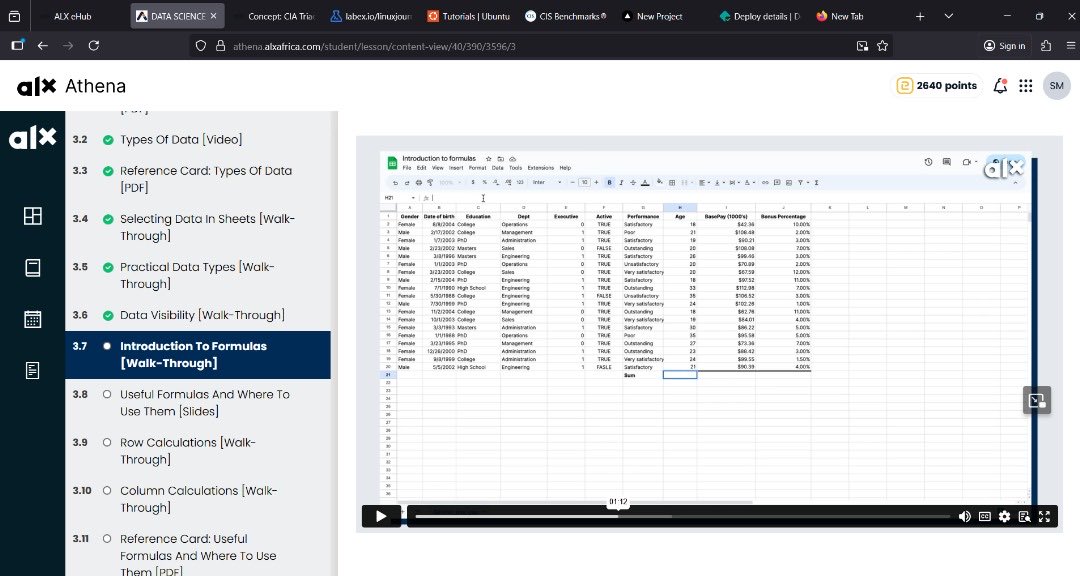
Documenting my Data Science & Engineering journey with @alx_africa
Committing to 100 days of learning, building, and sharing 📊🛠️
Follow along as I grow, tackle challenges, and document everything.
Let’s get better every day 💪
#100DaysOfData #DataScience #DataEngineering #ALX

English
Stephen Michael retweetledi
Stephen Michael retweetledi

Excel + SQL + Power BI = Data Analytics
Excel + Financial Modeling = Financial Analysis
Excel + Dashboarding = Business Intelligence
Excel + A/B Testing + KPI Tracking = Product Analytics
Excel + Google Analytics + Reporting = Marketing Analytics
Excel + Sales Data + Forecasting = Sales Analysis
Excel + HR Metrics + Workforce Planning = HR Analytics
Excel + Risk Modeling + Scenario Analysis = Risk Analysis
Excel + Investment Analysis + Valuation = Investment Analysis
Excel + CRM Data + Performance Tracking = Customer Analytics
Excel + Project Tracking + Resource Allocation = Project Management
Excel can literally make you rich
English
Stephen Michael retweetledi
Stephen Michael retweetledi

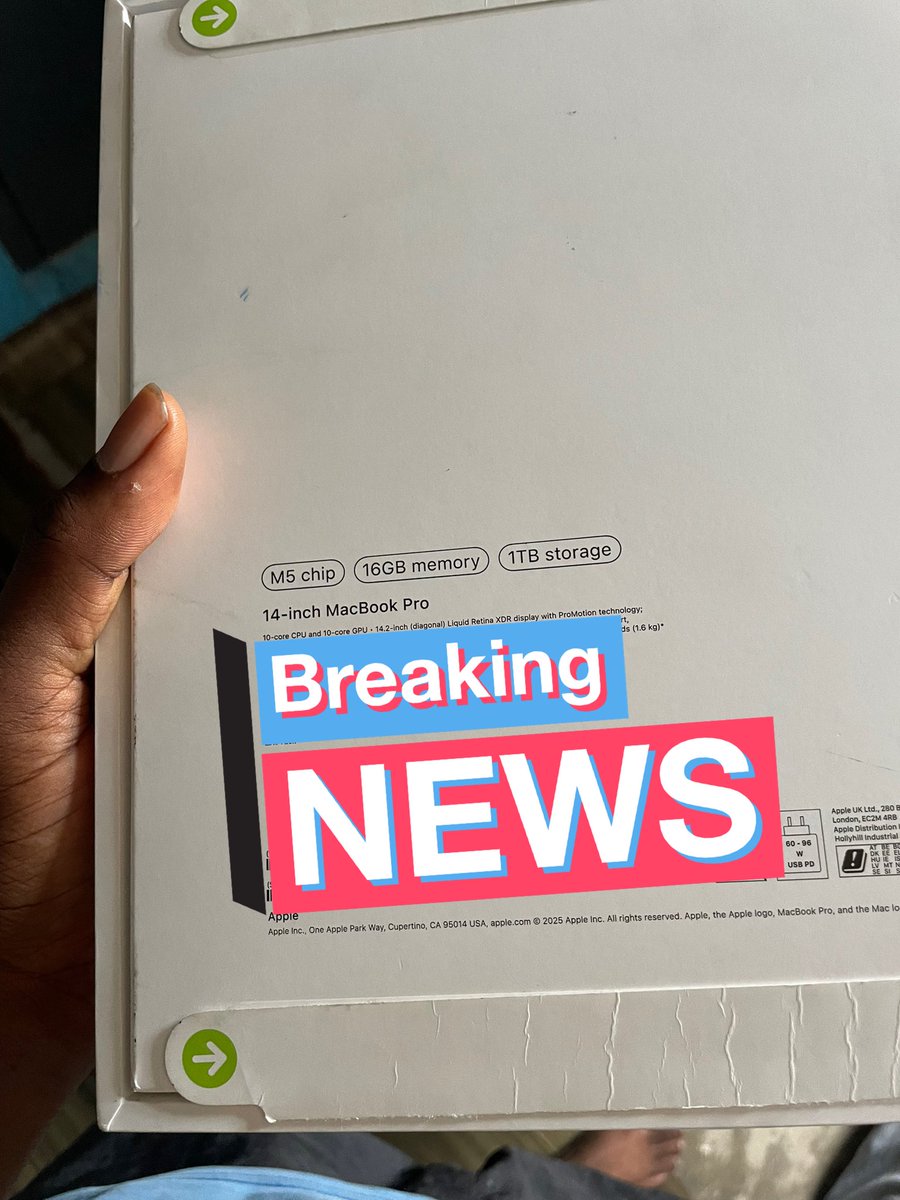
14inch M5 2025 MacBook Pro 🚀
Congratulations to me 🎉


Abiola Azeez (Lorenzo)@darnyy_abiola
an M5 in this economy?
English

I thought you guys said data analysis was easy ?
Please aside importing a data set what else is easy here? 😤
#DataScience #dataanlayst #dataEngineer
English
Stephen Michael retweetledi
Stephen Michael retweetledi

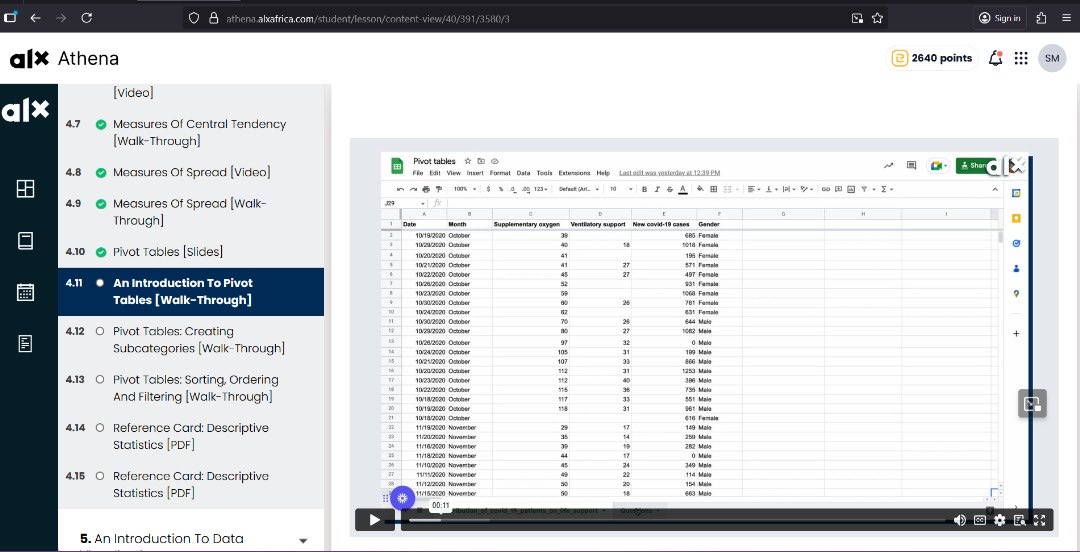
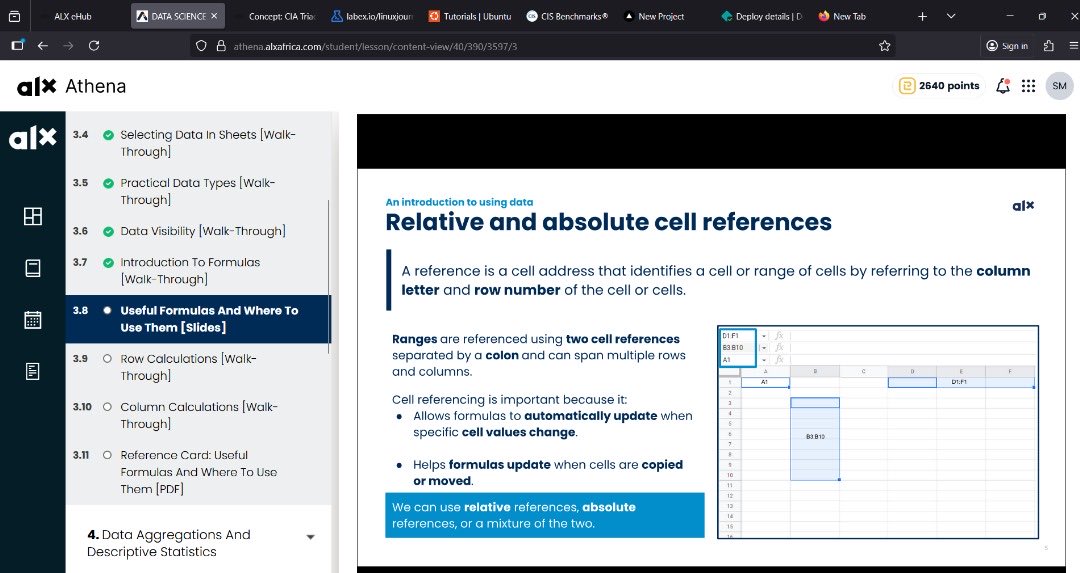
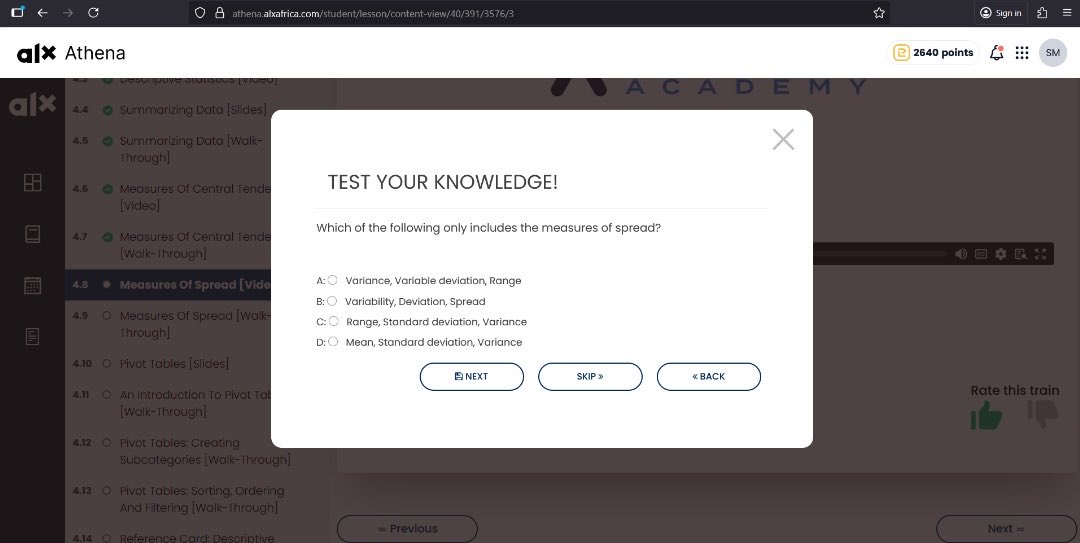
Deep dive into #DataScience fundamentals with @alx_africa
Learning how Measures of Spread (Variance, StDev) reveal data consistency, not just the average. Also, mastering spreadsheet power tools: Absolute/Relative Cell References and essential Pivot Tables
#datascience
English
Stephen Michael retweetledi

Cybersecurity Developer Learning Roadmap
|-- Foundations of Cybersecurity
| |-- Understanding Cyber Threats & Attack Vectors
| |-- Principles of Confidentiality, Integrity & Availability (CIA Triad)
| |-- Types of Cyber Attacks: Malware, Phishing, DDoS, MITM
| |-- Security Policies, Standards & Best Practices
| |-- Basics of Networking, Firewalls & VPNs
|-- Networking & System Security
| |-- TCP/IP, DNS, HTTP/HTTPS & OSI Model
| |-- Network Scanning & Packet Analysis (Wireshark, Nmap)
| |-- Intrusion Detection & Prevention Systems (IDS/IPS)
| |-- Secure Network Design & Segmentation
| |-- Managing Firewalls, Proxies & Access Controls
|-- Operating System & Application Security
| |-- Windows, Linux & macOS Security Fundamentals
| |-- File System Permissions & Process Management
| |-- Patch Management & System Hardening
| |-- Secure Software Development Lifecycle (SSDLC)
| |-- Application Sandboxing & Virtualization
|-- Cryptography & Data Protection
| |-- Symmetric & Asymmetric Encryption
| |-- Hashing & Digital Signatures
| |-- Public Key Infrastructure (PKI) & SSL/TLS
| |-- Secure Key Management Practices
| |-- Data Encryption at Rest & in Transit
|-- Web & API Security
| |-- OWASP Top 10 Vulnerabilities
| |-- Cross-Site Scripting (XSS), CSRF, SQL Injection
| |-- API Authentication & Authorization (OAuth2, JWT)
| |-- HTTPS & Secure Headers Configuration
| |-- Input Validation & Data Sanitization
|-- Ethical Hacking & Penetration Testing
| |-- Footprinting & Reconnaissance Techniques
| |-- Vulnerability Assessment Tools (Nessus, OpenVAS)
| |-- Exploitation Frameworks (Metasploit, Burp Suite)
| |-- Social Engineering & Phishing Simulations
| |-- Reporting & Mitigation Strategies
|-- Endpoint & Cloud Security
| |-- Endpoint Detection & Response (EDR) Solutions
| |-- Anti-Malware & Threat Containment Techniques
| |-- Securing Cloud Services (AWS, Azure, GCP)
| |-- Cloud Access Security Brokers (CASB)
| |-- Identity & Access Management (IAM) in Cloud
|-- Security Operations & Incident Response
| |-- Security Information & Event Management (SIEM)
| |-- Log Analysis & Threat Detection
| |-- Incident Response Lifecycle
| |-- Digital Forensics & Evidence Preservation
| |-- Threat Hunting & Malware Analysis
|-- Risk Management & Compliance
| |-- Risk Assessment Frameworks (NIST, ISO 27001)
| |-- Governance, Risk & Compliance (GRC) Concepts
| |-- Data Privacy Regulations (GDPR, HIPAA, PCI DSS)
| |-- Business Continuity & Disaster Recovery Plans
| |-- Audit & Security Posture Management
|-- Advanced Topics in Cyber Defense
| |-- Zero Trust Security Architecture
| |-- Threat Intelligence & Automation
| |-- Security Orchestration (SOAR)
| |-- AI & Machine Learning in Threat Detection
| |-- Cybersecurity for IoT & Industrial Systems
|-- Real-World Projects & Practice
| |-- Setting Up a Home Lab for Ethical Hacking
| |-- Penetration Testing Simulations
| |-- Web Application Vulnerability Testing
| |-- Cloud Security Assessment Projects
| |-- Developing Secure Applications End-to-End
|-- Continuous Learning & Certifications
| |-- CompTIA Security+, CEH, CISSP, OSCP
| |-- Cybersecurity Blogs, Podcasts & Forums
| |-- Open Source Security Tools Contribution
| |-- Capture the Flag (CTF) Challenges
| |-- Staying Updated with Emerging Threats
Get the Cybersecurity Developer Projects Ebook here: codewithdhanian.gumroad.com/l/tocvib
This ebook provides hands-on cybersecurity projects, ethical hacking labs, and defensive strategies to help you master real-world security practices from beginner to expert level.

English

𝗣𝗮𝗶𝗱 𝗖𝗼𝘂𝗿𝘀𝗲 𝗙𝗥𝗘𝗘 (PART - 1)
1. Artificial Intelligence + Data Analyst
2. Machine Learning + Data Science
3. Cloud Computing + Web Development
4. Ethical Hacking + Hacking
5. Data Analytics + DSA
6. AWS Certified + IBM COURSE
7. Data Science + Deep Learning
8. BIG DATA + SQL COMPLETE COURSE
9. Python + OTHERS
10 MBA + HANDWRITTEN NOTES
(72 Hours only ) Cost About - $500
To get FREE: -
1. Follow (So I can DM you)
2. Like & retweet
3. Reply " Send "

English