Stijn Volckaert
180 posts

Stijn Volckaert
@StijnVolckaert
Associate Professor @KU_Leuven @DistriNet. Working on Systems Security. Anti-Cheat Developer. Ethical Hacker. Maintainer of Unreal Tournament for OldUnreal.


To prevent exploitation of these issues, disable the ut2004:// URI handler during installation of "OldUnreal"



Unreal Tournament 2004






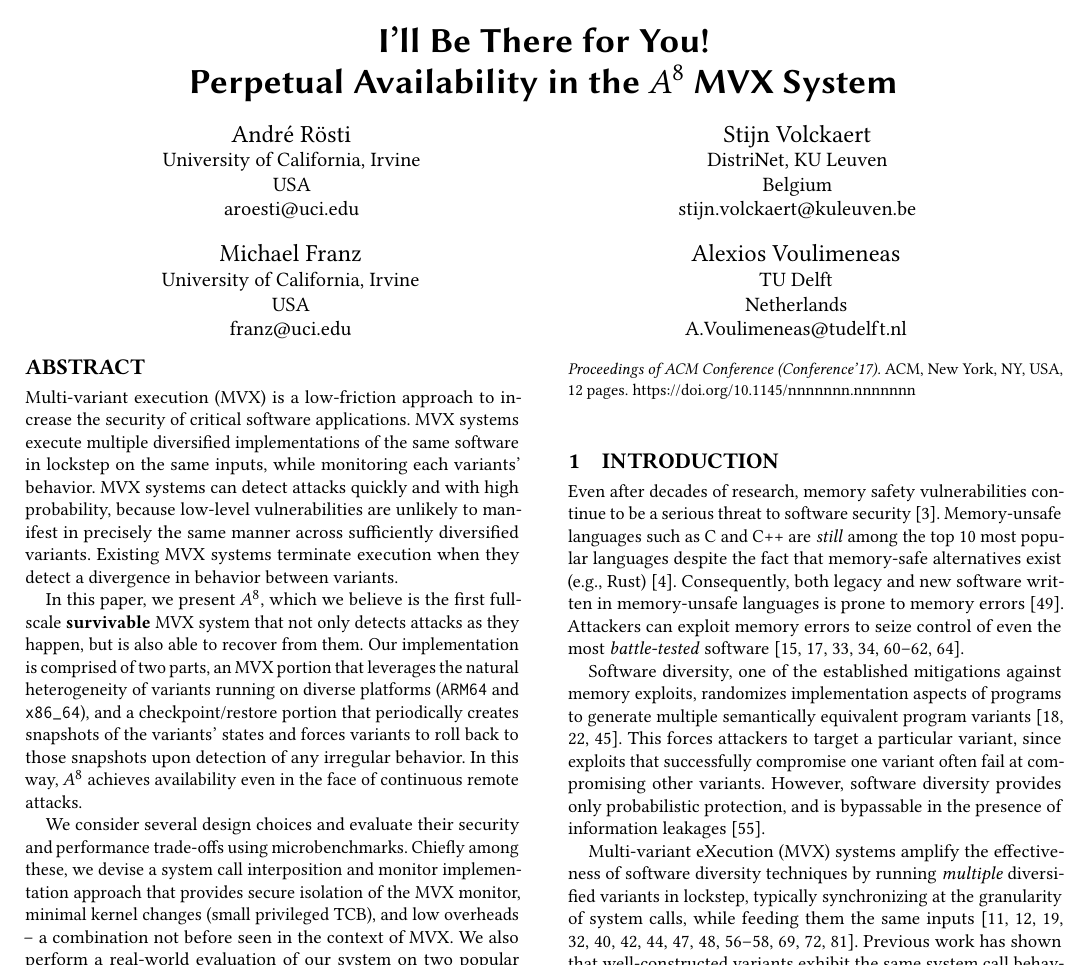
Congratulations to this year's second #ACSAC2024 distinguished paper award winners: André Rösti, Stijn Volckaert, Michael Franz, Alexios Voulimeneas 👏👏👏 The talk "I’ll Be There for You! Perpetual Availability in the A8 MVX System" is Thursday in the "System Security" session!



Topic: Memory Safe Languages Researcher: Adriaan Jacobs Drink: Rochefort Listen: podcasters.spotify.com/pod/show/hacke…




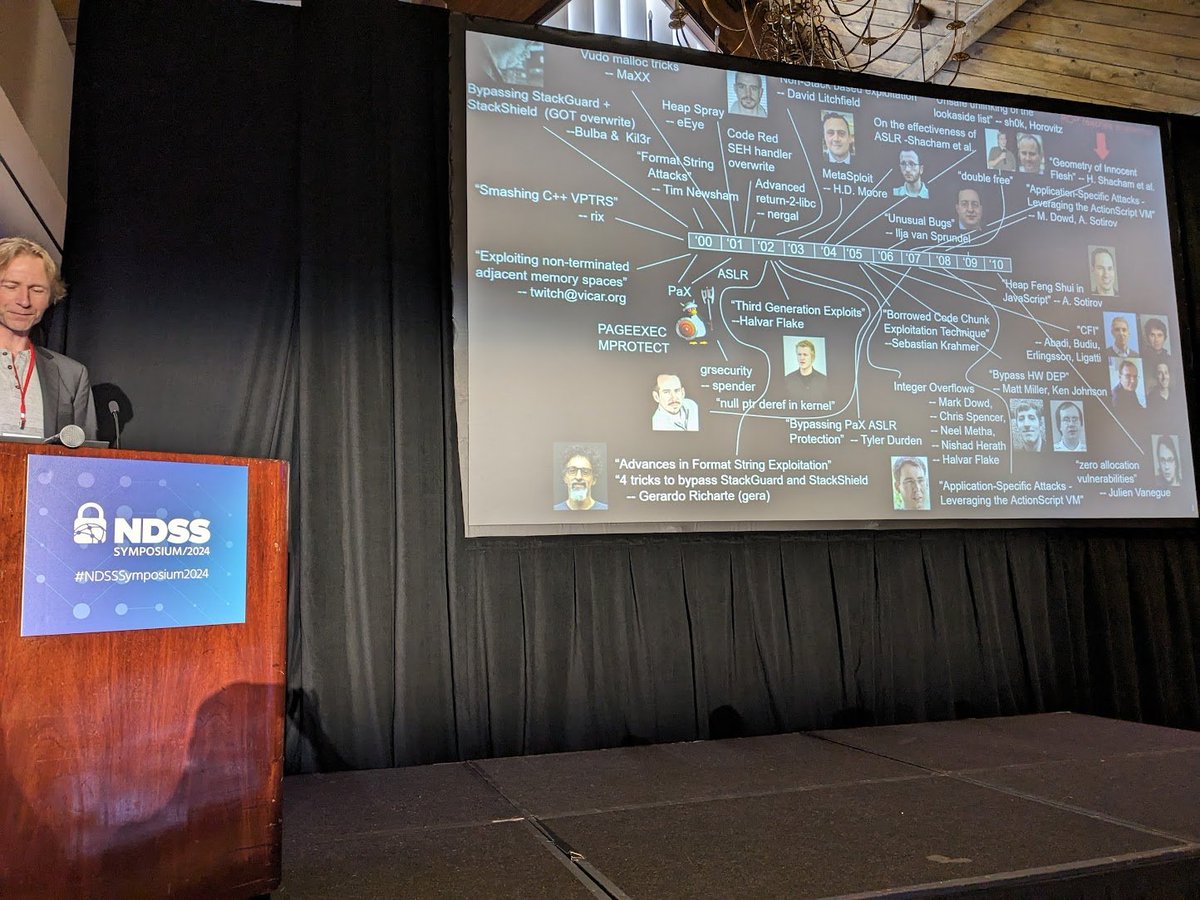
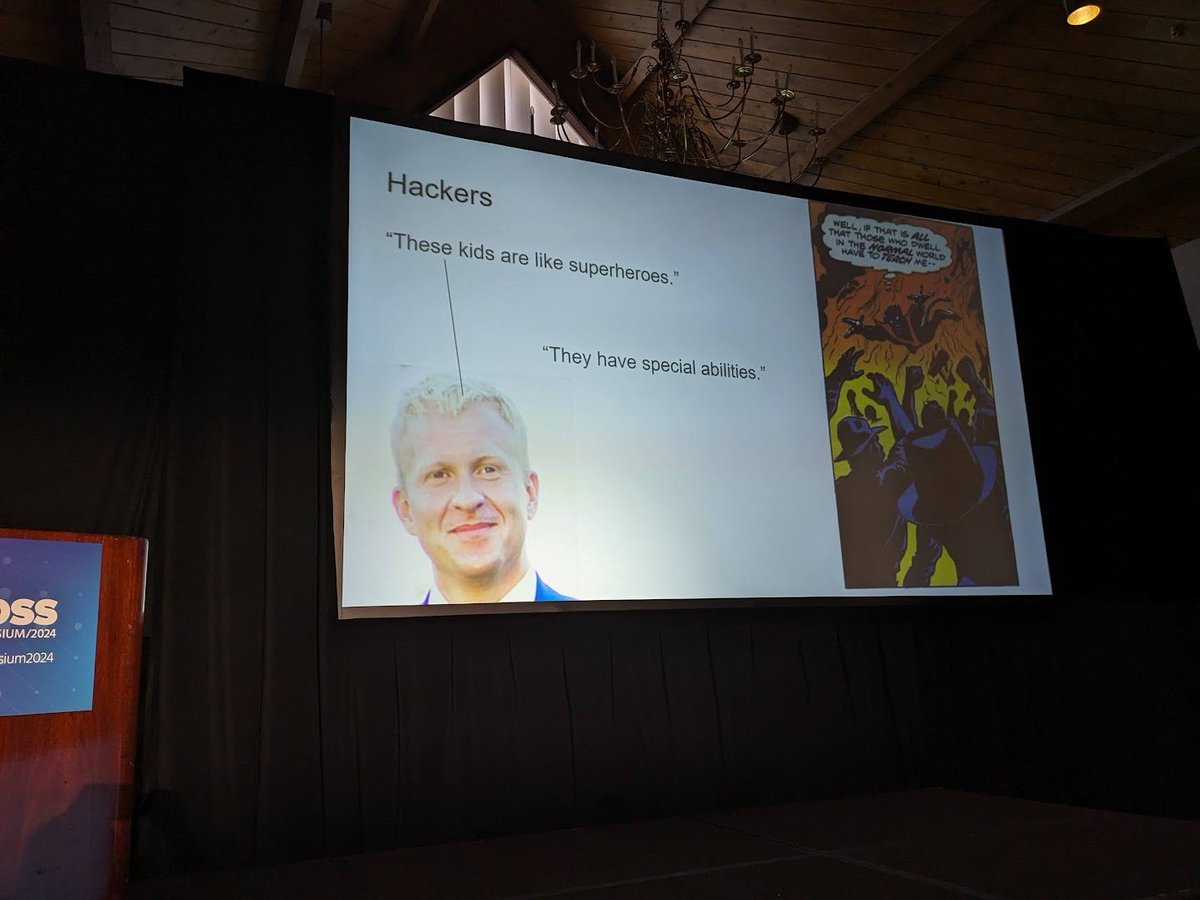
#WOOT24 session on memory corruption about to start @wootsecurity






Congratulations to @Karel_Dhondt for successfully defending his PhD thesis titled 'Analysis of User Privacy in Online Location-Based Services'. We wish you all the best in your career! #security #privacy #kuleuven