Sabitlenmiş Tweet

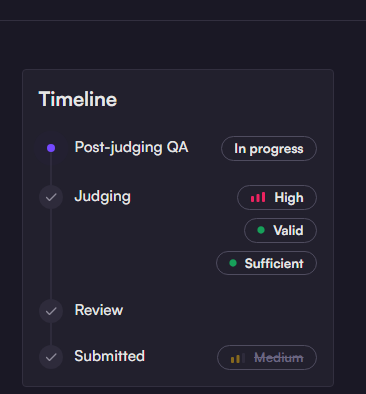
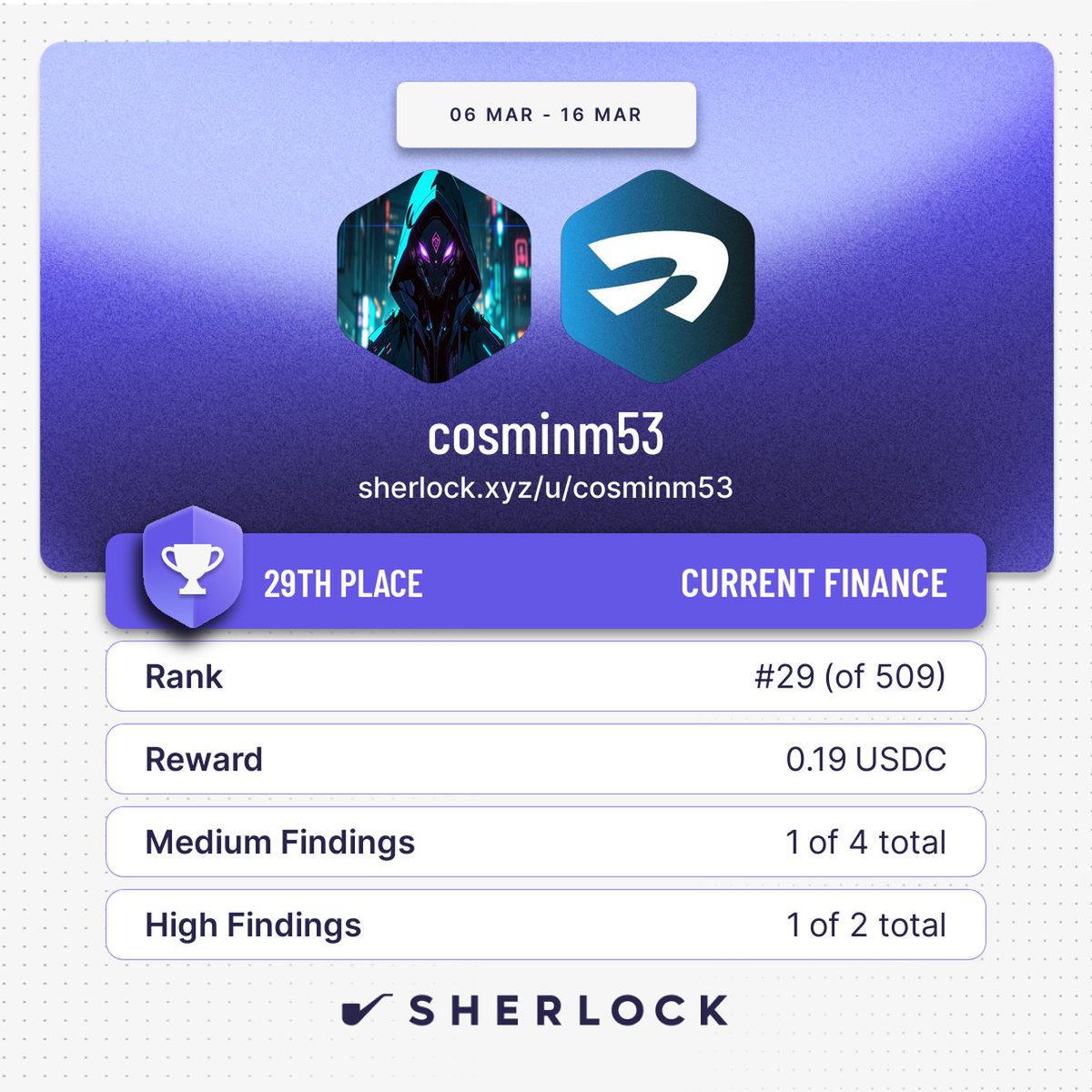
Day 32 of @bichistriver 's mentorship program. Great week, very productive. Also got my first High in a contest. Ready to get back to it 🫡
English
OUTLAW STAR
5.7K posts


@StrangerMontana
EVM Enjoyer, Security Researcher, Intern @ KannAudits













We’re proud to announce a strategic partnership between MST Blockchain and @KannAudits 🤝 🔐 This partnership brings: • Enhanced smart contract security and auditing standards • Stronger trust and reliability across MST-powered applications This collaboration ensures that every innovation built on MST stands on a layer of trust, transparency, and resilience. Together, MST Blockchain and Kann Audits are shaping a future where decentralized technology is not only powerful, but also secure and dependable.



