Team Axon
126 posts


Team Axon
@team__axon
An elite team of threat hunting experts by @hunters_ai. Follow us for timely updates on emerging cyber threats and more.
Katılım Ekim 2022
210 Takip Edilen166 Takipçiler
Team Axon retweetledi

More info can be found on our blogpost:
hunters.security/en/blog/azure-…
English

External communications are the primary threat in Microsoft Teams.
The fact that this capability is enabled by default in M365 tenants makes it particularly attractive for attackers.
More details in our latest blog: hunters.security/en/blog/micros…
#ThreatHunting #MicrosoftTeams
English

Threat hunting tip 🔥
Look for ChatCreated events in M365 logs where the sender domain is external + rarely seen.
This pattern often signals fake IT/Helpdesk phishing in Teams.
We share detection logic in our latest blog hubs.li/Q03G1Z-_0
#ThreatHunting #MicrosoftTeams
English

Attackers are abusing #MicrosoftTeams as an initial access vector.
- Fake IT/Helpdesk chats
- Vishing calls with no warning banners
- File delivery via hidden SharePoint links
We break down the logs, artifacts & hunting queries SOCs need: hubs.li/Q03G1Z-_0
English

Last week at @defcon 33’s @cloudvillage_dc , @CYBER_TLDR & @ElirazLevi shared Team Axon’s latest research on #Azure Managed Identities. Huge thanks to the organizers for selecting us to present and for all the great sessions 🔥 hunters.security/en/blog/azure-…

English

Understanding Azure Managed Identities (NHIs) is critical for defenders, red teamers, and researchers alike. Our researchers break down MI internals, JWT token abuse, and real-world attack vectors in Part 1 of our technical deep dive.
Read the research: hubs.li/Q03dGK7T0

English

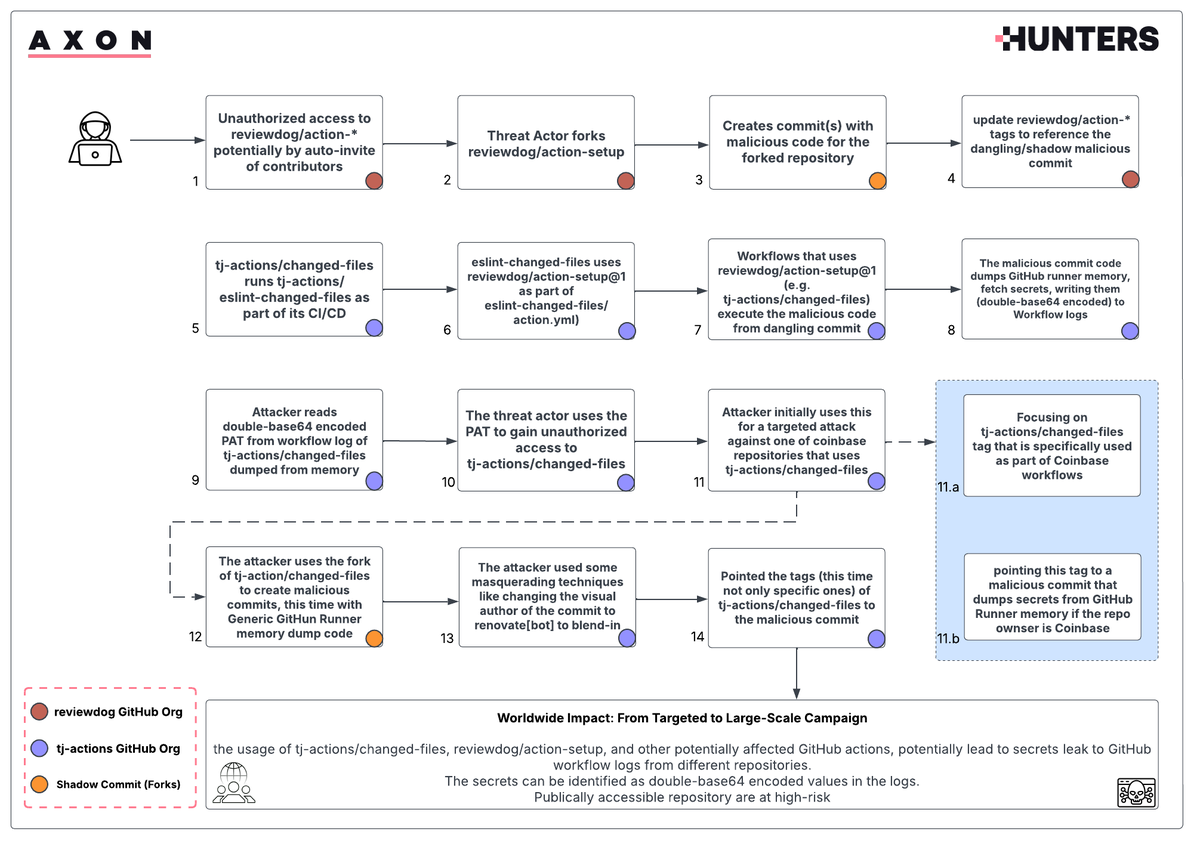
GitHub Actions Supply Chain Attack (tj-actions & reviewdog) update:
Team AXON dropped tools to detect secrets leaked via CVE-2025-30066 & CVE-2025-30154:
🔍 Secret Scanner
📦 Log Fetcher (Linux/Win)
Protect your repos now: hubs.li/Q03cXXTl0
English

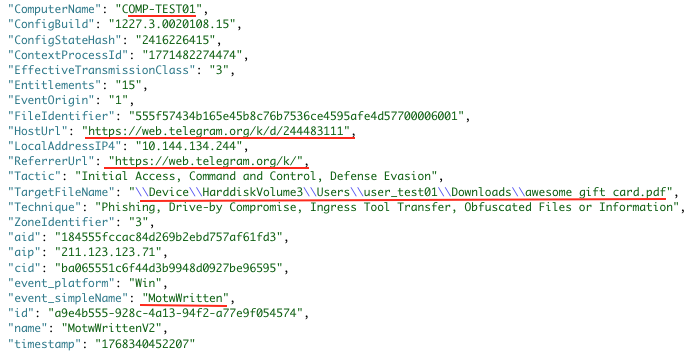
C2 over OneDrive, Social engineering via Microsoft Teams OneOnOne messages, and much more
#VEILDrive includes them all. The new threat campaign identified by team #AXON. IOCs, Hunting Queries, detailed analysis, can be found here: hubs.li/Q02WRnrn0
#CYBERSEC #DFIR #Hunters
English
Team Axon retweetledi

Breaking: #VEILDrive campaign uses Microsoft services for Command & Control! Unobfuscated Java malware evaded detection. Read the attack path + hunting queries from @Team__AXON 👉 hubs.li/Q02WQ_vr0 #ThreatHunting #CyberSec @InfosecInsights
English
Team Axon retweetledi

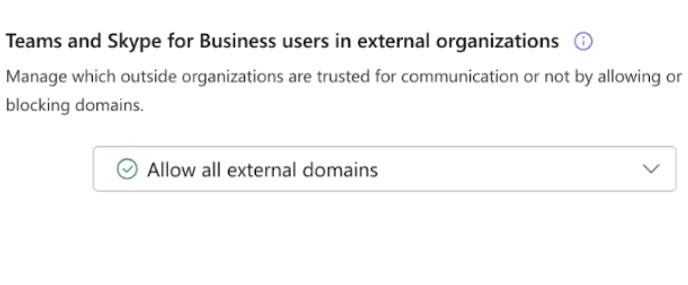
Hunters’ team AXON has observed a concerning rise in Microsoft services abuse over the past few months. A notable trend is the increase in targeted attacks initiated through social engineering via Microsoft Teams, specifically through OneOnOne messages that exploit the default “External Access” feature in Microsoft 365.
To protect yourself and your organization, make sure to:
✅ Allow only specific external domains (if necessary)
🚦 Strictly control your organization’s guest access settings
🚫 Block anonymous access
Stay tuned for more details coming soon!
#Microsoft365 #DFIR #THREATHUNTING #THREATINTEL #CyberSecurity #MicrosoftTeams
English
Team Axon retweetledi

1 / 2
We've researched how EDRs audit plist files in macOS LaunchAgents. Detection issues can allow persistence mechanisms to slip through, impacting visibility and security posture.
#Cybersecurity #macOS #EDR #ThreatHunting #Infosec

English

The following query identifies Win machines affected by the recent CrowdStrike outage. It detects C-00000291 driver downloads (based on LFODownloadConfirmation events,) and correlates it with deletions to identify repaired machines.
github.com/axon-git/rapid…
#Crowdstrikeoutage
English

Check out @ElirazLevi 's analysis of the MailItemsAccessed event. This can be crucial when investigating incidents in O365
Eliraz Levi@ElirazLevi
Microsoft has recently rolled out the cool MailItemsAccessed events by default for Audit standard functionality as well - not just for Audit premium anymore. Yet, figuring out if an email was actually read using these events can still be pretty tricky. The main challenges revolve around throttling and sync events. Check out this diagram to help simplify the validation process:
English