Sabitlenmiş Tweet

🚀 Introducing the Vulncure Penetration Testing Dashboard
Meet Vulncure Pentest Dashboard — the all-in-one platform designed to simplify and supercharge your penetration testing workflow.
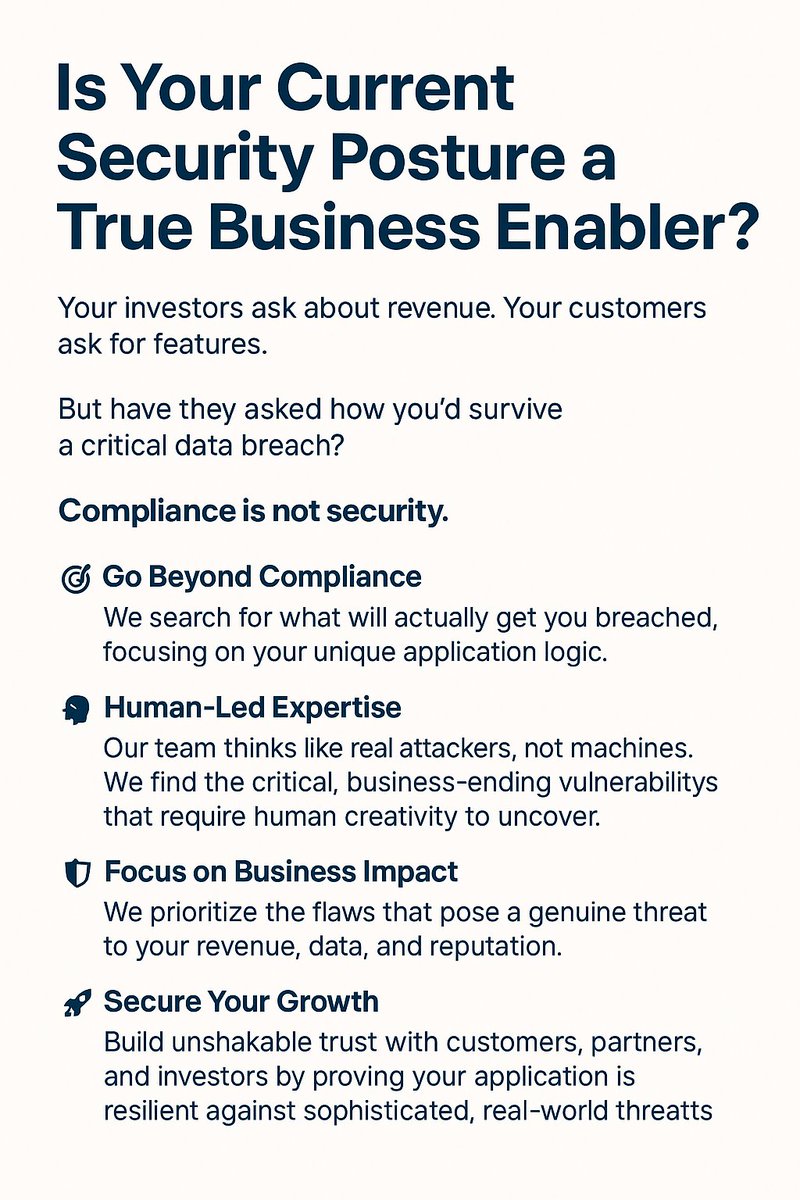
In this demo, we’ll walk you through how Vulncure helps you:
• ✨ Streamline your pentests – manage everything from one dashboard
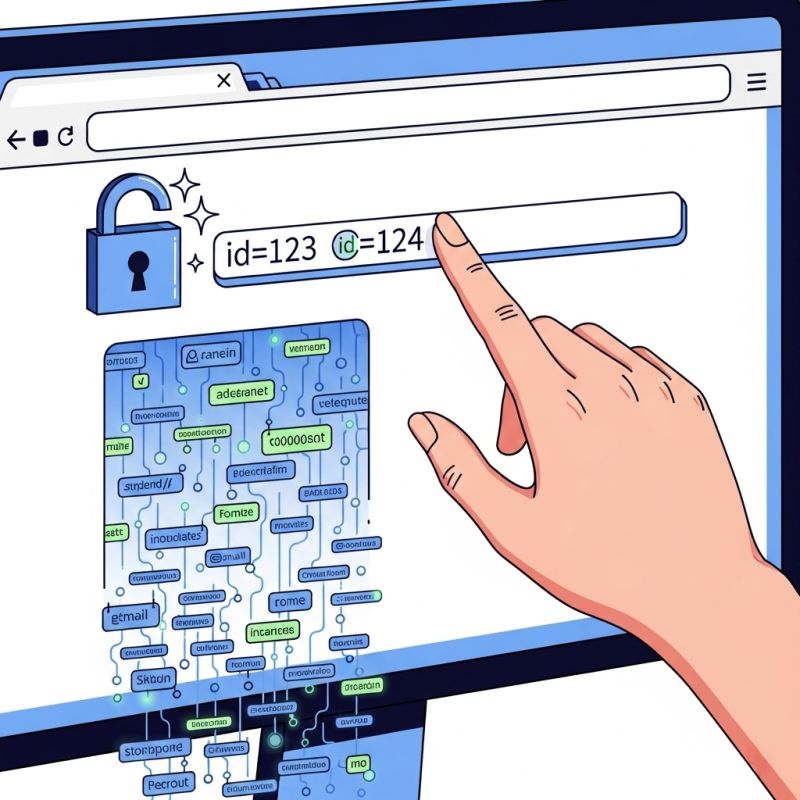
• ⚡ Track vulnerabilities in real time – no more outdated reports
• 📊 Generate professional reports instantly – audit-ready, jargon-free
• 🔐 Centralize asset management – know what’s protected and what’s not
• 📈 View instant security trends – stay ahead of risks across your organization
• 🛡️ Simplify compliance – make audits and testing requests hassle-free
Whether you’re a security leader, compliance officer, or pentester — Vulncure helps you secure smarter, faster, and easier.
👉 Learn more & sign up for a free trial: vulncure.com
English