Sabitlenmiş Tweet
0xki
6.4K posts


0xki
@W3B_AI_SR
WEB3 & AI security researcher #ARSENAL
Katılım Haziran 2025
2.9K Takip Edilen2K Takipçiler
0xki retweetledi

So you’re telling me that Andean Medjedovic walked away with $65,000,000
April 2026
- 23 years old
- Canadian math prodigy
- from Hamilton, Ontario
background
- finished high school at 14
- studied mathematics at University of Waterloo
described as “one of the brightest students ever”
obsessed with DeFi mechanics and AMMs
early crypto activity
- participates in bug bounties
- finds vulnerabilities legally
- builds reputation in Code4rena
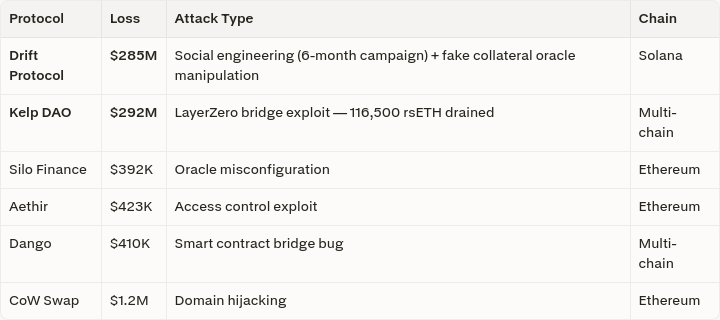
October 2021
Indexed Finance exploit
- manipulates reindexing mechanism
- uses flash loans to distort pool pricing
- drains $16.5M
- embeds “1488” references in addresses
- includes offensive messages in transactions
after the hack
- publicly admits involvement
- refuses to return funds
- rejects bug bounty
- Ontario court issues warrant
- he disappears
November 2023
KyberSwap exploit
- operating from a hotel in The Hague
- using a fake Slovak passport
- executes complex liquidity manipulation
- drains $48.8M across chains
total extracted ~$65M
what happens next, he sends on-chain message to Kyber team
demands control of the protocol
in exchange, returning only 50% of funds
“less than what they wanted, more than they deserve”
August 2024
- detained in Serbia
- held for over 90 days
- released due to insufficient evidence for extradition
- disappears again
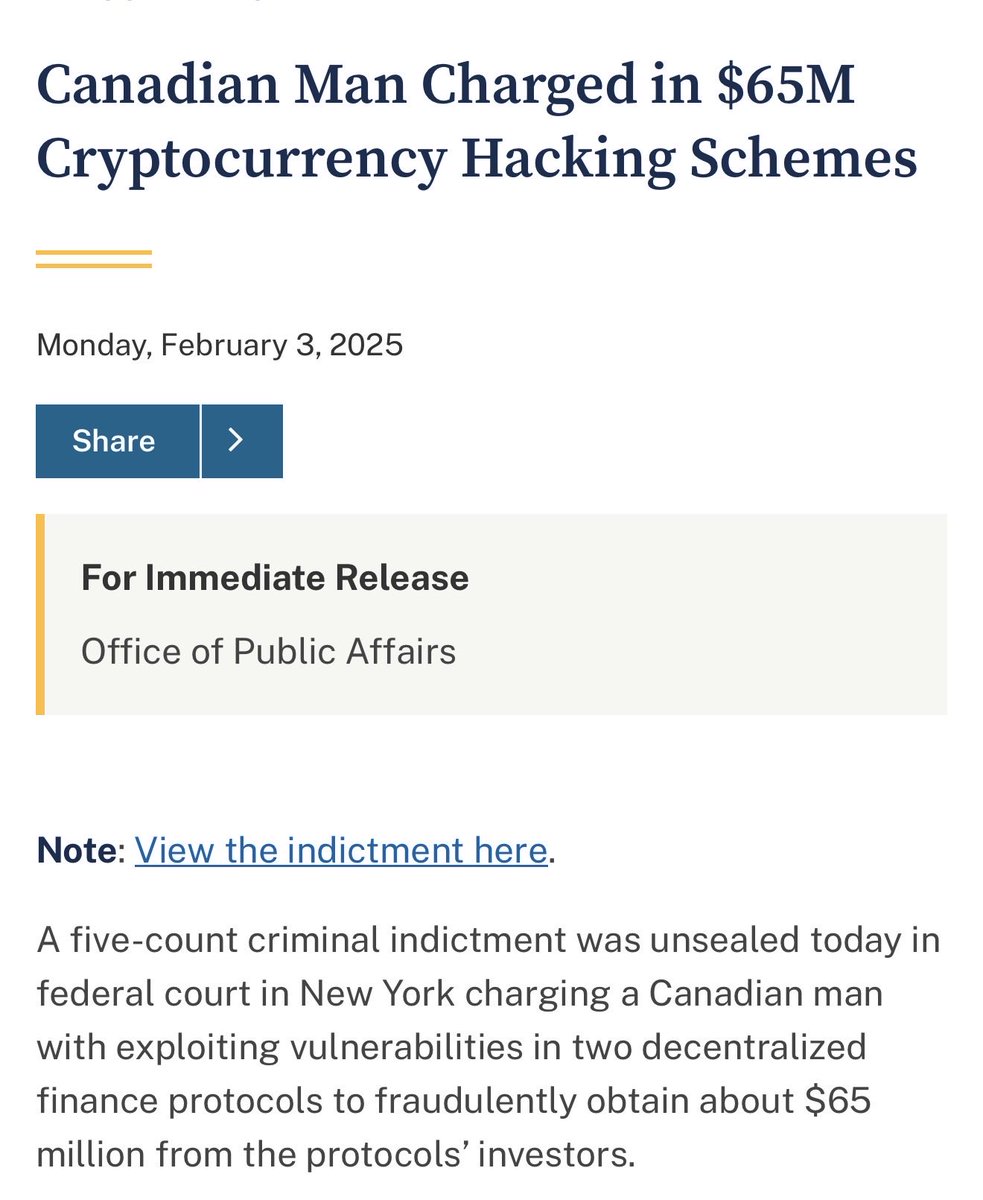
February 2025
DOJ indictment
February 2026
- hires U.S. lobbyist
- pays ~$300,000 retainer
goal was presidential pardon
April 29, 2026
current activity
- moves stolen funds
- sends $24.88M through Tornado Cash
- actively laundering
- still on the run
a fugitive still moving millions
English
0xki retweetledi

Another week, another exploit. I’m getting tired boss.
Again, no time lock. Why???
Wasabi Protocol was exploited for approximately $5.5 million across Ethereum, Base, Blast, and Bera.
The deployer admin key (0x5c629f8c...) was compromised. That key executed grantRole to assign admin privileges to the attacker’s contract with zero delay, bypassing any timelock.
The attacker’s orchestrator then called strategyDeposit on the affected perp vaults and liquidity pools, draining WETH, USDC, and other assets to attacker-controlled EOAs.
After the drainage, the compromised key granted admin to a new address (0x2eb7f20c...), which revoked all roles (ADMIN and others) from the original deployer.
No further access remains via that vector.
The protocol’s contracts operated as coded; the exposure stemmed from reliance on a single EOA admin without multisig or timelock protections. User LP-share tokens remain in wallets but are currently unbacked pending any compensation plan.
This is based on public reports and transaction data as of April 30, 2026.
Official confirmation and next steps from Wasabi Protocol are awaited.
Cointelegraph@Cointelegraph
🚨 ALERT: Wasabi Protocol exploited for $5M+ across multiple chains, including Ethereum and Base, per PeckShield.
English

@fawarano @HackenProof Recon. Invariants attack paths. Pervious audits etc. First. Then get yourself a game plan on where to start line by line. Is you understand the protocol and what it is aiming to do, it will be easier to look in spacific areas for vulnerabilities. Good luck.also Read what I post.
English

@W3B_AI_SR @HackenProof Congratulations sir. I’m a new SR and want advice plz.
Do you read the code line by line for bug bounty like how we do for audit contests ?
I want to jump into bug bounty since there is not enough contest recently but i don’t how how to do in front of large codebase
English

Yeay, I was awarded for a valid submission on @HackenProof hackenproof.com #hackenproofed #bugbounty
x.com/W3B_AI_SR/stat…
0xki@W3B_AI_SR
And a lot more pending #Goals
English
0xki retweetledi

90% of hacked projects skipped at least one of these:
- full test coverage
- internal code reviews
- free AI audit agents - no excuse to skip these
- 2+ independent audits from different firms
- bug bounty program after deployment
- background checks on every new hire
- off-chain security (frontends, CI/CD, key management)
- on-chain monitoring and alerts
- multisig + timelocks on privileged functions
- a documented incident response plan
Security isn't one step. It's a system.
English
0xki retweetledi

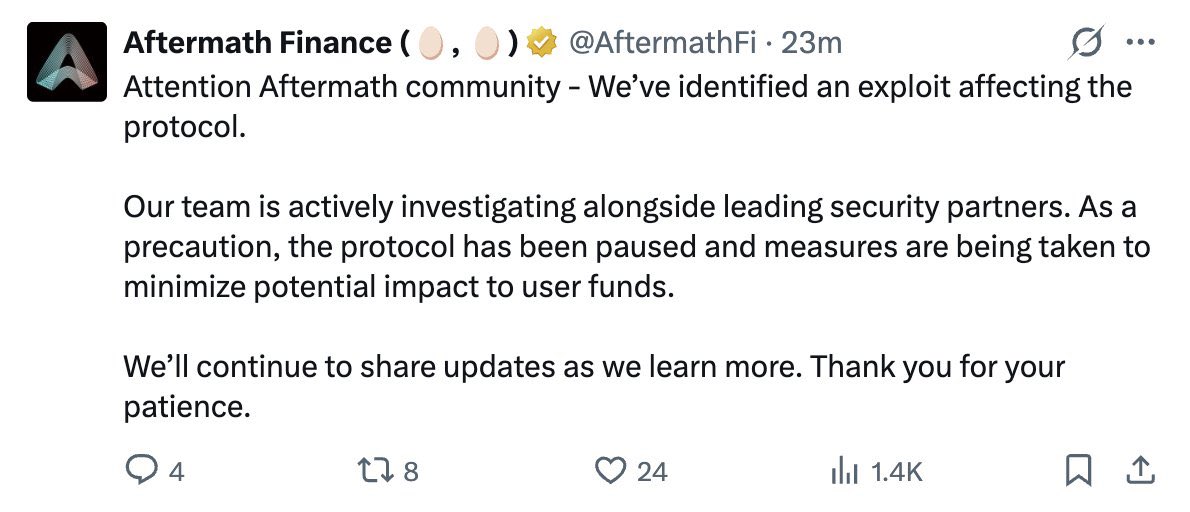
Another hack @AftermathFi. It’s been raining.
$1.4m gone
I think I have to finally say.
We white hats are not in a ready position to fight against blackhats on chain.
We are so bounded and limited to contests and bug bounties that our scope is dependent on these.
Maybe when we see beyond ourselves, we’d be a ready match for blackhats.
Those mfers are active on blocks, we are there fighting for a report to be escalated in our favor.
This is becoming sad.
WE CANNOT WIN, OUR TRAINING MODEL IS FLAWED.
English
0xki retweetledi

Web3 security has become a BRUTAL space for newcomers. 🤯
They’re overloaded with learning material, AI noise, and thousands of different opinions.
Opportunities to practice, build credibility, and prove yourself through security contests are fading. In some contests, you even have to pay just to submit a report, which is understandable given the flood of low-quality AI submissions.
Back when I was starting in 2021 / early 2022, I used to think it was a hard time to break into Web3 security.
But I was wrong. It was so simple. Compared to today, it was a far better environment for beginners.
Yes, it’s harder now imo. But harder also means fewer people are willing to push through it = far less competition.
That’s your edge. 🙂
English
0xki retweetledi

A victim just lost a Alchemix Yearn yvVault position $yvWETH (estimated $~1m), from an earlier approval to an unverified contract (etherscan.io/address/0x143a…). This unverified contract, created 10 days ago, turns out to be buggy and can be exploited for arbitrary call execution.
Here is the vulnerable logic from the decompiled contract, affected in the following exploit tx: etherscan.io/tx/0xebaaab69b…

English
0xki retweetledi

ALERT! Our system detected a suspicious transaction targeting an unverified contract (0x143a737bffc6414b61134f513ceed1a64390181a) on Ethereum a few hours ago, with an estimated loss of ~$983K. The root cause was a missing access-control check in the contract’s execute() function, which enabled arbitrary call execution.
By abusing a pre-existing unlimited yvWETH approval from the victim address (0x98289e90d6fc92a8769bc892d006a2baa7705afe), the attacker drained 384.67 yvWETH and later unwound the position for about 429.2 ETH.
Attack TX: app.blocksec.com/phalcon/explor…
🟦 Found by #PhalconSecurity, 🟦 Analyzed via #PhalconExplorer.
English
0xki retweetledi