Sabitlenmiş Tweet

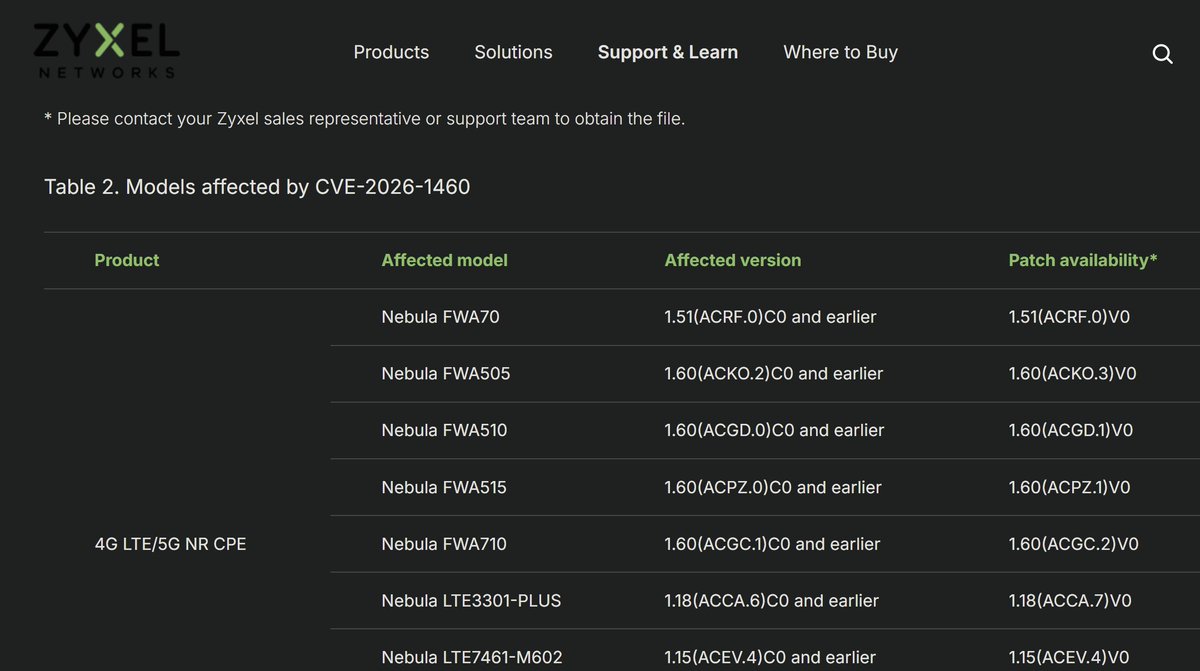
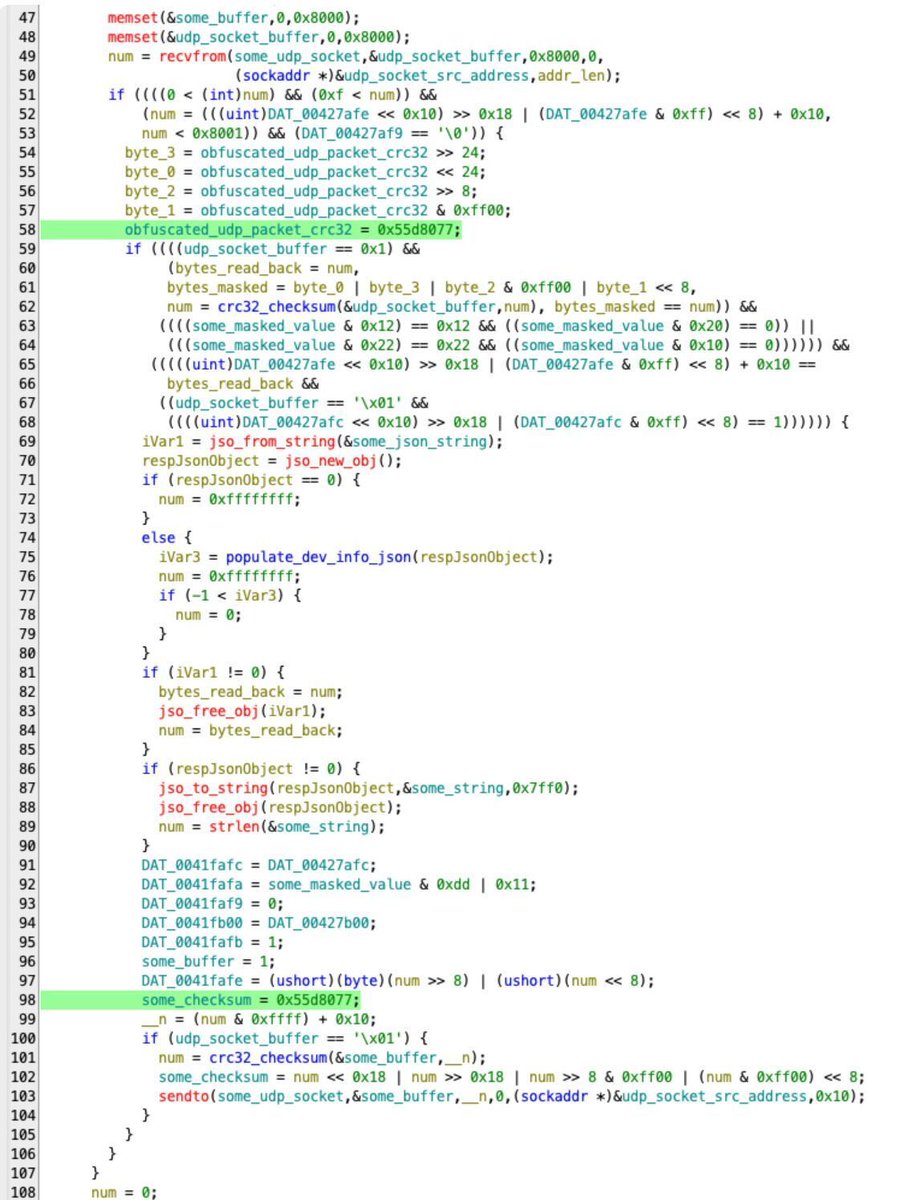
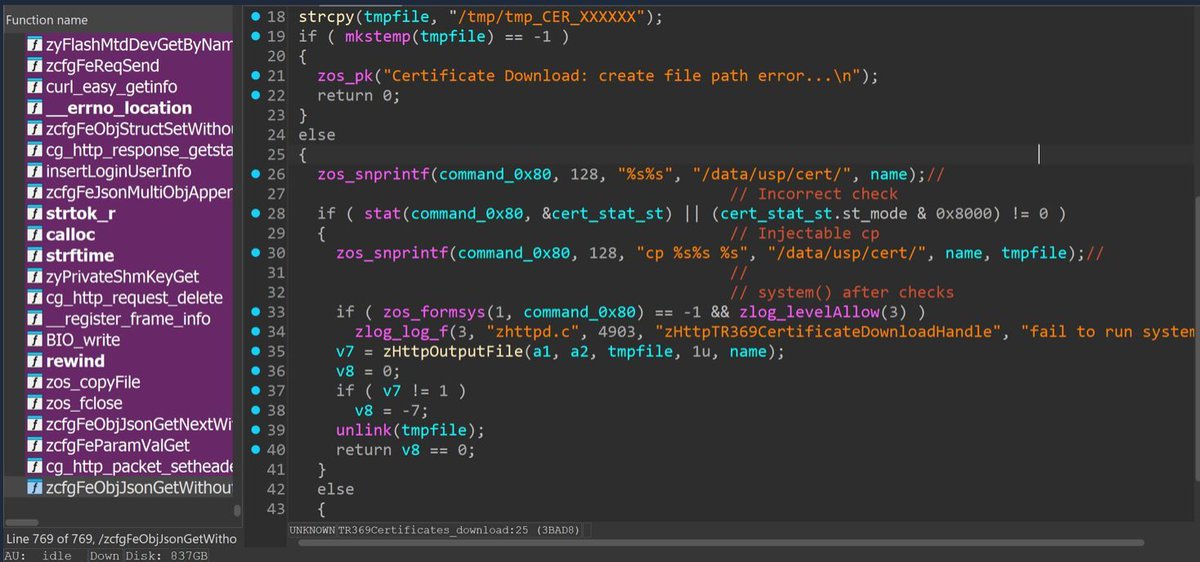
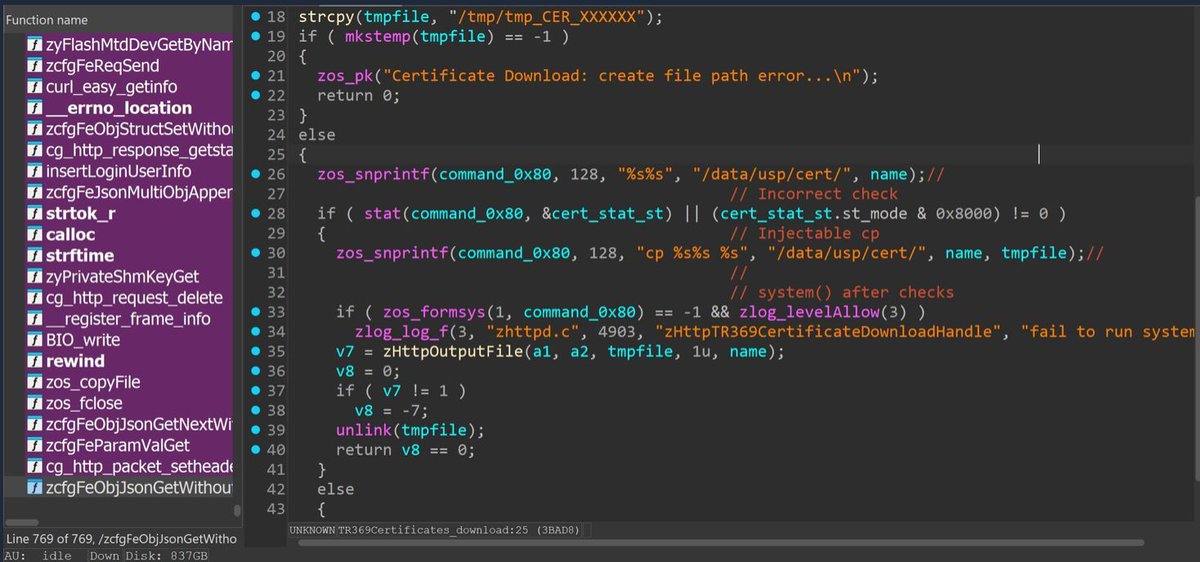
Zyxel DX3301-T0/EX3301-T0 Router Post Auth Vulnerability for root shell.
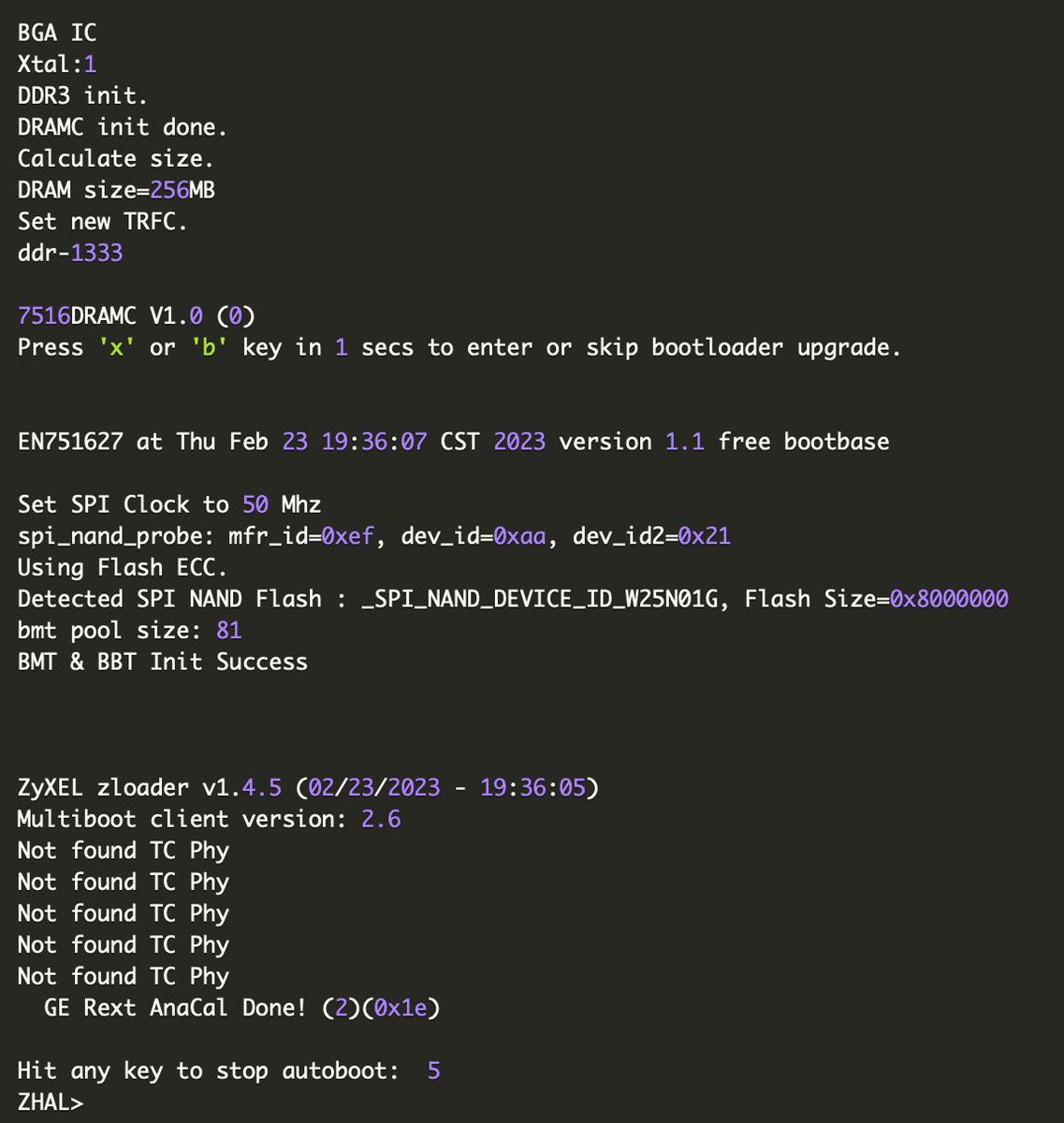
Bootloader vulnerability for full debug commands access.
General Notes
#infosec #zyxel #iot
watchfulip.github.io

English
Watchful IP
47 posts


@Watchful_IP
Security researching in the middle of the night. Focusing on ARM based embedded IoT


























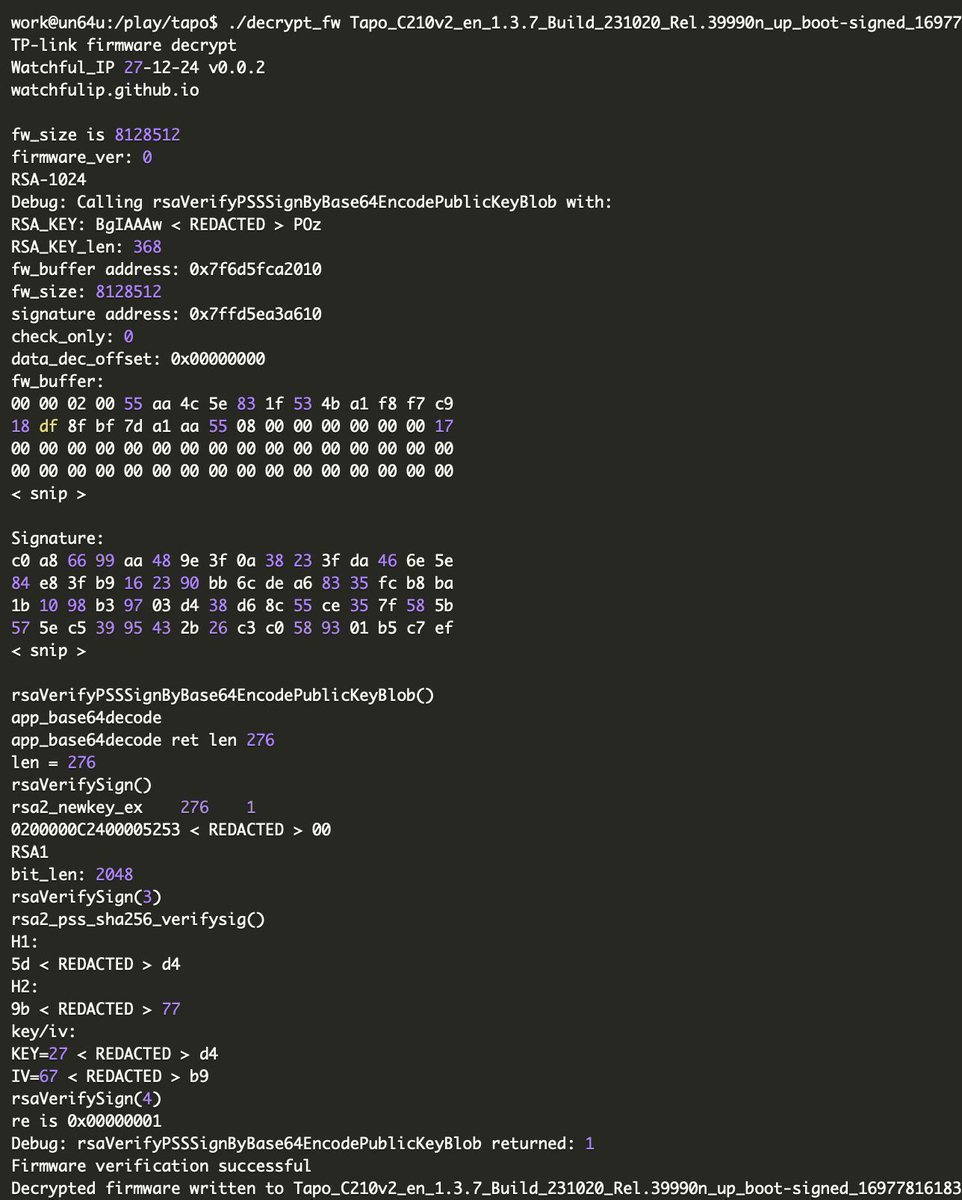
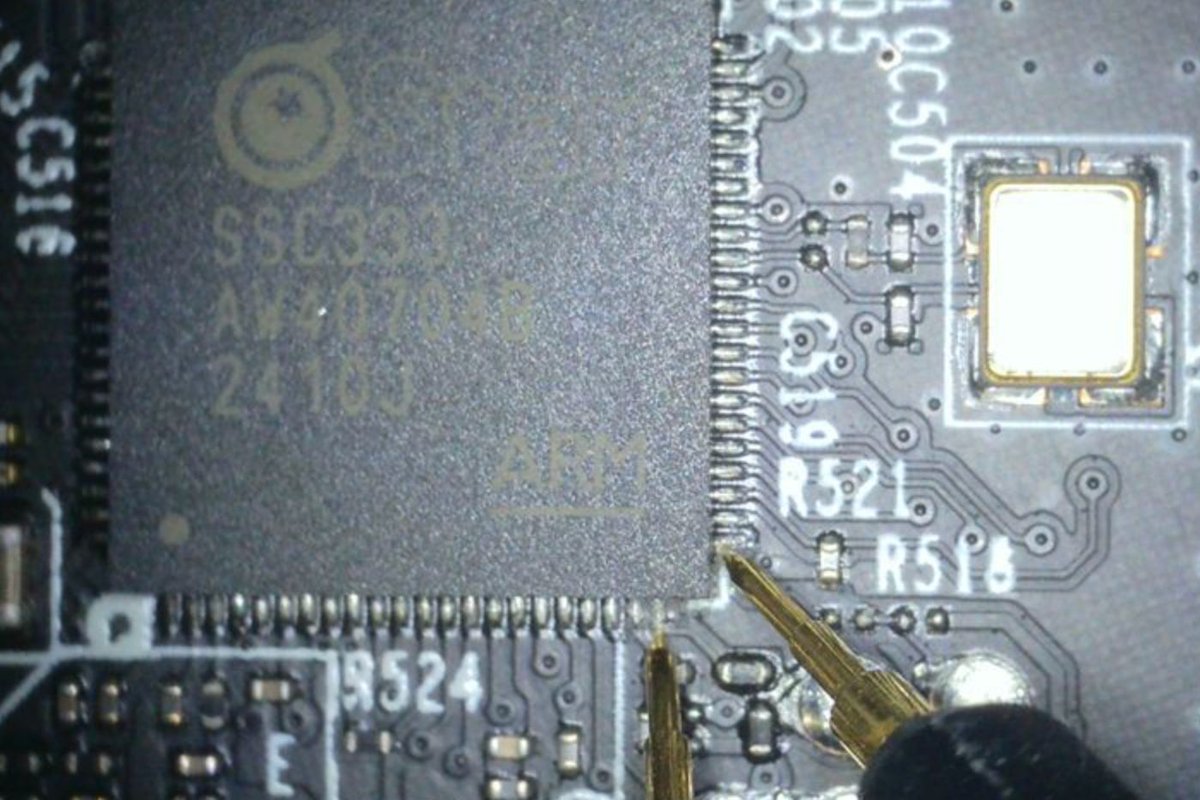



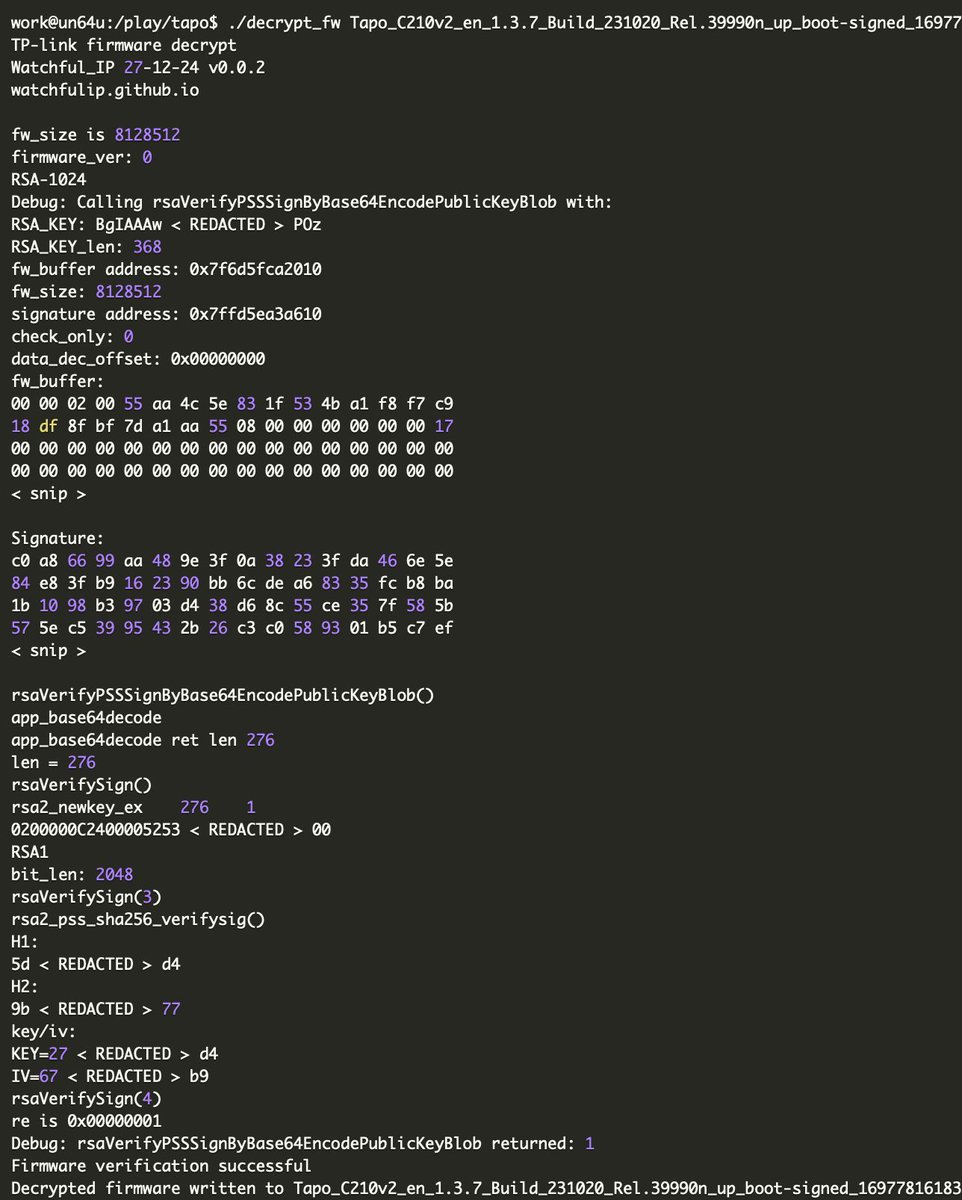
TP-Link (Tapo) C210 V2 cloud camera: bootloader vulnerability and firmware decryption watchfulip.github.io/28-12-24/tp-li… Credits @Watchful_IP #embedded #infosec