Sabitlenmiş Tweet
Wissam
3.6K posts



$1,000,000 in bug bounties came down to one decision:
pick a program and stick with it 👨💻😮💨
HX007, a hacker in the Bugcrowd community, made over $750K on a single program. Not by knowing more than everyone else. By knowing one target better than anyone else.
🔖 The longer you work a program, the more you understand the dev team behind it. Their patterns, their blind spots, the bugs they keep missing. It stops feeling like hunting and starts feeling like collaboration.
When nothing's clicking, HX007 switches to a VDP, racks up some P1s, and comes back with his confidence rebuilt. 💡
More advice from HX007 and why he hunts on Bugcrowd: bugcrowd.com/blog/how-i-hac…

English

🚨My #bugbounty course with @arcanuminfosec is 50% off for the entire month of April! This course teaches you how to go from "Zero to Hero" #hacking the web. Based on feedback, great for beginners or experienced hackers... may the 12345 be with you!😉
tinyurl.com/idorminator
English
THREAD 🧵
One of the most common statements I hear is:
“iPhones can’t be accessed or extracted.”
That belief usually comes from everyday user experience where devices are protected by strong encryption and security controls. However, in a controlled digital forensics laboratory, investigators use specialized forensic acquisition techniques that allow the structured extraction and analysis of data from iOS devices while maintaining evidence integrity.
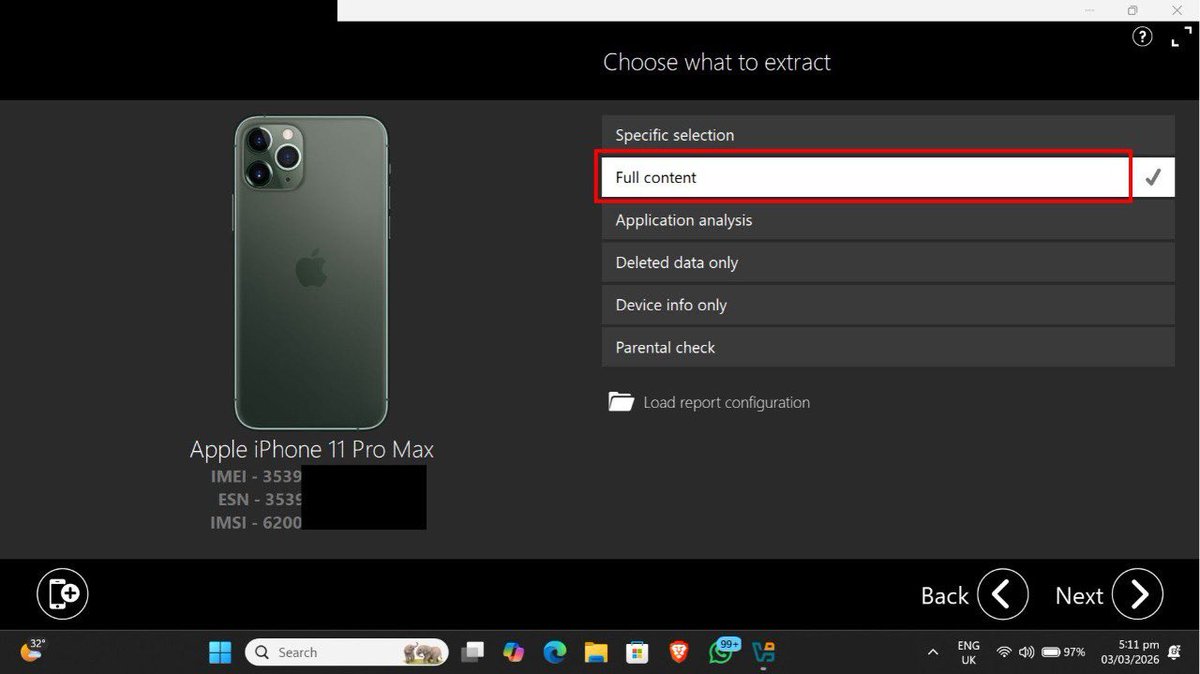
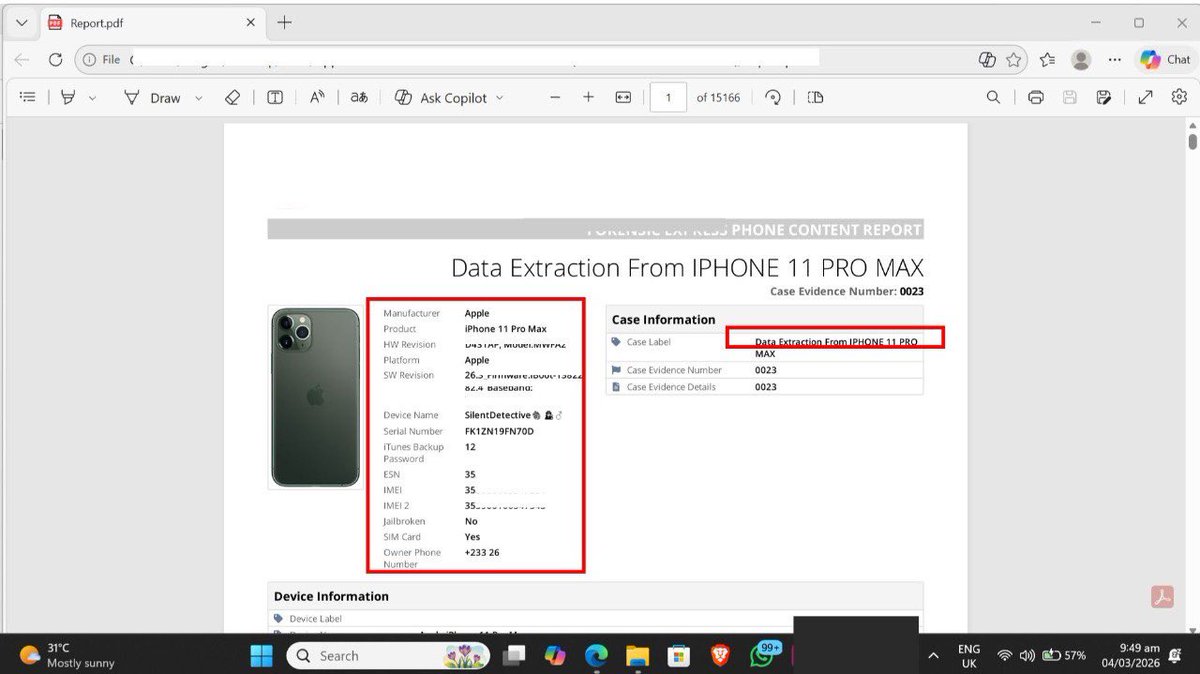
I recently conducted a forensic extraction on my iPhone 11 Pro Max to demonstrate how this process works in practice.
The examination began with device identification and preservation. Before any data acquisition takes place, the device must be documented to establish evidence integrity. Key identifiers such as the device model, serial number, IMEI, operating system version, SIM status, and device configuration are recorded. This step ensures the device can be uniquely identified and that any findings can later be verified.
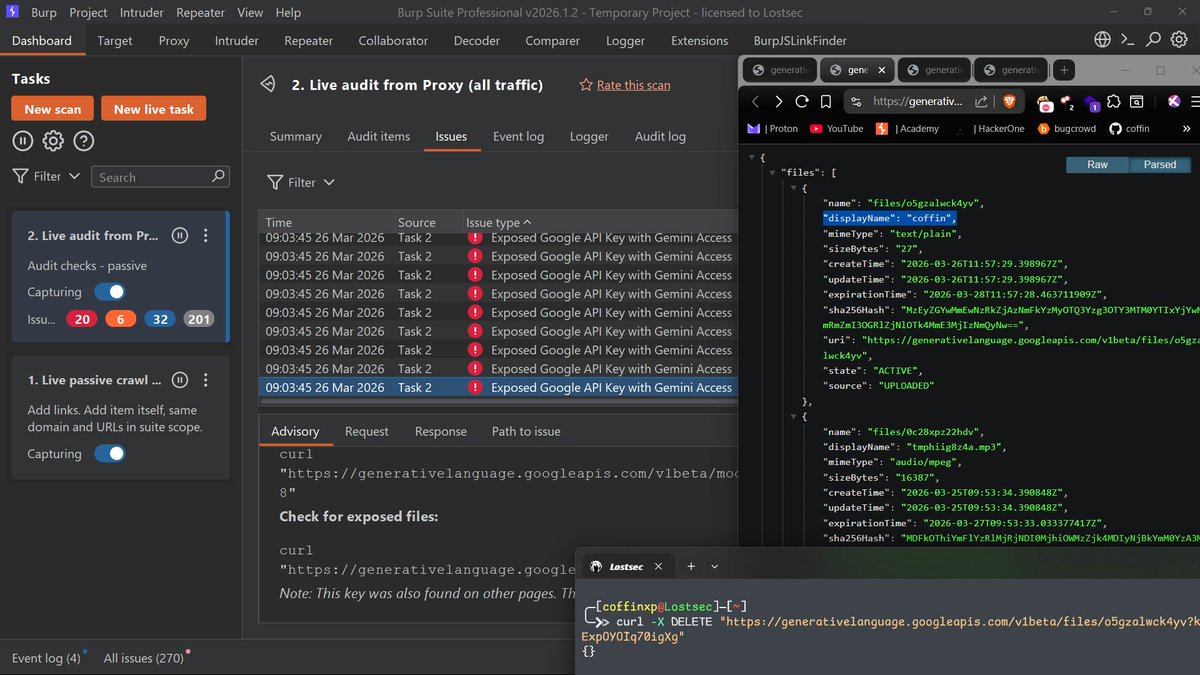
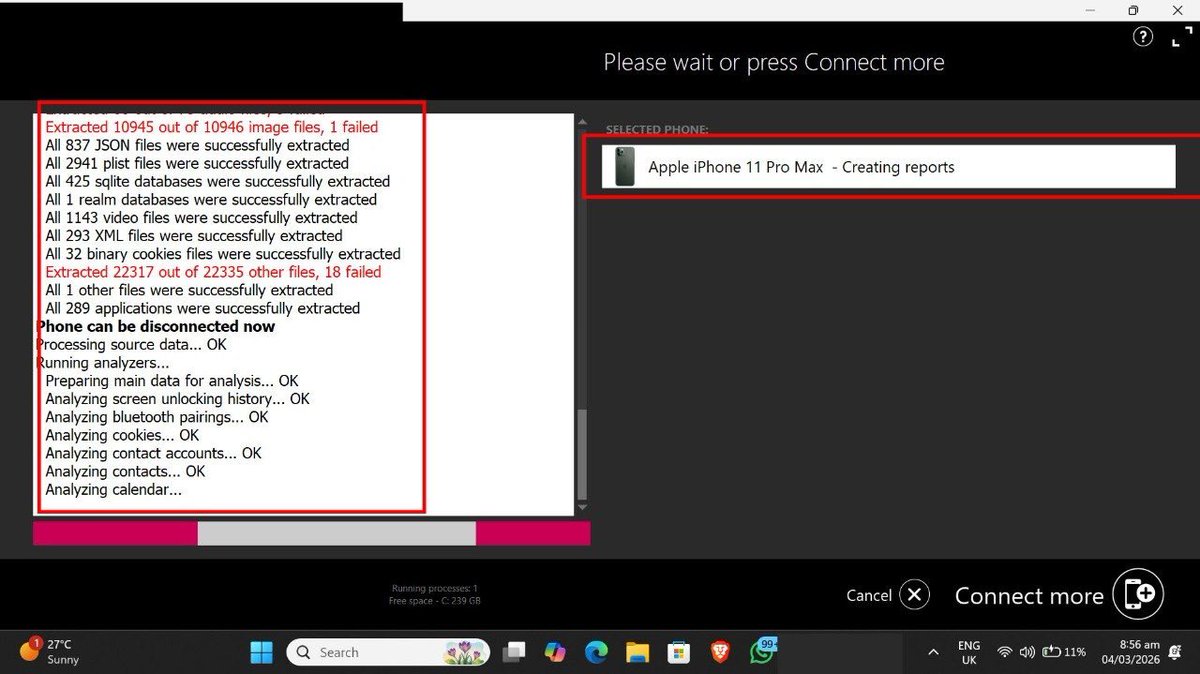
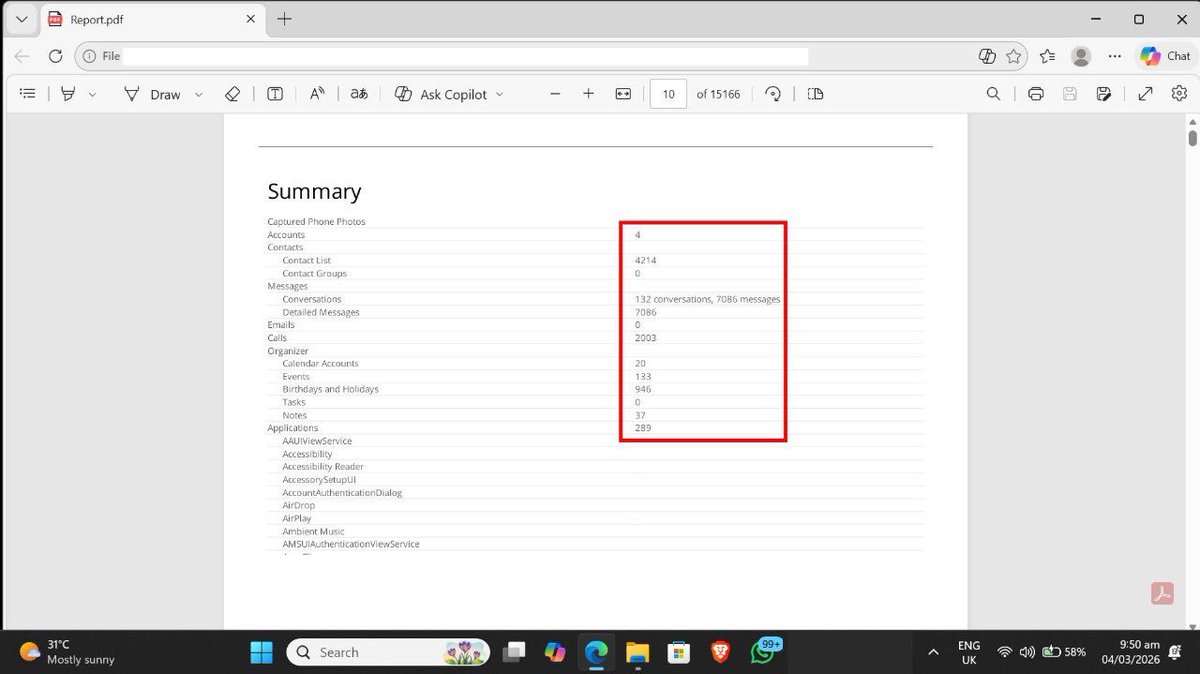
After the device is properly documented, the forensic acquisition phase begins. Instead of simply copying files, the extraction process reads structured data stored within the operating system and application containers. Smartphones store information across multiple formats including SQLite databases, JSON records, system logs, and application storage structures.
#DigitalForensics #MobileForensics #DFIR
#CyberSecurity #iOSForensics #CyberInvestigation #IncidentResponse
#Infosec #ForensicAnalysis
@Asaassim @RedHatPentester @elormkdaniel @cyberjeremiah @cybergirl_io @h4ruk7
Check thread 🧵
English

على مين حاط الفيس كابتن؟ ومن أول لاعب عندك في الدكة؟
FPL UCF@FPL_UCF
نسبة تسجيل السيتي للأهداف المتوقعة قلت اليوم بشكل غير مفهوم آخر مرة حصلت كان هالاند على الدكة هل من الممكن يكون هالاند اليوم دكة؟ 😨
العربية

Point-in-time pentests can’t keep up, while fully autonomous testing creates noise.
The solution? HackerOne Agentic PTaaS pairs specially trained AI agents with elite human validation to deliver results based on real-world exploitability, not theory.
This 50-second video shows you how it works.
English

🚨👀 Arne Slot on UCL impacting future plans: “The only thing I do know is that it happened before and recently [Klopp in 22/23] and it didn’t affect the future of that manager”.
“But that doesn't guarantee anything of course. Usually at this club several factors are taken into consideration”.

English
Wissam retweetledi