
WiFiProof
15 posts

@wifiproof
proof of attendance protocol using venue wifi and zk geolocation to verify physical presence without doxxing


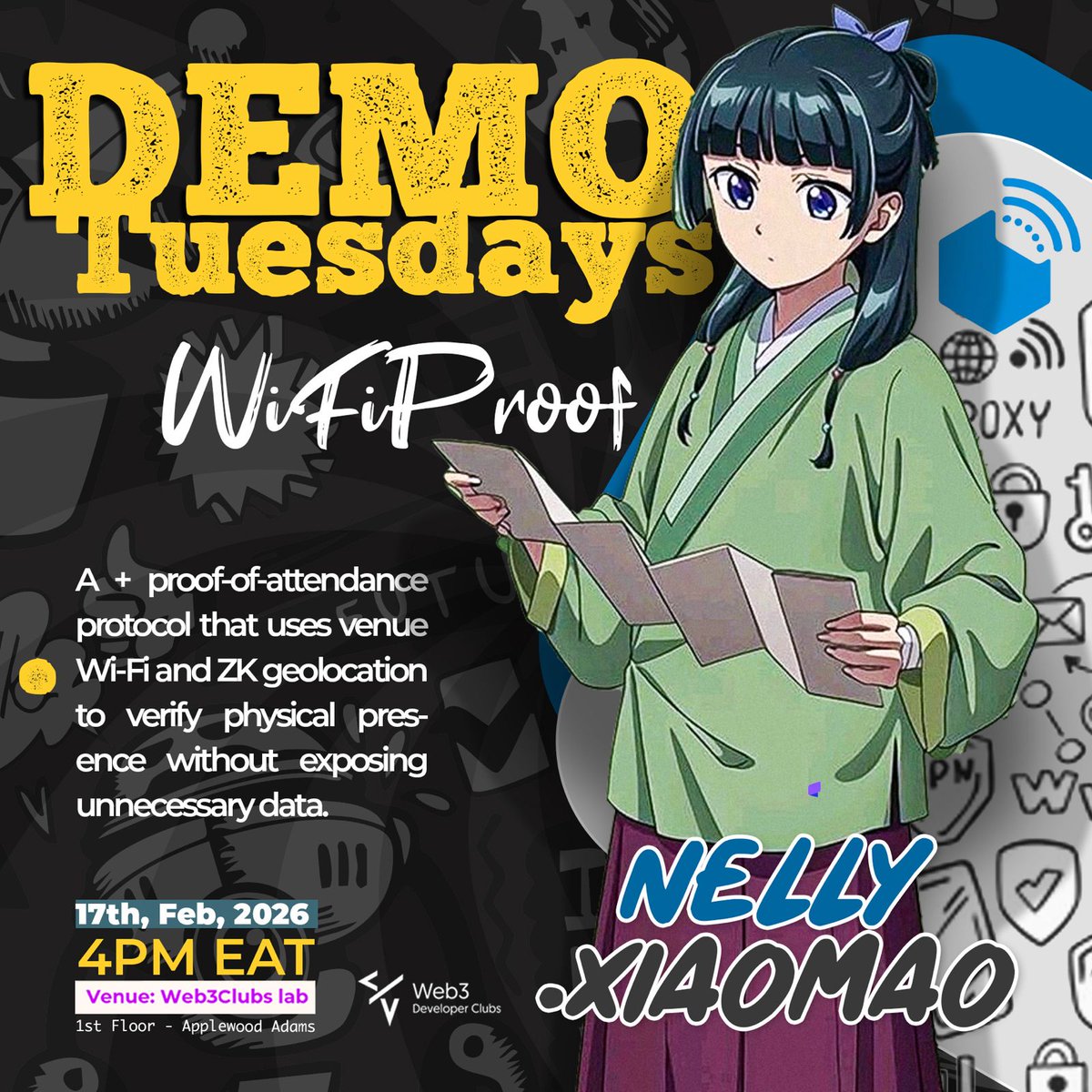
On September 23, 2025, I talked @wifiproof for the first time. At the time, it was a hackathon idea built around a very simple observation: whenever people arrive at a hackathon, conference, or venue, one of the first things they ask is, “What’s the Wi-Fi password?” That tiny ritual stuck with me. Because if you are physically in a venue, trying to connect to the venue’s Wi-Fi, that already says something important. It says you are there. And I kept asking myself: why do we still have to give away so much personal information just to prove something as simple as attendance? Why should proving “I was there” require exposing your name, phone number, email, or other unnecessary details? That question became WiFiProof. Version 1 was important because it proved the idea had life. People understood it immediately. They loved the concept. But if I’m being honest, v1 also showed me all the places where the design was not strong enough yet. There were real security assumptions and weaknesses that needed to be revisited. So I went back to the drawing board. Over the past few months, I’ve been building WiFiProof v2. Reworking assumptions. Fixing vulnerabilities. Tightening the security model. Improving the proof flow. Making the system more credible, more private, and much closer to the product I originally imagined. This has been one of those projects where the deeper you go, the more you realize how much care is required if you want to build something that is not just interesting, but actually trustworthy. And now, after all that iteration, WiFiProof v2 is ready for testing. Tomorrow, I’ll be demoing it at @Web3Clubs Labs. I’m excited, but more than that, I’m grateful. Grateful that an idea that started as a hackathon experiment is now at the stage where people can actually come interact with it, test it, question it, and help shape what it becomes next. If you’ve followed the journey since the first post, thank you. If this is your first time hearing about @wifiproof , welcome. And if you care about privacy, ZK, cryptography, proof of attendance, or building better systems for the real world, I’d love for you to come see what we’ve been working on. See you tomorrow at Web3Clubs Labs.

You’re at a crypto conference. First thing you do? (After grabbing coffee and dodging swag) ask: What’s the Wi-Fi password? What if that tiny ritual could become unforgeable, private proof that you were actually there? Enter: WiFiProof, built during @zk_monk hackathon 2025.🧵

Jam Session XXVI Recap ⚡️Base East Africa community hosted its XXVI consecutive Jam Session, diving deep into the world of zero-knowledge (zk) products on @base . The session was hosted by @vin_sipoi and @BasedKago featuring @nellycyberpro , the founder of @wifiproof for part two of her ongoing exploration of privacy, zk proofs, and real-world integrations. it was highly technical and refreshingly practical. For many of us still new to zk technology, Nelly managed to make complex cryptography concepts feel approachable and exciting. Understanding zk Proofs ⚡️Nelly defined zk proofs as a cryptographic protocol that allows one party (the prover) to prove to another (the verifier) that a statement is true without revealing any additional information. The verifier learns nothing beyond the fact that the statement is true, a core principle for ensuring privacy in decentralized systems. WiFiProof x Base Integration ⚡️The highlight of the evening was a live demo showcasing how @WiFiProof integrates seamlessly with @base. she walked us through both the front-end and back-end of her project, showing the process of generating proofs on Base and explaining how circuits validate a user’s claims. She also shared the user journey: ✅Attend an event. ✅Scan a QR code to access a captive portal. ✅The portal launches automatically in your browser, storing information locally. ✅A unique device secret is generated, which helps you create a proof of access to verify your presence privately and securely. ⚡️Importantly, the Wi-Fi portal can only be accessed by someone physically within the event’s Wi-Fi range , a smart privacy preserving limitation that ensures only real attendees can prove their presence. ⚡️Nelly plans to integrate directly with venue Wi-Fi systems, setting up the captive portal ahead of time to better understand environmental limitations such as bandwidth and signal range. Why Base? ⚡️ Nelly highlighted Base’s low gas fees on both mainnet and Base Sepolia, making it an ideal chain for scalable zk applications and privacy tools. Inspiration towards building @wifiproof ⚡️As a privacy maxi, Nelly’s motivation for WiFiProof stems from a desire to protect user data especially location and event attendance details while still enabling proof of participation. With WiFiProof, your identity remains private, and your data never leaves your device. Tools and Tech Nelly also walked participants through some of the tools powering WiFiProof’s zk system: ✅NOYA – abstracts away low-level constraints management, allowing developers to easily write logic into their circuits. ✅Barretenberg – a high performance zk backend that handles the heavy cryptographic lifting. ✅Foundry – used for deploying onchain and debugging verification processes. ⚡️During the discussion, @BasedKago encouraged adding a mini-app functionality to enhance accessibility and user interaction. He also encouraged Nelly and other builders in the session to apply for Base Batches 002,to continue scaling their projects within the Base ecosystem. The project is open source and open to contribution:github.com/wamimi/proof-o…




Jam Session XXV | zk Products on Base | WifiProof - Product Demo x.com/i/broadcasts/1…

🚨 Jam Session XXV | zk Products on Base | @wifiproof Product Demo Tonight, we explore zk-powered products on @Base and why @nellycyberpro is building @wifiproof , a privacy layer for onchain presence. We will unpack: 🔹 Why privacy matters onchain 🔹 How zK tech enables secure identity & interactions 🔹 A live demo of @wifiproof in action Tonight | 🕘 9PM EAT 🎙️ Hosted by @youngishinvesta with @nellycyberpro founder @wifiproof What are you building ? Join in and @buildonbase

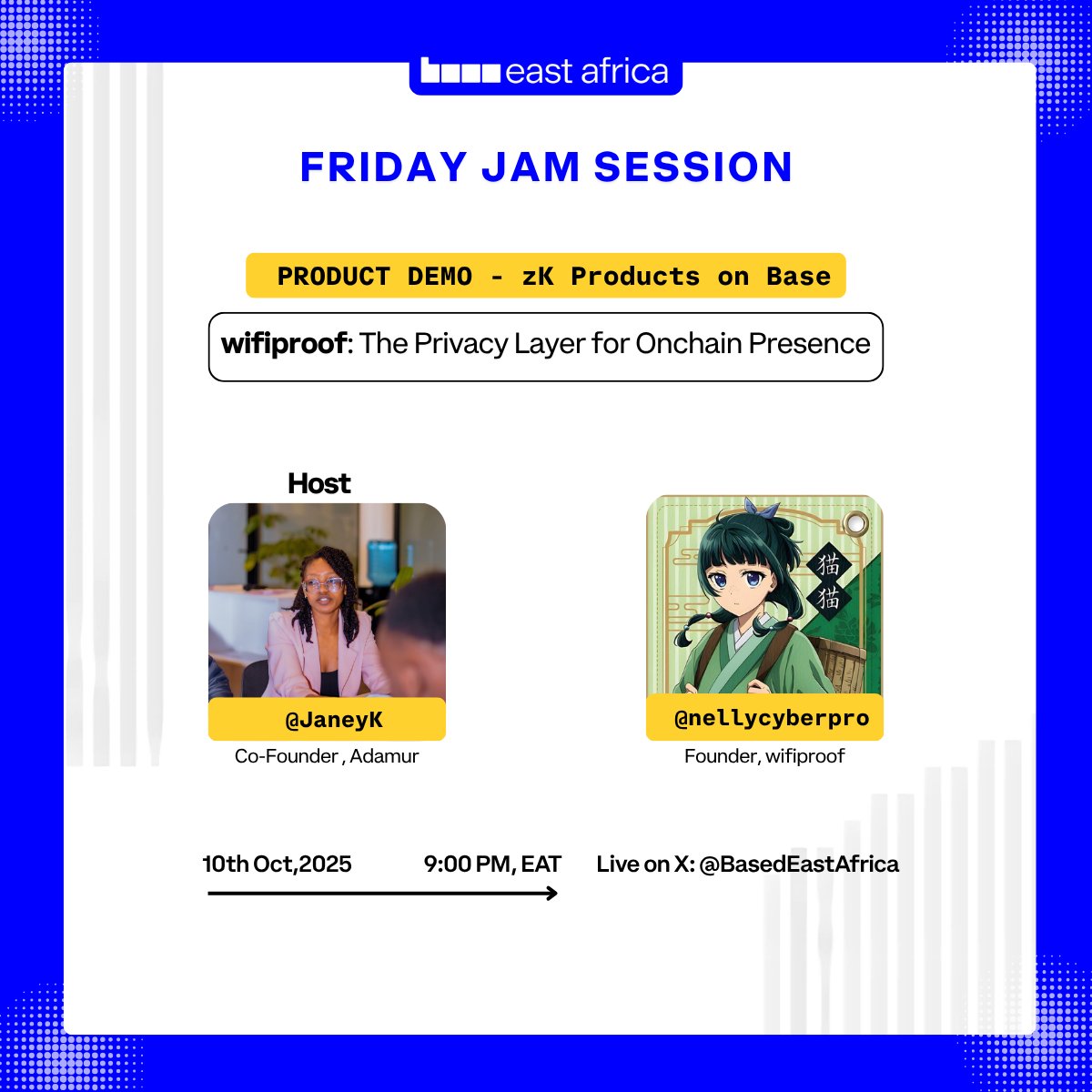
🚨 Jam Session XXV | zk Products on Base | @wifiproof Product Demo Tonight, we explore zk-powered products on @Base and why @nellycyberpro is building @wifiproof , a privacy layer for onchain presence. We will unpack: 🔹 Why privacy matters onchain 🔹 How zK tech enables secure identity & interactions 🔹 A live demo of @wifiproof in action Tonight | 🕘 9PM EAT 🎙️ Hosted by @youngishinvesta with @nellycyberpro founder @wifiproof What are you building ? Join in and @buildonbase




You’re at a crypto conference. First thing you do? (After grabbing coffee and dodging swag) ask: What’s the Wi-Fi password? What if that tiny ritual could become unforgeable, private proof that you were actually there? Enter: WiFiProof, built during @zk_monk hackathon 2025.🧵


