D 3 B B Y ❤️ retweetledi
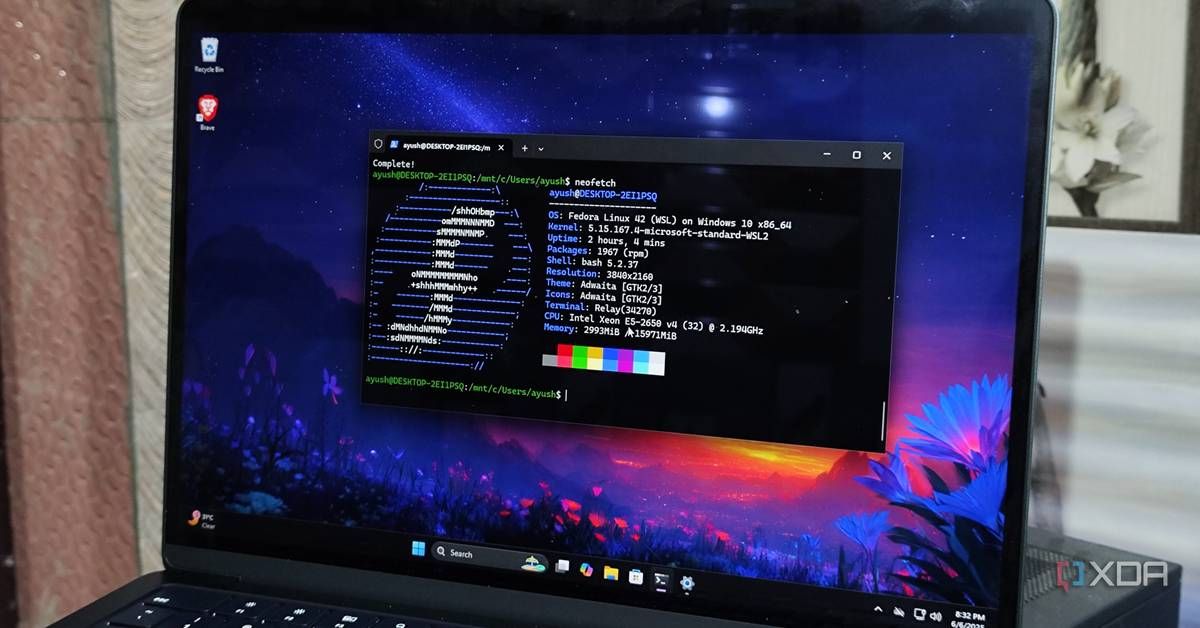
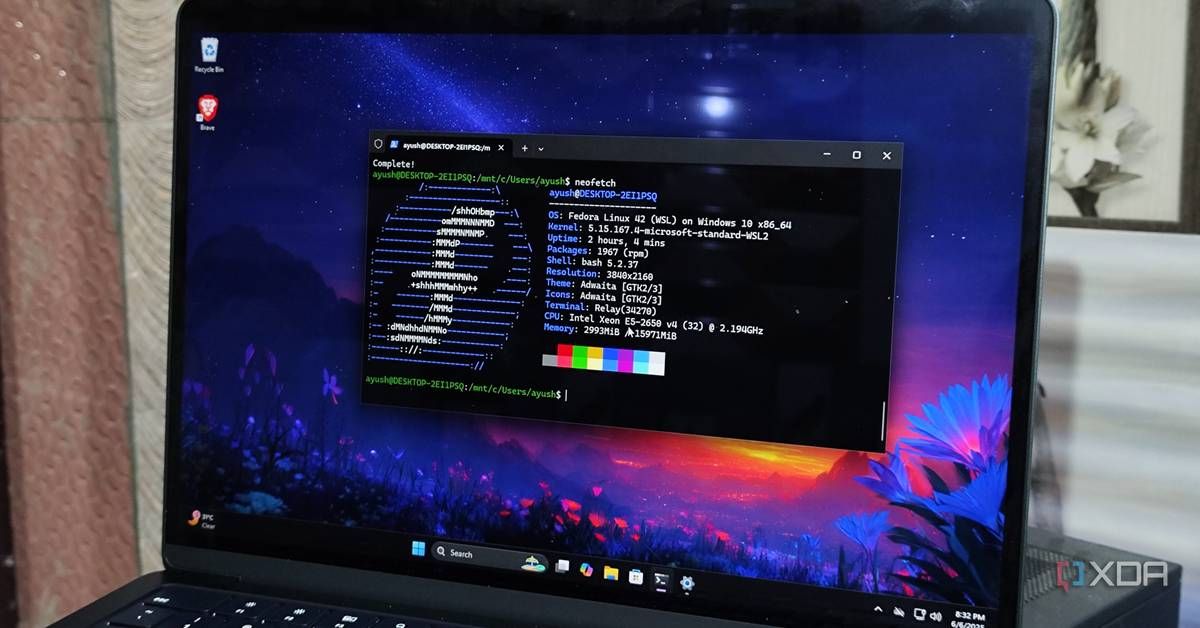
I tested dual-boot, WSL2, and VMs to run Linux apps on Windows, and only one was worth keeping
bit.ly/4d39eWS
English
D 3 B B Y ❤️
564 posts

@X4debbs
Turning complex business logic into simple, effective code. Specialist in Python & SQL. 🐍✨

I have added two new endpoints to the API. These endpoints get the data from the Ransomware IOCs by Group. A little over 19,000 in total for now. You can find the new endpoints and a updated note on the two API pages at the top. Interested in buying: darkwebinformer.com/api-details/