YingMuo
11 posts

YingMuo
@YingMuo
Rookie Security Researcher. Focus on IoT and learning macOS Security.
Katılım Temmuz 2019
202 Takip Edilen235 Takipçiler

Although I have participated in Pwn2Own Ireland/Toronto three times before, this was my first time applying for Pwn2Own Berlin. Unfortunately, I cannot show my macOS LPE at this year’s event. Rooting for my teammate this time.
NiNi@terrynini38514
Although I was the Master of Pwn at Pwn2Own Toronto 2022, this is my first time participating in #Pwn2Own in person. It’s a shame that I can’t demonstrate the Safari exploit developed by me and @h3xr4bb1t this time nor the other exploits polished by my colleagues at DEVCORE. We initially submitted 15 entries, including an amazing macOS LPE by @YingMuo. zerodayinitiative.com/blog/2026/5/13…
English

The slide from my Pwn2Own QNAP NAS talk at AVTOKYO2025 was published on 11/26. But Ryuokyo Canyon was so beautiful that I completely forgot to post about it on X 😅.
You can find the slide on the AVTOKYO website:
avtokyo.org/avtokyo2025/ti…]
English

My first English presentation. 😊
avtokyo@avtokyo
Returned to QNAP TS-464 at Pwn2Own and Pwned It Again! by Jian-Lin Peng #avtokyo
English
YingMuo retweetledi

Confirmed! All that's old is new again as the @DEVCOREteam used multiple injections and a format string bug(!) to exploit the QNAP TS-453E. Their unique bugs earn them $40,000 and 4 Master of Pwn points.
English
YingMuo retweetledi

Boom! YingMuo (@YingMuo), HexRabbit (@h3xr4bb1t), LJP (@ljp_tw) from DEVCORE Research Team and nella17 (@nella17tw) from the DEVCORE Intern Program needed little time to exploit the QNAP TS-453E NAS device. They head off to the disclosure room to provide details. #Pwn2Own
English
YingMuo retweetledi

[ZDI-25-309|CVE-2025-2146] (Pwn2Own) Canon imageCLASS MF656Cdw sfpcmAuthenticateSecAdmin Stack-based Buffer Overflow Remote Code Execution Vulnerability (CVSS 8.8; Credit: YingMuo (@YingMuo) working with DEVCORE Internship Program.) zerodayinitiative.com/advisories/ZDI…
English
YingMuo retweetledi

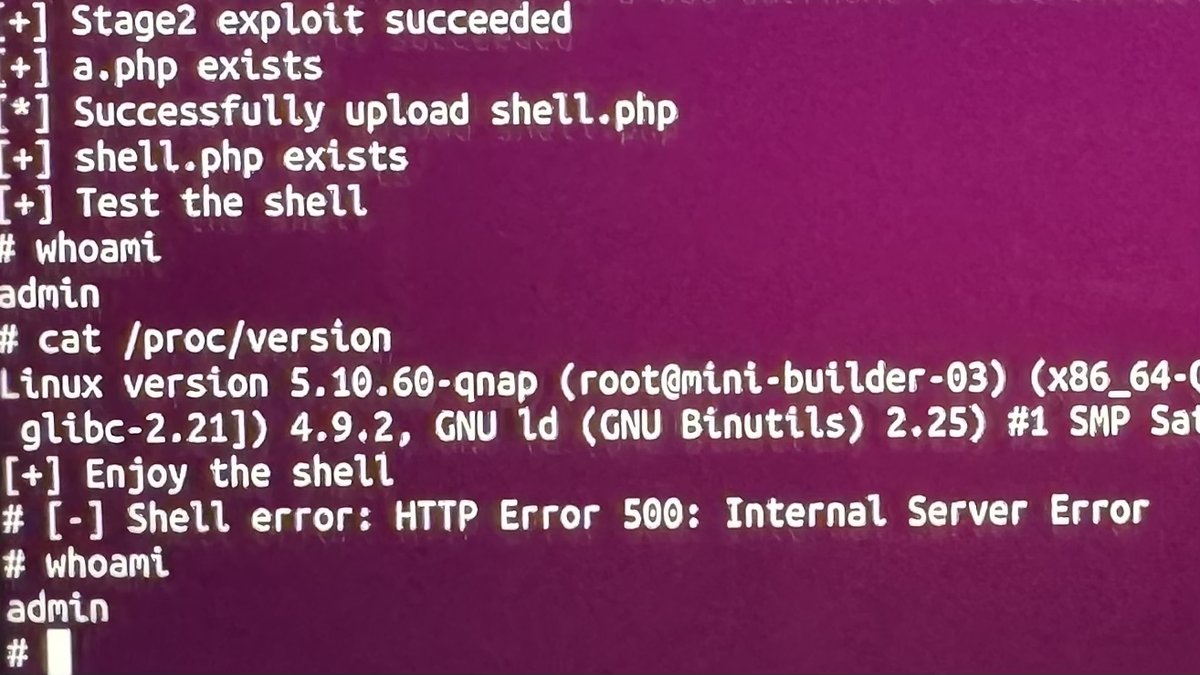
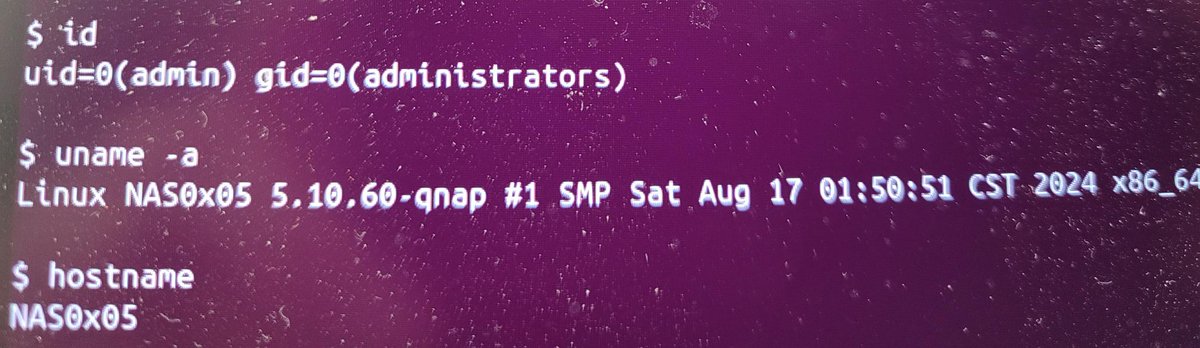
Confirmed! YingMuo (@YingMuo) working with DEVCORE Internship Program used an argument injection and a SQL injection to get their root shell on the QNAP TS-464 NAS. Their third-round victory gets them $20,000 and 4 Master of Pwn points. #Pwn2Own #P2OIreland
English
YingMuo retweetledi

Unfortunately, YingMuo (@YingMuo) of the DEVCORE Internship Program could not get his exploit of the Canon imageCLASS MF656Cdw working within the time allotted.
English
YingMuo retweetledi

I created a Linux Kernel challenge “Halloween” for the HITCON CTF Qual 2024 :). Below are the official writeup for “Halloween” and the unofficial writeups for "v8sbx" and "reEscape". Enjoy it!
Halloween & v8sbx: u1f383.github.io/ctf/2024/07/16…
reEscape: u1f383.github.io/ctf/2024/07/18…
English
YingMuo retweetledi

Success! A DEVCORE Intern was able to execute a stack overflow attack against the TP-Link Omada Gigabit Router and exploit two bugs in the QNAP TS-464 for the SOHO Smashup. They earn $50,000 and 10 Master of Pwn points. #Pwn2Own

English
