
Alexander Mackie
1K posts


Alexander Mackie
@ZanderMackie
Security research and other such things. Detection engineer @datadogHQ



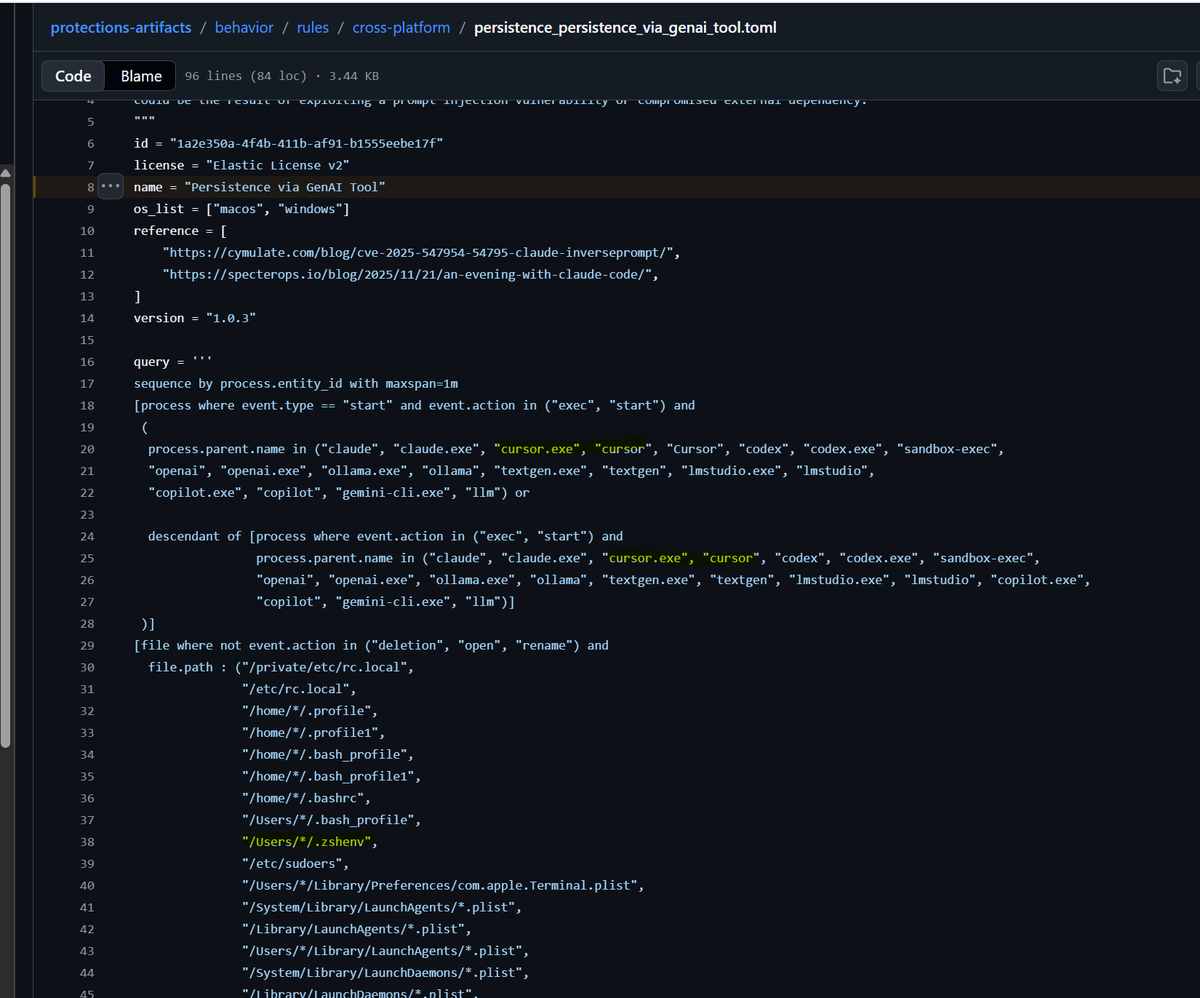
New blog: We found a sandbox breakout and remote dev tunnel bug in Cursor. Called it NomShub. It was fun making my vscode dev tunnel C2 dashboard pink. na2.hubs.ly/H04GPbw0

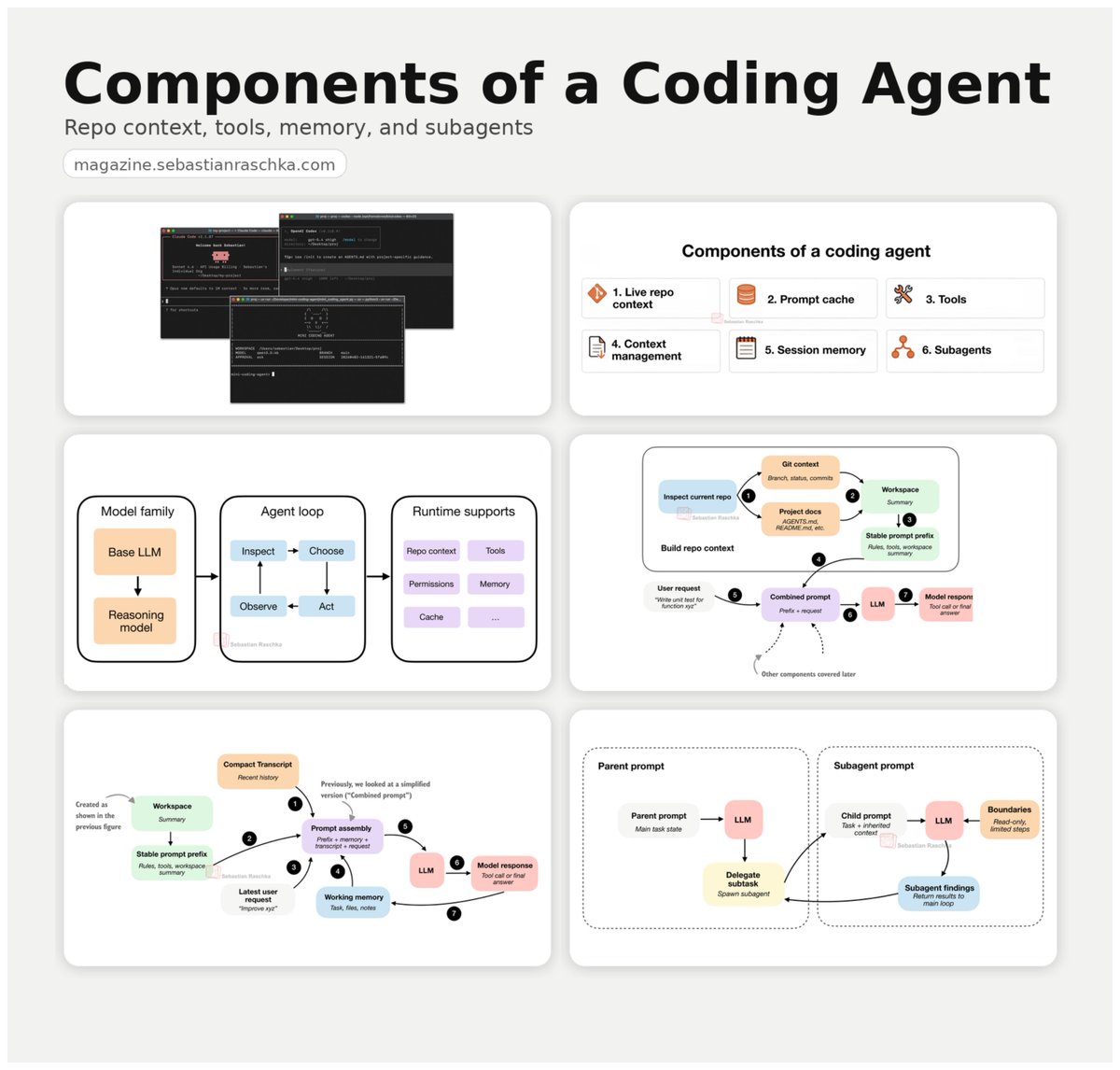
Nicholas Carlini, Anthropic Researcher, reports that Claude Code found multiple remotely exploitable security vulnerabilities in the Linux kernel. Includes a bug that evaded human software engineers for an astonishing 23 (!) years.


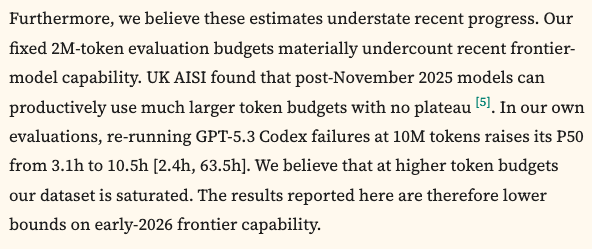
Here’s an independent domain extension of METR’s famous time-horizon analysis, applying it to offensive cybersecurity with real human expert timing data Similar to METR: 5.7 months doubling time. Frontier models now succeed 50% of the time at tasks that take human experts 10.5h.







Gemma 4 by @GoogleDeepMind debuts at 3rd and 6th on the open source leaderboard, making it the #1 ranked US open source model. By total parameter count, Gemma 4 31B is 24× smaller than GLM-5 and 34× smaller than Kimi-K2.5-Thinking, delivering comparable performance at a fraction of the footprint.




I'd say "I called this" but I didn't really call anything; more like standing on the shore going "yup, the tide is coming in". Most important open source project, went from slop reports to drowning in real vulnerability reports: lwn.net/Articles/10656…


North Korea planted malicious code in Axios - one of the most popular JavaScript libraries, used by developers worldwide: in AI tools, ML pipelines, and fintech infrastructure. Had the attack gone undetected, infected packages could have reached hundreds of thousands of projects, servers, and production systems - from startups to banks and government institutions. The malware collected host data and waited for orders from Pyongyang, running on Linux, macOS, and Windows. STARDUST CHOLLIMA - a DPRK unit specializing in cryptocurrency theft and software supply chain attacks is behind the op. The motivation is simple: cash for the regime. The target: everyone who has ever imported axios.




