Rohan
1.2K posts

Rohan
@_Base_64
Security Researcher on HackerOne, Worked with over 100 organizations and ranked among the Top 100 globally.
Katılım Mayıs 2018
1.3K Takip Edilen2.7K Takipçiler
Sabitlenmiş Tweet

Rohan retweetledi
Rohan retweetledi

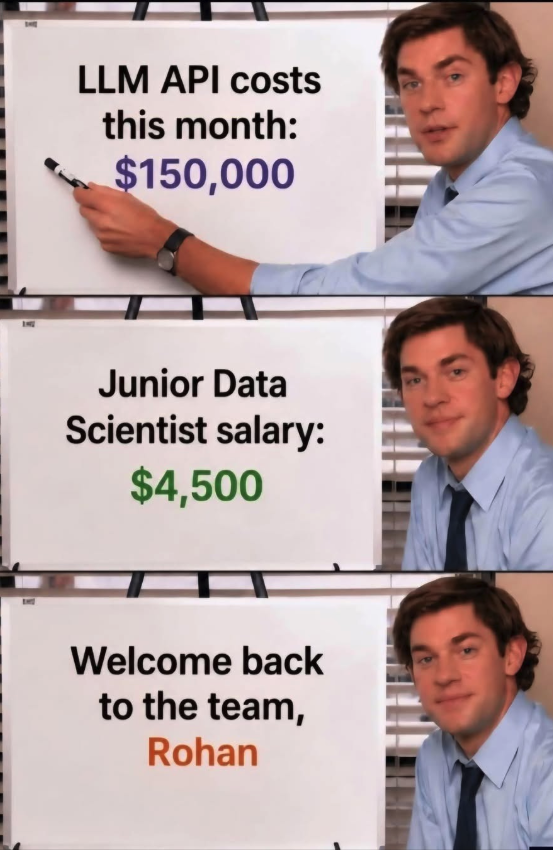
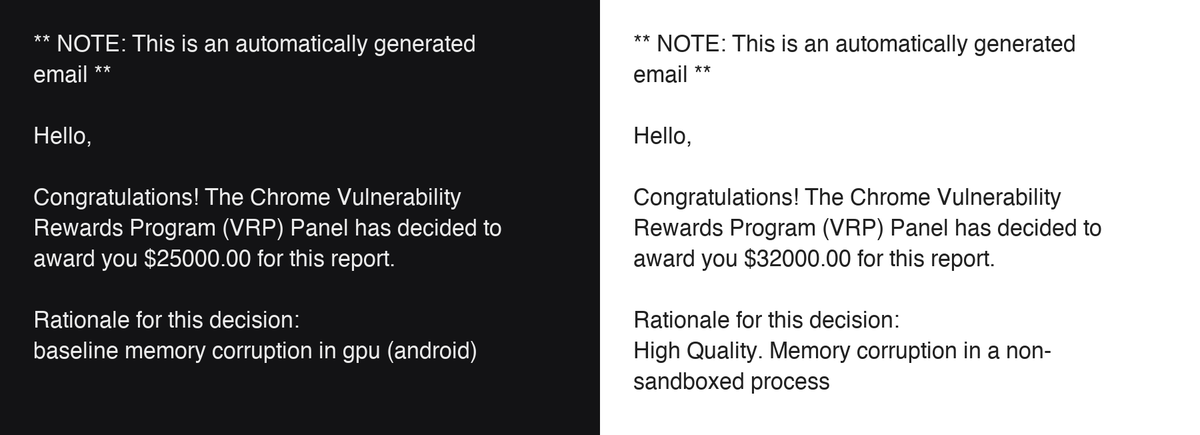
Google paid us $57,000 for two bugs in Chrome.
We’re not doing this for the bounty, but it’s always fun to get rewarded.
These bugs were found using nothing fancier than a $20/month AI subscription.
If you’re curious, come check out our talk at the Real World AI Security Conference at Stanford: seclab.stanford.edu/RealWorldAIsec/
We haven’t published the Chrome bugs in our MAD Bugs series. They work better as part of something even more fun, stay tuned!
English

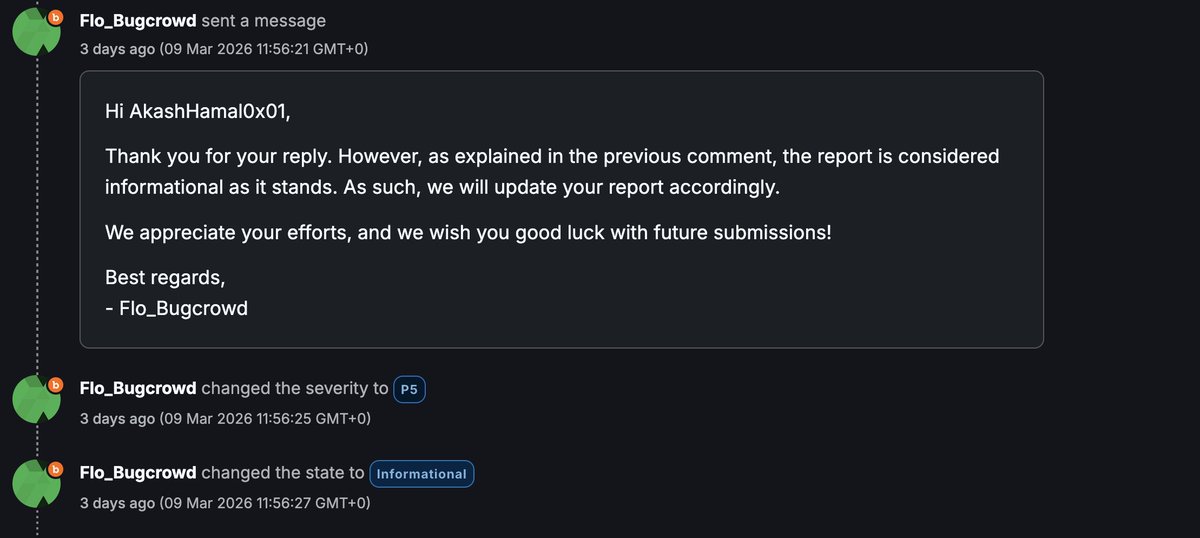
@AkashHamal0x01 One of my favourite programs moved from HackerOne to Bugcrowd, and it ended up taking around three months just to triage one report. After that experience, I decided to stop working on the program.
English

> Provide Cleanest POC, get informative
> Contact security team via Email, provide some insights of report and impact
> Triaged after 3 days
So how hard was it reproduce the report? i provided python POC, screenshots and everything , nothing stopped triage from making it info

root@AkashHamal0x01:~/ # 🇵🇭@AkashHamal0x01
Hunting on Bugcrowd be like : - 1 week gaps between replies = late triage - No manual severity? Found a vulnerability that is P2 or P1 but impact is not in VRT category? congratulations you cannot select severity and now your report will take like 1 week to be seen
English
Rohan retweetledi

Oh we do. I was just about to make a post on how this is reminiscent of when Nuclei came out. People were literally spamming anything Nuclei spat out as low severity or higher. Imagine an open scope vdp program and imagine all the results.
Now imagine 50+ hackers doing the same and reporting the exact same nuclei results. Now this feels exactly the same, but much worse.
Getting no results on Nuclei eventually pushed you to abandon the tool and learn web app, if you wanted to be successful. I really don’t see beginners willing to abandon Claude to learn and understand web applications and testing strategies. Of course a few will, but in my 5 years of triage, I can almost guarantee that most won’t.
And those people will be the first casualties of AI.
Michael Blake@Michael1026H1
Agents feel like the next Nuclei. Can be very helpful, but results really depend on customization and where you point it. I also expect a triagers will be dealing with a lot of reports that the reporter doesn't understand.
English
Rohan retweetledi

At @yeswehack, we use AI to solve security problems, not to harvest human intelligence. 🤖
Our rollout of AI features is grounded in non-negotiable principles 👇
🤝 AI where it helps, humans where it matters – automating repetitive tasks while experts focus on complex challenges and customer context
🧑💻 Humans-in-the-loop, always – augmenting analysts, but critical decisions remain firmly in human hands
🛡️ Customers in control – empowering security teams to choose which features to use, on their terms
Find out more: yeswehack.com/product/ai-vul…
English
Rohan retweetledi

Just heard about HackerOne allegedly training an AI pentesting agent on private bug bounty reports.
Which is great news.
I’ve always wanted to be part of something bigger than myself.
Like a dataset.
I logged into the platform to review one of my old private reports.
The one with the 47-step reproduction chain and the custom Burp extension I wrote at 2:13am.
It now feels less like a finding.
More like a contribution to the collective.
Some people are upset that private reports might be used to train an AI.
I prefer to think of it as mentorship.
I walked so the model could run automated recon at scale.
That’s legacy.
The platform says it’s trained on years of proprietary exploit intelligence.
Which sounds suspiciously like “stuff we already did.”
But I appreciate the rebrand.
I used to be a hacker.
Now I’m pre-training data.
Career growth.
I checked my dashboard to see if I get royalties.
There is no royalties tab.
But there is a leaderboard.
I assume the AI is climbing it.
I hope it enjoys the hoodie.
A few researchers are worried this devalues human work.
I disagree.
My work has never been more valuable.
It’s now infinitely reusable.
Like a zero-day sourdough starter.
I submit vulnerability reports.
The AI absorbs them.
The AI pentests the same targets next quarter.
Somewhere in there is synergy.
Or recursion.
Hard to tell.
I asked support if the AI will be submitting duplicate reports based on patterns it learned from mine.
They said the system is designed to enhance signal.
I respect that.
Nothing enhances signal like automation replaying my exact payloads at machine speed.
I’ve decided to lean into this.
From now on, I will optimize my reports for model readability.
Clear headings.
Concise PoCs.
Structured exploitation paths.
If I can’t win the bounty, I can at least improve the weights.
This is what scale looks like.
The future of bug bounty is continuous, AI-driven testing powered by historical exploit intelligence.
Which is a very elegant way of saying:
“Remember that bug you found? It found you back.”
I’m proud to be part of the ecosystem.
Even if the ecosystem is now pentesting itself.
Submitting my next report tonight.
For training purposes.
English
Rohan retweetledi
Rohan retweetledi

How to access servers behind Cloudflare by bypassing the firewall?
@FearsOff #bugbountytips #cloudflare #firewall #bypass
1) Found a sweet hostname but Cloudflare Firewall blocks you? There's a neat trick attackers can use if the origin is misconfigured.

English
Rohan retweetledi
Rohan retweetledi

As an update, H1 increased the severity to Medium 5.3 this morning, agreeing on the low complexity and adding a $1.5k bounty, totaling $2.9k. Not too shabby for a Medium, we are balling chat

GIF
publiclyDisclosed@disclosedh1
HackerOne disclosed a bug submitted by @0xw2w: hackerone.com/reports/2937622 - Bounty: $1,200 #hackerone #bugbounty
English

@b4tm4Nx0 @Hacker0x01 Congrats, bro! It’s a start—you’ll soon find bugs on BBP.
English

@_Base_64 @Hacker0x01 Today I was just tracking my shipment and found a XSS bug 😆
That's my first valid bug......But unfortunately the company doesn't have any BBP or VDP, however I reported them through their email.
English

@b4tm4Nx0 @Hacker0x01 Thanks :). It takes time to find the first bug, but be persistent, and you will definitely find your first bug. Focus on one vulnerability for now and look everywhere.
English

@_Base_64 @Hacker0x01 Congrats....
I am struggling to find my first valid bug
English

@_Base_64 @Hacker0x01 AAP ne Pakistan m kon se payment option chose kiya hai like bank, crypto etc
?
HT

@_Base_64 @Hacker0x01 where to practice this vuln type. 😂 any firing range near us?
English

Yay, I was awarded a $69,696.9 bounty on @Hacker0x01 .
Bug: Access to server credentials by threatening developer at gunpoint.
English

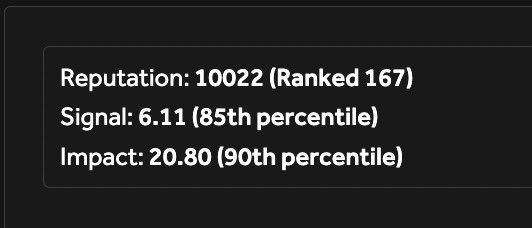
Crossed 10000 reputation points on @Hacker0x01, gaining 8013 reps in last 365 days.
Also reached all time top 170 hackers on @Hacker0x01
Next target - Reach all time top 100 on @Hacker0x01 without disturbing my personal life and as chill as possible like before.
#bugbounty #cybersecurity #achievement

English